
Orchestrating AI Agent Workflows for Scalable Employee Productivity
To download this as a free PDF eBook and explore many others, please visit the AugVation webstore:
Introduction
Purpose and Scope
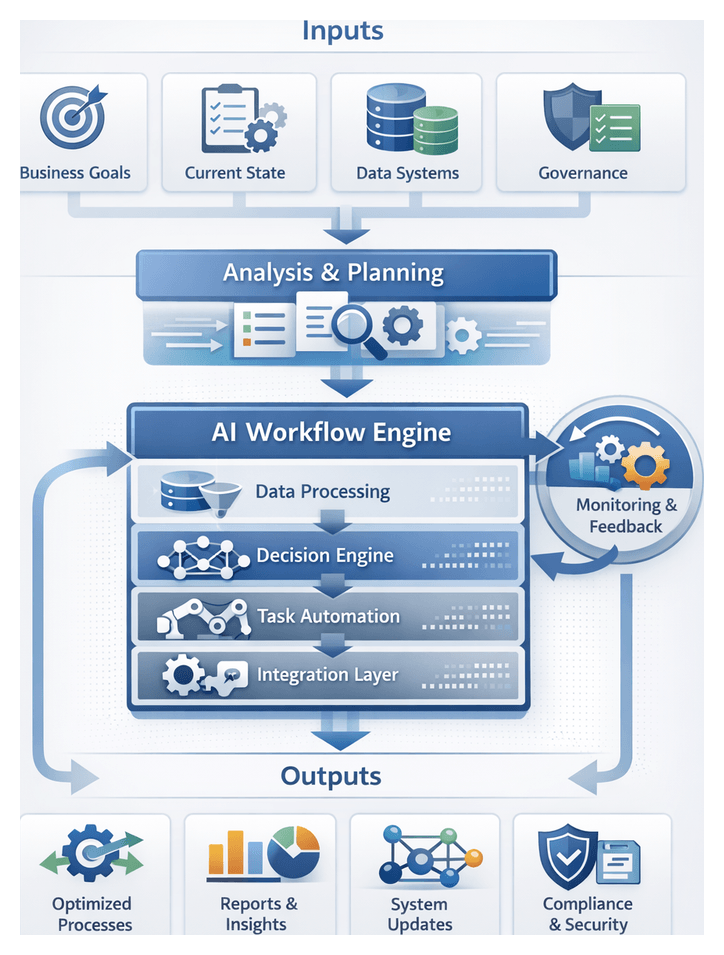
In the initial stage of an AI-driven workflow initiative, organizations establish a strategic foundation to drive scalable productivity. This stage clarifies pain points caused by fragmented tasks, manual handoffs, and data silos. It aligns executive sponsors, functional leaders, IT architects, and end users around shared objectives, success metrics, and governance principles. By documenting existing gaps and defining scope, timelines, and risk tolerance levels, stakeholders gain a unified vision. These preparations mitigate misalignment and technical dependencies, providing a baseline for all subsequent design, integration, and deployment activities.
Inputs and Prerequisites
- Stakeholder Alignment and Vision Setting: Document high-level business objectives, ROI targets, process latency issues, success criteria, and governance models.
- Current State Assessment: Conduct process mapping, time-and-motion studies, system log reviews, and frontline interviews to quantify manual effort and identify bottlenecks.
- Data and System Inventory: Compile an inventory of CRM, ERP, HRIS, ticketing systems, databases, data lakes, APIs, middleware, messaging platforms, data quality metrics, and security mechanisms.
- Governance, Security, and Compliance: Define data stewardship roles, model governance procedures, risk assessment frameworks, audit trail requirements, and policy enforcement thresholds.
- Executive Sponsorship and Resource Commitment: Secure budget, project timelines, cross-departmental participation, KPI definitions, and escalation paths.
- Risk Identification and Mitigation: Map risks related to data quality, legacy integration, change management, and regulatory constraints, assigning responsible parties and contingency actions.
- Scope, Boundaries, and Success Metrics: Draft a scope document outlining in-scope workflows, architectural boundaries, primary metrics like cycle time reduction and error elimination, and a high-level roadmap.
Designing a Structured AI Workflow
Enterprises operate within a complex mosaic of applications, data repositories, and human roles. A structured AI workflow serves as a blueprint that maps each activity to clear process steps, assigns responsibilities between automated agents and human contributors, and orchestrates data exchange. This end-to-end sequence ensures repeatability, visibility, and scalability, eliminating ad hoc decision-making and manual delays.
End-to-End Workflow Definition
Workflows begin with trigger conditions—such as new data arrival, user requests, or scheduled events—and proceed through AI-driven analysis, data transformations, automated actions, and user interventions. Outputs may be delivered to end users, forwarded to other systems, or fed back to support continuous optimization. Key characteristics include clarity of inputs and outputs, defined decision points leveraging AI inference or business rules, explicit integration points with systems like Salesforce, SAP S/4HANA, or document management platforms, exception handling, and audit logging.
Key Components
- Trigger Module: Initiates workflows based on events, messages, or schedules.
- Data Ingestion and Preprocessing: Extracts, cleanses, and normalizes data, applying anomaly detection and schema enforcement.
- Decision Engine: Applies business rules and model predictions, supporting branching logic and probabilistic inference.
- Task Orchestration Layer: Coordinates activity sequences, supports parallel execution, and routes tasks between AI agents and humans.
- Integration Connectors: Interface with external systems using REST APIs, message queues, or webhooks.
- Monitoring and Logging: Captures telemetry on execution times, error rates, and resource utilization for compliance and analysis.
- Feedback Loop and Learning: Ingests performance metrics and user feedback to retrain models and refine rules.
System Integration Patterns
Seamless interactions depend on standardized communication protocols, shared schemas, and resilient connectivity. Common patterns include:
- REST APIs for synchronous exchanges with platforms like Salesforce or SAP S/4HANA.
- Event-driven messaging via Apache Kafka, RabbitMQ, or Azure Event Grid.
- Webhooks for notifications and callbacks.
- Database connectors and file transfers for batch data.
- Authentication with OAuth2, JWT, or API keys.
For example, an AI agent may pre-screen customer support requests using the OpenAI GPT series, create tickets in a service management platform, and notify teams through Microsoft Teams or Slack.
Human and AI Collaboration
AI agents excel at high-volume tasks and pattern recognition, while humans provide domain expertise and ethical judgment. Workflows should delineate autonomous AI actions and handoff points for human review. In invoice processing, AI-based OCR services extract data, reconciliation agents validate against master data, and exceptions above thresholds route to human approvers. Approved invoices then flow to payment through the ERP system, with real-time updates sent via chat or email.
AI Agents as Unifying Operatives
AI agents bridge operational silos by coordinating services, automating decisions, and aligning human tasks with digital processes. They exhibit perception, reasoning, and action capabilities to monitor triggers, interpret context, and execute tasks autonomously or in tandem with users.
- Task Orchestration: Invoke services, applications, or sub-agents in defined sequences.
- Data Integration: Ingest, normalize, and route data for consistency.
- Contextual Reasoning: Apply domain rules and predictive models at runtime.
- Adaptive Learning: Refine performance through feedback and monitoring.
- Human-AI Collaboration: Facilitate handoffs and surface actionable insights.
Integration and Orchestration Patterns
- Event-driven coordination with Kafka or Azure Event Grid.
- API-first connectivity to Salesforce or SAP S/4HANA.
- RPA augmentation combining UiPath or Blue Prism with AI decision agents.
- Containerized microservices on Kubernetes.
- Hybrid workflows with approvals in Slack or Microsoft Teams.
Decision Automation and Human Oversight
Agents use rule engines, machine learning, and optimization models. They proceed autonomously when confidence exceeds thresholds, otherwise escalating to human reviewers. Recommendation engines, such as IBM Watson Assistant, rank options for customer support routing. Exception handling agents alert stakeholders, while approval workflows integrate with Oracle ERP for digital signatures and audit logging.
Case Illustrations
In purchase order processing, an AI agent extracts line items via OCR and NLP models on Google Cloud AI, validates codes against an ERP, checks inventory, and opens tickets when discrepancies arise. In HR onboarding, agents orchestrate document collection, background checks via AWS IAM, orientation scheduling, and compliance reminders.
Operational Benefits and Considerations
- End-to-end visibility through unified dashboards.
- Consistency and compliance with automated logic.
- Accelerated cycle times and improved responsiveness.
- Resource optimization by offloading routine tasks.
- Scalability via containerized architectures.
Key considerations include data governance, security controls, telemetry with Prometheus and Grafana, change management, and technology selection aligned with platforms like Azure AI or open-source frameworks such as TensorFlow.
Deliverables, Dependencies, and Handoffs
The Introduction stage produces strategic artifacts that guide detailed design and implementation and formalizes dependencies to ensure seamless progression.
Key Deliverables
- Process Gap Analysis Report: Identifies inefficiencies, handoffs, and silos, highlighting high-impact automation opportunities.
- Stakeholder Alignment Matrix: Maps roles, responsibilities, and communication preferences.
- Objectives and Success Metrics: Translates strategic goals into KPIs, targets, and timelines.
- High-Level Architecture Blueprint: Illustrates core AI ecosystem components, integration points, and data flows.
- Risk and Dependency Assessment: Lists technical, organizational, and compliance risks with mitigation strategies.
- Executive Recommendation Brief: Synthesizes findings for senior leadership, including timelines, resources, and cost-benefit analysis.
- Communication and Change Management Plan: Outlines stakeholder messaging, training strategies, and update cadence.
Critical Dependencies
- Executive sponsorship and defined governance frameworks.
- Stakeholder engagement sessions, including workshops and interviews.
- Access to process documentation, SOPs, and system specifications.
- Technology landscape audit covering applications, databases, and integration points.
- Data availability and quality assessments.
- Resource allocation and project team structure.
- Compliance constraints related to GDPR, HIPAA, or industry standards.
- Provisioning of collaboration and repository tools.
Handoff Mechanisms
- Gap Analysis to use-case teams for scenario prioritization.
- Success Metrics to data strategy groups for defining data requirements.
- Architecture Blueprint to agent design leads for module configuration.
- Risk Assessment to infrastructure and security teams for mitigation planning.
- Executive Brief to the steering committee for roadmap approval.
- Alignment Matrix to change management for tailored communications.
- Change Plan to the PMO for integration into project schedules.
Each handoff is accompanied by review meetings, approval checklists, version-controlled deliverables, and a centralized repository to preserve audit trails and accountability. This disciplined approach ensures that the project advances on a solid strategic and architectural foundation.
Chapter 1: Defining Productivity Objectives and Use Cases

Purpose and Scope of Objectives and Use Case Definition
Defining clear productivity objectives and consolidating use case inputs establishes the foundation for any AI agent workflow initiative. This stage translates high-level strategic imperatives into measurable performance metrics, aligns stakeholder expectations, and captures essential process and technology context. By articulating purpose and inputs at the outset, organizations maintain focus on delivering tangible business value throughout design, development, and deployment.
Many enterprises face operational complexity driven by siloed processes, manual handoffs, and fragmented reporting across marketing, sales, customer support, finance, and HR. These discontinuities undermine efficiency, obscure accountability, and frustrate employees. To address these challenges, leading organizations orchestrate AI agent workflows that automate repetitive tasks, surface actionable insights, and enforce standardized procedures. Establishing objectives and use case definitions equips teams with a clear roadmap, reducing uncertainty and accelerating time to value.
Translating Business Goals into Measurable Objectives
Translating strategic goals into quantifiable targets is critical to avoid drifting into proofs of concept with limited returns. Well-defined productivity objectives enable leaders to:
- Measure progress against benchmarks such as reduced turnaround times, error rates, or resource utilization.
- Align cross-functional teams on success criteria, avoiding misaligned priorities.
- Compare use case scenarios based on expected ROI, implementation cost, and strategic impact.
- Provide data-driven rationale for executive sponsorship, budget allocation, and change management.
Key Inputs for Objective Setting
Building meaningful objectives requires structured intake of information from business leaders, process owners, and technical teams. Essential input categories include:
- Strategic Imperatives: Documented business unit goals, enterprise strategic plans, and competitive targets that define desired outcomes.
- Stakeholder Requirements: Feedback capturing pain points, compliance needs, and success factors from department heads, frontline employees, and end users.
- Performance Indicators: Existing KPIs such as customer satisfaction scores, average handling times, throughput volumes, and cost per transaction.
- Process Documentation: Current process maps, standard operating procedures, and workflow diagrams revealing handoff points, decision gates, and data dependencies.
- Technology Landscape: Inventory of enterprise systems, data warehouses, APIs, and integration capabilities that will support or constrain agent deployment.
- Regulatory and Security Constraints: Compliance requirements, data privacy standards, and access control policies that must be enforced throughout AI workflows.
Prerequisites for Use Case Definition
Before ideation and evaluation begin, organizations must satisfy several conditions to ensure feasibility and integrity:
- Executive Sponsorship: Visible support from senior leadership secures resources, drives adoption, and aligns stakeholders.
- Cross-Functional Engagement: A steering committee or working group representing business, IT, legal, compliance, and data governance teams fosters shared ownership.
- Data Availability and Quality: Assessment of data sources for completeness, accuracy, timeliness, and accessibility is critical for reliable AI outputs.
- Technical Readiness: Documentation and validation of infrastructure capacity, API endpoints, authentication mechanisms, and toolchain compatibility.
- Governance Framework: Defined roles, decision rights, and approval workflows to manage changes in scope, data access, and performance criteria.
Use Case Intake and Prioritization Workflow
Managing a portfolio of AI use case proposals requires a structured intake and prioritization process. This workflow translates stakeholder requirements into validated scenarios, ranks them objectively, and secures executive approval. The following activities ensure that organizational goals drive consistent, high-impact automation initiatives.
Establishing a Use Case Intake Process
To manage ideation at scale and maintain transparency, organizations often deploy a centralized intake portal or form. Stakeholders submit proposals with scoped objectives, resource estimates, and success metrics. A solution provides templated intake forms that capture business requirement statements, high-level process flows, baseline performance reports, risk assessments, and technology integration matrices. Submissions are reviewed regularly in intake workshops, where standardized scoring criteria—such as expected ROI, complexity score, risk level, and strategic fit—are applied to prioritize requests objectively. Governance checkpoints at defined intervals ensure that emerging priorities and resource constraints inform approval decisions.
Prioritization Criteria
- Return on Investment: Quantified benefits versus total cost of ownership.
- Time to Value: Estimated deployment timeline and speed of measurable impact.
- Implementation Complexity: Technical dependencies, integration effort, and data preparation requirements.
- Risk Exposure: Data sensitivity, regulatory impact, and operational criticality.
- Scalability Potential: Ease of extending the use case across geographies or business units.
1. Stakeholder Requirements Gathering
In this activity, project managers coordinate interviews and workshops to capture detailed requirements. Key practices include:
- Scheduling sessions via calendaring systems and collaboration suites.
- Distributing prework questionnaires through survey tools to elicit priorities.
- Recording discussions in centralized knowledge repositories for traceability.
- Tagging requirements in a management system for version control.
- Assigning follow-up tasks to subject matter experts in project tracking software.
2. Defining Measurable Metrics
Once requirements are gathered, teams translate them into KPIs and target thresholds through:
- Mapping each requirement to productivity metrics such as cycle time, accuracy improvements, or customer satisfaction.
- Leveraging business intelligence dashboards to retrieve baseline performance values.
- Consulting data governance systems to verify metric definitions and lineage.
- Documenting target improvements (for example, 30 percent reduction in manual approval time).
- Storing metric definitions in a shared performance tracking repository.
3. Requirement Consolidation and Validation
Consolidating and validating requirements prevents redundant or infeasible scenarios from advancing:
- Importing requirements into an AI-augmented consolidation tool to identify overlaps.
- Applying semantic clustering algorithms to group related objectives.
- Reviewing consolidated groups with stakeholders via video conferencing platforms.
- Validating groupings against data availability constraints in the enterprise data catalog.
- Updating the requirements management database to reflect validated clusters.
4. Scenario Modeling and Prioritization
With validated requirements, the workflow proceeds to define and rank potential AI use case scenarios:
- Drafting scenario narratives that describe process inputs, decision logic, and expected outputs.
- Estimating effort, resource needs, and anticipated ROI using scenario evaluation tools.
- Invoking an AI ranking service—such as the ranking module in OpenAI API—to score scenarios based on complexity and business impact.
- Facilitating prioritization workshops with decision-makers using shared whiteboarding applications.
- Locking in a ranked backlog of use cases in the project management platform.
5. Final Alignment and Approval
- Generating a summary report of prioritized scenarios in a document management system.
- Circulating the report to the steering committee via secure file sharing.
- Collecting approvals or feedback using e-signature and approval workflows.
- Updating contract and budget planning tools with approved scope items.
- Notifying project teams and transitioning to design activities.
Workflow Actors and System Interactions
The intake and prioritization workflow orchestrates interactions between human actors and supporting platforms:
- Business Sponsors: Define strategic objectives in portfolio management tools and sign off on priorities.
- Project Managers: Orchestrate workshops and track tasks in project management systems.
- Subject Matter Experts: Provide domain context via knowledge repositories and collaboration suites.
- Data Analysts: Retrieve baseline metrics from data warehouses and BI dashboards.
- AI Services: Apply clustering, ranking, and semantic analysis algorithms through API calls.
- Governance Officers: Validate metric definitions in compliance and data governance platforms.
- Executive Review Board: Approves finalized backlogs using e-signature and approval tracking systems.
Outputs and Handoff Criteria
Upon completion of goal translation and prioritization, the following artifacts and conditions enable a seamless transition to design and development:
- Approved use case backlog with ranked scenarios and associated KPIs.
- Consolidated requirements document stored in the centralized repository.
- Baseline metric snapshot and target improvement thresholds.
- Stakeholder alignment sign-off records.
- Handoff checklist confirming data availability, scope clarity, and resource assignments.
AI-Driven Scenario Prioritization
AI agents leverage advanced algorithms to ingest diverse inputs—business objectives, process maps, historical performance data, and stakeholder feedback—and produce objective, data-driven scenario rankings. This approach replaces manual spreadsheet assessments and accelerates decision-making while maintaining transparency and repeatability.
Fundamentals of AI-Driven Evaluation
- Requirement Ingestion: NLU agents parse stakeholder documents and workshop notes to extract requirements and KPIs.
- Feature Extraction: Machine learning models convert qualitative inputs into structured features such as automation potential and risk reduction.
- Scoring Algorithms: Decision-optimization engines weigh factors like cost, risk, time-to-value, and resource availability.
- Ranking and Recommendations: Optimization routines produce a prioritized list of scenarios with confidence scores and sensitivity analyses.
Key AI Capabilities and Tools
- Natural Language Understanding: Frameworks like OpenAI and Microsoft Azure Cognitive Services process unstructured text.
- Machine Learning Classification and Clustering: Supervised models and unsupervised algorithms group and categorize use cases.
- Decision Optimization: Multi-objective solvers evaluate trade-offs between cost, risk, and impact.
- Knowledge Graph Analytics: Platforms such as IBM Watson and Google Vertex AI analyze relationships among processes and stakeholders.
- Explainable AI: Interpretability tools generate human-readable rationales for scenario scores.
Supporting Systems and Infrastructure
- Unified Data Repository: Centralized data lake or warehouse aggregates metrics, performance logs, and feedback.
- Metadata Catalog: Catalogs maintain metadata on source systems, data quality, and governance.
- Workflow Orchestration Engine: Platforms like Apache Airflow and UiPath automate sequencing of AI tasks.
- Visualization and Collaboration: Dashboards built with Tableau and Microsoft Power BI present rankings, confidence intervals, and analyses.
Agent Roles in the Prioritization Workflow
- Requirement Analysis Agent: NLU-powered agent extracts objectives and constraints from unstructured inputs.
- Feature Engineering Agent: AutoML transforms raw data into scoring attributes, quantifying complexity factors.
- Scoring and Ranking Agent: Applies decision-optimization libraries to compute weighted scores and run sensitivity analyses.
- Feedback Loop Agent: Captures stakeholder feedback, refines scoring models, and supports continuous learning.
Integration with Solution Architecture
Scenario prioritization outputs feed directly into agent design and configuration. Integration points include:
- Export of prioritized use cases as structured artifacts (for example, JSON) into the design repository.
- Automatic generation of configuration templates outlining AI capabilities, data sources, and performance targets for each scenario.
- Trigger mechanisms in the orchestration engine to commence design activities, defining agent archetypes and mapping capabilities.
Key Deliverables and Artifacts
The objectives and use case definition stage yields a structured suite of deliverables that guide design, development, and governance:
- Objectives-to-Metrics Mapping Worksheet: Aligns each strategic objective with baseline values, target improvements, calculation formulas, and ownership.
- Stakeholder Requirements Matrix: Captures inputs from business units, operations, IT, and compliance, including priorities and constraints.
- Use Case Prioritization Report: Ranks candidate scenarios based on business value, complexity, risk profile, and strategic alignment, including narrative methodology explanations.
