
Securing the Future with Intelligence A Comprehensive Guide to AI Agents in Security and Risk Management
To download this as a free PDF eBook and explore many others, please visit the AugVation webstore:
Introduction
Historical Evolution of Security Operations
Over the past thirty years, security operations have transformed from basic perimeter defenses into sophisticated, data-driven command centers. Early approaches relied on firewalls, intrusion detection systems, and signature-based antivirus software to protect network boundaries. Human analysts manually reviewed logs and hunted for threats, a reactive process that struggled to keep pace with the growing volume and complexity of attacks. The advent of Security Information and Event Management (SIEM) platforms addressed some limitations by aggregating logs and generating near–real-time alerts. Solutions such as IBM Security QRadar Advisor with Watson and Splunk Phantom introduced automation for alert triage, though significant human oversight remained essential.
The shift to big data analytics and cloud infrastructures gave rise to distributed Security Operations Centers (SOCs) capable of ingesting terabytes of telemetry. Endpoint Detection and Response (EDR) platforms like Palo Alto Networks Cortex XDR and CrowdStrike Falcon moved the focus inside the network perimeter, employing behavioral analytics and machine learning to detect anomalies on endpoints, servers, and cloud workloads. Despite these advances, the volume of alerts often overwhelmed security teams, revealing an urgent need for more intelligent, adaptive mechanisms that could learn from data, prioritize risk, and automate routine response actions.
Today’s landscape demands a transition from reactive detection to proactive, autonomous defense. Platforms such as Rapid7 InsightVM apply machine learning to vulnerability management, while the Darktrace Enterprise Immune System uses network immunology to model normal behavior and detect deviations. Yet adversaries innovate faster than traditional controls, driving organizations toward AI agents capable of end-to-end threat management with minimal human intervention.
Defining AI Agents within Security and Risk Contexts
AI agents in security are autonomous software entities that perceive environmental signals, reason over complex data sets, and execute actions to mitigate risk. Unlike rule-based automation, they employ adaptive learning and probabilistic reasoning to interpret threat indicators, assess risk likelihood, and recommend or enact countermeasures. Practitioners evaluate these agents across three core capacities:
- Perception: ingesting diverse streams of telemetry, logs, and external threat intelligence
- Reasoning: applying statistical inference, pattern analysis, or rule induction to predict adversarial behavior
- Action: initiating alerts, orchestrating workflows, or autonomously enforcing policies to contain or neutralize threats
To navigate the expanding ecosystem of AI-driven solutions, organizations employ interpretive frameworks and taxonomies:
- Function-Based Taxonomy: categorizing agents by core functions such as threat detection, incident response, vulnerability assessment, identity management, and compliance monitoring
- Autonomy Maturity Model: defining stages from semi-autonomous tools that require human approval to fully autonomous systems capable of closed-loop decision-making
- Data-Centric versus Behavior-Centric Agents: distinguishing solutions that rely on known indicators of compromise from those leveraging anomaly detection and predictive forecasting
- Integration Spectrum: positioning agents along a continuum from standalone point tools to deeply embedded components in Security Orchestration, Automation, and Response (SOAR) platforms
Rigorous evaluation criteria guide solution selection and alignment with risk management goals:
- Detection Accuracy and Coverage: true positive and false positive rates, mean time to detect, and scenario breadth
- Explainability and Transparency: human-interpretable justifications and auditability of decisions
- Scalability and Performance: throughput, latency, and capacity to process large data volumes
- Integration Flexibility: API support, data model compatibility, and ease of embedding within existing workflows
- Governance and Compliance Alignment: policy engines, audit logging, and adherence to frameworks such as NIST SP 800-53 and ISO 27001
- Operational Resilience: failover mechanisms, adversarial robustness, and behavior under degraded conditions
Market Drivers and Challenges for AI Adoption
Several converging factors accelerate AI agent adoption in security and risk management:
- Expansion of Attack Surfaces: cloud migration, microservices, Internet of Things (IoT), and remote work models increase the number of endpoints and applications requiring protection.
- Escalating Threat Sophistication: advanced persistent threats (APTs), ransomware-as-a-service, and automated exploit frameworks employ AI-driven techniques to evade detection.
- Talent Shortages: a global cybersecurity workforce gap exceeding half a million skilled professionals leads to alert fatigue and analyst burnout.
- Regulatory Pressures: stringent requirements for continuous monitoring, audit trails, and rapid incident reporting in finance, healthcare, and critical infrastructure sectors.
- Demand for Speed and Accuracy: organizations require faster decision-making under resource constraints to reduce dwell time and limit damage.
Legacy tools, designed for static perimeters, struggle in dynamic hybrid environments. Human analysts cannot sustain manual processes at scale, prompting a shift toward AI agents that shoulder routine tasks, surface high-priority incidents, and augment expert decision-making.
Ecosystem Forces Shaping Autonomous Decision-Making
The rise of AI agents reflects broader technological and market dynamics:
- Machine Learning Democratization: open-source frameworks and libraries enable rapid deployment of supervised, unsupervised, and reinforcement learning models.
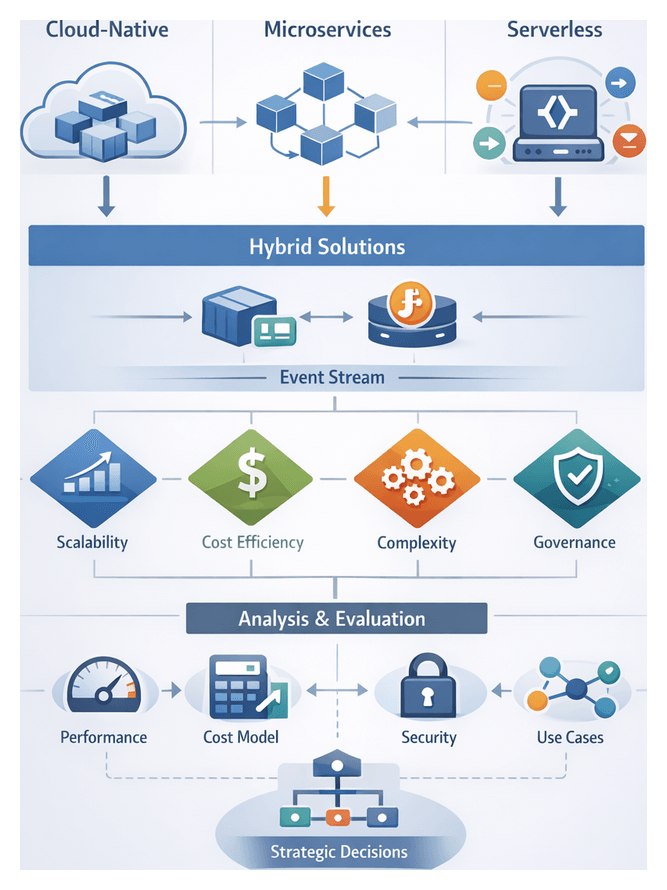
- Cloud and API-Driven Integrations: microservices architectures and API-first designs allow agents to interlink SIEM, SOAR, identity providers, and cloud consoles, fostering cross-domain orchestration.
- Zero-Trust and Risk-Based Models: continuous risk assessment at every transaction and access request requires adaptive controls orchestrated by AI agents.
- Economic Imperatives: rising total cost of ownership for traditional SOC tools, staffing challenges, and alert fatigue drive interest in automation that reduces time-to-containment and delivers measurable ROI.
These forces converge to create a fertile environment for AI agents to execute autonomous security decision-making tasks, operating at machine speed while preserving human oversight where it matters most.
Urgency of Autonomous Intelligence in Threat Landscapes
Today’s adversaries use automation, machine learning, and cloud computing to launch large-scale, adaptive campaigns. Polymorphic malware, self-propagating worms, and fileless techniques evade signature-based defenses, while expanding cloud and IoT environments defy static scans. Manual SOC workflows ingest millions of alerts daily, resulting in alert fatigue, high error rates, and extended dwell times that leave attackers free to explore networks and exfiltrate data.
With over three million unfilled cybersecurity positions globally, organizations cannot rely solely on human expertise. Autonomous intelligence agents ingest heterogeneous data streams, correlate events across domains, and surface high-fidelity insights without constant human intervention. Applications include:
- Cloud-native architectures with rapid asset provisioning
- IoT and operational technology in manufacturing and energy
- Remote and hybrid workforces with distributed endpoints
- DevSecOps pipelines integrating vulnerability assessment into CI/CD
- Supply chain ecosystems requiring real-time monitoring of third-party dependencies
For example, Darktrace Enterprise Immune System establishes dynamic patterns of life for every device, alerting on deviations. IBM Security QRadar Advisor with Watson uses natural language processing to contextualize alerts and automate root cause analysis. Palo Alto Networks Cortex XDR correlates telemetry across endpoints, networks, and cloud workloads to orchestrate behavior-based detection and automated response. These capabilities shrink detection-to-response windows from days to minutes, reducing the scope and impact of breaches.
Gartner projects that by 2025, organizations adopting AI-driven security operations will achieve 50 percent lower operational costs and 30 percent fewer successful breaches. Autonomous intelligence shifts security teams from reactive firefighting to proactive, risk-centric activities—threat hunting, adversary simulation, and resilience testing—supported by continuous situational awareness.
Reader Objectives and Insights Roadmap
This guide equips security and risk management professionals with the strategic, analytical, and conceptual frameworks needed to adopt AI agents effectively. By linking historical evolution, theoretical foundations, and practical perspectives, readers will learn to align AI capabilities with business objectives, governance models, and operational realities.
Intended Audience
- Chief Information Security Officers and risk executives
- Security operations managers and architects
- IT and DevOps leaders integrating compliance automation
- Data scientists and machine learning engineers
- Governance, risk, and compliance professionals
- Ethics and privacy officers
- Consultants and analysts advising on AI and enterprise resilience
Core Strategic Takeaways
Readers will gain a nuanced understanding of how to:
- Justify AI investments through risk reduction, operational efficiency, and compliance improvements
- Frame AI agents as collaborative partners that augment human expertise
- Design governance models balancing autonomy with oversight
- Measure key outcomes such as dwell time reduction, return on security investment, and compliance posture
Analytical and Interpretive Frameworks
The guide introduces models such as pattern-of-life analysis for insider threats, graph theory for fraud detection, and probabilistic risk analysis for financial transactions. It also presents scenario-based reasoning for incident prioritization, decision trees for remediation orchestration, and feedback loops for continuous learning.
Chapter Mapping
- Foundation of AI Agents in Security and Risk Management: terminology, agent taxonomy, architecture
- Threat Detection and Predictive Analytics Agents: anomaly detection and forecasting
- Automated Incident Response Agents: comparing rule-based and adaptive approaches
- Vulnerability Assessment Agents: autonomous scanning and exploit simulation
- Identity and Access Management Agents: adaptive authentication and policy adaptation
- Fraud Detection and Financial Risk Management Agents: real-time transaction integrity
- Compliance Monitoring Agents: NLP-driven regulation interpretation and continuous auditing
- Behavioral Analytics and Insider Threat Agents: unsupervised learning and contextual response
- Integration and Interoperability of AI Security Agents: modular architectures and standards
- Future Trends and Ethical Considerations: generative techniques, bias mitigation, governance
Key Considerations and Next Steps
- Ensure data quality and feature engineering to avoid skewed insights
- Plan for integration complexity with standardized APIs and data transformation layers
- Address model bias and explainability, maintaining audit trails for regulated environments
- Assess organizational readiness, including culture, skills, and governance structures
- Monitor changing threat tactics and update models with agile retraining mechanisms
- Select vendors with extensible roadmaps to avoid platform lock-in
Establish a cross-functional team to translate these insights into a pilot program. Define success criteria, prioritize high-impact use cases, and implement feedback loops for continuous refinement. With a foundation of responsible innovation and strategic alignment, organizations can operationalize autonomous intelligence and build a resilient, future-ready security posture.
Chapter 1: Foundation of AI Agents in Security and Risk Management

Security Operations Evolution and Market Drivers
Over the last two decades, security operations have transformed from manual, perimeter-focused defenses into complex, data-driven ecosystems. Early approaches relied on firewalls, intrusion detection systems and antivirus solutions to protect static network boundaries, with analysts manually correlating logs and investigating alerts. As enterprises embraced cloud services, mobile workforces and interconnected supply chains, the security perimeter dissolved and threat actors deployed advanced tactics such as targeted phishing, fileless malware and multi-stage campaigns. This shift generated vast volumes of unstructured data and alert noise, overwhelming traditional Security Information and Event Management platforms and manual processes.
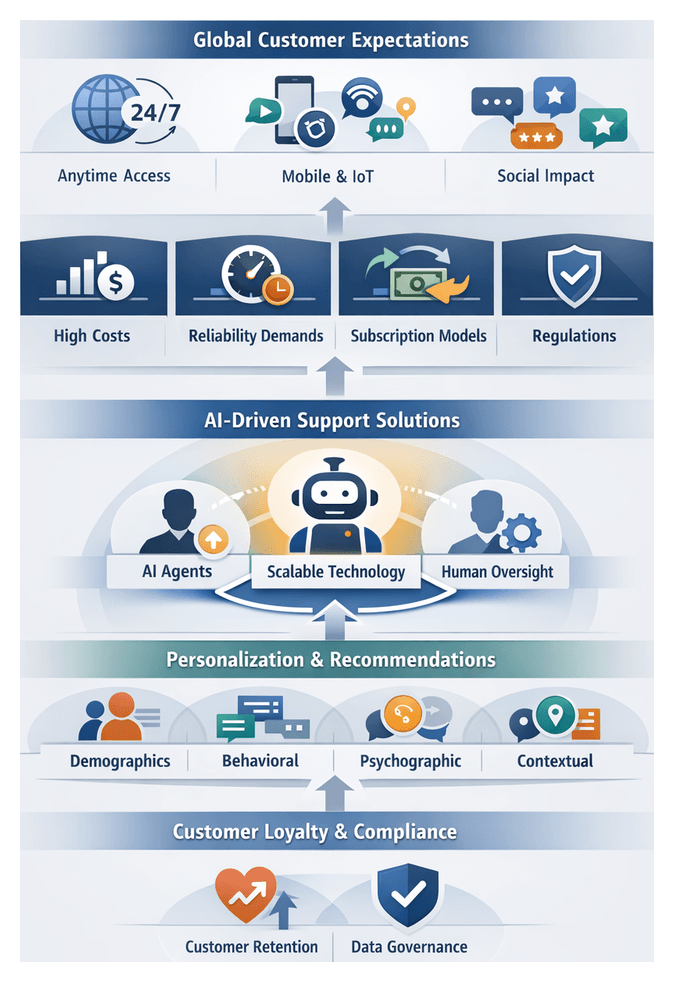
Key market forces driving the adoption of AI agents in security operations include:
- Escalating threat complexity that demands continuous analysis of heterogeneous data streams.
- Global talent shortages that constrain 24×7 monitoring and response capabilities.
- Regulatory pressure from standards such as GDPR and CCPA, which require robust incident detection and reporting.
- Operational efficiency imperatives to balance constrained budgets with proactive threat prevention.
These drivers have fostered a new paradigm integrating AI-driven agents capable of learning from data, reasoning about risk and autonomously executing response actions. Organizations now view autonomous intelligence as a strategic imperative to maintain resilience in the face of evolving threats.
Conceptual Framework for AI Agents
In security and risk management, AI agents are software entities that perceive their environment, make decisions based on analytical models and execute actions to achieve specific objectives. They extend beyond static rule engines by learning continuously, adapting to new threats and collaborating with human operators.
An AI agent architecture comprises three core modules:
- Sensing and Data Ingestion: Gathering telemetry from network sensors, endpoint agents, cloud workloads, identity logs and external threat intelligence feeds to ensure visibility across hybrid infrastructures.
- Reasoning and Decision Making: Applying supervised, unsupervised and reinforcement learning models alongside probabilistic inference and knowledge graphs to assess risk levels and prioritize responses.
- Action and Orchestration: Executing containment, remediation or recovery tasks—such as isolating endpoints, modifying firewall rules or revoking compromised credentials—via integration with platforms like Splunk Phantom and IBM Security SOAR.
AI agents can be classified by autonomy level:
- Advisory agents that recommend playbooks for human approval.
- Semi-autonomous agents that automate low-risk tasks while escalating complex scenarios.
- Fully autonomous agents that optimize response policies with minimal human intervention.
Defining these autonomy tiers clarifies governance requirements and guides integration into existing security ecosystems.
Modern Threat Landscape and the Case for Autonomous Intelligence
Cyber threats are proliferating in sophistication and scale. Recent trends include the explosive growth of Ransomware-as-a-Service, high-impact supply chain exploits, an expanding Internet of Things attack surface and stealthy advanced persistent threats. Traditional human-centric Security Operations Center models struggle to match the speed and complexity of these evolving risks.
Autonomous intelligence addresses these challenges by:
- Operating at machine speed to analyze terabytes of data in real time and initiate containment within seconds.
- Scaling consistently across on-premises, multi-cloud and edge environments.
- Learning continuously through feedback loops and reinforcement to refine detection models and reduce false positives.
Organizations that delay integrating autonomous AI agents risk exposure to advanced attacks, regulatory penalties and reputational harm.
Learning and Decision-Making Paradigms
Supervised Learning
Supervised learning models—such as random forests, support vector machines and deep neural networks—are trained on labeled datasets to achieve high accuracy on known threats. Advantages include predictable performance, alignment with audit trails and model explainability via feature importance and tools like LIME. Challenges include the effort to label data at scale and class imbalance. Platforms like IBM Security QRadar Advisor with Watson integrate supervised models with expert curation to streamline data annotation.
Unsupervised techniques—clustering, autoencoders and density estimation—detect anomalies without labeled data, uncovering novel attack vectors and insider threats. They adapt baselines in dynamic environments, but may produce higher false positives. Tiered alerting and correlation with threat intelligence feeds mitigate noise. Darktrace Enterprise Immune System exemplifies unsupervised deep learning that models enterprise “self” for rapid anomaly detection.
Reinforcement Learning
Reinforcement learning (RL) enables agents to optimize response strategies based on reward signals, balancing containment speed against business impact. Through simulated attack drills, RL agents learn multi-stage mitigation sequences and cumulative risk reduction. Early deployments use sandboxed environments—often built on frameworks like OpenAI Gym—before transitioning to controlled production. Palo Alto Networks Cortex XDR incorporates RL-inspired analytics for continuous policy refinement.
Hybrid and Ensemble Strategies
Combining learning paradigms enhances resilience against concept drift and adversary evolution. Common patterns include:
- Parallel ensembles that fuse supervised and unsupervised outputs via voting or meta-learning.
- Layered analysis where unsupervised models triage anomalies and supervised classifiers confirm threats.
- Contextual reinforcement using supervised pre-training followed by RL fine-tuning in feedback loops.
Effective orchestration of hybrid architectures requires standards for model governance, version control and continuous validation.
Reasoning and Decision Frameworks
Reasoning engines translate model scores into actionable decisions using Bayesian networks, rule engines and knowledge graphs. For example, platforms like Splunk Phantom embed rule-based playbooks, while knowledge graphs informed by the MITRE ATT&CK framework support multi-hop inference and threat attribution. Integrating symbolic logic with machine-learned signals balances agility with governance.
Autonomous Security Functions
Autonomous security functions embed intelligent decision-making into routine risk management workflows, reflecting an organization’s security maturity.
Continuous Monitoring and Observability
Agents ingest real-time telemetry from network logs, endpoints, cloud services and third-party feeds. Unsupervised learning and behavioral analytics establish dynamic baselines, surfacing subtle deviations. Analysts rely on dashboards from platforms such as Microsoft Sentinel and Darktrace Enterprise Immune System to maintain situational awareness across kill chain phases and regulatory controls.
- Frameworks like the OODA loop structure continuous detection workflows.
- Data integration from SIEM, EDR and cloud-native logs enables unified threat visibility.
- Compliance-driven monitoring generates evidence streams aligned with NIST SP 800-53 and ISO 27001.
Dynamic Threat Mitigation and Response
Adaptive agents convert static playbooks into context-aware remediation strategies. Using decision trees and Markov models, agents select actions that minimize time to containment while preserving business continuity. Platforms such as IBM Security QRadar Advisor with Watson and Palo Alto Networks Cortex XDR automate playbooks with human-in-the-loop checkpoints for ambiguous scenarios.
- Graduated response models isolate low-confidence threats automatically and escalate high-severity alerts to analysts.
- Response tactics refine continuously based on historical effectiveness and asset criticality.
- Policy guardrails ensure automated actions comply with governance and risk appetite.
Contextual Threat Hunting and Proactive Defense
Autonomous agents enable hypothesis-driven threat hunting by correlating cross-domain indicators against frameworks like MITRE ATT&CK. Tools such as Splunk Phantom and CrowdStrike Falcon orchestrate automated hunt campaigns, executing query templates and enrichment workflows to surface concealed threats.
- Hunt paradigms apply risk scoring and asset context to prioritize investigations.
- Threat intelligence feeds and behavioral baselines enrich hunt outcomes.
- Proactive defense allocates resources toward high-value investigations.
Policy Enforcement and Automated Compliance
Autonomous compliance agents translate regulatory texts into machine-executable rules, detecting and remediating policy deviations. Natural language processing frameworks adjust controls in real time—exemplified by Okta Adaptive MFA. Dashboards highlight compliance gaps and correlate them with operational changes.
- Governance taxonomies align enforcement with GDPR, PCI DSS and SOX.
- Risk-based prioritization focuses analysts on high-impact deviations.
- Audit trails support external audits and internal policy reviews.
Adaptive Vulnerability Management
Agents continuously assess exploit likelihood, asset exposure and threat context to prioritize remediation. Platforms like Rapid7 InsightVM integrate vulnerability detection with patch orchestration, using predictive risk scores based on CVSS metrics and real-world exploit data.
- Predictive scoring guides patching priorities by combining vulnerability metrics with threat intelligence.
- Adaptive scanning schedules optimize resource use and minimize operational impact.
- Integration with CMDBs maintains context-rich asset inventories.
Cross-Domain Orchestration and Collaborative Defense
Maximal value emerges when agents collaborate through shared data schemas and orchestration platforms, enabling end-to-end workflows. Modular architectures and standards like STIX/TAXII and OpenC2 allow platforms such as IBM Security SOAR to coordinate detection, response and compliance functions in alignment with defense-in-depth and zero trust principles.
- Standardized APIs and messaging protocols enable coherent threat intelligence exchange.
- Performance metrics such as mean time to detect and respond evaluate orchestration efficacy.
- Collaborative defenses preserve accountability while accelerating coordinated actions.
Strategic Insights and Adoption Roadmap
Organizational Readiness Dimensions
Successful AI agent adoption rests on people, processes and culture that support data-driven decision making. Readiness dimensions include:
- Data Maturity: Integrated, cleansed and contextualized data feeds underpin accurate models.
- Skill and Expertise: Cross-disciplinary teams of domain experts, data scientists and analysts are essential for continuous tuning.
- Process Integration: Embedding agents into incident response, vulnerability management and access review workflows ensures seamless augmentation.
- Executive Sponsorship: Leadership commitment secures budget and drives cultural acceptance of automated frameworks.
- Governance and Oversight: Policies for model validation, performance monitoring and exception handling maintain accountability and compliance.
Technology Alignment and Integration Considerations
AI agents deliver maximum value within cohesive, interoperable ecosystems. Critical factors include:
- Modular Architectures: Decoupled components for ingestion, analytics and orchestration enable incremental deployment and upgrades.
- Standards-Based Interfaces: RESTful APIs and common data schemas facilitate integration between SIEM, SOAR and ITSM tools.
- Vendor Ecosystem Compatibility: Integrating anomaly detection from Darktrace with orchestration in Splunk Phantom or pairing endpoint analytics from CrowdStrike Falcon with IBM Security QRadar Advisor with Watson.
- Scalability and Performance: Distributed computing and elastic cloud platforms support high-velocity data streams.
- Security and Resilience: Secure development lifecycles and adversarial testing harden agents against manipulation.
Data and Analytics Foundations
Robust analytic frameworks underpin AI agent effectiveness. Key considerations include:
- Model Transparency: Explainable AI techniques build trust and support forensic justification.
- Bias and Drift Management: Continuous validation and adaptive retraining guard against performance degradation.
- Hybrid Approaches: Layering rule-based logic with supervised, unsupervised and RL models ensures comprehensive detection.
- Contextual Enrichment: Incorporating threat intelligence, asset criticality and business context aligns decisions with risk appetites.
- Real-Time vs Batch Processing: Balancing streaming analytics for immediate response with batch analysis for strategic insights optimizes resources.
Governance, Risk and Compliance Frameworks
Robust governance balances agility with control. Essential elements include:
- Policy Definition: Defining agent autonomy boundaries, escalation thresholds and human-in-the-loop checkpoints.
- Auditability and Reporting: Logging agent decisions, model versions and data inputs for investigations and audits.
- Compliance Alignment: Mapping agent capabilities to ISO 27001, NIST SP 800-53 and GDPR control objectives.
- Risk Appetite Management: Incorporating residual risk from false positives and negatives into risk registers.
- Ethical Safeguards: Conducting privacy impact assessments and ethical reviews for behavioral analytics.
Measuring Impact and Maturity
To demonstrate value, organizations track metrics aligned with AI agent deployment stages:
- Detection Efficacy: True and false positive rates, time to detection.
- Response Acceleration: Mean time to containment and remediation.
- Operational Efficiency: Analyst productivity gains and automation coverage.
- Business Risk Reduction: Changes in breach frequency, remediation windows and compliance violations.
- Maturity Progression: Stages from pilot to full integration and continuous optimization.
Key Limitations and Risk Considerations
AI agents offer transformative potential but present inherent risks:
- Data Quality Constraints: Inaccurate or biased inputs lead to flawed outputs.
- Automation Bias: Overreliance without human validation can exacerbate errors.
- Adversarial Manipulation: Attackers may probe and evade agent logic without adversarial testing.
- Scalability vs Precision: Simplifying models for scale may reduce detection fidelity.
- Vendor Lock-In: Proprietary platforms can hinder future innovation and increase costs.
Phased Adoption Roadmap
Industry leaders recommend a phased approach to integrate AI agents effectively:
- Conduct a readiness assessment, aligning AI objectives with risk priorities.
- Launch targeted pilots in high-impact use cases such as anomaly detection and automated triage.
- Establish cross-functional governance bodies for policy, validation and ethical oversight.
- Scale deployment iteratively, investing in data infrastructure, talent and platform integration.
- Embed continuous feedback loops driven by performance metrics, user feedback and threat intelligence.
By aligning strategic insights with pragmatic execution, organizations can embed AI agents as integral pillars of their security and risk management ecosystem, balancing innovation with governance to achieve resilient, adaptive defenses.
Chapter 2: Threat Detection and Predictive Analytics Agents

Security Operations Evolution and Market Drivers
Over the last two decades, security operations have transitioned from perimeter-centric defenses—firewalls, intrusion prevention systems, antivirus—to intelligence-driven, proactive postures. Traditional controls depended on static rule sets and known signatures, protecting defined network edges. With the advent of cloud computing, mobile devices, remote workforces, and IoT proliferation, the security boundary has dissolved. Attackers exploit zero-day vulnerabilities, encrypted channels, and living-off-the-land techniques to bypass legacy defenses. In response, enterprises must achieve continuous visibility and resilience across hybrid architectures.
Several market forces are accelerating this transformation:
- Digital Transformation: Large-scale adoption of public and private clouds, microservices, and containerization requires holistic monitoring and dynamic policy enforcement across distributed assets.
- Regulatory and Compliance Pressure: Frameworks such as GDPR, CCPA, PCI DSS, and sector-specific mandates impose stringent requirements for data protection, breach reporting, and audit trails.
- Talent Shortages: A global cybersecurity skills gap limits the capacity of security operations centers (SOCs) to manually investigate alerts, driving automation to augment human expertise.
- Threat Complexity: Advanced persistent threat actors, ransomware gangs, and supply-chain attackers deploy multi-stage campaigns requiring rapid detection and containment.
- Data Proliferation: Exponential growth in telemetry from endpoints, applications, network devices, and OT sensors overwhelms manual processing capabilities.
- Cost Optimization: Organizations seek to reduce total cost of ownership by consolidating disparate security tools into integrated platforms and leveraging machine learning to streamline processes.
These dynamics have spurred next-generation security platforms—XDR, SOAR, threat intelligence systems—that incorporate artificial intelligence and machine learning. While these platforms improve coordination, many SOCs still face high alert volumes, lengthy investigation cycles, and inconsistent risk prioritization. Embedding autonomous AI agents into security ecosystems enables closed-loop workflows that ingest data, analyze signals, make decisions, and automate remediation. This agent-centric model unlocks scalable, adaptive defenses capable of responding to evolving threat vectors in real time.
AI Agent Framework and Integration
An AI agent within a security ecosystem is an autonomous software entity that perceives its environment, analyzes telemetry, learns from data, and takes actions. A comprehensive agent framework comprises:
- Perception Modules: Agents collect and normalize heterogeneous data—logs, network flows, endpoint sensor readings, identity management events, vulnerability feeds—through parsers, collectors, and enrichment engines. Data is structured and tagged to support downstream analysis.
- Analytical Core: Machine learning techniques—supervised, unsupervised, reinforcement learning—operate alongside statistical engines and heuristic rules. These components detect anomalies, profile behaviors, and forecast attacker tactics. Deep neural networks, autoencoders, clustering algorithms, and time-series models collaborate to refine detection accuracy.
- Decision Layer: Policy engines and probabilistic scoring mechanisms evaluate risk thresholds, context, and business impact. Decision logic orchestrates whether to escalate alerts, initiate automated containment, or continue monitoring. Human-defined playbooks integrate with adaptive policies to maintain governance and oversight.
- Action and Orchestration Interfaces: Agents interface with security controls—next-generation firewalls, endpoint protection platforms, cloud security APIs, identity providers—and with SOAR engines to execute remediation steps. Playbooks define multi-stage workflows across tools, ensuring coordinated response.
- Learning Feedback Loop: Outcomes of automated actions, analyst investigations, and post-incident reviews feed back into training pipelines. Reinforcement learning and model retraining reduce false positives and improve detection of emerging threats.
In an integrated ecosystem, specialized agents—threat-hunting assistants, vulnerability scanners, insider-risk monitors—operate concurrently at network, endpoint, identity, and application layers. They publish insights to a centralized orchestration platform, enabling situational awareness and granular control. This modular architecture augments human analysts, reduces manual toil, and delivers repeatable, consistent outcomes.
Anomaly Detection and Predictive Model Evaluation
Anomaly detection and threat forecasting models are the analytical backbone of proactive defense. Security teams, data scientists, and risk managers evaluate these models by both theoretical soundness and real-world performance. Model categories include:
- Supervised Classification Models: Algorithms such as decision trees, random forests, support vector machines, and deep neural networks trained on labeled datasets distinguish malicious from benign events with high precision, given quality labels. However, they may falter when encountering novel threats.
- Unsupervised and Semi-Supervised Techniques: Clustering, density estimation, and autoencoders learn normal behavior profiles and detect outliers without extensive labeling. Semi-supervised methods combine limited labeled samples with abundant unlabeled data to improve sensitivity.
- Statistical and Rule-Based Models: Z-score analysis, moving averages, time-series decomposition, and threshold-based heuristics offer interpretable detection of deviations from historical baselines.
- Time-Series Forecasting: ARIMA, exponential smoothing, and state-space models forecast key metrics—network traffic, system calls, user logins—and flag deviations as early warnings.
- Hybrid and Ensemble Frameworks: Layered pipelines integrate supervised classifiers, unsupervised detectors, and forecasting models to address varied threat characteristics and reduce blind spots.
Rigorous validation ensures model reliability. Key metrics and practices include:
- Confusion Matrix Analysis: Measuring true positives, false positives, true negatives, and false negatives to compute precision and recall.
- F1 Score and Fβ Measures: Balancing precision and recall according to cost of missed threats versus false alarms.
- ROC AUC: Evaluating trade-offs between true positive rate and false positive rate across thresholds.
- False Positive Rate and Alert Fatigue Metrics: Tracking proportion of low-risk alerts to maintain SOC efficiency.
- Detection Latency (Time-to-Detect): Measuring delay between anomaly onset and alert generation to minimize dwell time.
- Precision at K (P@K): Assessing accuracy within top-ranked anomalies to focus analyst effort.
- Cross-Validation and Bootstrapping: Ensuring generalizability and confidence intervals for performance metrics.
Security environments evolve rapidly, necessitating drift detection and bias mitigation. Techniques such as synthetic minority oversampling (SMOTE) and cost-sensitive learning address class imbalance, while continuous drift monitoring dashboards trigger retraining of models when data distributions shift. Interpretability frameworks—feature importance ranking, SHAP values, LIME explanations, rule extraction via decision trees—provide transparency for governance and build analyst trust.
Integration with SIEM and SOAR platforms enhances operational value. For example, IBM Security QRadar Advisor with Watson and Splunk Phantom ingest anomaly scores into centralized dashboards and automate incident response playbooks. Proprietary solutions like Darktrace Enterprise Immune System use unsupervised pattern discovery to detect novel threats in network telemetry. Security data scientists emphasize custom feature engineering, enriching models with threat intelligence feeds, vulnerability metrics, and user behavior logs to improve detection fidelity.
Strategic model selection involves trade-offs:
- Balancing Sensitivity and Specificity: Defining acceptable false positive rates against risk tolerance and resource capacity.
- Resource Allocation: Assessing in-house development costs versus off-the-shelf solutions, factoring expertise, data labeling, and validation processes.
- Governance and Compliance: Ensuring model decision trails and explainability meet regulatory requirements for audit and reporting.
- Vendor versus In-House Expertise: Choosing between managed detection services for rapid deployment and internal teams for deeper customization and control.
Operational Scenarios for Threat Forecasting
Threat forecasting provides strategic foresight by transforming real-time telemetry into predictive insights. Key operational scenarios include:
Network Security Operations
Forecasting engines analyze streaming flow data, endpoint logs, and vulnerability disclosures to project attack vectors and exploitation probabilities. SOC teams use severity forecasts to prioritize investigations, adjust sensor thresholds, and allocate analyst shifts. Scenario-based workshops map high-confidence predictions to containment playbooks using MITRE ATT&CK taxonomies, ensuring actionable intelligence.
Fraud Monitoring in Financial Services
Transaction monitoring agents synthesize sequential payment data, customer profiles, device fingerprints, and external economic indicators to estimate fraud likelihood. Outputs presented as risk bands drive proactive rule updates, credit limit adjustments, and customer re-authentication. Forecast models also support regulatory stress tests by simulating loss scenarios under varying market conditions.
Supply-Chain Risk Assessment
Forecasting bots ingest supplier performance metrics, open-source intelligence, and logistics data to predict disruptions—from component shortages to cybersecurity breaches in vendor networks. “If-then” impact matrices link forecasted risks to operational outcomes, guiding procurement strategies, alternative sourcing, and contingency budgeting.
Cloud and Hybrid Infrastructure Monitoring
Agents reconcile telemetry from public clouds—AWS, Azure, Google Cloud—and on-premises systems to forecast misconfigurations, emerging container vulnerabilities, and anomalous identity activities. Forecast outputs feed adaptive policy engines that dynamically enforce security controls, aligning with DevSecOps pipelines and continuous integration workflows.
Identity-Centric Forecasting
User and entity behavior analytics track login patterns, access requests, and device usage to forecast credential compromise or insider malicious activity. Risk trajectories—gradual deviations from historical baselines—trigger adaptive authentication and access reviews, balancing security and user experience.
Industrial Control Systems and Operational Technology
Forecasting in OT environments combines sensor readings, command logs, and maintenance histories to anticipate equipment failures or cyber-physical attacks. Cross-disciplinary teams use risk matrices mapping probability against safety, production, and compliance impacts. Predictions inform preventative maintenance schedules and isolation of critical subsystems.
Third-Party and Ecosystem Monitoring
Agents monitor vendor breach disclosures, patch cycles, and financial health metrics to forecast third-party risk exposure. Composite risk indices inform vendor scorecards, contractual terms, and insurance strategies within a holistic ecosystem risk model.
Collaborative Forecasting and Intelligence Sharing
Federated learning and shared threat intelligence feeds enable organizations to collaboratively train forecasting models without exchanging sensitive data. Sector-specific taxonomies and joint governance frameworks expand horizon scanning capabilities and accelerate discovery of emerging threat patterns.
Strategic Insights and Critical Deployment Considerations
Threat detection and predictive analytics agents elevate security operations from reactive to anticipatory postures. Key strategic insights include:
- Comprehensive Data Ingestion: Broad coverage across network, endpoint, cloud, identity, and OT data to minimize blind spots while retaining signal specificity.
- Hybrid Model Portfolios: Combining supervised classifiers for known threats, unsupervised detectors for zero-day anomalies, and ensemble techniques for layered defense.
- Robust Validation and Metrics: Employing confusion matrix analysis, ROC AUC, detection latency, precision at K, and continuous drift monitoring to maintain model efficacy.
- Explainable and Transparent AI: Integrating SHAP, LIME, and rule extraction to satisfy audit, compliance, and executive reporting requirements, fostering trust in algorithmic decisions.
- Seamless Platform Integration: Leveraging open APIs and messaging protocols to connect predictive engines with SIEM, SOAR, ticketing, and orchestration systems, ensuring coordinated response.
- Governance, Privacy, and Ethics: Aligning data usage policies with GDPR, CCPA, and sector mandates; establishing oversight mechanisms to prevent misuse of predictive signals.
- Total Cost and Resource Planning: Accounting for infrastructure, data engineering, model management, and specialized talent in cost-benefit analyses and phased rollouts.
- Cross-Functional Collaboration: Bringing together security engineers, data scientists, threat intelligence analysts, legal, and business stakeholders to align analytic hypotheses with organizational risk appetite.
Industry Perspectives and Tool Integration
Security leaders emphasize vendor neutrality and open frameworks to avoid lock-in. Open source libraries such as scikit-learn, TensorFlow, and PyTorch enable custom model development, while managed solutions accelerate deployment. Benchmarking against datasets like UNSW-NB15 and KDD Cup provides reference points, but real-world complexity requires production validation. Integration ease—API support, connector availability, dashboard unification—influences tool selection. Platforms that offer threat intelligence fusion, behavioral analytics, and incident orchestration under unified interfaces deliver higher ROI. Vendors differentiate by offering prepackaged playbooks, enrichment connectors to threat intelligence feeds, and low-code interfaces for custom analytics. Organizations must weigh the flexibility of open source against the turnkey capabilities of commercial platforms, aligning choices with maturity levels and strategic roadmaps. Collaborative ecosystems, enabled by standards such as STIX/TAXII, facilitate sharing of indicators and contextual threat data across stakeholders.