- Scenario Definition Templates: Standardized documents covering problem statements, personas, current and future states, KPIs, data needs, integration points, and exception handling.
- Assumptions and Risk Register: Logs project assumptions, identified risks, impacts, likelihood ratings, mitigation plans, and ownership.
- Executive Summary Deck: Concise presentation summarizing objectives, prioritized use cases, key metrics, high-level timelines, and resource needs.
Dependencies, Handoffs and Quality Gates
Ensuring a smooth transition to agent design and development requires clear preconditions, handoff criteria, and governance quality gates:
Preconditions and Resource Readiness
- Data Accessibility and Quality: Confirmation that required data sources are accessible, complete, and profiled, with cleaning and labeling plans in place.
- Infrastructure Provisioning: Development, testing, and production environments set up with compute, networking, storage, and security zones.
- Tool Licensing and Environment Setup: Licenses acquired and user accounts configured for AI frameworks, API management, and collaboration platforms.
- Security and Compliance Clearance: Data handling procedures, encryption standards, and access controls reviewed and approved.
- Budget Approval and Resource Allocation: Formal sign-off on budgets, headcount, and external services, including contingency plans.
- Governance Framework Integration: Alignment with change control boards, data governance councils, and AI ethics committees.
Handoff Criteria and Quality Gates
- Deliverable Completeness Check: All artifacts—mapping worksheets, matrices, risk registers—are populated, peer-reviewed, and version-controlled.
- Stakeholder Approval Confirmation: Formal sign-off by executive sponsor, product owner, and IT leadership documented via e-signature or governance board minutes.
- Dependency Resolution Status: Critical dependencies resolved or documented as action items with owners and due dates.
- Data and Security Clearance: Validation from data stewards and security officers that data quality and compliance requirements are met.
- Integration Spec Validation: API contracts, event definitions, and authentication methods approved by integration architects.
- Risk Mitigation Initiation: High-priority risks have mitigation actions underway; all risks have monitoring plans.
Stakeholder Roles and Collaboration Points
- Executive Sponsor: Provides strategic direction, secures funding, and approves executive summaries and risk registers.
- Product Owner: Validates use cases, prioritizes backlog, and ensures traceability of requirements.
- Business Analyst: Documents process flows, refines user stories, and maintains the requirements matrix.
- Data Engineering Lead: Defines ETL pipelines, collaborates on data quality, and validates data profiles.
- AI Solutions Architect: Develops architectural blueprints, selects AI models, and establishes technical constraints.
- Security and Compliance Officer: Reviews data protection measures and monitors regulatory adherence.
- Workflow Orchestration Specialist: Maps high-level flows, identifies event triggers, and confirms messaging infrastructure.
- Project Manager: Coordinates schedules, tracks dependencies, and updates status dashboards.
Best Practices for Governance and Continuous Improvement
- Maintain Data Quality Vigilance: Implement automated validation checks, periodic audits, and data stewardship practices to ensure input integrity.
- Define Transparent Scoring Criteria: Collaborate with stakeholders to establish clear weighting factors and thresholds; document parameters for traceability.
- Incorporate Human-in-the-Loop Reviews: Schedule interim checkpoints where domain experts validate AI-generated insights and rankings.
- Enable Iterative Refinement: Capture performance data from pilot deployments to recalibrate scoring models and use case priorities.
- Ensure Explainability and Auditability: Adopt explainable AI frameworks that produce human-readable rationales and maintain audit logs of automated decisions.
- Standardize Handoff Processes: Develop SOPs for review workshops, dependency tracking, and version control to ensure consistency.
- Leverage Automation: Automate notifications, version tagging, and dependency status updates to reduce manual overhead.
- Document Lessons Learned: Conduct retrospectives after handoff cycles to capture insights and update templates and checklists.
- Align with Agile Principles: Structure handoffs to support iterative sprints, providing design teams with prioritized user stories and minimal viable scenarios.
By rigorously defining objectives, executing AI-driven scenario prioritization, and enforcing robust governance and handoff processes, organizations lay the groundwork for scalable AI agent workflows that drive significant productivity improvements and strategic impact.
Chapter 2: Data Strategy and Preparation
The initial phase of an AI agent workflow establishes the foundation for reliable, scalable intelligence by defining how data is collected, cleansed, governed, and prepared for downstream use. Without this rigor, organizations risk feeding models with incomplete, inconsistent, or non-compliant data, leading to degraded performance, bias, and regulatory exposure. At its core, the data strategy and preparation stage aims to transform disparate raw inputs into high-quality, policy-aligned assets that drive automated decision-making and predictive analytics.
This stage focuses on three primary objectives:
- Ensuring data accuracy and consistency through standardized profiling and validation routines.
- Enforcing privacy, intellectual property, and regulatory policies via role-based controls and anonymization.
- Providing full transparency into data lineage and usage to support auditability and governance reviews.
By achieving these objectives, organizations lay a solid groundwork that reduces the risk of model drift and bias, streamlines agent configuration, and accelerates continuous improvement cycles.
Industry Challenges and the Need for a Structured Data Strategy
Across sectors such as finance, healthcare, manufacturing, and retail, enterprises grapple with an explosion of data sources and formats. Customer interactions, operational sensors, and third-party services generate high-velocity streams of structured and unstructured information. Traditional IT architectures often silo data in CRM, ERP, and document management systems, impeding unified analysis and resulting in inconsistent customer profiles, disjointed supply chain insights, and missed revenue opportunities.
The proliferation of unstructured content—emails, text transcripts, support tickets—further complicates consolidation efforts, while real-time IoT feeds demand scalable ingestion patterns. Without a coordinated data strategy, projects stall amid inconsistent records, duplicate entries, and governance blind spots. Manual compliance checks become untenable, policies go unenforced, and audit trails are incomplete.
A structured data strategy aligns technical processes, organizational roles, and compliance requirements into a coherent blueprint. It defines criteria for source selection, profiling standards, and policy enforcement mechanisms, moving enterprises beyond ad hoc data gathering toward repeatable, auditable practices. This alignment minimizes friction between domain experts and data engineers, ensures regulatory obligations are met, and preserves customer trust—especially critical in heavily regulated industries.
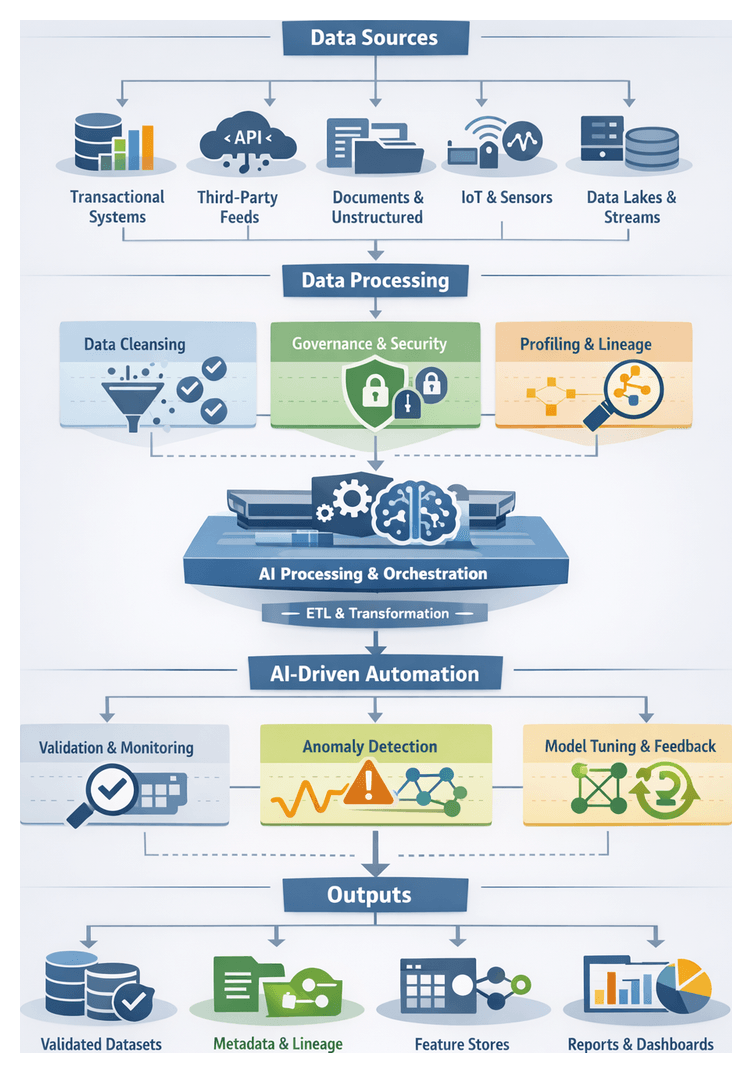
Data Inputs and Acquisition Prerequisites
Effective AI workflows depend on accurately identifying and assessing all relevant data sources. Common input categories include:
- Transactional Systems: Records from ERP, CRM, HRIS, financial ledgers, and supply chain platforms that capture business operations.
- Third-Party Data Feeds: Market intelligence, social media sentiment, geolocation, weather, and competitive benchmarks delivered via APIs.
- Document Repositories: Unstructured content stored in file shares, email archives, knowledge bases, and support ticketing systems.
- Sensor and IoT Streams: Telemetry from industrial equipment, environmental sensors, endpoint logs, and connected devices.
- Data Lakes and Warehouses: Centralized staging areas such as Databricks, Amazon S3, Hadoop clusters, or Azure Data Lake for bulk storage and archival.
- Event Streaming Platforms: Real-time capture of application logs and interactions using Apache Kafka.
Before ingesting data, certain prerequisites must be satisfied to ensure seamless integration, security, and compliance:
- Access Provisioning: Secure credentials, service accounts, OAuth tokens, and key management policies granted by data owners.
- Network and Connectivity: Firewall rules, VPN tunnels, VPC peering, and secure transport protocols (SFTP, HTTPS) configured between sources and ingestion endpoints.
- Cataloging and Classification: Inventory of data assets with metadata on sensitivity, retention policies, and business ownership.
- Regulatory and Contractual Review: Validation against internal policies, SLAs, and external mandates such as GDPR, HIPAA, or industry standards.
- Schema Specifications: Definitions of fields, data types, constraints, and relationships to guide downstream validations and transformations.
Neglecting these prerequisites can lead to pipeline failures, security vulnerabilities, and legal liabilities, compromising the entire AI initiative.
Data Quality, Cleansing, and Enrichment
Data quality is the linchpin of reliable AI outcomes. Cleansing processes detect anomalies—missing values, inconsistent formats, duplicates, and outliers—and remediate them before data enters model training or real-time inference pipelines. A systematic approach typically comprises profiling, standardization, enrichment, and validation steps, often automated through AI-driven tools.
- Profiling and Statistical Assessment: Analyzing distributions, null counts, and pattern anomalies using Azure Machine Learning, open-source frameworks, or custom scripts.
- Deduplication and Record Linkage: Merging duplicate records based on unique keys, fuzzy matching algorithms, or heuristic rules.
- Normalization and Standardization: Uniform formatting of dates, currencies, units of measure, and categorical values according to enterprise reference models.
- Missing Value Handling: Applying imputation techniques (mean, median, predictive) or exclusion rules to address incomplete records.
- Error Correction and Validation: Cross-reference checks against authoritative sources, automated anomaly detection, and rule-based correction routines.
- Data Enrichment: Augmenting records with auxiliary attributes such as geographic coordinates, NAICS codes, demographic segments, or sentiment scores.
By leveraging tools that integrate cleansing and profiling—such as AWS Glue DataBrew for interactive transformations—teams can accelerate cleaning at scale while enforcing corporate standards.
Governance, Compliance, and Metadata Management
Robust data governance frameworks codify policies and assign stewardship to ensure that all collection and cleansing activities adhere to internal and external mandates. Key governance elements include:
- Policy Definitions: Formal guidelines covering data classification, retention, access, and sharing, often documented in a governance charter.
- Role-Based Access Control: Fine-grained permissions managed via IAM, distinguishing between data stewards, engineers, and consumers.
- Metadata Cataloging: Automated lineage and provenance capture using platforms like Collibra or Immuta, facilitating impact analysis and traceability.
- Audit and Logging: Continuous recording of data access, transformations, and policy enforcement actions for regulatory audits.
- Risk Assessments: Periodic reviews to uncover compliance gaps, privacy risks, and potential breach vectors.
- Privacy Techniques: Pseudonymization, tokenization, and differential privacy applied to personally identifiable information.
Metadata repositories and data catalogs become the single source of truth, enabling business users and data professionals to discover assets, understand dependencies, and comply with governance protocols.
Stakeholder Collaboration and Alignment
Effective execution demands coordinated effort across business, IT, legal, compliance, and data science teams. Domain experts articulate use cases and define data relevance, IT provisions infrastructure and security controls, legal and compliance teams verify regulatory adherence, and data engineers design, implement, and monitor pipelines. Establishing regular forums—alignment workshops, change review boards, and RACI matrices—clarifies responsibilities, accelerates decisions, and prevents misalignment.
Cross-functional dependencies extend to DevOps and IT operations, which provision compute clusters, manage container orchestration, and monitor network configurations to support pipeline demands. Business SMEs validate feature definitions against real-world scenarios, while compliance officers verify that data usage aligns with contractual obligations and privacy commitments.
Early engagement of stakeholders reduces rework, sets clear timelines for data access, and aligns expectations for quality thresholds, governance requirements, and downstream deliverables. Transparent communication channels and shared documentation portals support ongoing collaboration throughout the AI lifecycle.
Pipeline Orchestration and Workflow
Data preparation pipelines orchestrate ingestion, transformation, enrichment, validation, and delivery through reliable, repeatable workflows. The core phases include:
- Ingestion and Extraction: Capturing data via batch ETL tools such as AWS Glue and real-time streams with Apache Kafka.
- Schema Discovery and Registration: Automated inference using sample records, with schemas registered in metastore services like Glue Data Catalog or Hive.
- Transformation and Enrichment: Declarative transformations using dbt or programmatic scripts in Apache Spark, implementing normalization, feature creation, and dataset joins.
- Orchestration and Scheduling: Workflow coordination through engines like Apache Airflow or Prefect, defining DAGs, dependency rules, retry policies, and SLA-based alerts.
- Validation and Monitoring: Embedding quality gates with frameworks such as Great Expectations, checkpoint validations, and schema tests to ensure data integrity.
- Scaling Strategies: Partitioned processing by time windows or business units, auto-scaling compute clusters, incremental change data capture, and resource quotas to maintain performance.
- Continuous Integration: Version-controlled workflows, automated testing of transformation logic, and deployment pipelines for production updates.
Error Handling and Recovery
Robust pipelines implement intelligent retry mechanisms with exponential backoff for transient failures, fallbacks to alternative data sources, and manual intervention hooks. Error events propagate to issue tracking systems, enabling prompt investigation and minimizing data downtime.
Observability and Logging
Structured logging in JSON format captures contextual details such as job identifiers, partition keys, and execution parameters. Health dashboards in Grafana or native UI panels provide real-time insights, while automated alerts inform on-call engineers of anomalies, failures, or SLA breaches.
These practices deliver a robust platform for data flow, enabling rapid detection and resolution of operational issues and facilitating capacity planning as workloads evolve.
AI-Driven Validation and Model Conditioning
Integrating AI-driven validation and conditioning into data pipelines transforms static checks into adaptive, intelligent processes that scale with data volume and complexity. Key capabilities include:
Automated Data Quality Monitoring
Continuous evaluation against predefined rules and metrics prevents corrupted or misaligned records from propagating. Schema enforcement tools, such as TensorFlow Data Validation and Great Expectations, verify field types, value ranges, and cross-field consistency. Semantic validation leverages natural language services like Azure Text Analytics to ensure categorical labels and text fields align with controlled vocabularies.
Anomaly Detection and Alerting
Real-time anomaly detectors identify distributional shifts, time-series outliers, and multivariate deviations. Statistical profiling with frameworks such as PyCaret Anomaly Detection, time-series monitoring via Amazon Lookout for Metrics or Azure Anomaly Detector, and multivariate techniques using scikit-learn alert teams to unexpected patterns. Integration with messaging platforms and incident management systems ensures rapid notification and resolution.
Model Conditioning and Continuous Tuning
Maintaining model performance requires automated hyperparameter optimization, drift detection, and calibration. Services like Amazon SageMaker Automatic Model Tuning and Google Vertex AI Hyperparameter Tuning accelerate parameter search. Concept drift monitoring using MLflow or Kubeflow Pipelines triggers retraining pipelines when live data diverges from training baselines. Calibration techniques such as Platt scaling are managed through the Databricks MLflow Model Registry, ensuring reliable probability estimates for decision thresholds.
CI/CD and Feedback Loops
End-to-end MLOps workflows, orchestrated with Prefect and CircleCI, integrate validation gates, automated testing, and containerized deployments. Event-driven pipelines leverage Apache Kafka or AWS EventBridge to channel validation failures into remediation functions or retraining triggers. Real-time dashboards deliver visibility into quality metrics, anomaly trends, and conditioning outcomes, ensuring continuous alignment between data and AI agents.
Data Outputs, Documentation, and Handoff Criteria
The culmination of data strategy, preparation, and validation yields a suite of artifacts ready for agent design and configuration. Rich metadata and well-documented transformation logic enable agent architects to understand feature semantics, data freshness, and potential biases before integrating inputs into design sprints. These outputs include:
- Curated Training and Validation Datasets: Labeled examples, feature vectors, and partitioned sets in Parquet, CSV, or JSON formats, verified against completeness and balance metrics.
- Feature Store Exports: Versioned feature tables with timestamped snapshots and lineage metadata, orchestrated through Apache Airflow and Databricks.
- Transformed Data Tables: Derived attributes, anonymized keys, one-hot encodings, and aggregated metrics maintained by Alteryx and Fivetran.
- Unstructured Data Artifacts: Tokenized text corpora, annotated image datasets in COCO or Pascal VOC formats, and enriched audio transcripts stored in document databases or object stores such as Snowflake.
- Metadata Catalog Entries: Detailed descriptions of each dataset, schema references, update frequencies, and owner contacts.
- Lineage Graphs and Quality Reports: Machine-readable and visual representations linking raw sources to final outputs, annotated with data quality metrics and anomaly statistics.
- Governance Certificates: Documentation of policy enforcement, masking procedures, consent records, and audit logs generated by Collibra or Immuta.
- Validation and Drift Logs: Time-stamped records of anomaly detections, drift events, and retraining triggers with rationale and resolution actions.
- Connectivity and Security Credentials: Service endpoints, API tokens, and access policies configured for downstream use.
- Transformation Scripts and Playbooks: Version-controlled code artifacts—including Python notebooks, SQL scripts, and orchestration DAGs—documenting pipeline logic and error-handling mechanisms.
- Stakeholder Sign-Off: Formal approvals from data stewards, compliance officers, and business sponsors confirming readiness for agent development.
Best Practices for Seamless Handoffs and Continuous Improvement
- Implement Version Control for Data and Code: Treat datasets, transformation scripts, and metadata as code, using Git or specialized versioning systems to track changes and roll back when necessary.
- Automate Documentation Generation: Use tools that extract schema definitions and data profiles to produce up-to-date documentation, reducing manual effort and errors.
- Establish Regular Synchronization Cadences: Schedule recurring meetings between data engineers, compliance teams, and agent designers to review output readiness, clarify requirements, and gather feedback.
- Define Clear SLAs and RTO/RPO Targets: Agree on service-level objectives for data availability, freshness, recovery objectives, and escalation paths to manage pipeline incidents.
- Centralize Artifact Storage and Discovery: Utilize a shared repository or data catalog platform as the single source of truth, providing controlled access and search capabilities across teams.
- Enforce Metadata Validation Rules: Implement automated checks to verify that required fields, descriptions, and classification tags are present before handoff.
- Provide Incremental Deliverables and Previews: Share data samples, lineage snapshots, and draft documentation early to solicit stakeholder input and avoid last-minute revisions.
- Conduct Post-Handoff Retrospectives: Gather teams to review what worked, what didn’t, and incorporate lessons learned into updated processes and playbooks.
By institutionalizing these practices, organizations foster a culture of continuous improvement and operational excellence. Data pipelines evolve proactively to accommodate new sources, emerging compliance requirements, and shifting business objectives, ensuring that AI agents remain tuned to organizational goals.