Continuous Improvement and Governance
Continuous improvement requires establishing governance forums—analytics councils, security architecture boards—that oversee model performance reviews, change management, and risk appetite alignment. Documented processes for model versioning, incident feedback incorporation, and periodic audit ensure sustainable predictive security programs. Training for analysts and executives on interpreting model outputs and understanding algorithmic limitations fosters organizational readiness and accelerates adoption.
- Data Quality and Completeness: Centralizing telemetry in data lakes with standardized schemas to ensure reliable model inputs and avoid sensor blind spots.
- Model Bias and Concept Drift: Implementing continuous retraining pipelines and fallback anomaly detection for novel threats.
- Balancing False Positives and False Negatives: Calibrating thresholds to align with resource capacity and risk tolerance, with tiered alert strategies for high-confidence automation and human review of lower-confidence events.
- Performance and Scalability: Provisioning compute and stream processing platforms to sustain real-time inference at scale and minimize detection latency.
- Integration Complexity: Prioritizing architectural standardization and open interfaces to reduce friction in embedding predictive agents within existing workflows.
- Governance and Compliance: Establishing audit trails for model decisions, data retention policies, access controls, and anonymization techniques to adhere to privacy regulations.
- Ethical Oversight: Formulating clear policy guardrails to govern the use of behavior-based analytics and prevent discriminatory or intrusive outcomes.
- Resource and TCO Planning: Conducting rigorous cost-benefit analyses for software licensing, infrastructure provisioning, data engineering, and talent acquisition.
By embedding autonomous AI agents within a modular architecture and enforcing disciplined governance, organizations can automate routine security tasks, elevate threat awareness, and anticipate adversarial changes. Iterative proofs-of-concept, phased deployments, and continuous feedback loops anchor a resilient, adaptive defense posture capable of meeting evolving strategic and operational objectives.
Chapter 3: Automated Incident Response and Remediation Agents
Contextualizing AI-Driven Incident Orchestration
Over the last twenty years, incident response has evolved from manual playbooks and analyst-driven workflows into sophisticated, AI-augmented systems. Early security operations centers struggled under the weight of rising alert volumes and complex threats—polymorphic malware, fileless attacks and coordinated campaigns that moved at machine speed. Legacy rule-based systems could not adapt to novel tactics, leading to delayed containment and unaddressed risks. This urgency spurred the adoption of orchestration platforms and automation, paving the way for AI-driven incident orchestration.
AI-driven incident orchestration coordinates artificial intelligence agents to manage end-to-end response workflows. It extends traditional SOAR capabilities by embedding adaptive learning and contextual reasoning throughout the incident lifecycle—alert triage, threat enrichment, decision guidance, containment, remediation and post-incident analysis. This shift from static playbooks to intelligent workflows empowers organizations to ingest heterogeneous data, derive real-time insights and execute actions with speed and precision.
Architectural Foundations
An effective AI-driven orchestration platform comprises interdependent modules that work in concert to automate and refine response actions.
- Data Ingestion and Normalization: Aggregates telemetry from endpoints, networks, cloud services, identity systems and external feeds. Normalization engines convert disparate formats into a unified schema for downstream analysis.
- Analytics and Intelligence Layer: Employs supervised, unsupervised and reinforcement learning models to detect anomalies, enrich alerts with threat context and assign risk scores. Natural language processing parses unstructured threat reports and security bulletins.
- Decision Orchestration Engine: Coordinates response workflows by translating risk assessments into conditional tasks across detection, containment and remediation phases. It supports parallel execution, escalation protocols and dynamic playbook adjustments.
- Automation and Execution Modules: Interfaces with firewalls, endpoint detection and response agents, identity management and cloud platforms to carry out containment and remediation via robust API integrations.
- Feedback and Learning Loop: Captures outcomes from automated actions, analyst overrides and post-incident reviews. This loop continuously refines model parameters and decision thresholds to improve future response accuracy.
- Governance and Audit Framework: Logs agent decisions, executed actions and human interventions. Enforces role-based access controls, change management procedures and compliance reporting for transparency and accountability.
At its core, the platform harmonizes a rich tapestry of data—asset inventories, user identities, network flows, process behaviors and threat intelligence. Timely ingestion, deep contextual enrichment and high data integrity enable AI agents to generate multidimensional risk scores that inform precise, prioritized actions.
Adopting AI-driven orchestration addresses persistent SOC challenges:
- Alert fatigue mitigation through automated false-positive filtering
- Accelerated response via automated isolation of endpoints and revocation of compromised credentials
- Standardized protocols across global teams to ensure consistency
- Scalability to handle growing digital footprints without proportional headcount increases
- Continuous improvement driven by feedback loops that refine decision logic
Decision Frameworks for Automated Response
Incident response decision frameworks guide automated or semi-automated remediation actions along two primary axes: rule-based schemas and adaptive learning models, and the level of context awareness incorporated into decision logic.
Rule-Based Versus Adaptive Models
Rule-Based Logic
Encodes expert knowledge as if-then statements within static playbooks. It delivers predictability, ease of audit and regulatory compliance by executing predefined action sequences when alert conditions trigger. However, its rigidity can impede adaptation to novel attack patterns, requiring manual overrides or delayed responses.
Adaptive Learning
Leverages historical incident data, real-time telemetry and threat intelligence to evolve remediation strategies. Supervised and reinforcement learning enable systems to propose contextually relevant actions and reduce analyst fatigue. The trade-off lies in transparency: complex models may lack explainability, necessitating robust governance to maintain trust.
Interpretive Frameworks and Governance Hierarchies
Practitioners align decision logic to established frameworks for clarity and control:
- NIST Special Publication 800-61r2 to map automated actions onto preparation, detection, containment, eradication and recovery phases.
- MITRE ATT&CK to prioritize responses against high-impact adversary tactics and techniques.
A tiered approval hierarchy balances speed and risk:
- Tier 1 Automated Actions: Low-risk tasks like isolating endpoints or blocking malicious IPs, executed without human intervention.
- Tier 2 Analyst-Review Actions: Mid-risk measures such as applying host-based firewall rules or resetting credentials, requiring confirmation.
- Tier 3 Expert Approval: High-impact steps like system reimaging or network segmentation changes, reserved for senior analysts.
Integration with Security Orchestration Platforms
Security orchestration platforms provide the connective tissue for AI agents, standardizing data exchange, maintaining audit trails and enforcing policies. Leading solutions:
Experts assess platform capabilities by integration breadth, data model consistency, workflow flexibility, analytics and governance controls. They categorize AI agent integration maturity into three levels:
- Data-Centric Integration: Agents enrich incident records via APIs but remain external to core playbooks.
- Workflow Integration: Agents execute discrete tasks—alert triage, enrichment or containment—within orchestrated playbooks.
- Adaptive Orchestration: Agents autonomously adjust playbooks in real time, leveraging feedback loops to refine response sequences.
Deeper integration elevates agent autonomy—from classification to direct execution of containment actions—while orchestration platforms enforce guardrails through policy definitions, approval thresholds and exception handling protocols.
Vendor strategy influences integration decisions. A single-vendor ecosystem simplifies data schemas and support but may limit innovation. A best-of-breed approach fosters access to specialized tools at the cost of increased connector management. Industry standards such as STIX/TAXII, OpenC2 and MITRE ATT&CK enable interoperability by aligning data taxonomies and playbook development across diverse environments.
Comprehensive governance spans change management, performance monitoring, cross-functional communication and training. Integrated platforms become learning hubs where AI agents and security professionals co-evolve—tuning playbooks, optimizing hand-offs and updating threat models to sustain resilience.
Balancing Speed and Accuracy
Automated response demands a strategic calibration of speed to limit dwell time and accuracy to preserve operational continuity. Key insights include:
- Response latency directly impacts risk exposure; milliseconds matter in preventing exfiltration.
- Precision preserves business workflows and stakeholder trust by minimizing false positives.
- Dynamic calibration—continuous adjustment of thresholds based on feedback loops and performance metrics—is essential.
- Human-machine collaboration, with escalation protocols and in-the-loop checkpoints, delivers optimal outcomes.
- Governance and auditability underpin trust through transparent logging and explainable decision trails.
Analytical Frameworks
Practitioners employ quantitative models to guide response profiles:
- Delay-Cost Analysis: Weighs expected losses from delayed containment against costs of misdirected interventions to derive optimal latency targets.
- Confidence Threshold Optimization: Uses ROC and precision-recall curves to set dynamic confidence scores that trigger automated or human-reviewed actions.
- Risk Score Calibration: Aligns actions with contextual risk assessments—asset criticality, user profiles and threat intelligence—to prioritize high-impact events.
- Continuous Feedback Loops: Feeds outcomes of automated actions—successful containments, false positives or user impacts—back into learning models to self-optimize over time.
Governance, Limitations and Future Directions
Robust governance ensures automated interventions comply with policies, SLAs and regulatory constraints. Essential controls include role-based approval gates, transparent decision logs, human-in-the-loop controls for high-impact actions and legal reviews for compliance. Even advanced systems face inherent limitations:
- Data Quality and Context Gaps: Noisy or incomplete telemetry can misguide agents.
- Model Bias and Drift: Static training data may fail to represent evolving adversary tactics.
- Adversarial Manipulation: Attackers may probe response behaviors to induce false positives or evade detection.
- Operational Overhead: Continuous model retraining and governance reviews demand dedicated resources.
- Integration Complexity: Interfacing with legacy infrastructure and third-party services can introduce latency and misconfigurations.
Looking ahead, innovation will converge on:
- Adaptive Orchestration Engines that self-adjust policies and thresholds in real time through meta-learning.
- Contextual Policy Networks built on knowledge graphs to assess downstream impacts before executing interventions.
- Explainable AI Enhancements that generate natural language justifications for automated decisions to improve audit readiness.
- Collaborative Intelligence Ecosystems leveraging federated learning to share anonymized threat insights and response strategies across organizations.
By grounding AI-driven orchestration in a framework of architectural rigor, decision analytics, integration maturity and robust governance, security teams can accelerate response velocity without sacrificing precision—transforming incident management into a resilient, adaptive discipline.
Chapter 4: Vulnerability Assessment and Penetration Testing Agents
Evolution of Vulnerability Assessment and the Rise of Autonomous Discovery
Over the past two decades, vulnerability assessment has transitioned from intermittent manual scans and scheduled network sweeps to continuous, automated processes embedded within security operations. Early practices relied on manual penetration tests and periodic network scans, often leaving extended windows of exposure. As threat actors deployed automated scanners, exploit kits, and sophisticated chaining techniques, traditional tools—bound by predefined signatures and static rule sets—struggled to keep pace with distributed, cloud-native, and microservices architectures.
Modern enterprise infrastructures span on-premises data centers, multi-cloud environments, containerized applications, Internet of Things endpoints, and remote devices. Each introduces unique protocols, configurations, and threat vectors. The convergence of operational technology and information technology further expands the attack surface to include industrial control systems and embedded devices with real-world safety implications. The result is an imperative for security teams to adopt self-driving, adaptive, and context-aware vulnerability discovery.
Key market and operational drivers fueling this shift include escalating threat sophistication, continuous delivery in DevOps pipelines, talent shortages, regulatory mandates for timely remediation evidence, and the demand for real-time risk posture visibility. These forces converge to transform vulnerability assessment into an autonomous discipline that continuously identifies, correlates, and prioritizes vulnerabilities with minimal human intervention.
Core Mechanisms of AI-Powered Vulnerability Discovery
Asset Identification and Profiling
Autonomous agents maintain a dynamic inventory of hardware and software assets by ingesting telemetry from network sensors, endpoint agents, cloud management APIs, and container orchestrators. Machine learning models classify unknown devices based on network behavior, protocol fingerprints, and system metadata. This continuous profiling ensures that ephemeral workloads and rapidly changing resources never evade assessment.
Contextual Vulnerability Correlation
AI systems correlate scan results with threat intelligence feeds, exploit databases, and internal incident logs. Natural language processing analyzes vulnerability descriptions and advisories to surface active exploit campaigns targeting specific software versions. By filtering out low-risk findings, security teams focus on exposures most likely to be weaponized.
Risk-Based Prioritization and Scoring
Autonomous platforms assign risk scores using predictive algorithms that factor in asset criticality, network exposure, exploitability metrics, and historical incident data. Reinforcement learning refines these models over time, aligning remediation recommendations with observed outcomes. This approach mitigates alert fatigue by directing attention to high-impact vulnerabilities.
Analytical Foundations and Continuous Learning
Machine learning underpins each stage of autonomous discovery. Supervised models trained on historical scan data distinguish true positives from false alarms, while unsupervised clustering detects novel vulnerability patterns. Feature extraction algorithms identify subtle indicators of weakness, such as unusual port combinations and misconfigured access controls. Graph analytics map relationships among assets, vulnerabilities, and threat actors, enabling simulation of potential attack paths and proactive defense planning.
Feedback loops continuously refine analytical models. As remediation actions unfold, agents adjust scanning heuristics and prioritization criteria to enhance accuracy and reduce manual tuning efforts.
Defining and Evaluating AI Agents in Security Ecosystems
AI Agent Taxonomy and Frameworks
- Detection Intelligence: Ingest and correlate heterogeneous data sources to identify anomalies, signature deviations, and emerging attack patterns.
- Decision Orchestration: Apply rule sets, probabilistic models, or reinforcement learning to determine optimal response actions within contextual constraints.
- Autonomous Execution: Initiate containment or remediation tasks—such as endpoint isolation or firewall adjustments—with varying degrees of human oversight.
Industry frameworks such as the MITRE ATT&CK® matrix, Gartner’s SIEM maturity model, and the NIST Artificial Intelligence Risk Management Framework guide practitioners in mapping agent capabilities to strategic objectives and identifying gaps in control coverage.
Perspectives on Autonomy and Adoption Models
- Human-in-the-Loop: Analysts approve critical response actions, ensuring decisions remain traceable to input data and model logic.
- Adaptive Automation: Agents begin with low-risk tasks, such as alert triage, and progressively advance to automated remediation under strict guardrails.
- Full Autonomy: Agents manage end-to-end incident workflows independently in high-velocity threat environments, minimizing human latency.
Organizations deploy AI agents via three primary models:
- Center-Led Deployment: A centralized team pilots agents, develops best practices, and extends capabilities to business units.
- Federated Approach: Business units select and manage agents tailored to their risk profiles under overarching governance.
- Managed Services Partnership: External providers deliver AI-driven operations through platforms such as CrowdStrike Falcon or Palo Alto Networks Cortex XDR.
Performance Metrics and Key Indicators
- Detection Accuracy: True positive rate versus false positive rate against benchmark data sets or red-team exercises.
- Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR): Speed and efficiency in identifying and mitigating threats.
- Alert Volume Reduction: Percentage decrease in alerts requiring human analysis.
- Cost Avoidance: Financial impact of incidents prevented or contained by agent actions.
- Model Drift and Update Cadence: Frequency of retraining cycles to maintain detection fidelity.
Continuous Validation in Dynamic Environments
Continuous validation treats security as an ongoing assurance process that adapts to shifting configurations, application updates, and dynamic workloads. Unlike static scans, validation agents integrate with DevSecOps pipelines, container orchestration platforms, serverless architectures, and multi-cloud deployments to provide a real-time risk snapshot for informed prioritization.
By aligning with COBIT objectives and the NIST Cybersecurity Framework, continuous validation extends passive monitoring to proactive verification of control effectiveness. Agents act as automated auditors, evaluating infrastructure-as-code templates, container images, and runtime behavior against policy baselines.
Integration with Cloud Security Posture Management tools—such as Qualys Cloud Platform, Tenable.io, and Palo Alto Networks Prisma Cloud—enables machine learning-driven risk scoring across diverse cloud services. Shift-left validation embeds policy-as-code checks into build pipelines, preemptively reducing exposures before deployment.
Continuous attack surface mapping leverages network discovery, cloud API enumeration, and orchestration visibility to construct real-time asset inventories. Predictive models trained on historical exploit data forecast which vulnerabilities are likely to be weaponized—for example, Tenable.io’s Predictive Prioritization. Integration with threat intelligence feeds contextualizes findings with active exploit campaigns, enhancing the relevance of validation outputs.
Optimizing Coverage and Managing False Positives
Balancing Coverage Depth and Breadth
Effective assessment balances comprehensive visibility across networks, endpoints, applications, containers, and cloud services (breadth) with thorough protocol analysis, code-level review, and exploit simulation (depth). A tiered scanning strategy assigns high-depth, frequent assessments to mission-critical assets, while lower-priority resources receive broader, less intensive scans. Dynamic risk scoring frameworks adjust priorities in real time based on threat intelligence, business context, and historical patterns. Tools such as Rapid7 InsightVM and Tenable.io facilitate this adaptive scanning approach.
Risk-Based Remediation Workflows
Autonomous agents synthesize exploitability metrics, active threat feeds, and asset roles to generate prioritized remediation queues. Composite risk scores extend CVSS baselines with contextual modifiers—such as compensating controls and network segmentation—enabling cross-functional teams to allocate patches, configuration updates, or network isolations where they matter most.
Reducing False Positives and Alert Fatigue
Multi-stage validation pipelines cross-verify initial findings against threat intelligence databases, historical scan results, and behavioral telemetry. Correlation with evidence of active reconnaissance or exploit attempts filters out low-confidence alerts. Human-in-the-loop feedback refines detection heuristics and suppression rules, while detailed explainability—highlighting code injection vectors or affected libraries—accelerates triage.
Continuous Improvement and Governance
Metrics-driven programs track scanning accuracy, coverage gaps, and alert validation rates. Periodic recalibration of machine learning models ensures alignment with evolving threat tactics. Post-remediation data informs risk scoring refinements, closing the loop between assessment, remediation, and validation. Governance frameworks establish roles, escalation paths, and exception procedures, supplemented by manual reviews and red teaming to address blind spots.
Integration with Security Platforms
- SIEM: IBM Security QRadar Advisor with Watson
- SOAR: Splunk Phantom
- Ecosystem Orchestration: Cisco SecureX
- Asset and Ticketing Systems: Unified dashboards correlate vulnerability data with incident records and IT service management workflows
- DevSecOps Toolchains: Embedding scans in code repositories, build servers, and deployment pipelines
Strategic Value and Organizational Impact
Adopting autonomous discovery and continuous validation delivers accelerated detection cycles, improved accuracy, resource optimization, enhanced resilience, and measurable ROI. Security teams shift from reactive patch management to predictive risk control, strengthening board-level confidence and supporting compliance by demonstrating a mature, data-driven approach. Embedding these practices within enterprise risk management fosters cross-team accountability, aligns performance metrics—such as mean time to validation and control compliance rates—with strategic objectives, and sustains cybersecurity investments as digital environments evolve.
Chapter 5: Identity and Access Management Agents
Security Operations Evolution and Market Drivers
Over the past two decades, security operations have shifted from manual log reviews and rule-based intrusion detection to centralized SIEM platforms and SOAR solutions. However, the rapid adoption of cloud infrastructure, containerization, and distributed architectures has outpaced legacy tools. Market drivers accelerating this transformation include the expanding attack surface from cloud and IoT deployments, increasingly sophisticated threat actors, stringent regulatory mandates for continuous monitoring and real-time reporting, a global shortage of skilled security professionals, and the demand for cost efficiency and operational resilience. These forces have rendered manual processes and static rules insufficient, creating an imperative for solutions that learn from data, reason about novel threats, and orchestrate responses at machine speed. Autonomous AI agents in security and risk management represent this paradigm shift, promising proactive, adaptive protection rather than reactive defense.
Framing AI Agents in Security and Identity Ecosystems
An AI agent in security and risk management perceives its environment through diverse telemetry, analyzes threats with machine learning, decides on optimal response strategies based on contextual risk assessments, and acts by executing containment, remediation, or investigation workflows without explicit human intervention. These functional dimensions—perception, analysis, decision, and action—span a spectrum from specialized detection modules to comprehensive orchestration engines. Industry examples illustrate this range:
- Threat Detection Agents such as Darktrace Enterprise Immune System, leveraging unsupervised learning to identify emerging anomalies
- Predictive Analytics Agents like IBM Security QRadar Advisor with Watson, forecasting threat trajectories from historical patterns
- Incident Response Agents including Splunk Phantom and Palo Alto Networks Cortex XDR, orchestrating rapid containment and remediation
- Vulnerability Assessment Agents such as Rapid7 InsightVM, using machine learning to prioritize critical weaknesses
- Identity and Access Agents like Okta Adaptive MFA, enforcing dynamic authentication policies informed by behavioral intelligence
By mapping AI agents to these roles, security leaders can evaluate emerging technologies, understand integration points with existing platforms, and identify essential capabilities for modern attack surfaces.
Understanding Behavioral Biometrics in Adaptive Authentication
Behavioral biometrics analyzes patterns in human interactions—keystroke dynamics, mouse trajectories, touchscreen gestures, and application usage—to continuously verify identity. Unlike static credentials, behavioral signals provide ongoing, probabilistic risk indicators. Integrated into risk-based authentication frameworks, these signals enable adaptive policies that respond in real time to deviations from user baselines.
Analytical Frameworks and Model Interpretation
Behavioral models employ supervised learning, anomaly detection, and probabilistic scoring, often within a Bayesian framework or ensemble methods combining autoencoders, clustering algorithms, and support vector machines. Dashboards map risk scores to policy thresholds, enabling dynamic triggers such as step-up authentication or session termination. Built-in logging supports audit trails and post-incident forensics.
Evaluating Performance and Operational Viability
- Accuracy Metrics: False acceptance rate (FAR), false rejection rate (FRR), and equal error rate (EER) guide maturity assessments, with optimal EERs typically below 5 percent.
- Scalability: Solutions must handle millions of events across desktops, laptops, and mobile devices without performance degradation.
- Privacy and Compliance: Pseudonymization, consent management, and data minimization ensure alignment with GDPR, CCPA, HIPAA, and internal governance frameworks.
Policy Adaptation and Risk-Based Controls
Dynamic access control adjusts authentication requirements based on composite risk scores derived from behavioral anomalies, geolocation, device reputation, and network context. Policies evolve from silent monitoring for minor deviations to step-up challenges or session termination for high-risk events. Standards such as OpenID Foundation RBA and FIDO Alliance guidelines inform consistent implementations that uphold the principle of least privilege.
Key Performance Indicators
- Authentication Efficiency: Reduction in step-up challenges versus baseline multi-factor authentication rates
- Risk Mitigation Impact: Decline in account takeover incidents and fraudulent access events
- User Friction Index: Satisfaction scores and dropout rates during authentication flows
- Operational Cost Savings: Decreases in helpdesk tickets for password resets and access issues
- Compliance Alignment: Audit readiness and evidence of adherence to data privacy regulations
Challenges and Future Directions
Behavioral biometrics faces debates over model bias, adversarial resilience, and privacy impact. Continuous validation, bias audits, and red-teaming exercises mitigate these risks. Emerging trends include federated learning for privacy preservation, explainable AI for transparency, and converged risk scoring platforms that integrate behavioral, threat intelligence, and network telemetry. Solutions like BioCatch and BehavioSec exemplify advanced behavioral verification in practice.
Managing Privileged Access at Scale
Privileged Access Management (PAM) has evolved from siloed controls to a strategic, identity-centric discipline aligned with Zero Trust principles. Modern environments feature a proliferation of high-risk identities—human users, machine credentials, API tokens, and service accounts—across cloud services, microservices, IoT devices, and distributed workforces. Effective PAM at scale requires intelligence-driven frameworks that assess risk, enforce policies, and adapt in real time.
Risk Models and Core Capabilities
- Contextual Risk Scoring: Real-time evaluations of user behavior, session attributes, geolocation, and device posture guide access decisions.
- Just-In-Time Privilege: Temporary, task-bound credentials minimize the exposure from dormant accounts.
- Secrets Management Integration: Vault solutions centralize storage and rotation of secrets, as exemplified by HashiCorp Vault.
- Behavioral Analytics: Machine learning detects anomalous privileged activity—command sequences, lateral movements—flagging potential insider threats.
PAM Maturity Continuum
- Discovery and Inventory of all privileged identities, including embedded credentials
- Vault and Control via platforms such as CyberArk and BeyondTrust, with role-based access, rotation, and session recording
- Automation and Orchestration integrated with ITSM, DevOps pipelines, and cloud platforms for credential provisioning and policy enforcement
- Intelligent Threat Analytics leveraging AI to correlate identity signals and prioritize alerts
AI-Enhanced Privileged Access Management
Advanced PAM platforms discover new credentials in code repositories and cloud consoles, apply natural language processing to translate policy documents into enforceable rules, and embed behavioral scoring engines to contextualize sessions. Identity governance systems such as SailPoint and Ping Identity provide entitlement reviews and role mining, ensuring privileged roles align with business functions and segregation of duties requirements.
Governance and Compliance Integration
- Periodic Privilege Access Reviews to validate assignments against business needs
- Policy Change Advisory Boards balancing security objectives with operational requirements
- Risk Acceptance Processes for controlled exceptions with defined sunset clauses
- Continuous Improvement Cycles informed by post-mortem analyses and analytics
Regulatory mandates such as SOX, HIPAA, and PCI DSS drive the embedding of compliance controls into PAM policy engines and real-time dashboards, turning reporting exercises into integrated outcomes of intelligent access management.
Balancing Security with User Experience
Effective identity and access strategies achieve robust protection without undue friction. Core tensions arise between risk coverage and user fatigue, model accuracy and adaptation speed, privilege restriction and operational efficiency, and privacy safeguards versus observability. Addressing these tensions requires analytical frameworks and governance mechanisms that prioritize both security and usability.
Analytical Frameworks
- Risk-Based Authentication Matrix: Contextual signals determine authentication requirements, with continuous monitoring of false positive and false negative rates.
- User Friction and Adoption Scorecard: Metrics such as time-to-authenticate, failure rates, and support ticket volume correlate with security incident data to identify high-burden controls.
- Behavioral Drift Analysis: Tracking deviations in keystroke dynamics, mouse movement, and touch gestures to measure drift tolerance and maintain model sensitivity without lockouts.
Strategy and Governance Considerations
- Define a Friction Budget to quantify acceptable authentication steps per scenario
- Adopt Iterative Policy Refinement through cross-functional teams that integrate security, UX, and compliance perspectives
- Invest in Explainable AI Techniques to maintain transparency and regulatory auditability
- Implement Just-In-Time and Just-Enough Access workflows for temporary, context-driven privilege elevations
- Ensure Data Privacy and Ethical Use via anonymization, retention limits, and user consent protocols
- Align with Compliance and Audit Requirements through traceable logs of authentication events, risk scores, and policy decisions
Limitations and Potential Pitfalls
- Overfitting Behavioral Models can increase false negatives when user patterns evolve
- Shadow IT Evasion may arise if controls impose excessive friction
- Bias and Discrimination Risks require rigorous bias testing and diverse data sampling
- Integration Complexity with existing directories and platforms can introduce latency and failure points
- Over-Automation Without Oversight may reduce visibility into edge-case decisions; a hybrid human-in-the-loop model balances efficiency with accountability
Strategic Recommendations and Roadmap
- Establish Cross-Functional Governance with an IAM steering committee representing security, IT, legal, UX, and business units
- Conduct Risk and Usability Assessments mapping access scenarios by criticality and user group to set friction baselines
- Deploy Phased Pilots of adaptive authentication and behavioral analytics agents, tracking KPIs for security and user impact
- Implement Continuous Learning and Model Auditing with feedback capture, periodic drift detection, and retraining
- Optimize for Accessibility and Inclusivity by validating flows for diverse users and providing alternative access methods
- Align with Compliance and Privacy Mandates through documented data policies and auditable evidence generation
- Scale with Modular, API-Driven Architectures supporting OAuth 2.0 and OpenID Connect for extensibility
- Foster a Culture of User Trust and Transparency by communicating the purpose of adaptive controls and offering explanations for challenges
By integrating AI-driven detection, orchestration, and adaptive controls within a robust governance framework, organizations can secure digital assets while delivering seamless user experiences. This strategic approach positions security operations to withstand evolving threats, regulatory demands, and the complexities of hybrid environments, achieving resilience, efficiency, and user satisfaction in equal measure.
Chapter 6: Fraud Detection and Financial Risk Management Agents
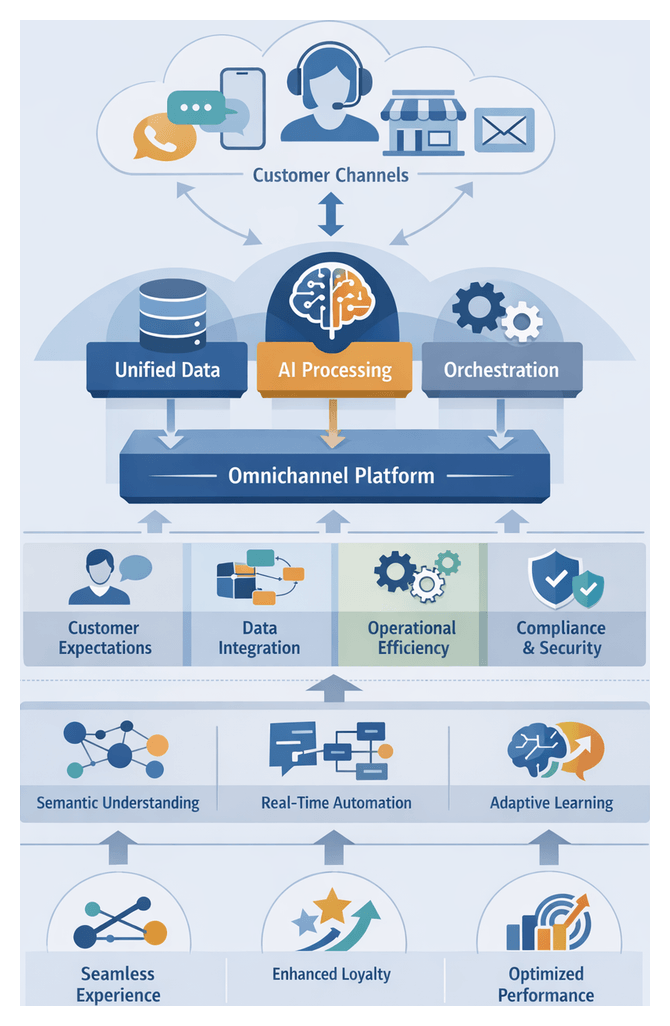
Security Operations Evolution and the Rise of AI Agents
Over the past two decades, security operations have progressed from manual log reviews, perimeter firewalls and signature-based antivirus tools to sophisticated, data-driven platforms embedding AI agents. Early teams manually correlated alerts from point solutions. As digital estates expanded across on-premises, cloud, mobile and IoT, organizations adopted SIEM platforms to centralize visibility but overwhelmed analysts with raw events and false positives. In response, security orchestration, automation and response solutions such as Splunk Phantom and Palo Alto Networks Cortex XDR introduced automated workflow integration. Yet static rules and playbooks still struggled to adapt to novel threats.
Today’s security leaders face relentless volume, velocity and variety of data, talent shortages and escalating compliance mandates. Adversaries leverage encryption, obfuscation and multi-stage kill chains that evade traditional defenses. To address these market drivers—escalating threat complexity, digital transformation, data proliferation, regulatory pressure and cost constraints—organizations are embedding intelligent, adaptive agents across security and risk workflows.
AI-driven platforms demonstrate this evolution. Darktrace Enterprise Immune System applies unsupervised learning to model normal network behavior and surface subtle anomalies. IBM Security QRadar Advisor with Watson enhances log analysis with natural language processing and cognitive reasoning. CrowdStrike Falcon leverages real-time endpoint telemetry and AI-based threat hunting to remediate malicious activity proactively. These agents process vast datasets, correlate disparate signals and deliver contextual alerts or automated actions with minimal human intervention.
Defining AI Agents in Security and Risk Management
Contemporary AI agents in security are modular, autonomous components that perceive data from diverse sources, reason about emerging threats and execute decisions within governance parameters. They go beyond scripted automation by integrating machine learning, natural language processing and probabilistic reasoning. Agents continuously ingest telemetry from network sensors, endpoints, identity systems and threat intelligence feeds, apply analytical models—from anomaly detection to causal inference—and recommend or enact containment, quarantine and remediation workflows.
Functional Taxonomy
Security and risk professionals categorize AI agent functions along two dimensions: analytic depth and operational scope. Four primary domains emerge:
- Sensing and Detection: Ingesting and correlating heterogeneous data to surface anomalies and indicators of compromise.
- Predictive and Forecasting: Applying time-series analysis, trend modeling and scenario simulation to anticipate emerging threats.
- Response and Orchestration: Translating analytic outputs into automated containment, policy enforcement or remediation actions.
- Governance and Compliance: Continuously auditing controls, mapping regulatory obligations and triggering policy adjustments.
Hybrid agents combine multiple domains and shift between advisory and execution modes based on risk severity. Collaborative ecosystems deploy specialized agents that coordinate via central orchestration layers, sharing situational awareness and delegating tasks dynamically.
Spectrum of Autonomy and Human Oversight
Agents operate along a maturity spectrum. In observability mode, they provide insights without intervention. In collaborative mode, they autonomously execute low-risk tasks—such as isolating compromised endpoints—while escalating high-impact decisions. In autonomous mode, agents self-initiate complex workflows under preapproved policies. CISOs assess readiness by evaluating policy clarity, risk appetite, staffing and audit capabilities. Phased adoption with transparent decision-making, explainability outputs and performance validation helps balance efficiency gains with accountability.
Real-Time Decisioning in Financial Systems
Financial institutions leverage real-time decisioning agents to evaluate risk and authorize or decline transactions in milliseconds. Faced with accelerating transaction volumes, sophisticated fraud schemes and stringent regulations, these agents have become strategic differentiators in customer experience, operational resilience and compliance alignment.
Deployment Scenarios
- Payment Gateways and Point-of-Sale: Agents assess authorization requests using historical payment patterns, device fingerprints, geolocation and behavioral signals.
- Online and Mobile Banking: Continuous monitoring of logins, fund transfers and account changes, correlating biometric and network intelligence to detect account takeover.
- Trading and Investment Platforms: Real-time flags for market-manipulation or wash-trading patterns to preserve market integrity.
- Lending and Credit Underwriting: Automated origination platforms evaluating applicant data, transaction histories and bureau insights for instant loan decisions.
Interpretive Frameworks
- Probabilistic Risk Modeling: Bayesian inference and logistic regression combine feature-level scores to yield interpretable risk contributions.
- Network and Graph Analysis: Graph metrics—such as centrality and community detection—identify collusive actors and money-laundering networks.
- Behavioral Pattern Recognition: Recurrent neural networks and autoencoders detect deviations in transaction timing, velocity and sequence.
Impact on Experience and Resilience
- Reducing Friction: Automated risk adjudication minimizes manual reviews and false declines, approving legitimate transactions in under 300 milliseconds.
- Adaptive Threat Response: Continuous ingestion of new fraud indicators and dynamic rule updates enhance resilience against zero-day scams.
- Operational Scalability: AI-driven platforms such as Feedzai and Featurespace provide elastic compute architectures, ensuring consistent latency during transaction spikes.
- Regulatory Compliance and Auditability: Solutions like FICO Falcon Fraud Manager embed explainability modules that attribute risk scores to specific transaction attributes.
Integration and Continuous Improvement
- Data Integration Layer: High-velocity streams from payment processors, fraud intelligence feeds and customer platforms must be normalized and unified.
- Model Governance Frameworks: Policies for validation, monitoring and retraining cadences align with Federal Reserve Model Risk Management guidelines.
- Cross-Channel Coordination: Unified orchestration platforms such as NICE Actimize share decision logic and case management across online, mobile and ATM channels.
- Feedback Loops: A/B testing and champion-challenger studies refine model parameters using outcomes from chargebacks and confirmed fraud cases.
Emerging Trends
- Generative Risk Simulation: Adversarial networks simulate novel fraud patterns to stress-test decision logic.
- Convergence of Fraud and Credit Risk: Unified risk scores reflecting transactional anomalies and creditworthiness.
- Federated Learning: Collaborative model training across institutions while preserving data sovereignty.
- Explainable AI: Investments in transparency frameworks to meet regulatory demands and mitigate bias.
Regulatory Frameworks and Model Governance
Financial services deploy AI agents under a complex regulatory landscape, including GDPR, PSD2, the Dodd-Frank Act, Basel III, OCC and CFPB guidance. These frameworks mandate data protection, consumer rights, transparency and robust risk management. GDPR’s “right to explanation” and PSD2’s Strong Customer Authentication rules drive architectures that combine predictive accuracy with auditability.
Explainability and Transparency
Balancing predictive power with interpretability leads to hybrid model designs. Pre-hoc methods—using transparent models such as generalized additive models or shallow decision trees—offer inherent clarity. Post-hoc techniques—employing SHAP or LIME—explain opaque models. Regulators require validation of explanation fidelity to ensure surrogate logic aligns with actual model behavior.
Auditability and Documentation
An unbroken audit trail must record every stage of the AI lifecycle. A model documentation dossier includes the agent’s purpose, data schemas, training methodologies, performance metrics, bias assessments, governance approvals and change logs. Versioned repositories enable rapid responses to regulatory inquiries and forensic analysis of false positive or unexplained decline events.
Ongoing Validation and Drift Monitoring
Continuous validation protocols detect model decay and emerging blind spots. Key performance indicators—true positive rate, false positive rate, precision, recall and AUC—are monitored in production. Predefined thresholds trigger retraining or retirement. Periodic back-testing against recent transaction data and simulated fraud scenarios exposes vulnerabilities to novel threats. Feature-level drift detectors flag shifts in transaction geographies, volumes or behavioral patterns, prompting governance reviews and data pipeline adjustments.
Governance Structures and Accountability
Formal governance models assign clear responsibilities across technology, risk and compliance functions. A Model Governance Committee oversees approvals, periodic reviews and incident escalations. Roles include Model Owners accountable for regulatory alignment, Data Scientists managing feature engineering, independent Model Validators conducting back-testing, Compliance Officers ensuring ethical guidelines and Audit teams reporting findings. Charters, SLAs and escalation procedures preserve accountability and enable rapid remediation of performance anomalies or compliance breaches.
Limitations
- Cross-Border Data Restrictions: GDPR and other data-sovereignty laws complicate global model training and dataset consistency.