Chapter 3: Agent Design and Configuration
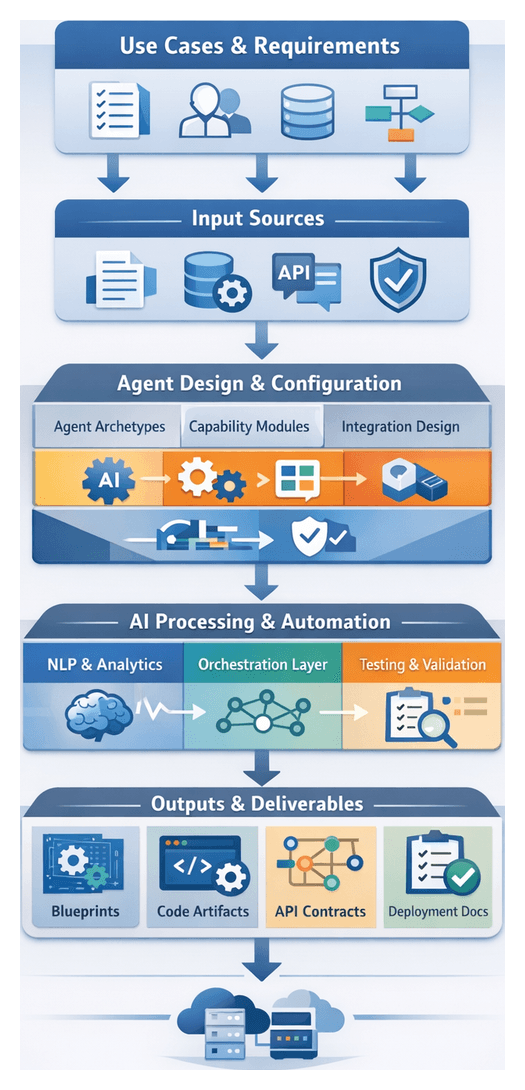
The Agent Design and Configuration stage bridges high-level use case definitions and the technical realization of AI agents within enterprise workflows. By translating strategic objectives into concrete agent archetypes, capability modules, and integration blueprints, this discipline ensures each agent delivers measurable value, aligns with organizational standards, and supports scalable deployment across diverse scenarios.
In complex environments, ad hoc development often leads to inconsistent results, costly rework, and low adoption. A structured design process enforces repeatable methodologies, fosters cross-functional collaboration, and promotes reuse of proven components. The outputs from this stage—blueprints, configuration manifests, and semantic documentation—lay the foundation for efficient platform provisioning, integration, and orchestration.
Key Objectives
- Define agent archetypes mapped to organizational roles and process patterns.
- Specify functional modules, AI capabilities, data schema mappings, and performance targets.
- Document integration points, API contracts, and human workflow escalations.
- Validate design assumptions against technical, operational, and compliance constraints.
Strategic Advantages
- Rapid onboarding of new use cases via standardized agent blueprints.
- Efficient collaboration and transparency with shared configuration artifacts.
- Continuous compliance and security validation through documented design reviews.
- Optimized total cost of ownership by reusing modular components.
- Traceability from business requirements to agent behavior.
Inputs and Prerequisites
- Use Case Definitions and Prioritization: Descriptions with success criteria guide archetype selection and feature sets.
- Stakeholder Requirements and Role Profiles: Interviews, workshops, and personas inform decision logic and escalation paths.
- Data Availability and Quality Assessments: Source systems, schemas, and readiness reports shape knowledge management and NLP modules.
- Process Maps and Integration Inventories: Flow diagrams and API catalogs capture triggers, transformation rules, and error-handling protocols.
- Technology Stack and Constraints: Infrastructure, middleware, and AI framework specifications determine compatibility requirements.
- Governance, Security, and Compliance Policies: Regulatory mandates and audit requirements establish design guardrails.
- Performance Targets and SLAs: Benchmarks for response times, throughput, and error rates drive tuning parameters and operational support agreements.
Environmental Conditions
- Cross-functional governance councils and working groups.
- Version control and change management processes in GitHub, GitLab, or Bitbucket.
- Accessible test and staging environments for safe validation.
- Tooling for modular development using IDEs, low-code platforms, or container frameworks.
- Training and knowledge transfer sessions leveraging Confluence and Microsoft Teams.
Handoff Criteria
- Completion of configuration blueprints with archetype definitions and module mappings.
- Approval of integration design documents including API contracts, event schemas, and data transformations.
- Validation of compliance matrices demonstrating security and regulatory alignment.
- Established test plans and acceptance criteria for performance and functionality.
- Agreement on deployment timelines, resource allocations, and cut-over strategies with operations teams.
With these prerequisites and criteria satisfied, subsequent deployment and orchestration stages proceed with clarity and minimal rework, accelerating time to value while mitigating risk.
Modular Design Workflow for Agent Setup
Building on agent archetypes and configuration inputs, the modular design workflow assembles reusable capability components into cohesive AI agent configurations. This structured process supports scalability, maintainability, and rapid iteration, guiding teams from module ideation through development, validation, and handoff for deployment.
Stage Inputs and Triggers
- Approved blueprints outlining required capabilities and interface contracts.
- Reference architectures specifying module roles and data flows.
- Prioritized scenarios and user stories.
- Provisioned environments with version control and collaboration tools.
Module Identification and Cataloging
- Function Mapping: Decompose blueprints into discrete capabilities such as intent recognition, dialogue management, data retrieval, decision logic, and external integration.
- Module Definition: Document inputs, outputs, APIs, performance SLAs, and security requirements for each capability.
- Catalog Registration: Record module metadata, version information, dependencies, and configuration parameters in a centralized registry.
- Dependency Analysis: Map shared libraries, data schemas, and service endpoints to inform integration sequencing.
Module Development and Configuration
- Specification Refinement in collaboration with business analysts.
- Implementation using OpenAI API for generative language, Microsoft Bot Framework for conversation flows, or IBM Watson Assistant knowledge connectors.
- Configuration Management via infrastructure-as-code templates and environment-specific settings.
- Unit Testing with automated suites to validate functional correctness.
- Peer Review through pull requests in GitHub, GitLab, or Bitbucket.
Orchestration Layer Integration
- Module Registration with service registries and messaging topics on Apache Kafka or RabbitMQ.
- Interface Binding using tools like those listed on AgentLinkAI or LangChain.
- Configuration Propagation of secrets and connection strings via secret management services.
- Smoke Testing to verify runtime module invocation and data bindings.
Human-in-the-Loop Collaboration
- Design Workshops with cross-functional teams.
- SME Reviews for domain-specific logic.
- UX Testing with prototype agents to refine conversational flows.
- Change Management Boards coordinating releases and preventing update conflicts.
Automated Testing and Validation
- Unit Tests triggered on commits.
- Integration Tests simulating module interactions.
- Load and Stress Tests identifying performance bottlenecks.
- Security Scans with Snyk or SonarQube.
- Acceptance Testing against business-driven criteria.
Security and Compliance Checks
- Static Code Analysis for insecure patterns.
- Dependency Audits for known vulnerabilities.
- Configuration Validation of encryption, token policies, and secure protocols.
- Audit Logging of access events and data transformations.
- Policy Enforcement gating promotions until issues are resolved.
Documentation and Handoffs
- Versioned module packages or container images in artifact repositories.
- Published API specifications and event schemas.
- Configuration templates and environment variable manifests.
- Operational runbooks detailing deployment steps, health checks, and rollback procedures.
- Metadata capturing authorship, version history, dependencies, and compliance attestations.
Clear coordination across design leads, development, DevOps, security, QA, and documentation teams ensures that modules are reliable, interoperable, and ready for integration into complex multi-agent orchestrations.
AI Capabilities Mapping to Agent Roles
Mapping core AI functions to agent archetypes creates a flexible ecosystem in which each component contributes distinct value. By aligning capabilities such as language understanding, knowledge retrieval, decision intelligence, and contextual memory with modular roles, organizations can build scalable, coherent workflows.
Natural Language Processing and Understanding
NLP and NLU enable agents to parse unstructured text, recognize intents, extract entities, and manage dialogues. Transformer-based models from OpenAI GPT or pipelines built with spaCy support sentiment analysis and multi-turn conversation management. Continuous training pipelines using TensorFlow or PyTorch ensure models evolve with new terminology and user behavior.
Knowledge Management and Retrieval
Retrieval-augmented generation (RAG) patterns combine generative models with vector databases like Pinecone to surface relevant content from internal documentation or external sources. Graph databases model entity relationships and automated curation workflows leveraging Prefect maintain accuracy and freshness of knowledge repositories.
Decision Intelligence and Optimization
Agents apply predictive analytics, optimization algorithms, and reinforcement learning to recommend actions or forecast outcomes. Tools such as OptaPlanner or custom Python pipelines handle scheduling, inventory planning, and dynamic pricing. Integration with real-time streams on Kafka enables live model updates and automated triggers via workflow engines.
Contextual Awareness and Memory Systems
Memory architectures combine session stores in Redis for short-term context with long-term archives in vector or relational stores. Policies for context window management and periodic pruning ensure coherent dialogues without performance decay, supporting roles from transactional assistants to compliance monitors.
Integration with Supporting Platforms and Services
Agents rely on container orchestration in Kubernetes and Docker, messaging layers like RabbitMQ or Kafka, and API gateways managing authentication, rate limits, and versioning. CI/CD pipelines in Jenkins, GitHub Actions, or GitLab CI automate testing, security scans, and model rollouts.
Security and Compliance Integration
Role-based access controls, audit logging, and encryption standards (AES-256, TLS 1.2 ) safeguard sensitive data. Secrets stored in HashiCorp Vault and policy engines enforce corporate and regulatory mandates. Privacy controls anonymize or redact PII to comply with GDPR and CCPA.
Performance, Scalability, and Maintainability
Monitoring frameworks like Prometheus and Grafana track inference latency and resource utilization. Model versioning with metadata enables safe rollbacks and A/B tests. Autoscaling policies for CPU, GPU, and memory usage ensure elastic performance, while canary deployments verify new releases under real-world conditions. Observability pipelines correlate logs, metrics, and traces to diagnose distributed issues.
This systematic mapping of AI capabilities to agent roles, supported by robust platforms and governance frameworks, establishes a resilient foundation for enterprise-wide agent deployments.
Configured Output Artifacts and Integration Handoffs
The culmination of agent design yields a comprehensive set of artifacts that describe each AI agent’s capabilities, interfaces, and operational parameters. Formal handoff procedures ensure integration and deployment teams receive all necessary context and dependencies to proceed efficiently.
- Agent Blueprints and Configuration Manifests including YAML or JSON templates, metadata annotations, and references to reusable libraries or container images.
- Capability Modules and Code Artifacts comprising source code repositories, unit test suites, and references to frameworks such as OpenAI APIs and Vertex AI.
- Interface Specifications and API Contracts with OpenAPI definitions, GraphQL or event schemas, and sequence diagrams.
- Test Cases and Validation Scripts covering integration scenarios, automated tests for Jenkins or GitLab CI, and performance benchmarks.
- Operational Runbooks detailing deployment steps, secret management, monitoring configurations, and troubleshooting procedures.
- Security, Compliance, and Governance Documentation specifying RBAC policies, encryption guidelines, and audit trail requirements.
Key Dependencies
- Data Model Availability including canonical schemas, ontologies, and sanitized datasets.
- Infrastructure Prerequisites such as container registry endpoints, Kubernetes namespaces, and service mesh configurations.
- Integration Endpoint Definitions covering API gateways, message broker topics, and authentication mechanisms.
- Security and Compliance Constraints involving key management services, data residency regulations, and certificate authorities.
- Stakeholder Sign-Off by business, legal, and compliance owners on acceptance criteria and audit requirements.
Integration Handoff Workflow
- Packaging and Versioning: Tag manifests, code repositories, and container images; publish artifacts to internal registries.
- Documentation Bundle: Compile blueprints, interface contracts, runbooks, and test suites; include a dependency matrix and issue log.
- Stakeholder Review and Approval: Conduct technical walkthroughs with infrastructure engineers; obtain sign-off via Jira tickets.
- Transition to Integration: Create deployment tickets referencing artifact versions and target environments; hand over credentials via HashiCorp Vault.
- Post-Handoff Validation: Execute smoke tests in staging; document deviations and assign action items to the design team.
By maintaining clear dependencies and following a structured handoff process, organizations minimize misconfiguration risk, align multidisciplinary teams, and accelerate time to market for AI agent solutions.
Chapter 4: Infrastructure and Platform Setup
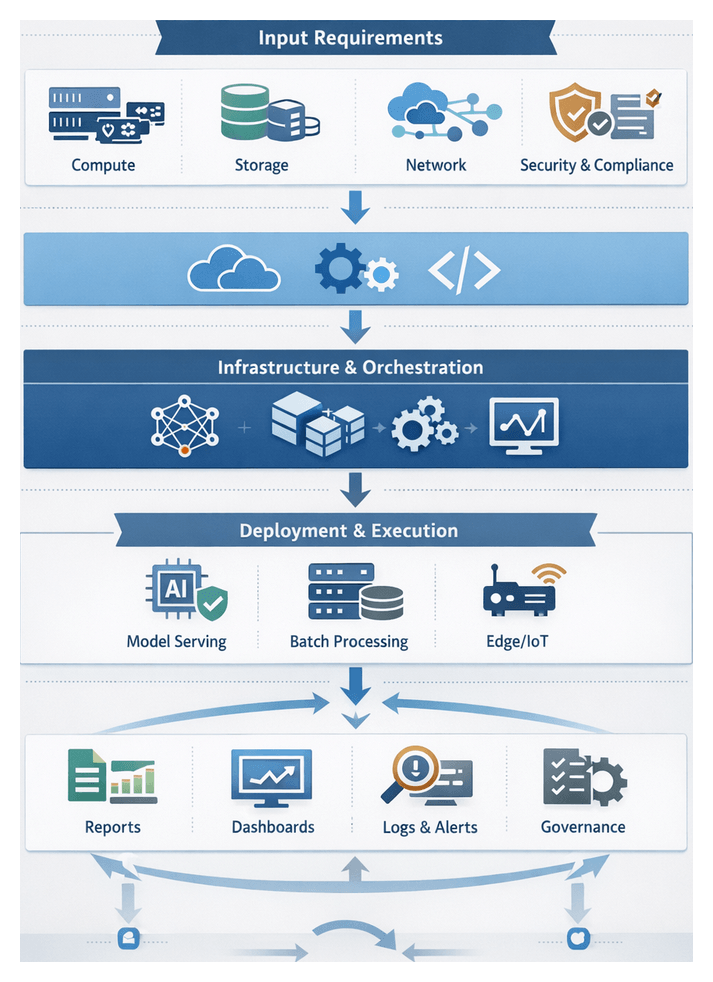
Defining the Purpose of the Infrastructure Requirements Stage
This stage establishes the foundational environment and platform to host, orchestrate, and scale AI agent workflows. It aligns compute, storage, network, security, and compliance specifications with enterprise objectives for performance, availability, and cost efficiency. By defining clear input requirements and preconditions, teams can provision infrastructure that supports rapid deployment, consistent operations, and seamless integration with existing systems.
Enterprises face challenges such as heterogeneous environments, unpredictable workloads, and evolving security mandates. Modern solutions leverage cloud-native architectures, container orchestration platforms, and infrastructure as code to accelerate time to value while maintaining governance. In hybrid or multi-cloud landscapes, a documented set of requirements creates a repeatable, auditable process that supports both agile experimentation and mission-critical production workloads.
Prerequisites and Core Input Specifications
Before provisioning, teams must align stakeholders on objectives, assemble resource inventories, and define organizational policies. The following domains outline the essential inputs for a robust infrastructure environment.
Compute and Scalability Requirements
- Workload profiling: expected CPU, GPU, memory, and I/O characteristics of training or inference tasks
- VM or container sizing guidelines for baseline and peak demands
- Deployment model: cloud instances (Amazon Web Services, Azure, Google Cloud Platform) versus on-premises virtualization
- Container orchestration with Kubernetes or Docker Swarm
- Auto-scaling policies and thresholds to accommodate dynamic workload fluctuations
Storage and Data Management Inputs
- Data volume estimates and growth projections for training datasets, model artifacts, and logs
- Performance requirements for block, object, and shared file systems
- Integration with managed services such as Amazon S3, Azure Blob Storage, or Google Cloud Storage
- Backup, snapshot, and archival policies aligned with RTO and RPO objectives
- Data locality considerations to minimize latency for geo-distributed agent interactions
Networking and Connectivity Conditions
- Design of virtual networks, subnets, and IP schemes to isolate AI traffic
- Firewall rules, security groups, and load balancer specifications for ingress and egress control
- Network peering, VPN tunnels, or dedicated links (Direct Connect, ExpressRoute) for secure communication
- Service mesh or API gateway patterns to manage microservices-level traffic
- Bandwidth and latency targets for real-time agent coordination across regions
Security, Identity, and Access Control Inputs
- Role-based access control definitions in Kubernetes or cloud IAM services
- Encryption standards for data at rest and in transit using TLS, VPN, or managed keys
- Integration with secrets management solutions such as HashiCorp Vault
- Network security controls, including intrusion detection and vulnerability scanning
- Audit logging and monitoring prerequisites to support compliance frameworks
Platform Provisioning and Orchestration Tools
- Infrastructure as code: Terraform, AWS CloudFormation, Azure Resource Manager
- Configuration management: Ansible, Chef, Puppet
- Container image build and registry tools: Docker and Harbor
- CI/CD pipelines with Jenkins, GitLab CI/CD, or Azure DevOps
- Artifact repositories for model and code versioning aligned with DevOps practices
Monitoring, Logging, and Observability Inputs
- Metrics collection frameworks: Prometheus or cloud monitoring services
- Visualization and dashboards: Grafana or native cloud consoles
- Log aggregation and search: Elastic Stack or Splunk
- Distributed tracing and application performance monitoring
- Alerting thresholds and notification channels for incident response
Compliance, Governance, and Cost Management
- Regulatory standards such as GDPR, HIPAA, PCI DSS, or SOC 2
- Policy definitions for data retention, audit trails, and change management
- Budget allocations, reserved instances, and spot instance strategies
- Tagging schemas to track cost by project, environment, and business unit
- Integration with governance platforms or GRC tools to track controls and exceptions
Platform Provisioning and Orchestration Workflow
An effective provisioning workflow translates architecture into a live runtime environment by coordinating cloud APIs, orchestration frameworks, and automation tools. Leveraging IaC, containerization, and CI/CD, organizations deploy consistent, repeatable platforms that support continuous integration and continuous deployment of AI agents.
Provisioning Strategy and Planning
- Capacity planning based on expected AI training, inference, and batch workloads
- Environment taxonomy with naming conventions, resource groupings, and tags
- Cost optimization through appropriate service tiers and scaling policies
- Security baseline defining network segmentation, access controls, and encryption
- Tool selection such as Terraform, AWS CloudFormation, Kubernetes, or Docker Swarm
Infrastructure as Code and Environment Definition
- Declarative templates for networks, compute clusters, storage volumes, and load balancers
- Parameterization of variables like region, instance size, and environment type
- Validation through static analysis or dry runs to detect errors and policy violations
- Version control and pull requests for peer review and rollback capabilities
Containerization and Image Management
- Base image selection or specialized data science images
- Dockerfile authoring with multi-stage builds to minimize image size and attack surface
- Image scanning via Clair or Trivy to detect vulnerabilities
- Registry management in Amazon ECR or Google Container Registry with lifecycle policies
- Semantic tagging for precise rollbacks and audits
Orchestration and Deployment Pipelines
- Pipeline definitions in Jenkins, GitLab CI/CD, or Azure DevOps sequencing IaC and container steps
- Environment promotion with automated tests, linting, and security checks
- Helm chart management for Kubernetes releases, ingress, and secrets
- Blue/green and canary deployments to mitigate risk and enable rapid rollback
- Dependency orchestration ensuring services like databases, queues, and agents deploy in order
Coordination, Error Handling, and Resilience
- Human approvals via ticketing or chat integrations before critical changes
- Event-driven triggers using webhooks to initiate downstream workflows
- Service mesh integration with Istio or Linkerd for secure mTLS and traffic policies
- Automated rollback and retry logic for idempotent operations
- Health checks and readiness probes to validate service functionality
- Alerting to incident management tools for on-call notifications
AI Service Deployment and System Roles
Deployment bridges model development and operational value delivery by orchestrating trained models and agents into production environments. A robust strategy ensures reliability, security, and maintainability while integrating with broader IT systems.
Deployment Models
- Real-Time Inference for chatbots and recommendation engines using containerized endpoints on Kubernetes
- Batch Processing with solutions like AWS SageMaker Batch Transform or MLflow pipelines for bulk predictions
- Edge and IoT Deployment via containerized models on local hardware using Azure Machine Learning
Core System Roles
- Control Plane: Manages scheduling, configuration updates, and policy enforcement in Kubernetes
- Data Plane: Runs inference workloads on nodes with GPU or CPU clusters via device plugins
- Service Mesh: Uses Istio or Linkerd sidecars for load balancing, traffic routing, and observability
- Monitoring and Logging: Collects metrics with Prometheus and logs with Fluentd or Elastic Stack
- Security Enforcement: Applies RBAC, vulnerability scanning, and audit logging integrated with identity providers
CI/CD for AI Services
- Automated testing: unit, integration, and performance tests to validate service logic and SLOs
- Artifact management: model registries like MLflow Model Registry or TensorFlow Extended
- Deployment strategies: blue/green and canary rollouts via sidecar proxies
Scaling, Resiliency, and Observability
- Horizontal Pod Autoscaling based on CPU or custom metrics
- Cluster autoscaling with cloud provider APIs to add nodes when needed
- Scheduling GPUs, TPUs, or FPGAs via device plugins for specialized workloads
- Liveness and readiness probes to restart unhealthy containers
- Replication and failover for stateless and stateful components
- Persistent volumes and object storage for data consistency
- Metrics: inference latency, throughput, error rates
- Logs: request traces and exception records
- Distributed tracing: end-to-end request tracking across services
Governance and Collaboration
- Role-based access controls integrated with identity providers
- TLS encryption in transit and at rest, with secrets stored in vault services
- Immutable audit trails recording deployment events and access requests
- Cross-functional interfaces between DevOps, data science, and IT operations
- ChatOps notifications and shared dashboards for real-time collaboration
Deployed Platform Outputs, Dependencies, and Handoff
The final stage produces operational artifacts, configuration outputs, and a dependency matrix that downstream teams use for integration. Formalized handoff processes ensure all requirements are met before application usage.