- Black-Box Dependencies: Proprietary models hinder explainability and auditability, requiring contractual safeguards.
- Regulatory Divergence: Contradictory regional requirements increase compliance complexity.
- Bias and Fairness Risks: Historical data may encode socio-economic biases, demanding rigorous fairness assessments.
- Rapid Regulatory Evolution: Emerging AI governance proposals necessitate adaptable architectures.
Strategic Imperatives
- Embed compliance expertise into development teams to shape feature selection and algorithm choice from inception.
- Invest in centralized model registries and metadata platforms for automated lineage tracking and version control.
- Design modular architectures that separate inference engines from explanation, monitoring and reporting layers.
- Implement continuous learning programs for risk, compliance and data science professionals to stay current with AI ethics and regulatory guidance.
- Partner with vendors committed to transparent model pedigrees, explainability standards and collaborative governance.
By aligning agent design with regulatory requirements, maintaining robust documentation, and embedding continuous validation and governance, organizations can transform compliance into a strategic advantage and sustain resilient, accountable AI-driven risk management.
Chapter 7: Compliance Monitoring and Policy Enforcement Agents
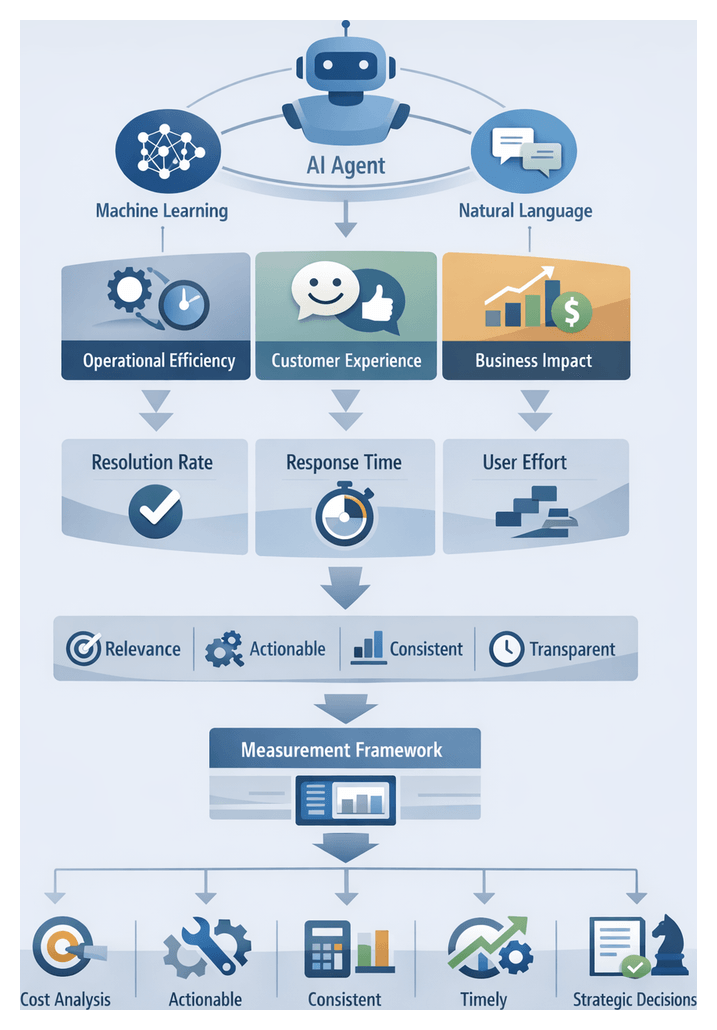
Automated Compliance Auditing Frameworks
Automated compliance auditing frameworks leverage artificial intelligence to transform periodic, manual audits into continuous, real-time assurance workflows. By integrating machine learning, natural language processing, and rule engines, these frameworks continuously ingest telemetry—from identity and access logs to configuration snapshots and security scans—and apply policy rules to detect deviations. This approach addresses the growing burden of overlapping mandates such as GDPR, CCPA, PCI DSS, and HIPAA, enabling organizations to identify gaps, generate evidence, and report findings with unprecedented speed and accuracy.
Early compliance efforts relied on spreadsheet checklists and quarterly reviews, struggling to keep pace with dynamic IT environments. The shift toward continuous controls monitoring began with GRC platforms that centralized policy repositories and basic automation. Advances in AI now allow systems to parse regulatory texts, translate requirements into machine-readable rules, and evaluate technical controls continuously. As a result, organizations move from sample-based audits to proactive, full-scope assurance.
Modern frameworks consist of three principal layers:
- Data Ingestion Layer: AI agents use connectors and APIs to normalize heterogeneous data—identity management logs, cloud configurations, network traffic—into a unified schema.
- Analytics and Rule Execution Layer: Rule engines evaluate control logic against live data streams. Machine learning models detect anomalies, while NLP modules interpret regulatory updates and map them to controls.
- Reporting and Remediation Orchestration Layer: Dashboards present compliance posture and risk scores. When deviations occur, AI-driven workflows assign remediation tasks and track resolution progress.
Key components include policy repositories tagged by jurisdiction and severity, control mapping modules that align requirements with technical configurations, evidence collectors that harvest snapshots and logs with integrity checks, continuous controls monitoring engines, and risk scoring systems that prioritize findings by impact and likelihood. Unified dashboards deliver real-time visibility for executives and audit committees, supported by narrative report generation that links regulations to evidence artifacts.
Organizations gain multiple benefits: efficiency gains of up to 70 percent in evidence collection, improved coverage through full-scope monitoring, faster response to violations, enhanced executive visibility, and scalable assurance without proportional increases in human resources. Leading solutions such as MetricStream and IBM OpenPages exemplify how AI agents streamline regulation interpretation, control testing, and continuous reporting.
Natural Language Processing for Regulatory Interpretation
Natural language processing (NLP) has become indispensable for mapping complex legal texts to actionable controls. Regulatory documents feature nested clauses, cross-references, and domain-specific terminology that require semantic parsing and reasoning beyond keyword matching. By adopting interpretive frameworks like IRAC (Issue, Rule, Application, Conclusion) and building domain ontologies, NLP systems extract named entities—actors, actions, objects—and establish logical relationships among provisions.
Ontologies underpin named-entity recognition and relation extraction, enabling AI agents to identify obligations, exceptions, and cross-references. Hybrid architectures overlay symbolic reasoning on statistical NLP outputs, improving traceability when, for example, an exception in one section negates a requirement elsewhere. Transformer-based models such as BERT variants fine-tuned on regulatory corpora capture long-range dependencies and handle multi-sentence inferences. Semantic similarity algorithms detect substantive amendments over time, focusing analyst attention on meaningful changes.
Performance metrics extend beyond precision and recall to include explainability and traceability. Composite evaluation frameworks integrate accuracy with auditability, requiring model outputs to carry confidence scores linked to source citations. Scenario-based testing and cross-domain validation ensure robustness across jurisdictions and regulatory domains. Human-in-the-loop governance remains critical: compliance and legal teams review model interpretations, maintain version control for ontologies, and log changes to training data.
Several platforms offer advanced regulatory NLP capabilities. Ascent RegTech provides machine learning-powered regulatory change management. Compliance.ai delivers regulatory intelligence that automates research and alerts. IBM Watson Discovery offers custom NLP model training and semantic enrichment for tailored compliance workflows.
Adoption decisions balance in-house development against commercial tools. Bespoke models can deliver tailored performance but demand significant data science investment. Third-party platforms accelerate deployment yet may pose integration and customization constraints. Future directions include generative AI for drafting compliance policies, adversarial testing frameworks to validate model resilience, and blockchain-integrated regulatory registries for real-time tracking of evidence.
Continuous Monitoring in Complex Environments
Continuous monitoring shifts compliance from periodic snapshots to ongoing visibility into control effectiveness across global, hybrid IT landscapes. Organizations face regulatory diversity—GDPR, country-specific data residency laws, PCI DSS, HIPAA—and technological heterogeneity spanning legacy systems, microservices, IoT endpoints, and SaaS applications. Data fragmentation and dynamic business processes further complicate assurance efforts.
Practitioners begin with ecosystem mapping to catalog assets, data flows, and critical control points. By overlaying risk-based regulatory requirements onto this map, teams prioritize monitoring where non-compliance carries the greatest impact. Analytical frameworks extend COSO, COBIT, and ISO 27001 models with dynamic elements:
- Risk-based Prioritization: Assign risk scores to controls and processes, directing monitoring agents to high-impact areas.
- Dynamic Thresholding: Use statistical process control and moving-window baselines to detect anomalies in evolving patterns.
- Event Correlation: Integrate SIEM data with compliance logs to identify cross-domain events indicating policy violations.
- Adaptive Alerting: Employ machine learning classifiers to filter noise, reduce false positives, and escalate genuine issues.
Process mining techniques reconstruct workflows from event logs, revealing deviations such as unauthorized access bypassing approval steps. Integration architectures vary between centralized hubs and federated data meshes. Platforms like IBM OpenPages, MetricStream, and Thomson Reuters Regulatory Intelligence offer connectors to ERP systems, cloud providers, SIEM platforms, and real-time event streams.
Continuous monitoring outputs serve diverse stakeholders:
- Regulatory Authorities: require auditable evidence, remediation records, and policy enforcement logs.
- Internal Audit: depend on dashboards showing control trends and exception logs for mid-cycle reviews.
- IT and OT Teams: need insights into configuration drift and security incidents intersecting with compliance.
- Executive Leadership: demand risk heat maps, key risk indicators, and assurance metrics aligned to business objectives.
High-variability environments present challenges: managing alert volumes to prevent fatigue, ensuring data integrity across diverse sources, adapting to regulatory updates in real time, and continuously evaluating control effectiveness. Techniques such as Bayesian threshold tuning and Plan-Do-Check-Act improvement loops help refine monitoring parameters and reduce false positives. Governance structures, like steering committees and compliance councils, validate that monitoring remains aligned to risk appetites and strategic priorities.
Real-world implementations illustrate value:
- A global bank reduced manual case reviews by 60 percent through machine learning–driven scoring of trade and access data.
- A manufacturing firm used process mining across eight countries to enforce procurement policies, cutting unauthorized spend by 15 percent.
- A hospital network integrated agents into its electronic health record system to flag anomalous patient data access, reducing privacy breach investigations by 40 percent.
Emerging trends point to predictive compliance, where monitoring agents forecast potential control failures and prescribe remediations. Generative AI may autonomously draft audit reports and policy updates, further enhancing agility. For security and risk leaders, embedding continuous monitoring into enterprise risk architecture is imperative to achieve resilient, compliant operations in an increasingly regulated landscape.
Accuracy, Audit Readiness, and Governance
Ensuring the reliability and audit readiness of AI-driven compliance mechanisms requires rigorous data governance, transparent logic, and collaborative oversight. Key practices include evidence mapping, continuous validation, and human-machine collaboration.
- Data Integrity and Lineage: Maintain governed data sources with metadata tracking to ensure audit evidence is traceable and reliable.
- Continuous Validation and Calibration: Regularly assess agent performance against regulatory and control objectives, recalibrating thresholds to accommodate organizational changes.
- Interpretability and Explainability: Provide natural language rationales and source citations to support audit inquiries and regulatory scrutiny.
- False Alert Management: Apply contextual risk scoring and threshold tuning to minimize noise and focus auditors on genuine compliance gaps.
- Regulatory Alignment Frameworks: Map outputs to standards such as COSO, ISO 19600, and NIST 800-53 for consistent audit traceability.
- Human-Machine Collaboration: Retain expert oversight to interpret nuanced obligations, validate agent recommendations, and ensure defensible decisions.
Practitioners must also navigate practical challenges:
- Complexity of Regulatory Texts: NLP engines may misinterpret ambiguous language or evolving provisions.
- Data Silos and Integration Overhead: Fragmented sources hinder seamless ingestion and real-time monitoring.
- Alert Fatigue and Response Capacity: Excess low-priority alerts can undermine trust and delay remediation.
- Evolving Regulatory Landscape: Jurisdictional differences and frequent updates demand continuous retraining and policy reengineering.
- Model Bias and Coverage Gaps: Limited training data can introduce blind spots in specialized domains.
- Audit Trail Completeness: Agents must produce immutable, timestamped artifacts for every decision to support formal audits.
To achieve audit preparedness, organizations should embed these strategic imperatives into governance frameworks:
- Evidence Mapping and Documentation: Define mappings between agent outputs, control requirements, and policy versions in centralized repositories.
- Automated Evidence Collection: Capture logs, configuration states, and exception reports in real time for rapid auditor access.
- Version Control and Change Management: Document policy updates and model retraining with formal approvals and timelines.
- Cross-Functional Collaboration: Align compliance, legal, IT, and audit teams to validate logic and prioritize enhancements.
- Periodic Third-Party Review: Engage external auditors to assess agent performance, bias risk, and interpretive accuracy.
- Governance Dashboards and Metrics: Track KPIs—false positive rates, policy coverage, remediation times—to support executive oversight.
Effective governance extends through the policy lifecycle and continuous improvement cycles:
- Policy Lifecycle Frameworks: Govern policy authoring, review, deployment, and retirement in sync with agent configurations.
- Model Governance Committees: Establish cross-functional bodies to oversee development, validation, and monitoring of AI models.
- Performance Assurance Processes: Conduct back-testing, simulations, and threshold tuning to validate agent effectiveness.
- Audit Trail Management: Enforce tamper-evident logging, immutable configuration snapshots, and secure archival of historical data.
- Feedback Loops: Enable auditors and users to report anomalies and suggest refinements, driving iterative model improvements.
- Regulatory Change Monitoring: Integrate intelligence feeds to flag updates and coordinate timely rule library enhancements.
Balancing technological innovation with disciplined oversight, organizations can harness AI agents to deliver continuous, accurate, and audit-ready compliance. By investing in data governance, transparent logic, and human judgment, security and compliance leaders will mitigate regulatory risk and achieve operational resilience in an increasingly complex environment.
Chapter 8: Behavioral Analytics and Insider Threat Detection Agents

Modeling User Behavior and Risk Profiling
Effective insider threat detection begins by capturing how legitimate users interact with systems under normal conditions and translating those patterns into dynamic risk profiles. Traditional perimeter defenses and static rules struggle to keep pace with hybrid environments, remote work and cloud adoption. User behavior analytics applies statistical methods and machine learning to model activity over time, enabling security teams to distinguish routine usage from anomalies that may signal malicious or negligent actions.
Leading platforms such as Securonix UEBA and Splunk UBA ingest terabytes of telemetry—authentication logs, file access events, cloud application telemetry, VPN sessions and privileged access requests—and normalize them into a consistent schema. Data ingestion pipelines leverage distributed frameworks to maintain fidelity and scale with organizational growth. Normalization yields unified fields (user identifier, timestamp, action type, resource) that feed downstream analytics.
Raw events are transformed through feature engineering, which distills inputs such as failed login rates, data transfer volumes and system access sequences into structured attributes. Contextual enrichment attaches metadata—user role, department, tenure, geolocation and device posture—creating a multi-dimensional feature set. This enrichment sharpens the differentiation between benign outliers and genuine risks.
Unsupervised learning methods cluster similar behavior patterns to establish baselines. Algorithms like k-means, DBSCAN and hierarchical clustering group users by activity distributions, while time-series analysis captures periodic patterns (daily logins, weekly report generation). Baseline models update incrementally to reflect seasonal trends and role changes, preventing outdated norms from triggering spurious alerts.
Risk scoring aggregates weighted anomaly indicators into a continuous metric. Each feature’s deviation from baseline contributes to an anomaly score, adjusted by historical reliability and asset criticality. Composite risk scores categorize incidents into severity tiers—informational, low, medium, high and critical—guiding response prioritization. Integration with SIEM and SOAR platforms enables automated workflows that triage and remediate incidents based on these scores.
Continuous feedback loops refine behavior models. Analyst verdicts (true positive, false positive, false negative) inform supervised retraining phases, adjusting feature weights and clustering parameters. Incident closure reports feed back into model updates, aligning profiles with evolving operational realities. Regular evaluation guards against concept drift and bias, ensuring risk profiles remain representative of current user habits.
Dynamic risk profiling empowers security operations centers to allocate resources proactively. High-risk users—those exhibiting unusual data access or policy violations—receive immediate scrutiny, while low-priority anomalies are deferred. Adaptive controls such as step-up authentication with Okta Adaptive MFA or session isolation are enforced when risk thresholds are breached. Executive dashboards display aggregated risk distributions, top drivers and remediation progress, informing strategic investments and compliance reporting.
Unsupervised Anomaly Detection Techniques
Unsupervised methods infer normal behavior from historical data and flag deviations without requiring labeled incident datasets. These techniques form a cornerstone of modern insider threat programs, capturing novel risk patterns that signature-based systems miss.
Clustering-Based Models
Clustering partitions data into groups of similar observations, establishing implicit baselines. Common methods include:
- k-means: Scalable and easy to tune according to organizational units, though it assumes convex clusters and requires a predefined k.
- DBSCAN: Density-based clustering that identifies dense regions and marks sparse points as anomalies, aligning well with network traffic analysis.
- Hierarchical clustering: Creates nested clusters, enabling inspection of anomalies at both global and departmental levels.
Clustering outputs integrate into SIEM platforms as risk indicators rather than stand-alone alerts. Domain context is essential: a small cluster of high-privilege administrators may be benign, whereas a solitary outlier performing similar actions warrants investigation.
Dimensionality Reduction and Reconstruction Models
Techniques such as principal component analysis (PCA) and autoencoders compress high-dimensional logs into latent representations. Reconstruction errors serve as anomaly scores:
- PCA: Transforms correlated features into orthogonal components. Deviations along low-variance components often signal unusual activity.
- Autoencoders: Neural networks that learn nonlinear reconstructions. Session reconstruction errors quantify divergence from learned norms.
- Variational autoencoders: Model data distributions probabilistically, enabling adaptive anomaly thresholds.
Alert thresholds are calibrated by monitoring reconstruction error distributions, balancing false positives and detection sensitivity. Contextual metadata—department, time-of-day, device risk—further refines prioritization.
Isolation Forest and Ensemble Methods
Isolation Forest isolates anomalies through recursive partitioning, yielding interpretable per-feature scores. Ensemble approaches combine outputs from clustering, reconstruction and isolation detectors, weighting each based on performance. Concordant signals across methods increase confidence and reduce alert fatigue.
Platforms like Darktrace Enterprise Immune System integrate probabilistic and pattern-based detectors in an ensemble, while Exabeam Smart Timelines reconstruct end-to-end user journeys and apply statistical and clustering detectors to highlight outliers.
Evaluation, Domain Adaptation and Calibration
Unsupervised model evaluation combines quantitative and qualitative frameworks:
- Statistical benchmarks: Monitor anomaly score distributions and detect concept drift.
- Expert validation: Analysts review high-score events to estimate true positive rates.
- Red-team exercises: Simulate insider scenarios to stress-test detection capabilities.
- Operational metrics: Track time-to-investigate and remediation efficiency.
Domain adaptation tailors models to industry contexts by incorporating domain-specific features (OT commands in manufacturing, transaction timings in finance), applying transfer learning to import pretrained detectors, and embedding policy constraints (allowed access locations or device types) early in the pipeline. Continuous calibration accommodates evolving work patterns and new collaboration tools.
Contextual Response Strategies
Contextual response strategies translate risk insights into calibrated actions that reflect user roles, data sensitivity and organizational priorities. Rather than uniform remediation, responses adapt to incident severity and business impact.
Analytical Frameworks
Key frameworks guide response orchestration:
- Risk-Based Prioritization: A dynamic risk score aggregates behavioral anomalies, asset value and impact, driving containment, notifications or enhanced monitoring.
- Situational Awareness: Contextual factors—time, location, project involvement—distinguish benign deviations from malicious intent.
- Adaptive Policy Mapping: Policies evolve through feedback loops, refining thresholds and controls as risk landscapes shift.
User and Data Context Interpretation
User context—role, tenure, baseline behavior—and data context—classification, ownership, regulations—are cross-referenced through a matrix to determine response levels. An engineer accessing a public code repository may trigger only an alert, whereas similar actions on a restricted design document prompt session lockdown.
Platforms such as Symantec Data Loss Prevention and Microsoft Purview Data Loss Prevention supply classification tags and policy definitions to response engines, ensuring controls align with compliance and business impact.
Enforcement via DLP and Endpoint Controls
Behavioral analytics agents collaborate with DLP and endpoint solutions to enact graduated controls:
- Session throttling: Limiting file transfers or clipboard operations on anomalous bulk exports.
- File quarantine: Moving sensitive documents to secure zones or requiring additional authorization.
- Credential revalidation: Prompting step-up authentication or temporary credential revocation.
Integration examples include Digital Guardian and CrowdStrike Falcon, which enable contextual triggers to enforce proportionate controls rather than enterprise-wide lockdowns.
Orchestration and Human-in-the-Loop
Contextual responses integrate into comprehensive workflows within platforms like Splunk Phantom and Palo Alto Networks Cortex XSOAR. Automated playbooks:
- Enrich incident tickets with user risk trajectories and data classification tags.
- Invoke multi-vector containment—network segmentation alongside endpoint restrictions.
- Notify compliance and HR teams when sensitive data is at risk.
Effective orchestration relies on standardized taxonomies and API-driven interoperability across detection, response and governance functions.
Governance, Feedback Loops and Continuous Refinement
Robust insider threat programs embed governance and ethical safeguards throughout their lifecycle. Cross-functional oversight, involving security, legal, compliance and HR, is essential to balance risk mitigation with employee privacy and organizational culture.
Key governance practices include:
- Policy transparency: Communicate automated action conditions to foster trust.
- Escalation protocols: Define human checkpoints for high-impact interventions like account suspension.
- Data retention and access controls: Secure behavioral telemetry in compliance with GDPR, HIPAA and other regulations.
Continuous refinement relies on feedback loops that integrate analyst verdicts and incident outcomes into model retraining. Active learning and semi-supervised feedback sharpen feature weights and clustering parameters, reducing false positives and adapting to concept drift. Regular privacy impact assessments, ethical oversight committees and audit trails for retraining decisions sustain trust and accountability.
Strategic Considerations for Insider Threat Programs
Behavioral analytics and insider threat detection agents offer transformative capabilities beyond perimeter defenses. Security leaders should adopt a holistic strategy that integrates advanced analytics, strong governance and cross-functional collaboration.
Strategic priorities include:
- Data quality and coverage: Establish thorough data inventories and integration strategies to eliminate blind spots from shadow IT and legacy systems.
- Model explainability: Ensure transparent scoring breakdowns that attribute risk drivers to specific behavioral features, supporting analyst trust and regulatory audits.
- Skill development: Invest in data science, security operations and change management training to sustain platform adoption and value delivery.
- Integration and interoperability: Coordinate behavioral analytics with SIEM, SOAR, IAM and DLP through standardized interfaces and workflows.
- Continuous performance evaluation: Monitor false positive rates, mean time to contain and business disruption metrics, feeding results back into analytical and policy refinements.
By weaving together analytical rigor, automated decisioning and ethical stewardship, organizations can elevate security operations into a proactive, risk-aware discipline. Insider threat detection agents become not only detectors of anomalous behaviors but orchestrators of contextually precise interventions that safeguard critical assets while preserving trust and productivity.
Chapter 9: Integration and Interoperability of AI Security Agents
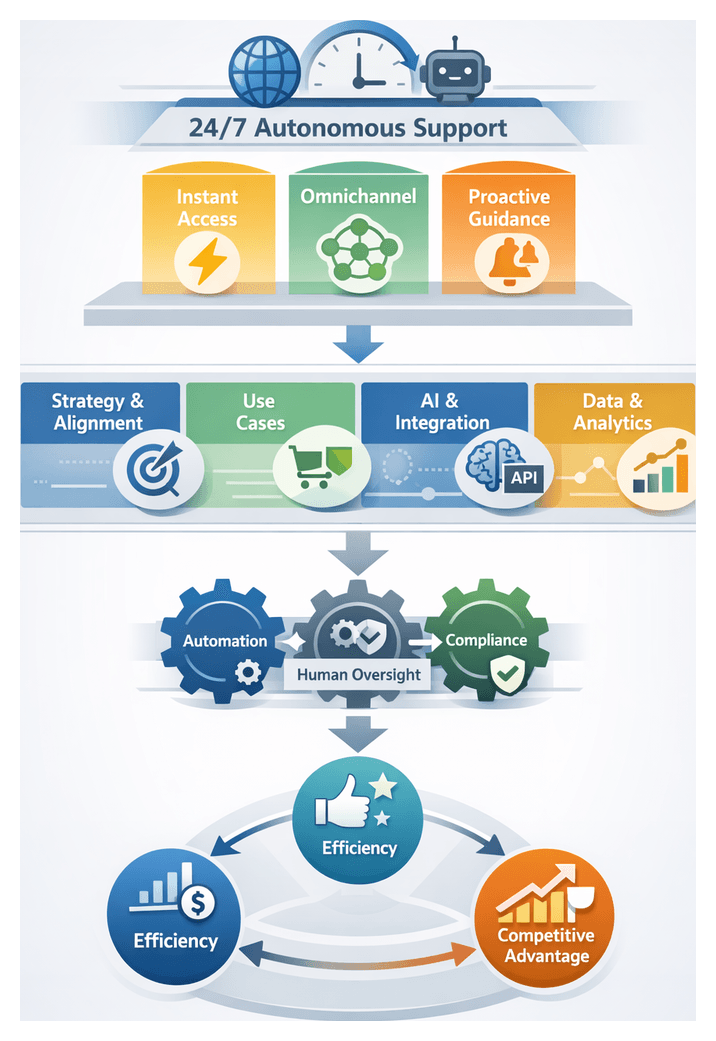
Contextualizing Interoperable Security Ecosystems
Modern security operations depend on a mosaic of specialized tools and platforms—threat intelligence services, endpoint detection agents, SIEM solutions, SOAR orchestrators, and compliance auditors. While each component addresses a distinct aspect of risk management, this diversity often yields fragmented data silos and disjointed workflows, hindering visibility across network, cloud, identity, and application domains. An interoperable security ecosystem dissolves these barriers by establishing a unified architecture in which AI-driven agents and platforms communicate through standardized interfaces and shared data models. This cohesion accelerates detection, enriches analysis, and automates response, reducing dwell time and enabling real-time coordination of defense actions.
Interoperability rests on three core attributes: modularity, scalability, and extensibility. A modular architecture decomposes security functions—data ingestion, threat scoring, incident orchestration, compliance auditing—into independent services with well-defined inputs and outputs. Scalability ensures performance under growing volumes of telemetry and evolving threat complexity. Extensibility allows for the rapid incorporation of new capabilities, from generative defenses and adversarial testing to advanced behavioral analytics. By embracing these principles, security architects can build ecosystems that adapt fluidly to organizational needs and threat landscapes.
Core Design Principles and Shared Standards
At the heart of interoperability lies a common framework governing data formats, communication protocols, and workflow orchestration. Adhering to an API-first development model, every agent and platform exposes consistent, well-documented REST or message-based interfaces that reveal configuration, telemetry, and action endpoints. Event-driven communication over message buses enables asynchronous exchange of security events, triggering automated and manual workflows without tight coupling. Centralized or federated normalization layers transform raw logs and alerts into a canonical schema—often defined by the Open Cybersecurity Schema Framework (OCSF)—so that all agents can fuse data across endpoints, network sensors, cloud audits, and identity systems.
Shared data models and industry standards are critical for semantic interoperability and ontological consistency. The Structured Threat Information Expression (STIX) and Trusted Automated Exchange of Indicator Information (TAXII) specifications establish a common vocabulary and transport mechanism for threat intelligence, while OpenC2 defines a universal language for security command and control. Common logging frameworks and schema definitions—implemented through JSON Schema or XML Schema—ensure that contextual information such as alert metadata, asset inventories, and course-of-action recommendations is uniformly understood and validated at each integration point.
- API-First Development: Publish versioned, machine-readable API contracts via the OpenAPI Specification.
- Event-Driven Architecture: Employ message brokers such as Apache Kafka or RabbitMQ for real-time event distribution.
- Data Normalization: Standardize telemetry through canonical schemas to support cross-platform analytics.
- Role-Based Access Controls: Enforce fine-grained permissions for both human users and agent identities.
- Idempotent Actions: Design automation commands to be safely repeatable and retriable.
- Observability and Monitoring: Integrate health checks, telemetry, and logging for all services and message queues.
Enabling Technologies and Frameworks
Implementing an interoperable ecosystem requires a technology stack that supports high-throughput event handling, containerized service management, and complex workflow coordination. Container orchestration platforms such as Kubernetes enable scalable deployment of individual security modules. Workflow engines like Zeebe and Camunda provide stateful orchestration of multi-step playbooks, handling conditional logic, human approval gates, and multi-source inputs.
For threat detection rule definition, the SIGMA project offers a vendor-agnostic language that can be translated into native queries for SIEM and endpoint platforms. Compliance monitoring benefits from standardized control definitions and assessment results via the NIST Open Security Controls Assessment Language (OSCAL). Together, these enabling technologies and frameworks accelerate integration, simplify continuous auditing, and support rapid iteration of security capabilities.
Standards for Data Exchange and API Governance
Shared standards and governance structures ensure that data exchanges preserve semantic clarity, maintain chain-of-custody, and support lifecycle management of interfaces. Semantic interoperability relies on formal ontologies like STIX 2.x for threat entities and relationships, as well as reference frameworks such as the NIST Cybersecurity Framework and ISO/IEC 27001 to align control taxonomies. Canonical data models, often defined via JSON Schema, enforce validation at the API boundary and reduce ambiguity when agents consume or emit structured messages.
Transport Protocols and Security
RESTful APIs over HTTPS remain the cornerstone for synchronous interactions, while pub/sub protocols such as AMQP, MQTT, or Apache Kafka excel at high-velocity event streams. Secure API interfaces employ OAuth 2.0 with JSON Web Tokens for scoped access and mutual TLS for service-to-service authentication. Payload integrity and confidentiality are ensured through JSON Web Encryption and JSON Web Signature, complemented by TLS certificate pinning. API management platforms enforce rate limiting, monitor usage patterns, and provide analytics for governance and compliance reporting.
Versioning and Lifecycle Control
Robust governance demands formal versioning strategies and deprecation policies. Semantic versioning (major.minor.patch) signals breaking changes, new features, and bug fixes, while deprecation timelines give integrators time to migrate. Compatibility matrices published in schema registries map supported versions between vendors and internal services, enabling coordinated upgrades. Cross-functional advisory boards review proposed changes, manage impact assessment, and maintain audit trails of policy metadata embedded within schema definitions.
Orchestrating Cross-Platform Threat Response
Cross-platform orchestration unifies detection and response across disparate security domains, transforming isolated alerts into coordinated defense actions. AI-driven agents normalize vendor-specific event schemas into a consolidated incident taxonomy and invoke playbooks that span network, endpoint, cloud, and identity controls. By adhering to STIX/TAXII for threat intelligence and OpenC2 for command messaging, orchestration layers remain vendor-agnostic and future-proof, allowing rapid integration of best-of-breed solutions.
Threat intelligence is enriched by ingesting external feeds—from commercial providers, open-source communities, or managed security service providers—and correlating them with internal telemetry. When a malicious indicator surfaces, the orchestration engine propagates enriched context to firewalls, cloud access security brokers, and identity management systems. AI-driven decision correlation applies machine learning to prioritize incidents based on asset criticality, business impact, threat actor profiles, and historical response outcomes, ensuring that high-risk events escalate to human analysts while routine containment actions deploy automatically.
In cloud-native environments, AI agents coordinate container image scanning, runtime protection, and dynamic network segmentation using platforms such as Palo Alto Networks Cortex XDR. For endpoint containment, integration with solutions like CrowdStrike Falcon facilitates automated quarantine and rollback sequences. In operational technology settings, orchestration workflows balance cybersecurity risk with process continuity, evaluating patch deployment and fail-safe triggers before any automated action.
Real-World Implementation Examples
A global financial institution deployed Splunk Phantom for security orchestration, integrating an AI-backed threat intelligence feed formatted in STIX/TAXII and behavioral analytics from Darktrace Enterprise Immune System. Automated playbooks contained anomalous lateral movement within minutes of detection, leveraging cross-domain insights to block malicious activity.
A multinational enterprise implemented Palo Alto Networks Cortex XSOAR as its central orchestration hub. By correlating endpoint telemetry, identity logs, and cloud workload metadata, the organization achieved unified incident management and automated response across on-premises and cloud environments.
In the public sector, agencies adopted IBM Security QRadar Advisor with Watson to ingest and normalize SIEM events, feeding enriched alerts into a custom policy engine that orchestrates remediation scripts. By standardizing on OCSF and OpenC2, development time for new integrations dropped by over 50 percent.
Challenges and Governance Considerations
- Legacy System Constraints: Proprietary protocols and limited APIs necessitate middleware or custom adapters.
- Data Privacy and Sovereignty: Cross-border exchanges require selective sharing, anonymization, and compliance with GDPR and similar regulations.
- Performance Overheads: Serialization, transport, and normalization of large event volumes can introduce latency; capacity planning is essential.
- Integration Security: Message buses and API gateways are high-value targets requiring strong encryption, authentication, and monitoring.
- Governance and Change Management: Clear ownership, version control, and schema registries prevent drift and ensure consistency.
Strategic Insights and Future Directions
Security leaders must view interoperability as a strategic competency rather than a technical feature. Embedding adaptive intelligence across perception, analysis, and action tiers accelerates risk assessment and response. A clear taxonomy of agent autonomy—predictive, prescriptive, adaptive—guides solution evaluation and aligns capabilities with organizational risk tolerance. Legacy, human-centric controls are insufficient against advanced, polymorphic threats; AI agents enable scalable defenses without proportional increases in headcount.
Emerging standards—such as CloudEvents for event envelopes, policy-as-code frameworks for centralized governance, adaptive schema discovery registries, and federated identity propagation—promise to enhance interoperability in multi-cloud, edge, and IoT deployments. GraphQL is under consideration for precise, nested data queries, though its adoption in security contexts hinges on finely grained access controls. Collaborative governance across industry consortia and open-source communities will determine the maturity and uptake of these innovations.
Guiding Reflections for Adoption
- How must existing workflows and governance structures evolve to accommodate autonomous decision-making?
- What quantitative and qualitative metrics will demonstrate ROI and risk reduction from AI-driven agents?
- Which data sources deliver the highest signal-to-noise ratio, and how will data governance ensure their integrity?
- What oversight mechanisms—dashboards, human-in-the-loop checkpoints, audit trails—are essential for trust and compliance?
- How will the organization manage the model lifecycle, including monitoring for drift, bias, and emerging threats?
- What cultural and skillset shifts are required to maximize the benefits of AI-driven automation?
Chapter 10: Future Trends and Ethical Considerations for Security AI Agents
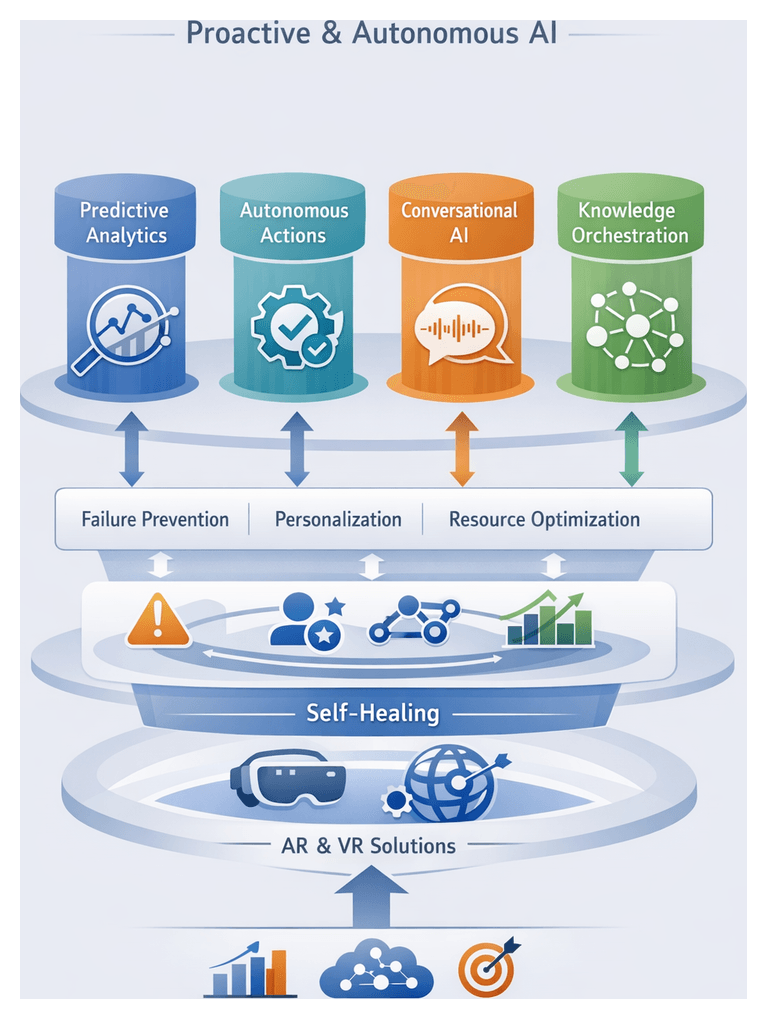
Security Operations Evolution and AI Integration
Over the past thirty years, security operations have transformed from manual, reactive processes into intelligence-driven ecosystems powered by artificial intelligence. Early security operations centers relied on perimeter defenses—basic firewalls and signature-based intrusion detection—and batch log reviews. As networks expanded and attack surfaces multiplied, Security Information and Event Management (SIEM) platforms emerged to centralize log collection and provide rudimentary analytics. However, the volume of alerts and false positives quickly overwhelmed analysts, leading to alert fatigue and delayed responses.
To address these challenges, the mid-2010s saw the rise of Security Orchestration, Automation, and Response (SOAR) solutions, which codified response playbooks, automated repetitive tasks, and integrated disparate tools into unified workflows. While SOAR improved efficiency, it remained bound by static rules and required ongoing tuning to keep pace with increasingly sophisticated threats.
The last five years have ushered in a paradigm shift as AI and machine learning augment security operations. Advanced analytics techniques—anomaly detection, behavioral profiling, and predictive threat intelligence—now power modern SOCs. User and Entity Behavior Analytics (UEBA) tools apply unsupervised learning to establish baselines of normal activity and identify deviations. Threat intelligence platforms leverage natural language processing to ingest and correlate data from open-source feeds, vulnerability reports, and dark-web monitoring. Leading solutions such as IBM Security QRadar Advisor with Watson and Palo Alto Networks Cortex XDR illustrate how machine learning models accelerate investigations, recommend remediation, and—even under predefined governance—autonomously contain threats.