Key Operational Artifacts
- Service endpoint definitions: FQDNs, load balancer addresses, and port mappings
- Configuration manifests: YAML or JSON descriptors with environment variables
- Infrastructure as code artifacts: Terraform state files and CloudFormation stacks
- Container images: tagged Docker images and vulnerability scan reports
- Monitoring dashboards: preconfigured Grafana or Datadog views and alert definitions
- Logging configurations: centralized forwarding to Elastic Stack or OpenSearch
- Security credentials: TLS certificates and OAuth2 client registrations
- Model registry entries: artifacts in MLflow with version metadata and lineage
Dependency Matrix
- Network: VPC peering, firewall rules, DNS zones, and service discovery
- IAM: RBAC entries for Kubernetes or cloud IAM policies
- Storage: object buckets and database connections for model binaries and logs
- Orchestration: compatibility with Kubeflow or Argo Workflows and CRDs
- Monitoring: webhook endpoints for PagerDuty or ServiceNow and API tokens
- Security: vault configurations and audit log destinations
- Model lifecycle: CI pipelines triggering retraining and redeployment workflows
Handoff Process
- Artifact Packaging: publish manifests, scripts, and templates to version control with semantic tags and generate a release bundle
- Dependency Verification: provide a matrix showing each dependency’s status and remediation steps
- Integration Playbooks: deliver runbooks with API examples, authentication flows, and error-handling scenarios
- Stakeholder Sign-Off: host review sessions with infrastructure, security, and integration leads and record approvals
- Automated Gates: promote artifacts into integration environments via CD pipelines and execute smoke tests
Best Practices for Smooth Transition
- Version Control Discipline: maintain strict branching and tagging for code and configuration artifacts
- Automated Validation: run connectivity, authentication, and schema compliance tests before integration
- Cross-Functional Communication: schedule regular syncs between platform engineers, security officers, and developers
- Dynamic Documentation: host runbooks and playbooks in collaborative platforms that update automatically
- Monitoring Readiness Checks: define SLIs and health checks to guard against upstream failures
By capturing deployed outputs in consistent formats, proactively managing dependencies, and formalizing handoff procedures, organizations transform complex provisioning into a transparent, repeatable process. This rigor accelerates integration and establishes the trust required for scaling AI agent workflows across the enterprise.
Chapter 5: Integration with Core Enterprise Systems
Integration Requirements and System Inputs
Successful AI-driven workflows begin with a detailed definition of integration requirements and system inputs. Technical teams, business stakeholders, and security architects must collaborate to inventory enterprise systems, define interface specifications, and establish data contracts. This upfront effort ensures AI agents interact reliably with mission-critical platforms such as Salesforce, SAP, Microsoft Dynamics 365, Workday, and ServiceNow without causing data inconsistencies or process bottlenecks.
- System Landscape Inventory: A centralized register of application names, versions, endpoints, hosting environments, and support SLAs. This serves as the single source of truth for API access coordination and change management.
- Interface and API Specifications: Machine-readable definitions of REST, SOAP, gRPC, and event-stream endpoints, including payload schemas, authentication schemes, rate limits, and error codes. Tools such as MuleSoft and Dell Boomi can publish OpenAPI or WSDL contracts to accelerate connector development.
- Data Model Alignments: Canonical schemas, entity mappings, data dictionaries, and master data attributes. Early collaboration with data architects and use of metadata repositories or MDM platforms ensures consistent transformations.
- Authentication and Authorization: Definitions of OAuth 2.0 flows, SAML assertions, API key policies, and certificate-based schemes, along with token lifecycles and role-based access controls. Security teams enforce least-privilege principles.
- Network and Infrastructure Prerequisites: VPN configurations, VPC peering, firewall rules, proxy settings, and bandwidth capacity. Secure connectors or on-premise agents bridge gap-to-cloud scenarios without exposing internal networks.
- Integration Patterns: Preferred approaches such as synchronous REST calls, event-driven messaging via Apache Kafka or RabbitMQ, batch file transfers, or webhooks. Pattern selection impacts latency, throughput, and resilience.
- Data Exchange Formats: Standardized formats like JSON, XML, Avro, or CSV, with agreed serialization settings, compression, and encryption. Versioning policies prevent schema drift.
- Performance and SLA Metrics: Throughput targets, latency thresholds, concurrency limits, and retry policies. These metrics drive capacity planning and connector tuning.
- Compliance and Audit Inputs: Requirements from GDPR, HIPAA, SOX, or industry mandates, including data residency, consent management, audit logging, and encryption standards.
- Stakeholder Alignment: Business objectives, process owners, escalation paths, and support models. Early agreement on use case scope and acceptance criteria ensures integration efforts deliver intended value.
By rigorously gathering these prerequisites, organizations establish a structured framework that enables AI agents to operate securely and efficiently across diverse enterprise systems. The next stage implements these inputs through API-driven connections and data flows.
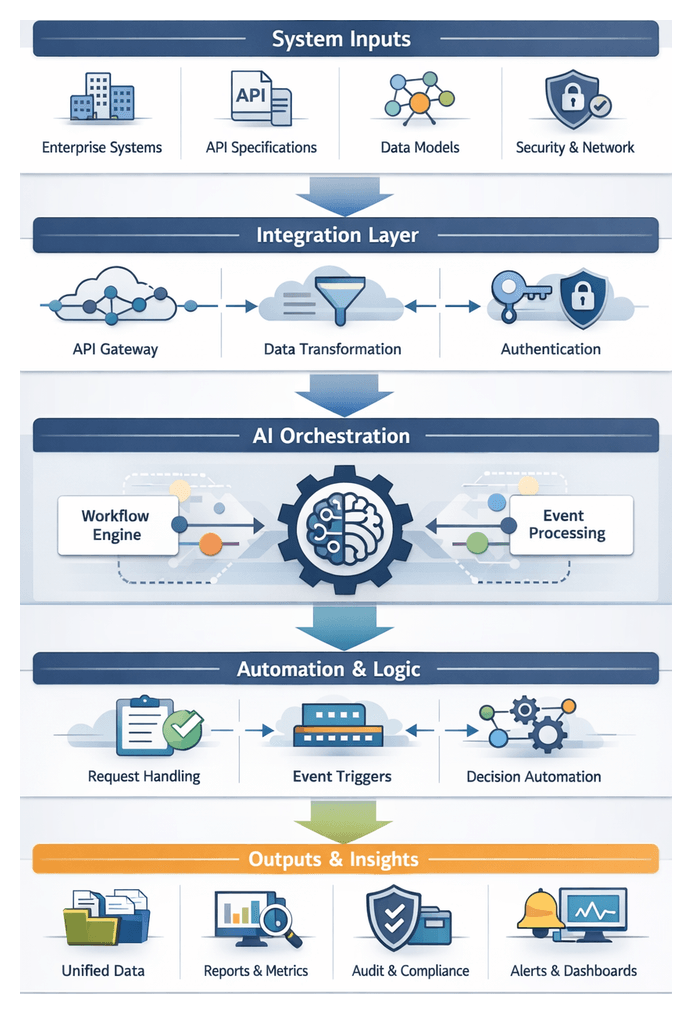
API-Driven Connection and Data Flows
The API-driven stage orchestrates real-time or near-real-time exchanges between AI agents and enterprise applications. An architectural stack typically comprises an AI orchestration layer, an API gateway or management platform, enterprise system endpoints, and message buses or transformation services. Together, these components ensure secure, resilient, and observable data flows.
Gateway Configuration and Routing
Platforms such as AWS API Gateway, Azure API Management, MuleSoft, and Oracle Integration Cloud centralize:
- Route mappings from logical API paths to backend endpoints.
- Rate limiting, throttling, and caching policies.
- Payload transformations to align request and response schemas.
- Authentication enforcement via OAuth 2.0, JWT, or mutual TLS.
- Versioning strategies to support backward compatibility.
Secure Authentication Handshakes
AI agents acquire tokens through OAuth 2.0 client credentials grants or OpenID Connect flows. Processes include:
- Service registration with identity providers to obtain client IDs and secrets.
- Token acquisition, introspection, and automated refresh logic.
- Secret management via vaults such as HashiCorp Vault or AWS Secrets Manager.
Request-Driven and Event-Driven Interactions
Workflows leverage both paradigms:
- Retrieving customer data before generating personalized correspondence.
- Querying inventory levels for order fulfillment decisions.
- Submitting transactions to ERP systems and confirming responses.
- CRM emits a lead-scored event consumed by a lead-routing agent.
- ERP publishes an order-shipped event triggering stakeholder notifications.
- HRIS signals an onboarding event starting document generation and training tasks.
Serialization, Validation, and Transformation
Payloads undergo:
- Format conversion between JSON, XML, Avro, or Protobuf.
- Schema validation against JSON Schema or XSD definitions.
- Field mappings, default values, and lookup enrichments via transformation templates.
- Addition of metadata such as timestamps, correlation IDs, or agent identifiers.
Coordination and State Management
Maintaining workflow context and preventing race conditions relies on:
- Correlation IDs passed in headers for end-to-end tracing.
- Distributed caches or stateful services for short-lived state.
- Distributed locks for single-threaded updates to shared resources.
- Callback endpoints for asynchronous responses or error notifications.
- Fan-in and fan-out patterns to aggregate parallel results.
Resilience and Error Handling
Robust patterns include:
- Exponential backoff retries for idempotent operations.
- Circuit breakers to isolate unhealthy endpoints and invoke fallback logic.
- Dead-letter queues for messages exceeding retry limits.
- Compensation transactions to roll back partial failures.
- Automated alerts to DevOps via integrated monitoring platforms.
Scalability and Observability
To meet enterprise demands, implement:
- Horizontal scaling behind load balancers and auto-scaling rules.
- Connection pooling and HTTP/2 multiplexing.
- Local caching within agents for repeatable lookups.
- Priority queues and throttling for critical transactions.
Observability is achieved through:
- Distributed tracing with OpenTelemetry or AWS X-Ray.
- Centralized logs in Splunk or Datadog (with PII redaction).
- Real-time dashboards for throughput, latency, and error rates.
- Health checks and synthetic transactions for end-to-end validation.
The API-driven layer transforms isolated agent tasks into secure, scalable, and observable processes that prepare data for unified operations.
AI Agents’ Role in Unifying Operations
AI agents unify fragmented processes by embedding intelligent services at key workflow junctures. They eliminate manual handoffs, reduce latency, and maintain end-to-end visibility across CRM, ERP, HRIS, and collaboration platforms. Integration relies on API gateways, event buses, and low-code orchestration tools to expose data and services securely.
- Service Abstraction: Agents invoke APIs via management platforms such as MuleSoft and IBM Cloud Pak for Integration, ensuring policy enforcement and governance.
- Event Streaming: Message brokers like Apache Kafka or Confluent enable real-time event subscriptions and enriched event publication.
- Low-Code Orchestration: Citizen developers configure triggers and actions in Microsoft Power Automate and Zapier, integrating AI agents for tasks like sentiment analysis or document summarization.
Automating Decision Points
AI agents accelerate decision nodes by combining:
- Data aggregation from CRM, ERP, and knowledge bases with predictive scoring or risk assessments.
- Model inference via serving frameworks such as TensorFlow Serving or custom microservices.
- Business rules engines for policy evaluations.
- Human-in-the-loop workflows through collaboration APIs in Slack or Microsoft Teams for high-risk cases.
Coordination Between Tools and Human Participants
Orchestrated workflows blend automated and manual tasks through:
- Task Assignment: Agents evaluate skills, workloads, and SLAs to route tasks to the right personnel.
- Notifications: Context-aware alerts via communication APIs keep users informed and prompt actions.
- Progress Tracking: Dashboards aggregate status updates, triggering escalations on exceptions or delays.
Supporting Infrastructure
- Orchestration Engines: Container platforms like Kubernetes host agents, while workflow engines such as AWS Step Functions and Apache Airflow define execution graphs.
- Model Serving and Feature Stores: Microservices expose inference endpoints and maintain versioned feature artifacts.
- Monitoring and Observability: Telemetry pipelines use Prometheus and Grafana, with AI-driven anomaly detection surfacing performance deviations.
- Data Governance: Metadata management systems enforce lineage, access controls, and retention, with audit frameworks capturing every agent interaction.
Use Cases and Impact Measurement
- Invoice Processing: OCR agents extract line items, validate vendors, and trigger approval workflows, routing exceptions to specialists.
- Customer Onboarding: Virtual assistants verify identities, provision accounts in CRM and billing systems, and flag negative sentiment for human outreach.
- IT Incident Management: Monitoring agents detect anomalies, classify severity, create tickets in service platforms, and suggest resolutions from knowledge-base agents.
Key performance indicators include reduced handoff times, lower error rates, faster cycle times, and improved user satisfaction. Telemetry feeds analytics platforms, guiding model retraining and orchestration refinements for continuous improvement.
Synced Data Outputs and Handoff Mechanisms
Upon completing integration and orchestration, the system produces synchronized artifacts and defines structured handoff strategies to downstream layers such as workflow orchestration, monitoring, and governance.
Consolidated Integration Artifacts
- Unified Customer Profiles combining records from Salesforce and other sources.
- Normalized Order Fulfillment Streams from SAP or Oracle ERP Cloud.
- Employee Activity Logs from Workday or SuccessFactors.
- Event-Driven Messages formatted as JSON or Avro and published to Apache Kafka topics.
- Integration Audit Reports capturing API calls, transformations, and errors.
Synchronization Preconditions and Dependencies
- API availability, versioning, and adherence to SLAs.
- Validated authentication tokens and certificates managed by MuleSoft or Workato.
- Schema alignment through canonical data models.
- Secure network configurations, TLS channels, and firewall rules.
- Automated data quality checks to verify completeness and consistency.
Output Packaging and Version Control
- Semantic versioning of schemas, scripts, and connectors for rollback and parallel deployments.
- Immutable data snapshots for audits and recovery.
- Git-backed storage of transformation logic and API contracts.
- Containerized delivery via Docker images for consistent CI/CD pipelines.
Handoff Interfaces
- Event triggers on message buses signaling workflow engines like Apache Airflow or Prefect.
- RESTful endpoints that orchestration layers invoke to retrieve consolidated data.
- Webhooks notifying orchestrators upon completion of synchronization tasks.
- Shared repositories in cloud storage with version tags for consistent reads.
Metrics for Monitoring and Analytics
- Throughput metrics, API response times, and end-to-end latency.
- Error and exception reports categorized by severity.
- Data quality summaries on missing fields and schema mismatches.
- Resource utilization logs for capacity planning.
These outputs feed into platforms such as Splunk and Datadog, where AI-driven anomaly detection ensures rapid issue detection.
Security and Compliance Deliverables
- Access control matrices mapping service accounts and roles.
- Encryption verification logs confirming AES-256 or TLS 1.2 compliance.
- Immutable audit trails of every transaction.
- Compliance certificates aligned to GDPR, HIPAA, or SOX frameworks.
Continuous Feedback and Iteration
- Change request logs for reported anomalies or enhancements.
- Performance benchmarks and trending indicators.
- Health dashboards showing service uptime and SLA adherence.
- Versioned documentation in shared knowledge bases.
Best Practices for Seamless Handoffs
- Standardize on interchange formats and enforce schema validation.
- Maintain an up-to-date API catalog and event schema library.
- Automate validation gates at each handoff point.
- Embed retry and circuit breaker patterns in integration flows.
- Define clear SLAs for data freshness and error rates.
- Synchronize release windows across integration and orchestration teams.
- Foster regular handoff reviews and cross-team collaboration.
By producing well-defined integration artifacts, adhering to synchronization preconditions, and implementing robust handoff mechanisms, organizations ensure that AI agent workflows transition smoothly to orchestration, monitoring, and compliance phases, driving scalable, enterprise-wide productivity gains.
Chapter 6: Workflow Orchestration and Automation
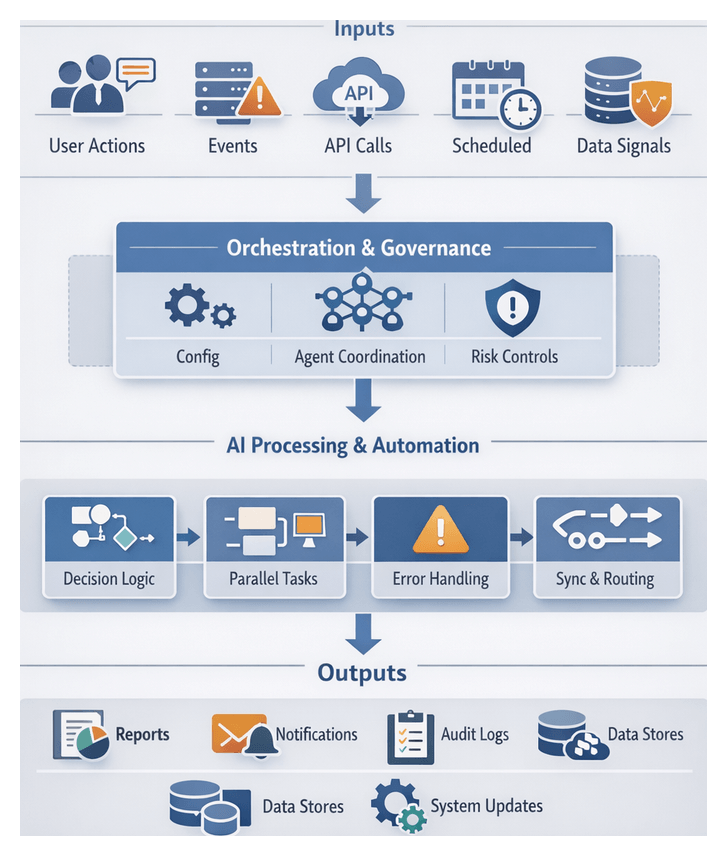
Orchestration Framework and Core Components
The orchestration layer functions as the central nervous system of AI-driven workflows, translating strategic objectives into reliable, scalable executions. It coordinates autonomous agents, human participants, and external systems by defining goals, triggers, handoff points, decision logic, parallel processing paths, and error-management strategies. A robust orchestration framework enforces governance rules, monitors agent health, and provides transparency into resource utilization, enabling rapid adaptation to evolving business conditions.
Triggers and Inputs
Triggers determine when workflows initiate, advance, or respond to external events. Categorizing triggers ensures consistency and traceability:
- User-Driven: Initiated via portals, chat interfaces, or CLIs, with inputs such as credentials and session context.
- Event-Driven: System events like file arrivals, database updates or webhooks carry payloads and metadata.
- Time-Based: Scheduled via cron or calendar rules for batch jobs, syncs, or audits.
- API-Driven: External calls with endpoint URLs, authentication tokens, and payload schemas.
- Data-Driven: Threshold alerts on streams or anomaly detections with source configurations.
- Manual Override: Administrative interventions specifying scope, credentials, and audit annotations.
Each trigger maps to input parameters, validation routines, and security checks. Well-specified triggers minimize manual intervention, accelerate response times, and provide audit points for compliance reporting.
Prerequisites and Configuration Artifacts
Before orchestration begins, foundational requirements must be met:
- Environment Configuration: Workflow engines, container runtimes, and network topology deployed with verified endpoints and DNS resolution.
- Agent Registration and Health: AI agents registered with heartbeat checks; unhealthy agents excluded from scheduling.
- Authentication and Authorization: Least-privilege credentials, tokens, or certificates for all participants.
- Configuration Artifacts: Versioned workflow definitions, decision tables, routing rules, and parameter files in a central repository.
- Data Availability: Accessible datasets, APIs, and queues with schema validation and quality checks.
- Policy and Compliance: Automated governance engines enforcing data handling and privacy regulations.
- Dependency Verification: Critical systems online with retries and fallbacks for transient failures.
Clear input specifications—YAML or JSON definitions, credential stores, parameter sets, routing tables, notification channels, policy rules, and schema registries—enable reproducible, validated executions and prevent runtime errors.
Risk Mitigation and Validation
Embedding robust checks preserves workflow integrity:
- Schema Validation: Pre-execution data format and range checks.