By embedding AI-driven capabilities into security workflows, organizations reduce dwell time, compress mean time to detect (MTTD) and mean time to respond (MTTR), and strengthen resilience against polymorphic malware, advanced persistent threats, and multi-stage campaigns.
Market Drivers and the Shift to Proactive Security
Several market forces have converged to demand autonomous, intelligence-driven security solutions:
- Digital Transformation: Cloud migration, hybrid IT, and DevOps practices expand the attack surface, requiring real-time visibility and adaptive defenses.
- IoT and OT Proliferation: Connected devices introduce endpoints with limited security controls, amplifying risk and complexity.
- Remote and Distributed Workforces: The shift to remote work renders perimeter-centric defenses obsolete, driving identity-centric security.
- Cost Efficiency: Economic pressures compel optimization of resources, reduction of manual toil, and demonstration of measurable ROI.
- Advanced Threat Ecosystem: Nation-state actors and cybercriminals refine tactics, techniques, and procedures, necessitating proactive threat hunting and continuous learning.
- Regulatory Evolution: GDPR, CCPA, PCI DSS, HIPAA, and sector-specific mandates impose stringent monitoring and reporting requirements, stretching limited resources.
In response, security teams are transitioning from reactive, perimeter-focused operations to proactive, intelligence-driven postures. Autonomous AI agents ingest and normalize diverse data streams—network telemetry, endpoint logs, cloud APIs, and threat feeds—apply machine learning to detect anomalies and forecast breach scenarios, and recommend or execute containment actions. This shift enables organizations to anticipate threats, prioritize risk, and make autonomous decisions at machine speed.
Ethical Risk and Bias Mitigation in Security AI
As AI agents assume greater autonomy in security operations, evaluating and mitigating ethical risk and bias becomes critical. Practitioners frame ethical risk across five dimensions:
- Fairness: Ensuring agent decisions do not disadvantage particular user groups or demographics.
- Transparency: Providing interpretable explanations for alerts, risk scores, or automated responses.
- Privacy: Safeguarding sensitive data that agents consume and generate.
- Accountability: Establishing human oversight mechanisms and governance structures.
- Robustness: Minimizing unintended consequences and resisting manipulation through adversarial inputs.
Experts employ analytical frameworks to identify and quantify bias. Fairness metrics—demographic parity, equal opportunity, disparate impact ratios—evaluate detection rates across subpopulations. Adversarial testing uses synthetic or curated datasets to expose discriminatory behaviors. Comprehensive audit trails record model inputs, computations, and outputs, facilitating traceability. Stakeholder reviews by cross-functional teams interpret model behavior and surface latent biases. Standards such as NIST’s AI Risk Management Framework and IEEE’s Ethically Aligned Design guide continuous monitoring and inclusive data practices.
Transparency and explainability are addressed through local and global interpretability techniques. Tools like LIME (Local Interpretable Model-agnostic Explanations) and SHAP (SHapley Additive ExPlanations) derive feature attributions for individual decisions, helping analysts understand why an event was flagged. Simplified surrogate models or rule extraction methods provide high-level overviews of agent logic. Contextual dashboards correlate automated actions with user behavior logs or network traffic patterns, enabling security teams to validate rationale.
Products such as IBM Security QRadar Advisor with Watson incorporate explainability workflows with natural language summaries and statistical rationales. Similarly, Darktrace Enterprise Immune System offers visual AI insights mapping anomalies to underlying inferences, fostering trust among responders.
Effective bias mitigation requires robust governance structures that embed ethical considerations into AI lifecycles. Organizations adopt centralized AI ethics boards, distributed domain-specific guardianship, and external risk advisory councils. Leading firms publish AI principles and governance charters—Microsoft’s Responsible AI initiative and IBM’s AI Ethics Board exemplify public accountability.
Responsible AI policies across finance, healthcare, and critical infrastructure emphasize inclusive data practices, explainability requirements, continuous validation, and compliance alignment. Fraud detection platforms like CrowdStrike Falcon and Splunk Phantom align model governance with anti-money laundering regulations, ensuring alerts withstand audit scrutiny and uphold fairness obligations.
Mitigating bias involves trade-offs—performance versus fairness, explainability versus proprietary methods, resource allocation, and speed versus oversight. Security leaders integrate ethical metrics into key performance indicators to make data-driven decisions on acceptable risk levels and resource priorities.
Governance Frameworks for Autonomous Defense
Governance frameworks align autonomous defense capabilities with organizational objectives, ethical norms, and regulatory requirements. This dynamic system encompasses policy articulation, oversight modalities, and accountability flows. Policy articulation defines principles and risk appetite guiding AI decisions. Oversight modalities—human-in-the-loop, human-on-the-loop, and human-off-the-loop—determine when human intervention is required. Accountability flows ensure traceability from automated decisions back to responsible actors.
Human-in-the-loop models combine real-time human checkpoints with agent recommendations, offering control at the cost of latency. Human-on-the-loop delegates routine triage and containment to agents while reserving escalation authority for humans, balancing speed and oversight. Human-off-the-loop models authorize agents to execute predefined actions autonomously, maximizing responsiveness but requiring robust preauthorization and calibrated risk tolerance. Many organizations adopt hybrid strategies, dynamically adjusting oversight based on context.
Regulatory imperatives shape governance frameworks across domains. Financial institutions align with Basel Committee and Anti-Money Laundering directives, demanding audit trails and explainability. Energy and utilities comply with NERC CIP standards, integrating autonomous agents with operational technology governance boards and fail-safe measures. Government and defense agencies follow rigorous accreditation processes and continuous authorization reviews under frameworks like the U.S. Department of Defense’s Risk Management Framework (RMF).
Interpretive frameworks harmonize cyber risk management with AI ethics. NIST’s Cybersecurity Framework (CSF) functions—identify, protect, detect, respond, recover—are augmented by the AI Risk Management Framework, emphasizing fairness, transparency, and accountability. ISO/IEC 27001 integrates with ISO/IEC 42001 on AI management systems, while the EU AI Act prescribes risk-based governance measures. Industry consortia such as the Open Group and IEEE contribute reference architectures and ethical AI principles, advocating continuous monitoring, periodic audits, and stakeholder engagement.
Governance extends beyond technical rules to cultural and organizational dimensions. Autonomous defense agents shift roles from hands-on incident management to oversight and strategic coordination, requiring AI literacy, data ethics acumen, and systems thinking. Cross-functional governance committees—security operations, legal, compliance, risk management, and business units—review agent performance metrics, policy adherence, and updates, fostering shared responsibility and adaptability.
Boards and executive leadership demand quantifiable metrics—mean time to detection, false action rate—that reflect both operational effectiveness and governance maturity. Cyber insurance premium models now account for AI-driven defenses, adjusting based on governance practices. Providers like Darktrace Enterprise Immune System and IBM Security QRadar Advisor with Watson differentiate through integrated governance capabilities, linking performance dashboards to compliance modules and audit trails.
Emerging trends in governance include continuous validation, self-assessment mechanisms, and governance fabrics using distributed ledger technologies for immutable decision records. Governance orchestration platforms automate policy distribution, role-based access controls, and exception workflows. Industry consortia aim to establish shared benchmarks, threat intelligence exchanges, and certification schemes for autonomous defense.
Strategic Roadmap for Responsible Deployment
Deploying AI agents in security operations requires a structured roadmap that balances innovation with oversight. The following guiding principles and phased approach help organizations manage risks, build stakeholder confidence, and maximize value.
Guiding Principles
- Alignment with Objectives: Map AI initiatives directly to enterprise risk priorities, regulatory requirements, and business outcomes to avoid siloed experiments.
- Transparency and Explainability: Use interpretable models—whether rule augmentation in IBM Security QRadar Advisor with Watson or custom detectors—so teams can investigate alerts, support audits, and refine policies.
- Risk-Based Iteration: Adopt agile, risk-informed cycles. Pilot early under controlled conditions, validate assumptions, and shape subsequent phases to avoid overcommitment to unproven architectures.
- Cross-Functional Collaboration: Involve security architects, data scientists, legal advisors, and business stakeholders to ensure privacy, compliance, and operational constraints inform model design and response playbooks.
- Continuous Monitoring and Adaptation: Incorporate metrics for performance degradation, drift detection, and feedback loops to capture emergent risks, model inaccuracies, and adversary tactics.
Implementation Phases
- Phase 1: Assessment and Alignment: Perform a gap analysis of controls, response processes, and data availability. Identify priority domains—endpoint detection with CrowdStrike Falcon or identity verification via Okta Adaptive MFA. Engage legal and compliance to surface regulatory constraints.
- Phase 2: Pilot and Validation: Develop prototype agents for constrained use cases—network anomaly detection or high-volume alert triage. Establish evaluation criteria for detection accuracy, false positives, explainability, and overhead. Use sandbox or isolated segments to measure impact safely.
- Phase 3: Scaling and Integration: Expand deployment across adjacent domains and integrate with SIEM, SOAR, or vulnerability management tools such as Rapid7 InsightVM. Standardize data schemas and APIs for interoperability, and define escalation paths for human analysts to override or refine actions.
- Phase 4: Governance and Continuous Improvement: Establish an AI security council to oversee model updates, policy revisions, and compliance. Implement automated checks for model drift, bias indicators, and emerging threats. Allocate resources for adversarial research and next-generation defenses.
Key Considerations and Limitations
- Model Bias and Fairness: Audit outcomes with bias assessment frameworks to prevent skewed detection performance.
- Data Quality and Provenance: Ensure accurate metadata, time synchronization, and taxonomies. Incomplete logs degrade algorithms and raise false positives.
- Adversarial Adaptation: Integrate adversarial testing—simulating polymorphic malware and data poisoning—to validate resilience.
- Regulatory Fragmentation: Maintain a regulatory matrix to track GDPR, CCPA, PSD2, and sector-specific mandates for data handling and enforcement actions.
- Operational Complexity: Prioritize interoperability and centralized orchestration to avoid conflicting directives from multiple agents.
- Skill Gaps and Change Management: Invest in training and recruit machine learning and threat intelligence experts to support data-driven security culture.
- Technical Debt and Maintainability: Use disciplined code reviews, modular architectures, and version control to reduce long-term debt and enable agile adaptation.
Future Outlook and Adaptive Mindset
The boundary between human and machine decision-making will further blur as AI agents mature. Organizations with an adaptive mindset—continuous experimentation, robust governance, and cross-disciplinary collaboration—will excel. They will leverage generative defenses that synthesize countermeasures to novel attacks, integrate adversarial learning loops for near-real-time refinement, and adopt open standards and shared intelligence to amplify collective defense. Dynamic risk scoring and policy-driven intervention thresholds will balance autonomy with human oversight. Ultimately, responsible innovation in cybersecurity rests on continuous learning—technologically and organizationally—to stay ahead in the evolving threat landscape.
Conclusion
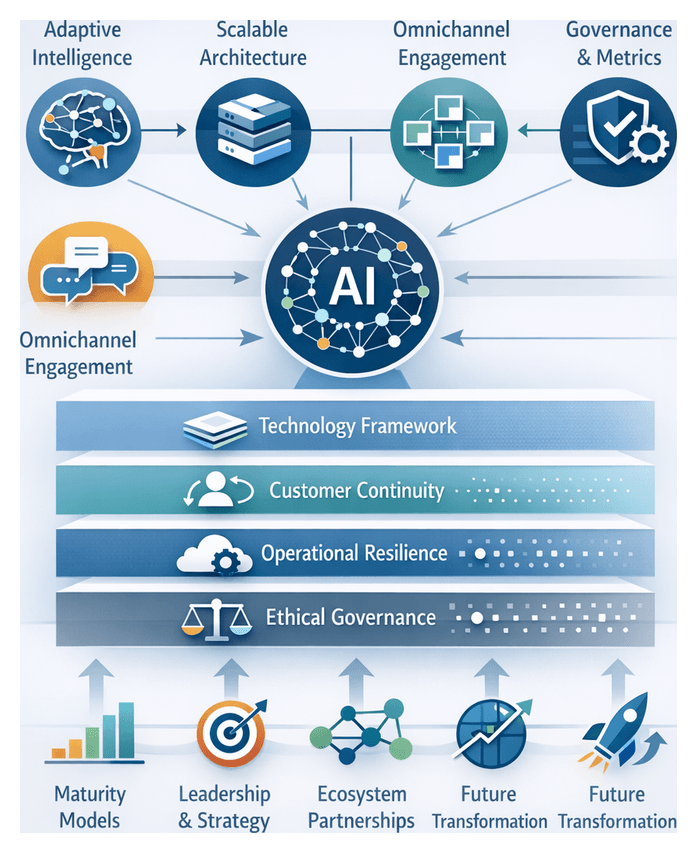
Synthesis of AI Security Agent Foundations
Modern security operations rest on a unified framework of autonomous AI agents that ingest data, generate intelligence, and execute remediation actions. Three architectural pillars drive these capabilities:
- Learning and Adaptation: Continuous ingestion of structured and unstructured data refines predictive models, updates threat signatures, and evolves decision policies to address emerging risks.
- Reasoning and Orchestration: Logic layers—from rule-based engines to probabilistic inference and reinforcement learning—correlate events, assess risk, and determine responses within governance boundaries.
- Action and Remediation: Automated workflows execute containment, mitigation, or escalation steps through APIs, orchestration platforms such as SOAR, or direct endpoint control, ensuring rapid and auditable interventions.
These pillars form a closed-loop system: learning updates reasoning, reasoning triggers actions, and action outcomes feed back into learning. This continuous cycle underpins adaptive defense at scale.
Building on this foundation, specialized agents address distinct security domains:
- Threat Detection and Predictive Analytics Agents analyze telemetry and external feeds to surface anomalies and forecast attack vectors.
- Automated Incident Response Agents orchestrate triage and remediation playbooks with contextual nuance.
- Vulnerability Assessment and Penetration Testing Agents use reinforcement learning for exploit simulations within DevSecOps pipelines.
- Identity and Access Management Agents enforce adaptive authentication and least-privilege policies through behavioral biometrics.
- Fraud Detection and Financial Risk Management Agents apply network analysis to transaction data for real-time anomaly scoring and compliance audit trails.
- Compliance Monitoring and Policy Enforcement Agents automate evidence collection and continuous control auditing via natural language processing of regulatory texts.
- Behavioral Analytics and Insider Threat Detection Agents model baseline user behavior with unsupervised learning to prevent data exfiltration.
- Integration and Interoperability Agents define data exchange standards and API frameworks to unify detection, response, and governance modules.
- Future Trends and Ethical Considerations explore generative defense, adversarial testing, and governance frameworks for transparency and accountability.
Emerging Patterns and Strategic Imperatives
Across domains, several cross-cutting themes guide the deployment and governance of AI agents:
- Analytical Frameworks: Risk-based prioritization quantifies impact and likelihood; trade-off matrices balance precision versus recall and speed versus accuracy; feedback-loop architectures ensure continuous improvement; contextual taxonomies delineate scenarios for autonomous action, human oversight, or hybrid collaboration.
- Integration and Ecosystem Thinking: Modular architectures and standardized interfaces (RESTful APIs, event streaming) enable plug-and-play interoperability. Shared data layers aggregate signals for real-time correlation, while orchestration hubs coordinate cross-domain playbooks.
- Balancing Automation with Human Oversight: Adaptive autonomy thresholds adjust to asset criticality and risk levels; explainability techniques support trust and audit readiness; role-based collaboration defines when agents triage alerts and when analysts assume investigation; escalation protocols codify severity thresholds and approval workflows.
- Data as the Central Nervous System: Heterogeneous source fusion, metadata-driven context, and governed data lifecycles ensure semantic consistency, quality assurance, and compliance across analytics models.
- Continuous Learning and Adaptive Resilience: Streaming analytics and incremental training update models in real time; scenario-based stress testing via generative adversarial techniques informs resilience planning; drift monitoring and stewardship guard against model decay; cross-domain threat intelligence accelerates multi-vector detection.
- Governance and Ethical Considerations: Ethical risk assessments evaluate privacy, bias, and societal impact; policy-driven control objectives codify standards (ISO 27001, NIST); accountability frameworks assign ownership and maintain immutable decision logs; stakeholder engagement models involve legal, compliance, and business leadership.
From these patterns, security leaders derive strategic imperatives:
- Invest in Data Quality and Integration: Establish robust pipelines, unify telemetry, and enforce governance.
- Adopt Phased Deployment: Start with high-value use cases—such as anomaly detection or automated patch validation—and expand iteratively.
- Govern with Transparency: Define decision thresholds, escalation paths, and human-in-the-loop reviews with explainability mechanisms.
- Foster Cross-Functional Collaboration: Align security, IT, risk, and business units around shared AI roadmaps.
- Prioritize Adaptability: Design feedback loops incorporating incident outcomes, red team insights, and threat intelligence.
- Align Investment with Outcomes: Track KPIs—mean time to detect, false-positive reduction, audit cycle times—to measure impact.
Agile Integration and Governance Transformation
Embracing organizational agility requires viewing AI agents as catalysts for continuous adaptation rather than static tools. Fluid teams monitor agent performance metrics and leverage real-time dashboards to refine policies, allocate resources dynamically, and anticipate new risks. Executive reviews focus on improvements in detection time, reduction in uncontrolled escalations, and resilience metrics.
Governance must evolve from manual rule enforcement to oversight of machine-driven policies. Three domains of transformation include:
- Policy Stewardship: Codify legal and ethical standards into model constraints and establish clear authority for updates.
- Performance Validation: Conduct ongoing audits of outputs to detect drift, bias, and unintended consequences, collaborating with data scientists and audit teams.
- Incident Accountability: Define post-event review boards to assign responsibility for agent actions and foster transparency.
Cross-functional collaboration ecosystems dissolve silos among cybersecurity, IT operations, risk management, legal, and business units. Tactics include:
- Shared data platforms for unified analysis of agent outputs
- Co-development forums where security engineers and business owners align on success metrics
- Regular tabletop exercises integrating AI agent insights into crisis simulations
- Feedback loops from compliance audits, threat intelligence, and customer incidents to refine models
Embedding ethical and risk-based frameworks—such as the NIST AI Risk Management Framework and IEEE P7000 standards—ensures fairness, privacy, and transparency. Strategic leaders use these lenses to evaluate decision impacts, maintain stakeholder trust, and secure deeper AI adoption while safeguarding reputations.
Finally, aligning AI security investments with business outcomes transforms security into a driver of resilience and growth. By translating performance gains—reduced dwell time, improved threat coverage, and operational savings—into dollar-based value and business enablement metrics, leaders secure executive sponsorship and cross-organizational buy-in.
Future-Ready Mindset and Guiding Principles
To sustain innovation in AI-driven security, organizations must cultivate a future-ready mindset anchored in continuous evolution, robust guardrails, and principled collaboration.
- Continuous Evolution: Institutionalize iterative model development with feedback loops among analysts, threat intelligence teams, and compliance officers to mitigate drift and counter novel tactics.
- Recognize Limitations: Address data quality constraints, model opacity, and adversarial manipulation through layered validation, adversarial testing, and periodic audits.