- Dependency Health Checks: Probes for service availability and latency thresholds.
- Idempotency Controls: Deduplication tokens or request hashes to prevent duplicate processing.
- Concurrency Limits: Throttling parallel tasks to avoid resource exhaustion.
- Retry and Backoff: Exponential backoff, circuit breakers, and fallback agents for transient errors.
- Audit Logging: Capture trigger metadata, parameters, decision outcomes, and timestamps.
- Alerting Rules: Threshold-based notifications for errors, latency spikes, or resource overuse.
These validations, combined with central monitoring, enable proactive issue resolution and continuous optimization of orchestration logic.
Decision Logic and Execution Flow
Decision logic and execution flow design formalize how workflows respond to inputs, evaluate conditions, and transition between tasks. By decoupling rules from code, organizations empower business analysts to refine processes and maintain compliance without redeploying agent implementations.
Architectural Components
- Trigger Definitions: Events or conditions that start workflows.
- Decision Nodes: Checkpoints evaluating Boolean expressions, threshold checks, or rule-engine lookups (DMN standards recommended).
- Action Steps: Tasks executed by AI agents, services, or humans.
- Parallel Branches: Concurrent execution of independent tasks.
- Synchronization Points: Gateways awaiting parallel tasks completion.
- Exception and Fallback Handlers: Paths for errors or unmet conditions.
- Termination Criteria: Success or abort conditions defining workflow completion.
Platforms like Apache Airflow, AWS Step Functions, Azure Logic Apps, Temporal, Prefect, and Dagster offer built-in constructs for these components, accessible via code or visual interfaces.
Branching, Parallelism, and Error Handling
- Conditional Branching: Use guard conditions, default fallback paths, and limit nesting to preserve clarity.
- Parallel Execution: Fan-out tasks—such as translation, summarization, and compliance checks—then synchronize results with timeouts and health checks.
- Retry Policies: Configure exponential backoff and circuit breakers for transient failures.
- Fallback Strategies: Bypass noncritical tasks when dependencies fail, escalate after defined thresholds, and log exceptions for forensic analysis.
Integration and AI-Driven Branching
Workflows integrate with external systems via APIs, message buses, and event streams. Centralized orchestration directs calls, while hybrid choreography patterns leverage published events. Key patterns include batch versus real-time transfers, idempotent steps with unique transaction IDs, and secure, rate-limited API designs.
Embedding AI models enables:
- Predictive Routing: Prioritizing cases based on model scores.
- Adaptive Paths: Reinforcement learning refines branching logic over time.
- Explainability Checks: Human review gates for low-confidence inferences.
- Online Learning Triggers: Flagging data for retraining when error rates spike.
Connectors from platforms like IBM Watson Orchestrate simplify embedding AI inference and telemetry capture for optimization.
Visualization, Testing, and Version Control
- Diagramming Tools: Visual editors for stakeholder review.
- Simulation Environments: Emulate inputs and responses to validate flows.
- Source Control: Store definitions in Git for change tracking and rollback.
- Continuous Integration: Automated syntax checks, simulations, and staged deployments.
Governance processes—peer reviews, automated tests, and secure deployment gates—ensure decision logic evolves with the same rigor as software code.
AI-Driven Task Coordination and Routing
At the entry point of orchestration, AI-powered engines classify tasks, balance loads, and manage context throughout multi-step processes, integrating human review where necessary.
Task Classification and Routing
- Intent Extraction: Transformer models from OpenAI parse descriptions to identify actions and qualifiers.
- Metadata Tagging: Enrich tasks with customer segments, risk levels, and SLA requirements via CRM integrations.
- Dynamic Routing: Rule engines map classified tasks to agent queues, human teams, or workflows based on policies and real-time workloads.
Dynamic Load Balancing
- Predictive Throughput: ML models forecast processing times using telemetry from data lakes.
- Priority Queues: Reinforcement learning adjusts priorities to favor critical tasks.
- Resource Awareness: Integration with Kubernetes and Apache Airflow ensures routing accounts for CPU, memory, and network loads.
Context Preservation and Handoff Management
- State Stores: Distributed databases maintain workflow checkpoints.
- Semantic Embeddings: Vector databases support context lookup for related documents and chat logs.
- Payload Serialization: JSON or protocol buffers over Apache Kafka or RabbitMQ for reliable message exchange.
Human-in-the-Loop Integration
- Approval Gates: Conditional branches route tasks to users with alerts via email, chat channels, or work management systems.
- Interactive Interfaces: Platforms provide summaries, scores, and override capabilities.
- Feedback Loops: Human decisions feed model retraining pipelines to improve accuracy.
Exception Handling and Adaptive Recovery
- Anomaly Detection: Unsupervised learning and statistical monitors flag deviations.
- Automated Remediation: Playbooks in AWS Step Functions or Azure Logic Apps trigger retries or fallback services.
- Escalation Workflows: Unresolved issues reroute to specialized teams with enriched diagnostics.
Workflow Outputs, Dependencies, and Handoffs
Upon completion, orchestrated workflows generate standardized outputs, leverage critical infrastructure, and deliver artifacts to downstream systems via reliable handoff mechanisms.
Generated Artifacts and Metrics
- Process Artifacts: JSON or XML definitions capturing task sequences, branches, and outcomes from engines.
- State Snapshots: Checkpoints in frameworks such as Prefect for fault recovery and replay testing.
- Audit Logs: Chronological records of decisions, inputs, outputs, and API calls for compliance and SIEM integration.
- Inter-Agent Exchanges: Event payloads on Apache Kafka buses, revealing data transformations.
- Performance Metrics: Throughput, latency, error rates emitted to monitoring platforms or data warehouses.
- Notification Payloads: Outbound messages—emails, approval requests, or alerts—tracking in task management tools.
- Exception Reports: Detailed error records feeding incident management systems.
- Compliance Deliverables: Policy evaluation results, encryption logs, and access records for audit repositories.
- Contextual Metadata: Data lineage, model version identifiers, and configuration parameters for traceability.
Supporting Dependencies
- Orchestration Engines: Coordinators like Dagster or Prefect interpret definitions and emit events.
- Message Brokers: Apache Kafka or RabbitMQ for decoupled communication and event replay.
- State Stores: Redis, DynamoDB, or relational databases for low-latency checkpointing.
- Observability Tools: Prometheus, Weights & Biases, and Grafana for telemetry and alerts.
- Security Frameworks: IAM services, KMS, and audit middleware enforcing encryption and access policies.
- Data Storage: S3, Google Cloud Storage, Snowflake, or BigQuery for artifact persistence and analytics.
- Notification Systems: Email gateways, collaboration platforms, and tasking tools integrated via APIs.
- Secrets Management: Vault or AWS Secrets Manager for secure credential storage.
- Schema Registries: Versioned data models and interface contracts validated at runtime.
Handoff Mechanisms
- API-Driven Transfers: REST or gRPC endpoints push artifacts and logs to downstream services with authentication and schema validation.
- Event Streams: Publish-subscribe topics in Kafka or RabbitMQ enable loosely coupled integrations and event replay.
- Data Warehouse Loading: ETL/ELT pipelines load metrics and reports into Snowflake or BigQuery for BI consumption.
- Task Management: Engines generate tickets in Jira, ServiceNow, or Teams, embedding context and resuming workflows upon approval.
- Notification Services: Twilio or SendGrid deliver templated alerts with traceable delivery receipts.
- Monitoring Systems: Forward metrics and exceptions to Grafana or Weights & Biases with automated escalation scripts.
- Compliance Pipelines: Push governance artifacts to immutable storage for scheduled audits and regulatory reviews.
This end-to-end orchestration approach—combining clear triggers, rigorous validation, adaptive decision flows, AI-powered routing, and structured handoffs—delivers scalable, transparent, and resilient multi-agent workflows that drive enterprise productivity and continuous improvement.
Chapter 7: Monitoring and Analytics

Monitoring Objectives and Data Input Feeds
Effective monitoring is foundational to AI agent orchestration frameworks. This stage establishes clear observability objectives, defines necessary data input feeds, and ensures prerequisites are met. By capturing telemetry and event streams across infrastructure and application layers, organizations gain real-time insights into agent performance, reliability, and user interactions. This transparency enables proactive issue resolution, performance optimization, and alignment with service level agreements.
Scope and Key Objectives
Monitoring encompasses the collection, aggregation, analysis, and visualization of data that reflect system performance, resource utilization, business transactions, and user experiences. Core objectives include:
- System Reliability: Track uptime, incident frequency, and agent responsiveness to meet service level objectives.
- Performance Optimization: Measure latency, throughput, and resource consumption to identify bottlenecks and guide scaling strategies.
- Error Detection and Resolution: Capture exceptions and failed workflows, with alert thresholds and routing to operations teams or automated remediation routines.
- Business Impact Monitoring: Correlate task completion rates, user engagement, and response accuracy with revenue or cost metrics.
- Security and Compliance Oversight: Monitor access patterns, data transfers, encryption status, and policy violations in real time.
- Capacity Planning: Use resource consumption trends and predictive models to forecast scaling needs.
- Operational Transparency: Provide accessible dashboards and drill-down reports for stakeholders across technical and business units.
- Continuous Feedback: Feed monitoring insights back into agent training, configuration, and workflow redesign.
Essential Data Input Feeds
- Infrastructure Metrics: CPU, memory, disk I/O, network throughput from hosts, containers, or serverless platforms; cloud provider statistics from AWS, Azure; Kubernetes metrics.
- Application Telemetry: AI agent processing times, inference rates, queue lengths; custom events from orchestration engines; health checks and heartbeats.
- Log Streams: Structured and unstructured logs with metadata; access logs, audit trails, API traces.
- Business Events: User actions from interfaces; workflow milestones; KPI updates.
- External Integrations: Transaction logs from Salesforce, SAP, Workday; message bus events via Apache Kafka, Amazon Kinesis, Google Pub/Sub; webhooks.
- User Feedback: Satisfaction ratings, free-text comments, support ticket metrics, sentiment scores.
- Security and Compliance Logs: Authentication events, data access logs, encryption key usage; IDS alerts and SIEM feeds.
Consolidating these feeds in a unified observability platform—using tools such as Prometheus, Grafana, Splunk, and Datadog—enables cross-domain correlation and holistic insights.
Prerequisites and Input Conditions
- Instrumentation Strategy: Adopt standard libraries and agents for metrics, logs, and events.
- Data Schema and Tagging: Define naming conventions, metadata schemas, and labels for environments, versions, and business contexts.
- Observability Platform Deployment: Provision metrics servers, log aggregators, event brokers, and dashboards with scalability and high availability.
- Security Controls: Enforce encryption, role-based access, audit policies, and retention schedules.
- Time Synchronization: Use NTP or equivalent for consistent timestamps.
- Network Configuration: Open required ports, configure firewalls, load balancers, and service meshes.
- Storage and Retention: Allocate storage and define retention periods to balance cost and compliance.
- Alerting Setup: Predefine thresholds, escalation paths, and integrate with Slack, Microsoft Teams, PagerDuty, or Opsgenie.
- Baseline Validation: Conduct initial data validation and establish performance baselines for anomaly detection.
Analytics Dashboard and Alert Workflow
Transforming raw telemetry into actionable insights requires a coordinated workflow spanning data ingestion, real-time analytics, visualization, and notification systems. This pipeline ensures that operations and business teams have immediate visibility into system health and performance.
Real-time Data Ingestion and Preprocessing
- Use Apache Kafka, Amazon Kinesis, or Azure Event Hubs for high-throughput pipelines.
- Implement preprocessing with Apache Flink or AWS Lambda for schema validation, timestamp alignment, enrichment, and filtering.
- Route validated events to a raw data lake for batch analytics and to real-time analytics topics for immediate consumption.
Metrics Computation and Aggregation
Stream processors perform sliding window aggregations—such as counts, averages, and percentiles—using Apache Flink or Spark Structured Streaming. Parallel anomaly scoring leverages services like Azure Anomaly Detector and AWS Lookout for Metrics, or custom models in Kubernetes. Aggregated metrics and anomaly scores feed feature topics for dashboards and alert evaluation.
Visualization Rendering and Dashboard Updates
- Dashboard tools like Grafana, Kibana, Splunk, and Tableau connect to time series databases such as InfluxDB or Elasticsearch.
- Anomaly scores appear as overlay markers or colored thresholds on charts.
- Operators use drill-down filters to explore event details when thresholds are crossed.
- Panels refresh automatically via polling or WebSocket push updates.
Alert Detection and Notification
- Rule Evaluation: Use Prometheus Alertmanager or Datadog to ingest metrics and scores.
- Threshold Comparison: Apply static or dynamic thresholds derived from statistical models.
- Severity Assignment: Classify alerts as info, warning, or critical based on business impact.
- Notification Routing: Dispatch via email, SMS, Slack, Teams, PagerDuty, or incident management platforms.
- Escalation Policies: Route unacknowledged alerts to backup recipients or on-call personnel.
Cross-system Coordination and Roles
- Data Engineers maintain streaming pipelines and schema compatibility.
- AI/ML Engineers train and deploy anomaly detection models.
- DevOps Teams provision and scale clusters, databases, and dashboards.
- Operations Analysts define rules, configure dashboards, and respond to alerts.
- Business Stakeholders consume dashboards for strategic decisions and request new KPIs.
Scalability and High Availability
- Partition event streams across Kafka brokers or Kinesis shards.
- Deploy stateless preprocessing and analytics in Kubernetes with horizontal autoscaling.
- Use distributed time series databases like InfluxDB Enterprise with clustering and replication.
- Implement circuit breakers and backpressure to prevent overload.
- Configure multi-region failover for analytics clusters and dashboard services.
Best Practices for Optimization
- Version control dashboard configurations and alert rules in Git.
- Use blue-green deployments for analytics engine updates.
- Define clear ownership for each alert category.
- Schedule regular reviews to refine thresholds and retire obsolete alerts.
- Leverage synthetic transaction monitoring for baseline data.
- Embed runbooks and documentation in dashboards for incident response guidance.
AI-driven Anomaly Detection and Insights
AI-driven anomaly detection replaces static thresholds with adaptive, data-driven models that learn normal behavior and surface irregularities in real time. Integrated into the monitoring pipeline, these capabilities reduce mean time to detection, improve prioritization, and reveal latent issues.
Data Ingestion and Contextual Enrichment
- Collect logs, metrics, traces, and interactions via Amazon CloudWatch, Splunk, or Elastic Observability.
- Harmonize schemas to enable consistent feature extraction.
- Tag events with business context—application tiers, service owners, regions, and customer segments.
Unsupervised Baseline Modeling
- Clustering (DBSCAN, k-means) to identify dense regions and outliers.
- Autoencoders for reconstruction error detection.
- Seasonal-trend decomposition (STL) to separate periodic patterns.
Managed services like Google Cloud AI Platform and Azure Monitor support real-time retraining and inference.
Supervised and Semi-Supervised Techniques
- Classify events and predict severity using historical incident data.
- Recommend remediation steps through integrations with ServiceNow or Jira Service Management.
- Bootstrap with limited labels and refine through human feedback.
Real-Time Inference and Prioritization
- Deploy lightweight scoring near data sources to reduce latency.
- Deduplicate correlated alerts to prevent notification fatigue.
- Combine anomaly scores with business impact metrics for risk scoring.
Root Cause Analysis and Causal Inference
- Traverse service and infrastructure dependency graphs.
- Apply probabilistic graphical models and counterfactual reasoning.
- Mine log sequences and frequent patterns leading up to anomalies.
Insight Generation and Visualization
- Cluster similar anomalies over time to reveal chronic issues.
- Forecast recurrence using time series models.
- Produce natural language summaries of anomaly clusters and hypotheses.
- Embed AI outputs in Datadog or Tableau dashboards.
Automated Remediation and Human-in-the-Loop
- Enforce governance via policy engines for guardrails.
- Provide decision support agents with concise anomaly summaries and recommended actions.
- Capture remediation outcomes to refine models and thresholds.
Feedback Loops and Model Refinement
- Allow operators to label false positives and negatives for retraining.
- Track remediation success and impact to evaluate model predictions.
- Adjust sensitivity dynamically based on drift and changing conditions.
Governance and Compliance Integration
- Record audit trails of model decisions and alert lifecycles.
- Enforce role-based access for sensitive telemetry.
- Monitor conformance of detection and remediation to security policies.
Report Outputs, Dependencies, and Feedback Loops
The monitoring and analytics stage culminates in dashboards, reports, alerts, and recommendations that inform decision makers, administrators, and development teams. Structured handoffs and feedback loops ensure these insights drive continuous improvement and align with organizational objectives.
Analytical Report Outputs
- Executive Summary Dashboards: High-level KPIs such as throughput, resolution times, and agent utilization via Power BI or Tableau.
- Operational Performance Reports: Detailed metrics on error rates, latency, queue lengths, and SLA compliance.
- Anomaly and Incident Logs: Catalogs of AI-detected events with context, severity, and root cause hypotheses using Splunk or Anodot.
- User Interaction Summaries: Metrics on human-agent handoffs, override rates, and feedback sentiment.
- Predictive Trend Analyses: Machine learning projections guiding capacity planning and scheduling.
Visualization and Delivery Channels
- Embedded Dashboards: iFrame or native connectors for Grafana panels in enterprise portals.
- Automated Email Digests: PDF or HTML summaries delivered by role and frequency.
- Alerting Systems: Real-time notifications in Teams, Slack, or ServiceNow.
- Data Warehouse Exports: Aggregated metrics into Amazon Redshift or Snowflake for cross-functional reporting.
Key Dependencies for Report Generation
- Telemetry and Event Streams: Continuous feeds via Apache Kafka or Amazon Kinesis.
- Data Transformation Pipelines: ETL/ELT processes using Apache Airflow or AWS Glue.
- Metadata Repositories: Process definitions, agent configurations, and business rules.
- Machine Learning Model Services: Inference endpoints that supply anomaly scores and predictions.
- Governance and Access Control: Role-based permissions and data export policies.
Feedback Loop Mechanisms
- Model Retraining Triggers: Alerts on drift or performance degradation initiate retraining workflows.
- Orchestration Logic Adjustment: Automated pull requests update routing rules and decision trees.
- Knowledge Repository Updates: Curated annotations and incident resolutions enhance the collaborative knowledge base.
- Governance Reviews: Compliance deviations feed audit systems and policy adjustments.
- Capacity Scaling Actions: Forecasted workload surges trigger auto-scaling in cloud or container platforms.
Handoff to Adjacent Stages
- Continuous Improvement: Performance reports and logs guide feature reprioritization and model updates.
- Governance and Compliance: Audit packages and security incident records support regulatory assessments.
- Knowledge Management: User feedback and incident annotations enrich documentation and FAQs.
- Infrastructure Operations: Scaling recommendations inform auto-scaling policies and provisioning.
- Business Strategy: Executive dashboards influence roadmap decisions and budget planning.
Traceability and Accountability
- Artifact Versioning: Reports, models, and configurations versioned with metadata on ownership and rationale.
- Audit Trail Logging: Unique identifiers and timestamps record feedback events and handoffs.
- Role-Based Ownership: Designated owners receive automated notifications for approvals and escalations.
- Service-Level Agreements: SLAs defined for report latency, data freshness, and feedback execution, with meta-monitoring for compliance.
Chapter 8: Collaborative Knowledge Sharing
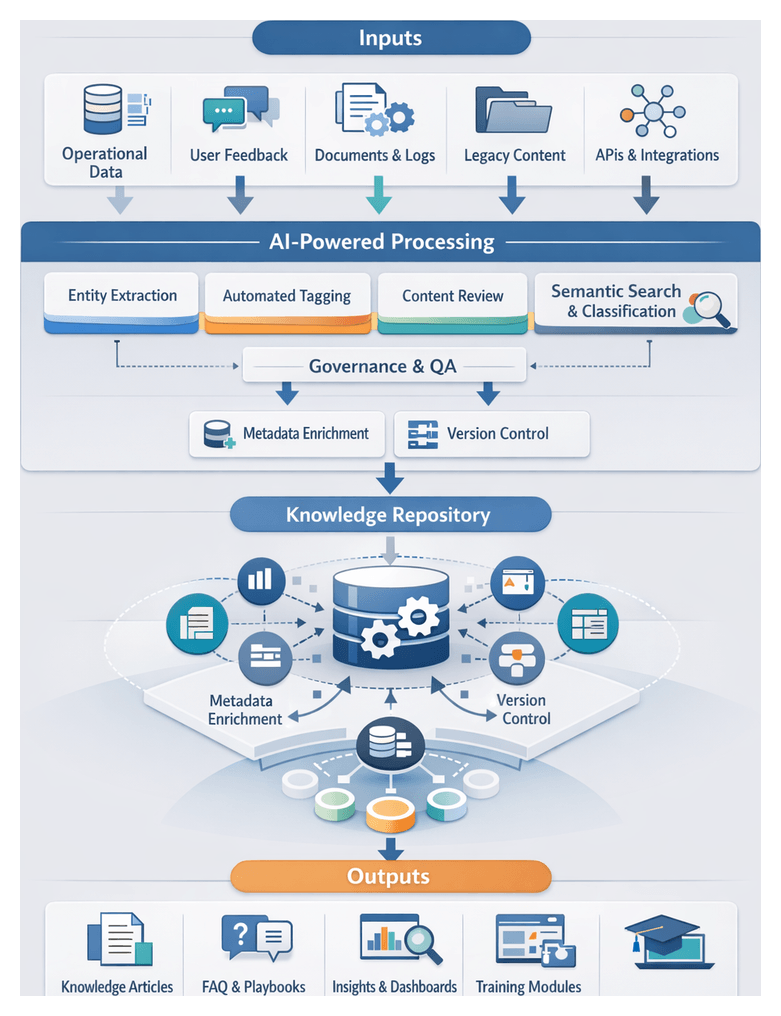
Knowledge Capture Framework
Goals and Purpose
In the collaborative knowledge sharing stage, the objective is to capture, consolidate, and curate insights from AI agents and human participants to create reusable knowledge assets. Clear capture goals ensure that decision rationales, exception handling, and best practices are documented to preserve institutional memory, accelerate onboarding, and support continuous learning. Standardized templates and taxonomies enforce consistency and simplify retrieval, while feeding historical insights back into AI design and orchestration drives adaptive improvement and alignment with real-world use cases. Embedding knowledge management into the AI agent lifecycle mitigates risks of context loss, promotes transparency, and enhances scalability across distributed teams.
Inputs, Prerequisites, and Conditions
Effective knowledge capture relies on operational, technical, and contextual foundations that minimize friction and support high-quality content generation.
- Governance Frameworks: Defined roles, review cycles, version control, and compliance policies enforce data privacy and access permissions.
- Technology Integration: APIs, webhooks, and native connectors link AI platforms, collaboration tools, and knowledge repositories to automate ingestion and metadata tagging.
- Stakeholder Alignment: Training and communication plans ensure that contributors understand objectives and follow standardized procedures.
- Metadata Standards: Consistent schemas for topic tags, source identifiers, and confidence scores enable efficient indexing and retrieval.
- Content Sources: Agent interaction logs, user feedback submissions, operational documentation, performance metrics, legacy repositories, and multimedia assets.
- Technical Requirements: Standardized formats (JSON, XML, CSV, plain text), semantic annotations, access control mechanisms, data quality checks, and scalable ingestion pipelines.
- Environmental Factors: A culture of knowledge sharing, user incentives, real-time capture for time-sensitive industries, localization support, and integration hubs.
By establishing these prerequisites, organizations enhance transparency, accelerate onboarding, support continuous improvement, and mitigate compliance risks, transforming ad hoc interactions into a living knowledge repository.
Repository Workflow and Contribution Flow
The repository workflow structures content submission, review, integration, and governance to maintain accuracy, consistency, and timeliness. AI-driven curation tools and version control systems orchestrate handoffs between stakeholders, while human experts provide domain context. Transparent workflows reduce duplication, accelerate onboarding, and improve decision support.
Content Submission and Version Control
Contributors submit content via standardized templates or portals, including chat interfaces or platforms such as Confluence and SharePoint. AI agents validate formatting, extract entities, and assign initial classifications. Automated drafting assistance from OpenAI or Microsoft Azure Cognitive Services suggests structural improvements. Version control systems track revisions, preserve change history, and support rollback.
Collaborative Editing and Review
AI matching algorithms route submissions to reviewers based on domain expertise and workload. Workflows support parallel or sequential reviews, track comment resolutions, and remind stakeholders of open items. Real-time co-authoring features enable simultaneous edits, while AI detects conflicts and recommends lead editors to reconcile differences.
Integration with External Systems
- Source Monitoring: Agents detect updates in PLM, LMS, or ticketing systems and trigger content refresh workflows.
- Unified Search Indexing: Integrations ensure that external reference material appears alongside internal content with consistent relevance scoring.
- Cross-Repository Linking: AI inserts hyperlinks to related artifacts by analyzing semantic relationships.
Automated Metadata Tagging and Classification
AI-powered agents use named entity recognition, topic modeling, and rules engines to assign taxonomy tags. Continuous feedback loops allow reviewers to validate or override tags, enabling agents to refine accuracy over time.
Governance and Quality Assurance
- Policy Enforcement: Automated checks validate security classifications and detect sensitive information.
- Quality Metrics: Agents evaluate readability, coherence, and completeness against thresholds.
- Audit Trails: Logs capture submission, review, and approval activities with timestamps and change summaries.
Notifications and Coordination
Orchestration agents manage alerts via email, chat, or in-tool notifications based on submission receipts, review assignments, and approvals. Adaptive reminders analyze responsiveness to prevent delays, and contextual summaries guide stakeholders with links to pending tasks.
Workflow Metrics and Insights
- Cycle Time Analysis: Tracks submission, review, and publication durations.
- Contributor Dashboards: Shows top contributors, workload distribution, and engagement rates.
- Predictive Bottleneck Detection: Forecasts delays using historical data and current workloads.
These insights drive continuous workflow optimization, inform resource allocation, and enhance throughput and quality.
AI-Driven Semantic Search and Classification
Semantic search and automated classification transform raw assets into organized, searchable repositories. By understanding intent and context, AI-driven search reduces friction and surfaces relevant expertise, while classification ensures alignment with enterprise taxonomies.
Core AI Capabilities
- Contextual Embeddings: Transformer-based models from OpenAI encode text into vectors for nearest-neighbor search.
- Automated Taxonomy Generation: Clustering and topic modeling propose new categories and update ontologies.
- Entity Recognition and Linking: Services like Amazon Kendra identify and link mentions to canonical entities.
- Relevance Ranking and Personalization: ML models integrate behavioral signals to tailor results to user roles and preferences.
- Continuous Learning: Feedback loops capture implicit and explicit signals to retrain classification and ranking algorithms via platforms like Elastic Enterprise Search.
Supporting Infrastructure
- Search Engine: Platforms such as Microsoft Azure Cognitive Search handle ingestion, tokenization, and semantic ranking.
- Vector Database: Solutions like Pinecone or FAISS support low-latency approximate nearest-neighbor search.
- Metadata Store: Graph databases maintain taxonomy labels, entity relationships, and version history.
- Monitoring Framework: Dashboards track query volumes, response times, and model drift, feeding analytics back into retraining workflows.
Workflow Roles and Interactions
- Ingestion: Search engines parse text, invoke NLP preprocessing, and extract metadata.
- Embedding: Services generate and store vectors linked to document identifiers.
- Enrichment: NER and taxonomy engines annotate content and classify documents.
- Synchronization: Transactional or event-driven pipelines keep text indexes, vector stores, and metadata repositories consistent.
- Query Processing: Orchestration combines keyword and semantic results, applies ranking, and returns ordered content.
- Feedback Loop: Interaction logs and ratings feed analytics stores to retrain models, closing the learning loop.
Strategic Benefits
- Improved findability and reduced search time.
- Enhanced knowledge reuse through entity linking and related content suggestions.
- Scalable taxonomy management that adapts to evolving terminology.
- Data-driven insights into search patterns and knowledge gaps.
- Consistent user experience via personalized relevance ranking.
Shared Knowledge Outputs and Handoffs
Collaborative knowledge sharing produces artifacts that feed downstream workflows, AI agents, analytics, and governance processes. Clear deliverables, dependencies, and handoff mechanisms ensure seamless knowledge flow into operational and analytical systems.
Artifact Deliverables
- Structured Knowledge Articles with metadata, version histories, and cross-references.
- FAQ Sets curated from agent interactions and user feedback.
- Semantic Indexes and Embeddings for AI-driven retrieval.
- Taxonomy and Ontology Definitions aligning domain entities and relationships.
- Playbooks and Best Practices with procedures, heuristics, and benchmarks.
- Content Change Logs and Audit Trails capturing contributor actions.
Dependencies and Production Criteria
- High-fidelity capture of interaction logs and user feedback.
- Automated classification outputs from trained NLP models.
- SME reviews via tools like Confluence or SharePoint.
- Governance rules for redaction, encryption, and distribution.
- Version control in Git-based platforms or enterprise content services.
- Search infrastructure such as Elasticsearch or vector stores like Pinecone.
Packaging and Delivery Formats
- RESTful APIs exposing JSON payloads for orchestrators and agents.
- Bulk export files in CSV, XML, or JSONL for offline analytics.
- Content feeds and webhooks for real-time synchronization.
- SDK libraries in Python, Java, or JavaScript for custom integrations.
- User-facing portals with search, filters, and recommendations.
Handoff Processes
Key integration points for knowledge artifacts include:
- Orchestration and Agent Configuration: Registration of API endpoints, incorporation into decision nodes, updating agent skills with new embeddings and taxonomies, and dynamic prompt injection to enhance generative responses.
- Analytics and Monitoring: Usage metrics collection, dashboards via Tableau or Power BI, anomaly alerts, and feedback loops for content improvement.
- Governance and Compliance: Audit trail exports, IAM synchronization, encryption key rotations via HashiCorp Vault, and policy enforcement hooks.
- Training and Onboarding: LMS packages in SCORM or xAPI formats, interactive simulations, certification materials, and automated onboarding workflows.
- Quality and Reliability: Contract testing of API schemas, staging environments for end-to-end tests, synthetic health monitoring, and rollback procedures.
By codifying outputs and handoff mechanisms, organizations embed continuous improvement, maintain compliance, and ensure that knowledge assets deliver maximum value across AI-driven and human workflows.
Chapter 9: Governance, Security, and Compliance

Governance and Access Control Foundations
This stage establishes rules that secure AI workflows, align with regulations such as GDPR, HIPAA, and SOC 2, and integrate with internal security policies. Defining clear authorization, accountability, and risk mitigation policies ensures AI agents operate under controlled conditions.
Key Inputs and Preconditions
- Regulatory frameworks and standards documentation for GDPR, HIPAA, SOC 2.
- Organizational policies on data classification, encryption, incident response.
- Role-based and attribute-based access models with definitions of user and agent roles.
- Risk assessments, threat models, and data classification schemes tagging assets as public, internal, confidential, restricted.
- Stakeholder requirements from IT security, legal, compliance, and business owners.
- Policy-as-code repositories such as Open Policy Agent.
- Identity management integration with Okta, Azure Active Directory, and AWS Identity and Access Management.
- Audit and logging requirements, retention periods, formats for compliance and forensic analysis.
- Change management and approval workflows to maintain policy versioning and rollback capabilities.
Enforcement Conditions and Best Practices
- Principle of Least Privilege applied to all agents and users.
- Dynamic, context-aware authorization with attribute-based policies.
- Automated provisioning and de-provisioning via identity providers.
- Multi-factor authentication for sensitive functions.
- Segregation of duties to prevent conflicts of interest.
- Policy engine deployment for real-time evaluation and enforcement.
- Training and awareness programs for developers and administrators.
- Baseline security configurations for encryption, network segmentation, endpoint protection.
Security Workflow and Audit Paths
An orchestrated security workflow applies prevention, detection, response, and auditing controls across AI agent lifecycles. Each stage coordinates systems such as IAM, encryption services, SIEM platforms, and human reviewers to enforce policies and maintain auditability.
Asset and Data Classification
- Inventory discovery via automated agents scanning cloud and on-premise resources. Integrations with tools like Prisma Cloud detect new instances and storage.
- Metadata tagging of assets with sensitivity labels. AI-driven classifiers analyze unstructured data and suggest tags.
- Owner assignment workflows route classification tasks to data stewards for validation.
Access Control Enforcement
- Policy definitions in IAM systems such as Akamai Identity Cloud or Azure Sentinel integrated IAM.
- Gateway-based policy evaluation for every API call, considering user role, resource classification, context.
- Just-in-time provisioning for elevated privileges and automated pattern-based pre-approvals.
- Automated approval and escalation notifications to security owners, with decisions logged for auditing.
Data Encryption and Protection
- Key management with HSMs or cloud KMS services like AWS KMS and Google Cloud KMS.
- Encryption policies driven by classification labels, enforcing server-side encryption with customer-managed keys.
- TLS 1.2 with mutual authentication for all inter-service communication, managed by platforms such as IBM QRadar.
- Tokenization and masking services for high-sensitivity data to protect PII in logs and dashboards.
Continuous Monitoring and Event Correlation
- Log aggregation from AI platforms, servers, network devices, and IAM via solutions such as Splunk and Microsoft Sentinel.
- Event enrichment adding context like user identity, asset classification, and threat intelligence.
- ML-driven correlation and anomaly detection to group events into incidents and prioritize alerts.
- Automated alert routing and escalation to analysts or AI response bots according to SLAs.
Incident Response and Escalation
- Automated containment, e.g., quarantining resources, disabling accounts using tools like Prisma Cloud.
- Forensic data collection with snapshots and memory dumps stored in tamper-proof repositories.
- Integrated case management and AI-driven assistants for root-cause analysis and next-step suggestions.
- Orchestration scripts for remediation tasks and verification of restored operations.
- Post-incident reviews to document timelines, impacted assets, root causes, and lessons learned.
Audit Trail Generation and Reporting
- Event retention and immutable archival per retention policies for various record types.
- Compliance report generation for ISO 27001, SOC 2, GDPR using pre-configured templates.
- Interactive dashboards displaying metrics such as failed access attempts, encryption coverage, and response times.
- Automated sign-off workflows with digital signatures to ensure non-repudiation.
- Continuous improvement feedback loops feeding audit findings into policy and control updates.
AI-driven Policy Interpretation and Automation
AI capabilities enhance policy interpretation, monitoring, and dynamic enforcement across compliance and governance frameworks. NLP engines ingest regulatory and internal policy documents, mapping obligations and restrictions to system configurations.
Policy Interpretation and Enforcement
Natural language processing and ML classifiers translate policy texts into actionable rule sets for access controls, encryption requirements, and transaction limits. AI agents continuously scan policy repositories for updates—such as GDPR or HIPAA revisions—and trigger automated updates to enforcement mechanisms.
Real-time Monitoring and Alerting
AI-driven systems ingest telemetry from network sensors, endpoints, application logs, and cloud platforms into unified streams. Tools such as Splunk and Microsoft Azure Sentinel normalize data and apply anomaly detection models to surface high-priority alerts based on risk scores.
Automated Risk Detection and Incident Response
Integrations with orchestration platforms like AWS Security Hub and IBM Guardium enable AI agents to initiate containment workflows—isolating endpoints, revoking sessions, and sanitizing data—then trigger forensic analysis and generate incident reports.
Machine Learning for Adaptive Compliance
Supervised and unsupervised learning pipelines retrain detection models and rebaseline normal behaviors to adapt to evolving patterns. Reinforcement learning optimizes monitoring thresholds and response strategies through feedback loops of incident outcomes and audit findings.
Integration with Governance, Risk, and Compliance Platforms
Bi-directional APIs link AI modules with platforms such as Archer, ServiceNow GRC, and OneTrust. Updates to control requirements propagate to monitoring rules, while recurring compliance gaps generate remediation tickets and assign ownership within GRC workflows.
Privacy, Ethics, and Explainability
Data anonymization techniques, including tokenization and differential privacy, protect PII during analysis. Explainable AI frameworks produce action traces detailing evaluated rules, triggering data points, and confidence scores to support auditability and fairness.
Operationalizing and Scaling AI Compliance Agents
Containerization and orchestration ensure versioning, scalability, and rolling updates of AI modules. Centralized logging and event buses collect outputs from policy interpreters, anomaly detectors, and orchestrators. Meta-agents perform health checks, self-tests, and manage updates to maintain high availability.
Collaborative Oversight and Human-AI Partnership
AI agents augment human analysts by surfacing insights and automating routine tasks, while ambiguous cases are flagged for expert review. This partnership model enhances trust in AI decisions and ensures alignment with business objectives and ethical standards.
Future Directions
Generative AI will automate policy drafting and report creation. Advanced graph analytics will map regulatory obligations to data lineage, and federated learning will enable cross-organizational threat models without sharing sensitive data, advancing proactive compliance.
Compliance Documentation and Continuous Improvement
Structured reports and artifacts validate that AI workflows meet organizational and regulatory standards, support audits, and drive continuous refinement of controls.
Compliance Documentation Outputs
- Policy Adherence Matrix: Mapping of policies to system components and workflow steps.
- Security Configuration Report: Inventory of firewall rules, encryption settings, IAM configurations, and vulnerability scans.
- Audit Trail Log Export: Standardized logs capturing user actions, system events, and AI decisions.
- Risk Assessment Summary: Evaluation of risks with quantitative scores and mitigation status.
- Compliance Certificate: Formal attestation of adherence to standards and regulations.
- Exception and Waiver Log: Records of approved deviations with compensating controls.
Dependency Mapping and Resolution
- Governance policy repositories with version control and change management.
- Configuration Management Database (CMDB) for asset and control mapping.
- IAM systems for role definitions and authentication logs.
- SIEM platforms for comprehensive event data integration.
- Risk assessment frameworks with threat intelligence and vulnerability data.
- Third-party compliance tools for GDPR, HIPAA, SOC 2, ISO 27001 reporting.
Handoff Procedures to Audit and Governance Teams
- Packaging and Versioning: Bundle deliverables into a versioned archive with manifest files.
- Secure Distribution: Transfer via encrypted channels or secure document systems.
- Handoff Checklist: Verify contents, data integrity, and acknowledgments.
- Stakeholder Sign-Off: Time-boxed review for formal approval.
- Issue Tracking and Remediation: Log findings in tracking systems and monitor remediation progress.
- Archival and Retention: Store artifacts per regulatory retention schedules with tamper-evident protection.
Integration with Continuous Monitoring and Improvement
- Feedback of key metrics—policy deviations, remediation times—into monitoring dashboards.
- Automated triggers to initiate policy reviews based on compliance findings.
- Workflow adjustments informed by audit outcomes, strengthening controls and detection logic.
- Periodic compliance drills and simulated audits to validate reporting processes.
- Cross-functional retrospectives and knowledge sharing to propagate lessons learned.
This closed-loop approach ensures AI governance remains proactive, resilient, and aligned with evolving regulatory landscapes.
Chapter 10: Scaling and Continuous Improvement
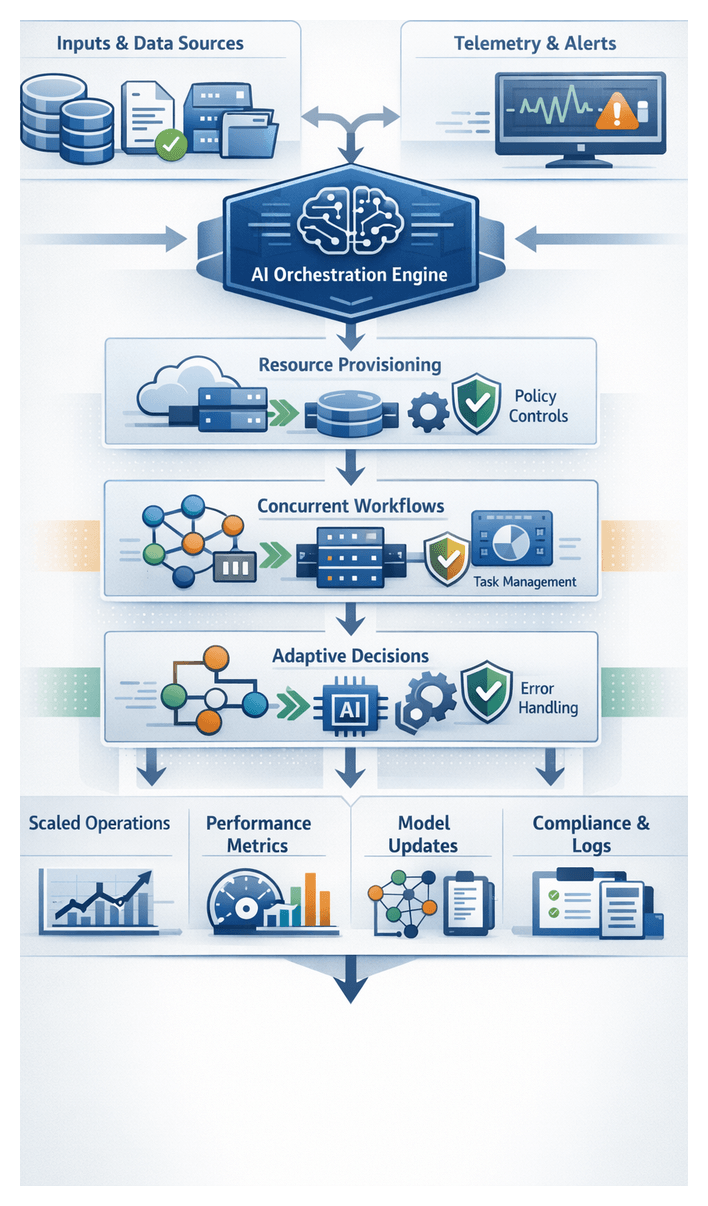
Background and Purpose of Scaling
Scaling shifts AI from isolated workflows to comprehensive enterprise systems. This phase ensures compute resources, data pipelines, governance policies, and user experiences can grow cohesively, avoiding silos that compromise performance and compliance. It tests the AI ecosystem’s ability to manage increased loads, uphold response-time SLAs, and adhere to regulatory standards across various regions and platforms. By establishing clear success metrics—like transaction throughput, task completion rates, and cost per interaction—organizations can align technical capabilities with strategic goals, guiding provisioning, monitoring, and optimization efforts. Integrating telemetry, user feedback, and anomaly detection into centralized dashboards fosters a continuous improvement loop, allowing for swift identification of bottlenecks and timely adjustments to models, infrastructure, and processes. Additionally, formalizing scale-out procedures enhances collaboration among data science, IT operations, security, and business teams, equipping organizations to proactively address constraints and deliver impactful AI-driven experiences.
Strategic Objectives and Prerequisites
- Throughput Enhancement and Concurrency Goals: Define targets for simultaneous agent interactions—such as 10,000 requests per minute at 95th-percentile latency under 300 ms—to dimension infrastructure and validate under load.
- Geographic and Platform Distribution: Deploy regional Kubernetes clusters or edge nodes to achieve sub-100 ms round-trip times in new markets and support multi-cloud, hybrid and on-premise environments.
- Resilience and Fault Tolerance: Establish RTO and RPO targets—such as five-minute failover between zones and zero data loss—using load balancers, auto-scaling groups and replicated stateful services.
- Cost Optimization and Efficiency: Target reductions in cloud spend per interaction through rightsizing, spot-instance strategies and dynamic autoscaling based on CPU and memory utilization.
- Use Case Expansion: Scale from initial pilots to multiple business domains—such as sales, customer support and HR—by supporting a defined number of production-ready scenarios within a set timeframe.
- Automation versus Human-in-the-Loop: Specify percentages of fully automated interactions and escalation thresholds for human review to balance risk and maintain service-level agreements.
Prerequisite Conditions
- Validated Pilot Performance: Demonstrate stable latency, throughput and error rates under representative loads, with positive user feedback informing capacity planning.
- Operational Playbooks: Maintain runbooks covering deployments, rollbacks, incident response and capacity adjustments to reduce mean time to resolution.
- Governance and Compliance: Secure approvals for data classification, privacy impact assessments and alignment with frameworks such as GDPR or HIPAA.
- Cross-Functional Alignment: Define roles and responsibilities across data science, DevOps, security and business units, and establish change control and monitoring ownership.
- Automated Testing Suites: Integrate unit, integration, performance and end-to-end tests into CI/CD pipelines to prevent regressions during scaling changes.
Key Readiness Inputs
- Performance Metrics: Analyze time-series telemetry from tools like Prometheus and Datadog to identify peak loads and capacity cushions.
- Capacity Forecasts: Translate business growth projections into infrastructure needs—CPU core-hours, memory, network throughput and storage IOPS—aligned with budget models.
- Infrastructure Audits: Review Kubernetes autoscaler settings, Terraform state files and service quotas for platforms such as AWS SageMaker and Kubeflow.
- Data Pipeline Profiles: Validate throughput and latency of ETL and streaming frameworks—using Apache Kafka and Apache Airflow—under anticipated scale.
- Security Readiness: Incorporate vulnerability assessments, penetration-test findings, encryption key schedules, role-based access controls and audit log configurations.
- Governance Artifacts: Ensure model approval workflows, data retention policies and change management procedures are in place with decision logs and exception registers.
- Operational Supports: Maintain runbooks, on-call schedules and escalation paths in platforms like PagerDuty or Splunk, and provide training materials for new scenarios.
- Change Management Plans: Prepare communication matrices, training schedules and phased rollout plans, backed by early-adopter programs and feedback mechanisms.
Scaling Workflow Processes and Iteration
Triggering Scale Operations
Scalable workflows rely on event-driven triggers from telemetry streams. Latency-based, volume-based, resource-based and business-driven thresholds feed into an event bus, where AI-enhanced monitoring algorithms classify alerts by severity and dispatch scale requests with contextual metadata—workflow IDs, utilization metrics and priority levels.
Resource Provisioning and Configuration
Upon trigger validation, Infrastructure as Code templates provision compute, storage and network resources via cloud APIs or virtualization platforms. An AI-driven policy engine enforces security, compliance and cost controls, while configuration agents apply environment-specific settings, secret injections and data pipeline rerouting.
- Retrieve IaC templates and parameters from version control.
- Validate against compliance and governance policies.
- Invoke APIs to provision resources.
- Apply network, access-control and secret-management scripts.
- Register new nodes or services with the orchestration engine.
Orchestrating Concurrent Workflows
A workflow engine expresses processes as directed acyclic graphs, assigning tasks dynamically to agents via message brokers or service meshes. Real-time capacity and historical performance profiles guide task routing, heartbeats detect failures and checkpointing supports workflow resumption.
- Task enqueuing and dequeueing via message brokers.
- Agent health checks and dynamic workload balancing.
- State persistence for fault recovery.
Adaptive Workflow Branching
Decision nodes evaluate runtime metrics—error rates, data quality scores—and route tasks to remediation or parallel paths. AI decision modules predict failure patterns, trigger fallback agents or human reviews, and enforce quality gates to maintain reliability at scale.
Continuous Integration and Deployment for Workflows
CI/CD pipelines version workflow definitions and agent code through unit, integration and performance tests. Blue-green and canary strategies enable incremental rollouts, with automated governance checks and rollback mechanisms ensuring stability.
- Checkout code and pipeline definitions.
- Execute automated test suites, including load tests.
- Review compliance and performance reports.
- Deploy to staging for user acceptance testing.
- Roll out to production with monitoring and rollback readiness.
Coordination and Feedback Loops
Regular planning sessions, sprint reviews and governance checkpoints align DevOps, AI Ops, DataOps, security and business teams. Shared dashboards display real-time scaling metrics, cost implications and compliance status. As agents emit structured events on task completion, stream processors enrich data and AI-driven anomaly detectors trigger remediation workflows, closing the loop on continuous improvement.
Governance and Compliance in Scaling
- Automated policy validation during provisioning and deployment.
- Role-based access control enforced at orchestration steps.
- Immutable audit logs capturing configuration changes and approvals.
- Periodic compliance scans and corrective actions for policy drift.
Model Retraining and Adaptation Roles
Continuous Performance Monitoring and Drift Detection
AI components assess model health using statistical drift methods—such as population stability index and Kolmogorov-Smirnov tests—and real-time concept drift monitoring. Alerts surface via dashboards in Kubeflow Pipelines or MLflow, triggering automated retraining workflows when thresholds are exceeded.
Automated Data Pipeline Orchestration
- Data ingestion connectors capture new logs and transactions.
- Feature stores like Feast ensure consistent feature definitions and lineage.
- Validation modules apply schema checks, outlier detection and imputation.
- Data versioning with DVC tracks snapshots for auditability.
- Orchestrators such as Apache Airflow or Prefect schedule pipelines and manage dependencies.
Hyperparameter Tuning and Model Selection
- Bayesian optimization guides hyperparameter searches.
- Meta-learning leverages past experiments to seed configurations.
- Population-based training runs parallel model variants.
- Amazon SageMaker Automatic Model Tuning benchmarks and ranks candidates.
- Ensemble generation modules optimize bias–variance trade-offs.
CI/CD for Models
- Model registries in MLflow Model Registry track versions and metadata.
- Containerized delivery with Kubernetes or similar platforms.
- Canary and blue-green deployments validate performance under live traffic.
- Automated checks enforce API contract and latency requirements.
- Governance gates require approvals based on risk and performance thresholds.
Feedback Loop and Continuous Learning
- User interaction logs capture corrections and engagement metrics.
- Active learning modules select high-value samples for labeling.
- Human-in-the-loop reviews integrate expert judgments for uncertain predictions.
- Dashboards track business KPIs to inform strategic adjustments.
- Retraining cadence adjusts based on feedback volume and performance degradation.
Governance, Compliance and Auditability
- Policy enforcement engines validate retraining actions against regulations.
- Role-based permissions control retraining triggers and deployment approvals.
- Audit logs record data versions, configurations and evaluation reports.
- Explainability tools generate transparency reports and bias alerts.
- Automated compliance reports compile documentation for regulators.
Scalable Infrastructure and Resource Optimization
- On-demand GPU/TPU clusters provisioned by orchestration platforms.
- Spot and preemptible instances managed to balance cost and SLAs.
- Feature-store caching minimizes data-transfer overhead.
- Distributed training using TensorFlow or PyTorch.
- Adaptive auto-scaling adjusts cluster size based on queue depths and utilization.
Collaboration and Role Orchestration
- AI-driven task assignment engines allocate reviews based on expertise.
- Notification workflows route approvals and performance alerts.
- Shared experiment dashboards provide real-time retraining visibility.
- Knowledge repositories index documentation and best practices.
- Integration with ITSM tools aligns retraining releases with maintenance windows.
Improvement Outputs, Dependencies, and Deployment Handoffs
- Updated Model Artifacts: Versioned binaries, serialized weights and checkpoints with metadata on training data, parameters and benchmarks.
- Configuration Sets: Deployment manifests, environment variables, rate-limit thresholds and routing rules for orchestration services.
- Performance Reports: Pre- and post-improvement metrics—latency, throughput, error rates and business KPIs—visualized via dashboards in MLflow or Amazon SageMaker.
- Documentation and Runbooks: Deployment guides, troubleshooting procedures, rollback instructions and governance checklists.
- Pipeline Snapshots: Data processing, feature-engineering and validation pipeline definitions captured in Kubeflow, Git and container images.
- Data: Versioned datasets, feature stores and ingestion jobs, with documented transformations and compliance approvals.
- Infrastructure: Compute clusters, GPU/TPU quotas, network configurations and storage volumes defined via IaC tools like Terraform or CloudFormation.
- Integration APIs: Event-bus schemas, middleware settings and SDK compatibility matrices for upstream and downstream systems.
- Change Management: Approved change requests, security reviews and audit logs confirming governance checkpoints.
- Quality Gates: Automated validation of performance thresholds, regression tests and compliance checks before deployment.
- Coordination: Joint planning sessions, shared runbooks and ticketing in Jira or ServiceNow for deployment tasks and timelines.
- Version Control: Tagged release candidates in Git with release notes documenting changes and upgrade instructions.
- Rollback Paths: Scripts, backups and feature toggles enabling rapid reversion to previous models or configurations.
- Post-Deployment Validation: Canary testing, blue-green strategies and live-traffic monitoring of user-facing KPIs to confirm productivity gains or trigger rollbacks.
Conclusion
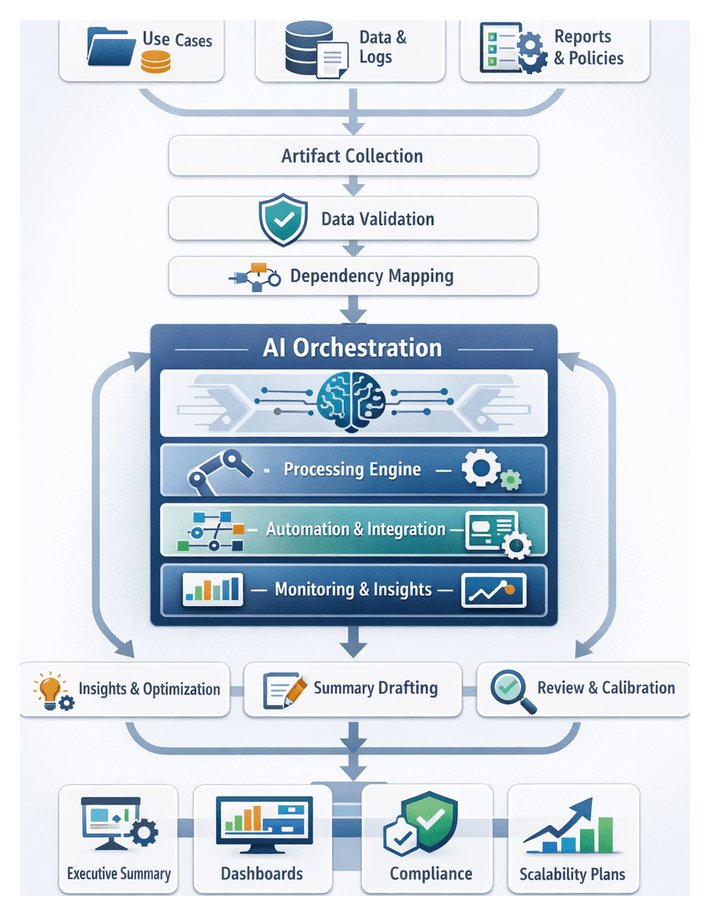
Comprehensive Workflow Synthesis
Bringing together discrete stages of AI agent orchestration into a unified narrative is essential for strategic alignment, operational transparency, and continuous improvement. By consolidating objectives, designs, metrics, and insights—from initial use-case definition through scaling and governance—organizations create an integrated framework that highlights interdependencies, validates strategic outcomes, and informs future planning.
Key prerequisites for this synthesis include finalized deliverables from each stage (use-case documentation, data strategy reports, agent blueprints, infrastructure diagrams, integration specifications, monitoring dashboards, governance policies, and scaling plans), performance metrics captured at handoff points, stakeholder feedback records, version-controlled repositories, and proof of compliance clearance. Cross-functional representation in review sessions ensures that perspectives from operations, IT, security, and business units inform the summary and prevent critical dependencies from being overlooked.
The consolidation process typically unfolds through the following sequence:
- Artifact Collection: Aggregate all reports, logs, and configuration artifacts into a centralized repository.
- Data Validation: Verify the integrity of performance metrics and handoff records, resolving anomalies.
- Dependency Mapping: Create an interdependency matrix that traces how outputs from one stage feed into the next.
- Insight Extraction: Facilitate workshops to capture lessons learned, risks, and optimization opportunities.
- Summary Drafting: Develop a narrative that highlights how each stage contributed to efficiency, risk mitigation, and user satisfaction.
- Review and Calibration: Circulate the draft among stakeholders to reconcile divergent viewpoints and ensure accuracy.
- Finalization and Distribution: Publish the approved summary through governance channels and store it in a knowledge repository.
Deliverables from this phase often include a multi-format summary document with stage-by-stage objectives and outcomes, key performance indicator analyses, lessons learned, an interactive dependency diagram, executive dashboards, a repository link to underlying artifacts, and recommended next-step actions for continuous improvement. Packaging the summary in narrative, visual, and tabular formats ensures adoption across executive, program management, and operational audiences.
Efficiency and Productivity Gains
Unified AI agent workflows drive measurable improvements by eliminating manual handoffs, automating routine tasks, and providing end-to-end visibility. Core components—automated task routing, real-time data synchronization, proactive exception handling, and embedded knowledge sharing—interact to reduce cycle times, error rates, resource usage, and direct labor costs.
Automated Task Routing and Decision Acceleration
- Handoff Latency Reduction: 40–60% decrease in time between task completion and assignment.
- Faster Decision Cycles: Up to 50% reduction in decision latency, as reported by Forrester benchmarks.
- Routing Accuracy: Over 90% classification accuracy in directing tasks to the appropriate agent or specialist.
For example, a financial services firm using UiPath reduced loan processing times from 48 hours to under 8 hours by orchestrating document ingestion, credit evaluation, and compliance checks in real time.
Real-Time Data Synchronization and Workflow Continuity
- Unified Data State: API-driven connectors maintain a single source of truth, reducing reconciliation efforts by 70%.
- Event-Based Updates: Agents subscribe to streams for 24/7 responsiveness and fresh data.
- Automated Exception Detection: Predictive models from DataRobot monitor synchronization health and trigger remediation.
A retail chain integrated point-of-sale, inventory, and logistics systems with predictive anomaly detection to cut stock-out incidents by 35% and excess inventory by 20%.
Proactive Exception Handling and Reduced Rework
- Continuous Monitoring: AI agents track process metrics and flag anomalies immediately.
- Automated Remediation: Specialized agents execute corrective workflows for predefined exception types.
- Human-in-the-Loop Escalation: Tasks with low confidence are routed to experts with contextual data.
A healthcare provider automated patient eligibility verification using semantic analysis. Hybrid exception handling cut erroneous denials by 65% and improved claims throughput by 45%.
Embedded Knowledge Sharing and Skill Augmentation
- Real-Time Recommendations: Contextual guidance reduced new-employee onboarding time by 30%.
- Semantic Search Integration: AI-powered search in a central repository cut research time by 50%.
- Collaborative Editing: Versioned contributions drive continuous refinement of decision rules.
Quantifying Productivity Gains
- Cycle Time Reduction: Median 45% decrease in end-to-end process duration.
- Manual Effort Savings: 60% reduction in repetitive task labor.
- Error Rate Improvement: 30% fewer exceptions or defects.
- Cost Savings: Average 20% of process budget saved in the first year.
- Employee Satisfaction: Improved engagement scores reflecting reduced administrative burden.
Case Study: End-to-End Order Fulfillment
- Order Capture: A virtual sales assistant validates and enriches CRM records.
- Inventory Check: An orchestration engine invokes an inventory agent for real-time stock queries.
- Credit Approval: A machine-learning risk assessment agent authorizes or escalates orders.
- Shipment Scheduling: A logistics agent selects carriers, generates labels, and updates customers.
- Invoice Generation: An invoicing agent issues invoices and triggers payment workflows.
This workflow reduced processing time from 72 hours to 6 hours, cut manual interventions by 85%, and improved on-time delivery from 78% to 96%.
Strategic Impact of Unified AI Workflows
Enhancing Organizational Agility
- Real-Time Indicators: Continuous analysis of CRM, ERP, and external data to detect market shifts.
- Dynamic Resource Allocation: Automatic reconfiguration of task assignments and priorities.
- Generative AI Prototyping: Rapid campaign and service design using OpenAI and Azure Cognitive Services.
Accelerating Data-Driven Decision Making
- Predictive Alerts: Insights from Amazon SageMaker and custom ML pipelines feed executive dashboards.
- Root-Cause Diagnostics: AI-driven analysis identifies process bottlenecks.
- Rapid Experimentation: A/B simulation frameworks integrated into the orchestration engine.
Driving Sustainable Productivity Gains
- Context-Aware Assistants: Guided procedures reduce error rates and onboarding time.
- Automated Quality Control: Agents validate data inputs, eliminating manual checks.
- Self-Service Analytics: Business users request insights without IT mediation.
Fostering Innovation and Continuous Improvement
- Feature Stores and Model Versioning: Streamlined deployment of novel algorithms.
- Feedback Loops: Monitoring dashboards inform retraining pipelines.
- Collaborative Knowledge Hubs: Semantic search agents share best practices enterprise-wide.
Optimizing Resource Utilization and Cost Efficiency
- Serverless and Containerized Deployments: Automatic scaling to workload demands.
- Workload Scheduling Agents: Batching off-peak tasks to reduce cloud costs.
- ETL Consolidation: Eliminating redundant pipelines to lower storage overhead.
Strengthening Risk Management and Compliance
- Automated Policy Enforcement: Data usage checks, interpretability audits, and bias detection.
- Tamper-Proof Audit Trails: Secure logging of agent interactions and decisions.
- Governance Workflows: Automated remediation and documentation upon detecting anomalies.
Elevating Customer Experience and Market Responsiveness
- Personalized Engagement: Conversational AI integrated with CRM systems for tailored recommendations.
- Proactive Communication: Predictive analytics to anticipate delays and manage expectations.
- Adaptive Marketing Orchestration: Multi-channel campaigns that adjust messaging in real time.
Building a Foundation for Future Growth
- Modular Expansion: Adding new AI services without disrupting existing workflows.
- Cross-Domain Reuse: Applying proven patterns enterprise-wide.
- Vendor Flexibility: Standardized APIs avoid lock-in and support best-of-breed integrations.
Adaptability and Future Reuse
Reusable Framework Outputs
- Modular Workflow Templates: Parameterized orchestration blueprints optimized for various triggers and error-handling patterns.
- Configuration and Deployment Manifests: Versioned infrastructure definitions for consistent provisioning.
- Agent Capability Libraries: Preconfigured AI modules with interface definitions and usage examples.
- Governance and Security Playbooks: Policies, access control matrices, and compliance checklists refined through audit cycles.
- Performance Benchmark Reports: Historical telemetry and SLA metrics serving as baselines for future rollouts.
- Knowledge Transfer Guides: Annotated procedures and best-practice recommendations for rapid onboarding.
Key Dependencies and Enablers
- Modular Architecture and API Contracts: Microservices design and standard interfaces for plug-and-play integration.
- Centralized Artifact Repository: Immutable, access-controlled storage with semantic versioning.
- Unified Identity and Access Management: Consistent authentication and role-based access controls across environments.
- Cross-Functional Governance Council: Steering committee to validate framework updates and maintain an evolution roadmap.
- Standardized Monitoring and Telemetry: Central observability platform for logs, metrics, and traces.
- Skilled AI and DevOps Talent: Expertise in model management, orchestration, and continuous delivery.
Handoff Mechanisms and Stakeholder Engagement
- Automated Template Provisioning: CI/CD integration for parameterized workflow instantiation via infrastructure-as-code.
- Contextual Onboarding Sessions: Workshops and training modules tailored to business-unit needs.
- Dedicated Support Channels: Chat forums, issue trackers, and office hours for rapid query resolution.
- Handoff Checklists and Acceptance Criteria: Formal sign-off processes for sandbox deployments, security reviews, and monitoring validation.
- Feedback Integration Loops: Mechanisms to capture enhancement requests and usage metrics for governance council review.
By synthesizing workflow stages, quantifying productivity gains, articulating strategic impacts, and codifying adaptability practices, organizations transform AI agent orchestration into a repeatable, scalable, and future-proof capability. This integrated framework drives operational excellence, empowers decision-makers, and establishes a living ecosystem of reusable assets that accelerates AI-driven innovation across the enterprise.
Appendix
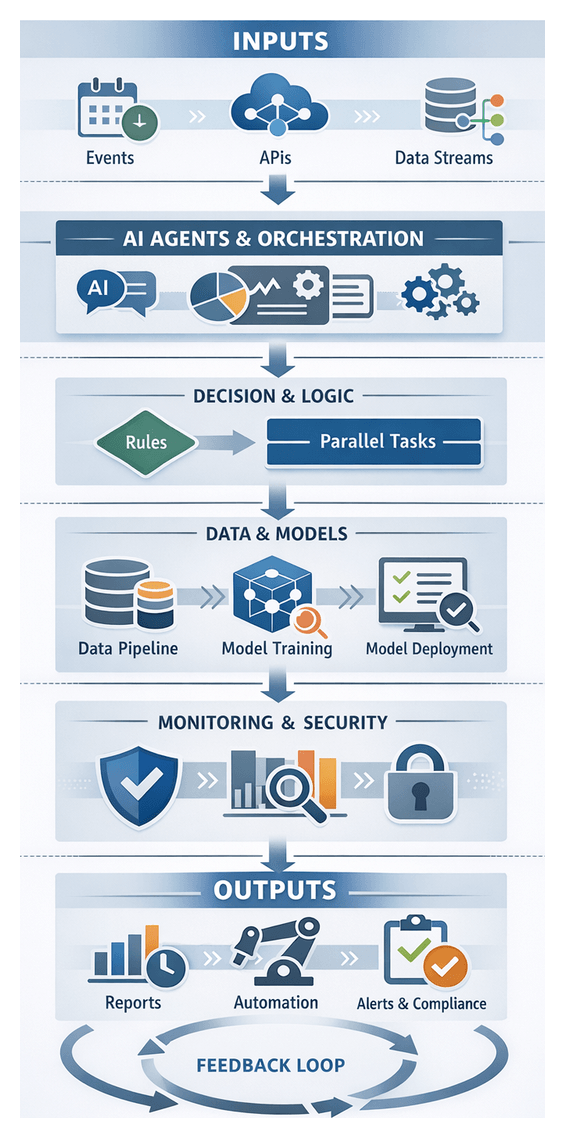
Core Components of AI Agent Workflows
AI Agents and Orchestration
AI agents are autonomous software components that perceive environments through inputs, apply reasoning or learning algorithms, and take actions to achieve defined objectives. In enterprise settings they execute tasks such as data retrieval, decision support, natural language understanding, and process automation. Each agent encapsulates a specific capability—conversation management, predictive analytics, or document processing—exposed via well-defined interfaces and configurable to use case scenarios. By orchestrating multiple agents in a unified workflow, organizations gain scalable automation, consistent rule execution, and rapid adaptation to changing requirements.
Workflows codify sequences of activities that transform inputs into outputs under business logic and decision criteria. An orchestration engine directs execution, invoking agents, applying rules at decision nodes, handling exceptions, and managing parallel or sequential tasks. Key orchestration concepts include:
- Trigger inputs such as events, API calls, or schedules
- Decision nodes that evaluate business rules or AI-driven models
- Parallel branches to optimize throughput
- Synchronization points that await parallel completion
- Exception handlers with fallback or escalation paths
Data Management and Model Lifecycle
Reliable AI workflows depend on end-to-end data pipelines that ingest, cleanse, transform, and deliver data to downstream systems or models. Pipeline orchestration with tools such as Apache Airflow or Prefect ensures scheduling, dependency management, and retries. Feature stores provide centralized repositories for engineered features, maintaining metadata on definitions, transformations, freshness, and lineage to ensure parity between training and inference.
Model registries track versions of trained models and metadata including data provenance, performance metrics, and deployment status. Platforms like MLflow and Kubeflow automate development, validation, deployment, monitoring, retraining, and retirement, supporting robust MLOps practices.
Continuous Integration and Deployment (CI/CD) pipelines extend DevOps to AI. Components include source control, automated testing, artifact repositories, deployment orchestration with Kubernetes and Helm, and rollback mechanisms. Infrastructure as Code with Terraform or AWS CloudFormation ensures repeatable, versioned provisioning of compute, network, and storage resources.
Monitoring, Observability, Governance, and Security
Monitoring collects health and performance metrics while observability infers internal state via logs, traces, and metrics. Dashboards built with Grafana, Datadog or Elastic Observability display key indicators. Alert workflows and automated drift detection services such as Amazon Lookout for Metrics and Azure Anomaly Detector support proactive maintenance of model performance.
Governance enforces structured policies, roles, and procedures. Artifacts include policy documents, access control matrices, audit trails, and approval workflows. Security and compliance layers protect data confidentiality, integrity, and availability through encryption at rest and in transit, identity and access integration with Okta or Azure Active Directory, continuous vulnerability scanning, and alignment with frameworks such as GDPR, HIPAA, and SOC 2. Scaling and capacity planning forecast resource requirements, guide autoscaling and load testing, and maintain service levels during growth phases.
AI Capability Mapping Framework
The mapping framework aligns AI functions to stages of an enterprise AI agent workflow, ensuring the right technologies address the right tasks. This modular approach supports informed selection, resource allocation, and accelerated implementation.
Productivity Objectives and Use Case Definition
- Natural Language Understanding to parse stakeholder requirements
- Semantic Clustering of use case proposals using transformer models
- Decision Optimization with multi-criteria scoring
- Explainable AI to generate human-readable prioritization rationales
Data Strategy and Preparation
- Data Profiling AI to assess quality and recommend cleansing actions
- Automated Schema Inference for semi-structured and unstructured sources
- Anomaly Detection for outliers and drift in data streams
- Governance Policy Engine enforcing masking and retention via policy-as-code
Agent Design and Configuration
- Capability Recommendation Engine suggesting agent archetypes
- Natural Language Generation to draft configuration templates and prompts
- Knowledge Graph Integration for domain entity mapping
- Configuration Validation AI to verify compliance with design constraints
Infrastructure and Platform Setup
- Capacity Forecasting Models for resource demand prediction
- Automated Provisioning Orchestrators applying AI-driven policies in clouds
- Security Hardening AI scanning for misconfigurations and vulnerabilities
- Cost Optimization Agents recommending rightsizing and spot strategies
Integration with Core Enterprise Systems
- API Schema Extraction using NLP to generate client code and contracts
- Semantic Mapping of data fields between agents and systems like CRM or ERP
- Event-Driven Intelligence classifying streams and routing events
- Data Synchronization Monitoring for API latencies and consistency
Workflow Orchestration and Automation
- Decision Tree Learning mining historical traces to optimize branching
- Reinforcement Learning Agents learning optimal task routing and parallelism
- Dynamic Task Classification assigning tasks in real time
- Adaptive Retry and Fallback Policies adjusting intervals and fallbacks
Monitoring and Analytics
- Anomaly Detection Models examining metrics, logs, and interactions
- Predictive Analytics forecasting capacity needs and SLA breaches
- Root Cause Analysis AI correlating telemetry to propose incident causes
- Automated Alert Prioritization scoring alerts by severity and impact
Collaborative Knowledge Sharing
- Semantic Search Engines delivering contextually relevant results
- Automated Classification tagging content by taxonomy
- Natural Language Summarization condensing long-form content
- Feedback Analysis Agents detecting content gaps to prioritize updates
Governance, Security, and Compliance
- Policy Extraction AI parsing regulations into machine-readable rules
- Continuous Compliance Monitoring evaluating configurations and flows
- Privacy-Preserving Techniques applying anonymization and differential privacy
- Explainable AI Frameworks generating transparent model explanations
Scaling and Continuous Improvement
- Drift Detection Models triggering retraining workflows
- Automated Hyperparameter Tuning using Bayesian optimization
- Resource Orchestration Agents optimizing cluster scaling
- Feedback Loop Orchestration integrating operational metrics and user feedback
The adaptive framework supports evolution with emerging technologies such as multimodal processing, causal inference, and generative capabilities, enabling each workflow stage to independently adopt innovations.
Managing Variations and Edge Cases
Complex enterprise environments introduce nonstandard scenarios that can degrade AI operations. Proactive identification and mitigation of variations and edge cases across data, integration, workflows, user behavior, performance, security, and model inference domains sustain reliable, scalable solutions.
Data Quality Variations
- Missing or Null Values: automated imputation, default substitution, validation gates
- Outliers and Anomalous Patterns: profiling, IQR filters, AI-driven quarantine for review
- Schema Evolution and Format Drift: discovery, backward-compatible parsing, metadata registry
- Data Distribution Drift: continuous monitoring and automated retraining triggers
Integration and Connectivity Edge Cases
- API Timeouts and Rate Limits: exponential backoff, circuit breakers, fallback caches
- Version Incompatibilities: contract testing, versioned endpoints, interface adapters
- Network Partitioning and Outages: multi-region failover, message buffers, event replay
- Message Duplication and Ordering: idempotent APIs, sequence identifiers, deduplication logic
Process and Workflow Variations
- Conditional Approvals: rule engines routing tasks by context-specific criteria
- Parallel and Sequential Paths: orchestration forks and joins for multi-branch reviews
- Ad Hoc Overrides: human-in-the-loop gates with audit logging
- External Collaboration: standardized event formats, secure webhooks, partner wrappers
User Interaction Edge Cases
- Ambiguous or Incomplete Queries: clarification dialogs and FAQ retrieval
- Multilingual and Locale Variations: language detection, locale-aware parsing, multilingual models
- Session Drop-offs and Re-entrancy: state stores with expiration and resumption policies
- Invalid or Malicious Inputs: sanitization, schema validation, threat detection modules
Performance and Load Variations
- Burst Traffic Spikes: autoscaling groups, serverless compute, preload mechanisms
- Cold Start Latency: predictive prewarming of instances
- Resource Contention: quotas, namespace isolation, priority scheduling
- Long-Running Tasks and Timeouts: checkpointing and configurable timeouts with fallbacks
Governance, Security, and Compliance Edge Cases
- Data Residency Requirements: region-specific pipelines and failover rules
- Consent Management: verification before processing and re-consent triggers
- Policy Conflict Resolutions: prioritization engines and legal escalation logs
- Emergency Access: just-in-time workflows with strict auditing
Model Behavior and Inference Edge Cases
- Hallucinations and Overconfidence: retrieval-augmented architectures with confidence gating
- Bias and Fairness Violations: fairness detectors and balanced retraining datasets
- Out-of-Domain Inputs: low-confidence detection routing to fallback pipelines
- Model Version Skew: canary deployments, feature flags, rollback triggers
Deployment and Scaling Variations
- Hybrid Cloud and On-Premise Deployments: unified orchestration with environment-specific overrides
- Hotfix and Emergency Deployments: hotfix branches, automated testing, expedited approvals
- Blue-Green and Canary Releases: traffic splitting with automated performance comparisons
- Cross-Region Failover and Disaster Recovery: multi-region replication and DNS failover
Knowledge Repository Variations
- Content Schema Evolution: versioned registries and migration scripts
- Edge-Case Knowledge Gaps: AI detection of frequent no-result queries prompting SME review
- Stale or Conflicting Content: AI-driven review cycles for consolidation or deprecation
Monitoring and Alerting Exceptions
- Alert Storms: AI correlation clusters related alerts into unified incidents
- False Positives and Negatives: adaptive anomaly detection refining thresholds
- Maintenance Windows: coordinated suppression and re-enablement of checks
Best Practices
- Design for Idempotency to guarantee safe message replays
- Implement Graceful Degradation to preserve core functions
- Use Feature Flags and Canary Releases for controlled rollouts
- Maintain Comprehensive Logging and Audit Trails for diagnosis and compliance
- Automate Edge Case Testing in CI/CD pipelines
- Embed Human-in-the-Loop for high-risk scenarios with decision context
- Leverage Continuous Feedback to refine edge-case handling iteratively
AI Tools and Resources
The following AI-driven platforms, frameworks, and standards support the components, mappings, and best practices outlined above.
AI Tools Mentioned
- OpenAI: Provider of advanced generative AI models including GPT series for natural language processing, text generation, and semantic understanding.
- Microsoft Azure Cognitive Services: A suite of prebuilt AI APIs for language understanding, vision, decision, and speech capabilities that integrate with Microsoft cloud infrastructure.
- IBM Watson: AI and machine learning platform offering services for language translation, speech to text, visual recognition, and conversational agents.
- Google Vertex AI: End-to-end managed machine learning platform on Google Cloud for building, training, and deploying models at scale.
- Apache Airflow: Open-source workflow orchestration tool that defines, schedules, and monitors complex data pipelines as directed acyclic graphs.
- UiPath: Robotic process automation platform that automates repetitive tasks and integrates AI capabilities for document processing and decision making.
- Tableau: Business intelligence and data visualization tool that creates interactive dashboards and supports real-time analytics.
- Microsoft Power BI: Cloud-based analytics service providing data visualization, interactive dashboards, and real-time reporting.
- Databricks: Unified data analytics platform powered by Apache Spark, designed for data engineering, machine learning, and collaborative analytics.
- AWS Glue: Serverless ETL service that prepares and transforms data for analytics and machine learning on Amazon Web Services.
- Apache Kafka: Distributed event streaming platform for building real-time data pipelines and streaming applications.
- Prefect: Workflow orchestration tool that manages tasks as Python code, enabling dynamic pipelines and robust error handling.
- dbt (Data Build Tool): Transformation workflow tool for analytics engineering that enables version control and testing of SQL-based data transformations.
- Fivetran: Automated data integration platform that syncs data from sources into data warehouses or lakes with minimal configuration.
- Snowflake: Cloud data platform offering data warehousing, data sharing, and data lake capabilities with scalability and concurrency.
- Collibra: Data governance and catalog solution that manages data policies, lineage, and compliance across the enterprise.
- Immuta: Automated data governance platform that enforces data access policies and ensures compliance with regulations.
- Great Expectations: Open-source data validation framework that builds testable expectations for data quality and schema compliance.
- TensorFlow Data Validation: Library for exploring and validating machine learning data, detecting anomalies, and enforcing schema constraints.
- MLflow: Open-source platform for managing the machine learning lifecycle, including experiment tracking, model registry, and deployment.
- Kubeflow: Machine learning toolkit for Kubernetes that supports portable and scalable ML workflows, model training, and serving.
- HashiCorp Vault: Secrets management tool that secures, stores, and tightly controls access to tokens, passwords, and encryption keys.
- AWS SageMaker: Fully managed service enabling data scientists and developers to build, train, and deploy machine learning models quickly.
- Amazon Lookout for Metrics: Automated anomaly detection service for time-series data that identifies unusual patterns in metrics and KPIs.
- Azure Anomaly Detector: Cognitive service that detects anomalies in time series data and raises alerts for unexpected events.
- Elastic Observability: Integrated solution for logging, metrics, and tracing built on the Elastic Stack for end-to-end visibility.
- Pinecone: Vector database service for similarity search and semantic retrieval at scale.
- Snowflake Streamlit Integration: Framework for building data apps and interactive dashboards directly on Snowflake data.
Additional Context and Resources
- Decision Model and Notation (DMN): Standard for modeling and executing decision logic, maintained by the Object Management Group.
- General Data Protection Regulation (GDPR): EU regulation for data protection and privacy, enforcing strict controls on personal data processing.
- Health Insurance Portability and Accountability Act (HIPAA): US regulation establishing national standards for protecting sensitive patient health information.
- SOC 2: Audit standard defining criteria for managing customer data based on five trust service principles: security, availability, processing integrity, confidentiality, and privacy.
- ISO/IEC 27001: International standard for establishing, implementing, and improving an information security management system.
- Apache Kafka Documentation: Official guide and reference for deploying and managing Apache Kafka clusters.
- TensorFlow Documentation: Comprehensive resource for TensorFlow model development, training, and deployment.
- PyTorch Documentation: Official tutorials and API reference for the PyTorch deep learning framework.
- Kubernetes Documentation: Source for Kubernetes concepts, tutorials, and API references.
- Docker Documentation: Official guide for Docker container creation, image management, and orchestration.
- Terraform Documentation: Resource for defining infrastructure as code and managing lifecycle with Terraform.
- Apache Airflow Documentation: User guide, operator reference, and best practices for Airflow workflows.
- Great Expectations Documentation: Instructions for building data validation tests and integrating with data pipelines.
- Feast Feature Store: Reference for deploying and using Feast to manage features in machine learning pipelines.
- Open Policy Agent (OPA): Policy-as-code engine for unified, context-aware policy enforcement across the stack.
- PRISMA Cloud: Cloud security posture management and threat detection for multi-cloud environments.
- ServiceNow GRC: Integrated governance, risk, and compliance platform for managing audit cycles and policy lifecycles.
- PagerDuty: Incident management and response platform for orchestrating alerts and on-call workflows.
- Splunk: Platform for searching, monitoring, and analyzing machine-generated big data via a web-style interface.
- Datadog: Cloud monitoring and analytics platform for metrics, traces, and logs across applications.
- Argo Workflows: Kubernetes-native workflow engine for orchestrating parallel jobs and pipelines.
- Kubeflow Pipelines: End-to-end pipeline orchestration component of Kubeflow for building and deploying portable workflows.
- MLflow Model Registry: Component of MLflow for managing model versions, staging, and deployment.
- Amazon SageMaker Automatic Model Tuning: Service for automating hyperparameter optimization on AWS.
- Google Vertex AI Hyperparameter Tuning: Managed service for automated hyperparameter search on Vertex AI.
- Azure Machine Learning: End-to-end platform for data preparation, experimentation, and model management on Microsoft Azure.
Further Reading and Industry Resources
- Orchestrating AI Agent Workflows Whitepaper: In-depth exploration of multi-agent orchestration patterns and best practices. Available from leading AI consultancies and vendor sites.
- State of Data Governance Report: Annual research report on data governance trends, challenges, and technologies. Published by industry analysts.
- AI Ethics Guidelines: Frameworks published by organizations such as the IEEE and OECD for responsible AI development and deployment.
- Design Patterns for Scalable AI: Collection of architectural patterns and anti-patterns for building scalable, maintainable AI systems. Often included in cloud provider documentation and community repositories.
- Knowledge Graph Best Practices: Industry recommendations for designing, populating, and maintaining knowledge graphs to power semantic search and decision intelligence. Published by data management experts.
- Feature Store Architectures: Technical whitepapers detailing the design and implementation of feature stores for real-time and batch inference. Provided by data platform vendors.
- Continuous Integration for ML (CI/CD): Guides and case studies on best practices for integrating machine learning models into DevOps workflows, ensuring reproducibility and governance. Hosted by MLOps communities.
The AugVation family of websites helps entrepreneurs, professionals, and teams apply AI in practical, real-world ways—through curated tools, proven workflows, and implementation-focused education. Explore the ecosystem below to find the right platform for your goals.
Ecosystem Directory
AugVation — The central hub for AI-enhanced digital products, guides, templates, and implementation toolkits.
Resource Link AI — A curated directory of AI tools, solution workflows, reviews, and practical learning resources.
Agent Link AI — AI agents and intelligent automation: orchestrated workflows, agent frameworks, and operational efficiency systems.
Business Link AI — AI for business strategy and operations: frameworks, use cases, and adoption guidance for leaders.
Content Link AI — AI-powered content creation and SEO: writing, publishing, multimedia, and scalable distribution workflows.
Design Link AI — AI for design and branding: creative tools, visual workflows, UX/UI acceleration, and design automation.
Developer Link AI — AI for builders: dev tools, APIs, frameworks, deployment strategies, and integration best practices.
Marketing Link AI — AI-driven marketing: automation, personalization, analytics, ad optimization, and performance growth.
Productivity Link AI — AI productivity systems: task efficiency, collaboration, knowledge workflows, and smarter daily execution.
Sales Link AI — AI for sales: lead generation, sales intelligence, conversation insights, CRM enhancement, and revenue optimization.
Want the fastest path? Start at AugVation to access the latest resources, then explore the rest of the ecosystem from there.