- Human-in-the-Loop Collaboration: Preserve active human oversight at critical decision points to interpret recommendations, override as needed, and provide contextual insights.
- Explainability and Transparency: Prioritize interpretable models that trace alerts to underlying features and satisfy audit requirements.
- Ethical Design and Bias Mitigation: Embed fairness assessments and bias audits throughout the development lifecycle.
- Cross-Disciplinary Collaboration: Align data scientists, security engineers, legal advisors, and business leaders around shared risk appetites and strategic priorities.
- Governance and Policy Alignment: Define agent scope, permissible actions, escalation protocols, and accountability structures, supported by governance councils and periodic reviews.
- Performance Measurement and ROI Tracking: Deploy metrics for accuracy, latency, false positives, and cost savings to justify investments and guide resource allocation.
- Resilience through Diversity: Use heterogeneous model ensembles and multi-vendor approaches to mitigate single-point-of-failure risks.
Key considerations shaping realistic roadmaps include data governance and privacy constraints, regulatory volatility, interoperability challenges, model drift, talent scarcity, scaling constraints, vendor lock-in risks, and ethical implications. By balancing ambition with operational realities, security leaders foster a culture of responsible innovation where AI agents augment human judgment, reinforce resilience, and empower enterprises to navigate an ever-shifting threat landscape with confidence and agility.
Appendix
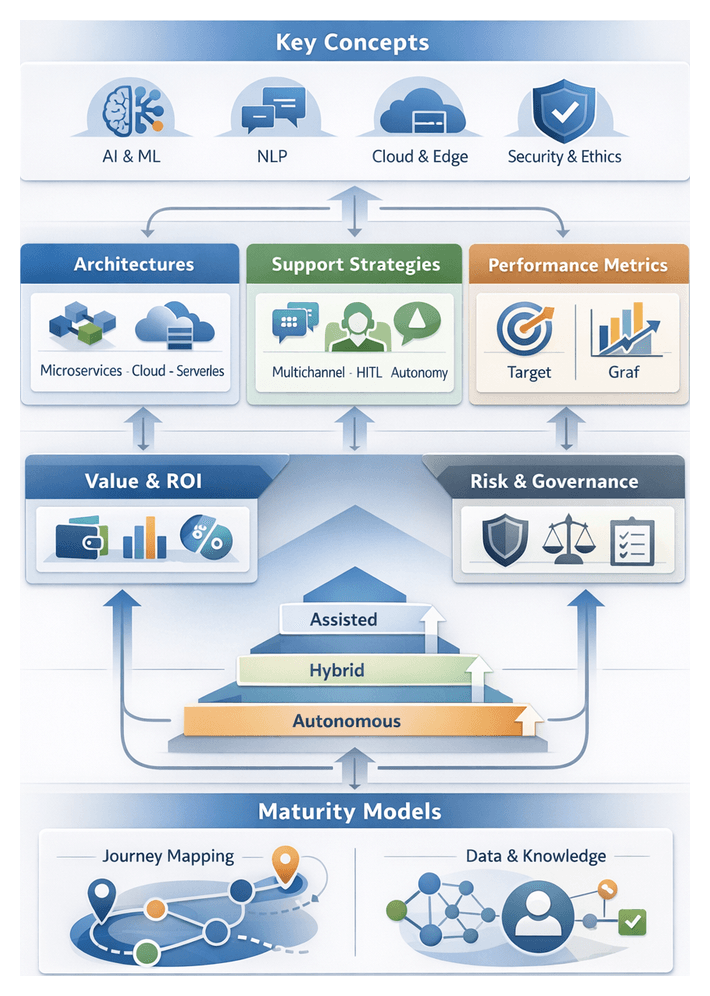
Glossary of AI Security Terms
This glossary clarifies terminology essential for understanding AI-driven security and risk management architectures, analytics, and governance models.
- Artificial Intelligence Agent: A software entity that perceives security data, applies analytical models to assess risk, and executes actions within a security ecosystem.
- Autonomous Security Agent: An AI agent that operates routine tasks without direct human approval, dynamically adjusting behavior based on feedback and evolving threats.
- Perception Module: Component responsible for ingesting, normalizing, and enriching telemetry from network sensors, endpoints, cloud workloads, identity systems, and threat feeds.
- Reasoning Engine: Analytical core where predictive, probabilistic, or rule-based models interpret data to generate risk assessments, prioritize incidents, and recommend responses.
- Orchestration Interface: Integration layer through which agents execute containment, remediation, or investigative actions across firewalls, endpoint platforms, identity providers, and SOAR systems.
- Supervised Learning: Paradigm in which models are trained on labeled datasets to classify events or predict outcomes based on historical ground truth.
- Unsupervised Learning: Approach where models identify patterns, clusters, or anomalies in unlabeled data, useful for detecting novel or previously unseen threats.
- Reinforcement Learning: Technique in which agents learn optimal actions by receiving reward signals from simulated or real environments, refining response policies over time.
- Anomaly Detection: Process of identifying deviations from established behavioral baselines to surface insider threats, zero-day exploits, or sophisticated attack techniques.
- Predictive Analytics: Application of statistical and machine learning models to forecast potential security events, enabling proactive defense and resource allocation.
- Extended Detection and Response (XDR): Integrated approach correlating telemetry across endpoints, networks, and cloud services for unified threat detection and automated response.
- Security Information and Event Management (SIEM): Platform that aggregates, normalizes, and correlates log and event data from multiple sources to identify security incidents and support investigations.
- Security Orchestration, Automation, and Response (SOAR): System automating routine workflows, integrating disparate tools, and orchestrating cross-platform response playbooks to accelerate incident handling.
- Endpoint Detection and Response (EDR): Technology that continuously monitors endpoint activity, uses behavioral analytics to detect threats, and enables automated containment on devices.
- User and Entity Behavior Analytics (UEBA): Methodology modeling normal behavior patterns of users and devices to uncover anomalous activities via statistical and machine learning techniques.
- Threat Intelligence: Contextualized information about adversary tactics, indicators of compromise, and attack infrastructures used to enrich detection and guide response.
- MITRE ATT&CK® Framework: Knowledge base of adversary tactics and techniques structured to support threat modeling, detection development, and incident analysis.
- STIX: Structured Threat Information Expression, a standardized format for representing threat intelligence artifacts such as indicators and attack patterns.
- TAXII: Trusted Automated eXchange of Indicator Information, a protocol enabling sharing of STIX-formatted threat intelligence between platforms.
- Zero Trust: Security model that assumes no implicit trust in network perimeters or user identities, enforcing continuous verification and least-privilege access.
- Least Privilege: Principle granting users and systems only the permissions required to perform their tasks, minimizing attack surface and damage potential.
- Data Fusion: Process of combining diverse data sources—such as logs, threat feeds, and contextual metadata—to create a unified view for comprehensive analysis.
- Model Drift: Gradual degradation of a machine learning model’s performance as data distributions shift over time, requiring retraining or recalibration.
- False Positive: Alert generated by an AI agent in response to benign activity mistakenly classified as malicious, leading to wasted analysis time and alert fatigue.
- False Negative: Security event that goes undetected by an AI agent, representing a missed opportunity to prevent or mitigate an incident.
- Explainable AI: Techniques and frameworks that provide interpretable explanations for AI-driven decisions, supporting transparency and auditability.
- Model Governance: Policies, processes, and oversight mechanisms ensuring machine learning models remain accurate, compliant, and free of unintended biases.
- Feedback Loop: Mechanism by which outcomes of agent actions and human evaluations are fed back into training pipelines to improve future performance.
- Digital Twin: Virtual representation of an asset or process used to simulate threat scenarios, test agent behaviors, and validate response strategies safely.
- Ensemble Learning: Approach combining multiple machine learning algorithms to improve detection accuracy and reduce variance in predictions.
- Feature Engineering: Process of selecting, transforming, and creating data attributes that enhance the predictive power of models in security analytics.
- Playbook: Predefined sequence of detection, enrichment, and remediation steps encoded in an orchestration platform to automate response workflows.
- Incident Response: Coordinated process of detecting, containing, eradicating, and recovering from security incidents, often guided by AI agents and orchestration tools.
- Vulnerability Management: Continuous process of discovering, classifying, prioritizing, and remediating security vulnerabilities in systems and applications.
- Privileged Access Management: Discipline and technology for securing, monitoring, and controlling elevated credentials and administrative privileges.
- Adaptive Authentication: Risk-based access control that adjusts authentication requirements dynamically based on real-time contextual signals and user behavior.
- Behavioral Biometrics: Continuous analysis of user interaction patterns—such as typing rhythm and mouse movements—to validate identity and detect compromise.
Architectural and Analytical Frameworks
Agent Architecture
AI security agents follow a modular architecture divided into three core components:
- Sensing and Data Ingestion: Collect telemetry from networks, endpoints, cloud workloads, identity systems, and third-party threat feeds.
- Reasoning and Decision Making: Apply machine learning, statistical inference, symbolic engines, and knowledge graphs to detect anomalies, score risk, and select response strategies.
- Action and Orchestration: Execute automated containment and remediation via firewalls, endpoint controls, credential management, and SOAR integrations.
Autonomy Spectrum
Agents align along a spectrum of autonomy, chosen to match organizational risk tolerance and maturity:
- Advisory Agents: Recommend actions and contextual insights for human analysts.
- Semi‐Autonomous Agents: Execute low-risk playbooks and escalate complex scenarios for approval.
- Fully Autonomous Agents: Perform end-to-end response actions within predefined policy guardrails under human oversight.
Learning Paradigms
- Supervised Learning: Signature detection and classification using labeled datasets; explainability via feature importance and local surrogate models.
- Unsupervised Learning: Clustering, density estimation, autoencoders, and isolation forests to surface novel threats without ground-truth labels.
- Reinforcement Learning: Policy optimization for dynamic response scenarios, refining containment sequences through reward-based feedback.
- Ensemble and Hybrid Models: Fusion of multiple learners—parallel voting, layered analysis, contextual RL—to balance precision and adaptability.
Threat Detection and Analytics
- Data Fusion: Correlate logs, network flows, and endpoint events to construct unified threat views.
- Anomaly Detection: Employ statistical thresholds, time-series forecasting (ARIMA, state-space models), and ML to flag deviations from dynamic baselines.
- Graph-Based Analysis: Map entities and relationships to uncover fraud rings and lateral movement within networks.
- Predictive Pattern Recognition: Supervised classifiers and NLP-enriched models forecast emerging risks.
Incident Response Models
- Rule-Based Orchestration: Encode expert procedures as static playbooks for triage and containment.
- Adaptive Learning: Refine response tactics via supervised and reinforcement learning based on feedback loops.
- Tiered Collaboration: Divide tasks into low-risk automated actions, mid-risk analyst reviews, and high-risk expert approvals.
Vulnerability Assessment
- Continuous Asset Profiling: Maintain real-time inventories via network and cloud APIs.
- Contextual Correlation: Enrich scan results with threat intelligence and exploit databases.
- Predictive Risk Scoring: Combine CVSS metrics, exploit likelihood, and business impact using ML models.
- Graph Analytics: Simulate attack paths to anticipate multi-stage compromise scenarios.
Identity and Access Management
- Adaptive Authentication: Adjust security challenges based on real-time risk scores derived from device, geolocation, and behavior signals.
- Behavioral Biometrics: Continuous session verification via keystroke dynamics, mouse gestures, and usage patterns.
- Just-In-Time Privilege: Issue time-bound elevated access on demand and revoke automatically.
- Risk-Based Policy Adaptation: Scale controls proportionally by mapping composite risk scores against policy tiers.
Fraud Detection and Financial Risk
- Transaction Risk Scoring: Combine anomaly detection, supervised classifiers, and temporal patterns for real-time fraud mitigation.
- Network and Graph Analysis: Detect laundering rings and complex fraud schemes by correlating entity relationships.
- Real-Time Decisioning: Deliver millisecond-level risk assessments in payment gateways and trading systems.
- Regulatory Model Governance: Ensure auditability, explainability, and compliance with Basel III, PSD2, and anti-fraud mandates.
Compliance Monitoring and Policy Enforcement
- Regulation NLP: Translate legal texts into machine-readable control rules using natural language processing.
- Continuous Controls Monitoring: Evaluate configurations against policy requirements in real time.
- Automated Evidence Collection: Capture snapshots, logs, and test results to populate audit trails.
- Risk-Scoring Dashboards: Aggregate control gaps into prioritized remediation workflows and compliance metrics.
Behavioral Analytics and Insider Threats
- Baseline Profiling: Cluster and analyze multi-source telemetry to establish normal behavior baselines.
- Unsupervised Anomaly Detection: Use autoencoders, Isolation Forests, and ensembles to surface novel deviations.
- Composite Risk Scoring: Aggregate feature anomalies into holistic threat metrics.
- Contextual Response: Orchestrate interventions—session isolation, step-up authentication, DLP actions—based on user and data context.
Integration and Interoperability Standards
Ethical Governance and Oversight
- Ethical Risk Dimensions: Fairness, transparency, privacy, and robustness in AI decision-making.
- Bias Detection: Fairness metrics audits and adversarial testing to reveal and mitigate model biases.
- Explainability Layers: SHAP, LIME, and surrogate models for both local and global interpretability.
- Model Governance: Versioning, change control, and audit trails to maintain compliance and accountability.
- Privacy Safeguards: Data minimization, pseudonymization, access governance, and impact assessments.
- Human Oversight: Policy definition, exception handling, ethical review, and strategic guidance within human–machine partnerships.
AI-Driven Tools and Platforms
- Darktrace Enterprise Immune System: Unsupervised ML platform modeling normal behavior to detect subtle anomalies.
- IBM Security QRadar Advisor with Watson: NLP and ML extension enriching SIEM alerts and recommending investigative steps.
- Splunk Phantom: SOAR platform integrating controls to automate playbooks and streamline incident management.
- Palo Alto Networks Cortex XDR: XDR solution combining endpoint, network, and cloud data with ML for detection and containment.
- Palo Alto Networks Cortex XSOAR: Unified SOAR with low-code playbook editor and integration marketplace.
- CrowdStrike Falcon: Cloud-native endpoint protection using AI to identify malware, ransomware, and identity-based threats.
- Rapid7 InsightVM: Vulnerability risk management applying predictive analytics and live dashboards for remediation prioritization.
- Okta Adaptive Multi-Factor Authentication: IAM service enforcing dynamic authentication policies based on risk signals.
- Microsoft Sentinel: Cloud-native SIEM and SOAR ingesting hybrid telemetry and applying AI models for detection and automation.
- IBM Security SOAR: Orchestration and case management platform coordinating automated and human-driven response workflows.
- Cisco SecureX: Cloud-delivered platform unifying visibility, automation, and threat response across Cisco and partner solutions.
- ServiceNow Security Operations: Integrated GRC and SOAR aligning incidents with IT workflows and risk management.
- MetricStream GRC Platform: Governance, risk, and compliance system for policy management, controls monitoring, and audit tracking.
- IBM OpenPages: Risk and compliance platform using AI to interpret regulatory changes and automate control assessments.
- Ascent RegTech: AI-driven regulatory change management mapping new rules to internal policies.
- Compliance.ai: Regulatory intelligence platform using NLP to track and interpret global compliance updates.
- IBM Watson Discovery: AI search and content analytics engine extracting insights from unstructured regulatory texts and threat reports.
- Qualys Cloud Platform: Suite of cloud-native security and compliance modules for continuous asset discovery and vulnerability assessment.
- Tenable.io: Cloud-based vulnerability management applying ML to triage findings and predict exploit likelihood.
- HashiCorp Vault: Secrets management tool securing, storing, and rotating credentials, API tokens, and encryption keys.
- Splunk User Behavior Analytics (UBA): Unsupervised learning add-on detecting compromised credentials and insider threats.
- Exabeam Smart Timelines: UEBA solution reconstructing sessions and detecting suspicious activity sequences.
- Digital Guardian Data Loss Prevention: Data protection platform leveraging content inspection and contextual analytics to prevent exfiltration.
- Microsoft Purview Data Loss Prevention: Unified solution for discovering, classifying, and protecting sensitive information in Microsoft 365.
- CyberArk Privileged Access Security: Platform for discovering, vaulting, and monitoring privileged credentials with session recording and analytics.
- BeyondTrust Privileged Remote Access: Solution securing and auditing remote and privileged sessions across hybrid environments.
- SailPoint IdentityNow: Identity governance platform automating access certifications and policy enforcement at scale.
- Ping Identity Platform: Suite of IAM services including adaptive MFA, single sign-on, and risk-based access controls.
- Feedzai: Real-time fraud detection and decisioning engine for payment and banking systems.
- Featurespace: Platform using adaptive behavioral analytics to detect and prevent financial crime.
- FICO Falcon Fraud Manager: Scalable fraud detection system for payments and e-commerce with explainable AI modules.
- NICE Actimize: Financial crime and compliance suite integrating real-time analytics and case management.
Regulatory References and Further Reading
- GDPR: General Data Protection Regulation – EU data privacy and subject rights.
- CCPA: California Consumer Privacy Act – State law granting consumer data rights.
- PCI DSS: Payment Card Industry Data Security Standard – Global standard for securing card data.
- HIPAA: Health Insurance Portability and Accountability Act – US law governing protected health information.
- SOX: Sarbanes-Oxley Act – US federal law for audit and financial reporting requirements.
- Basel III: International banking regulation on risk management and capital adequacy.
- PSD2: Payment Services Directive 2 – EU directive for strong customer authentication and open banking.
- NIST Cybersecurity Framework (CSF): Voluntary framework for managing cybersecurity risk.
- NIST AI Risk Management Framework (AI RMF): Guidance for trustworthy and responsible AI.
- ISO/IEC 27001: International specification for information security management systems.
- ISO/IEC 42001: Standard for AI management systems and governance principles.
- NIST SP 800-53: Catalog of security and privacy controls for federal information systems.
- NIST SP 800-61r2: Guidance on incident response lifecycle and best practices.
- OpenAI Gym for Security: Simulation environments for RL agents in cybersecurity testbeds.
- Adversarial Machine Learning Playbook: Techniques for testing and strengthening models against malicious inputs.
- MITRE Shield: Knowledge base of active defense and adversary engagement strategies.
- CIS Controls: Prioritized set of actions to prevent and detect cyber threats.
- OWASP Top Ten: Standard awareness document for web application security risks.
- SANS Reading Room: White papers, case studies, and research on security topics.
- IEEE Ethically Aligned Design: Guidelines for ethical AI system development.
- AI Incident Database: Repository of real-world AI system failures, breaches, and biases.
The AugVation family of websites helps entrepreneurs, professionals, and teams apply AI in practical, real-world ways—through curated tools, proven workflows, and implementation-focused education. Explore the ecosystem below to find the right platform for your goals.
Ecosystem Directory
AugVation — The central hub for AI-enhanced digital products, guides, templates, and implementation toolkits.
Resource Link AI — A curated directory of AI tools, solution workflows, reviews, and practical learning resources.
Agent Link AI — AI agents and intelligent automation: orchestrated workflows, agent frameworks, and operational efficiency systems.
Business Link AI — AI for business strategy and operations: frameworks, use cases, and adoption guidance for leaders.
Content Link AI — AI-powered content creation and SEO: writing, publishing, multimedia, and scalable distribution workflows.
Design Link AI — AI for design and branding: creative tools, visual workflows, UX/UI acceleration, and design automation.
Developer Link AI — AI for builders: dev tools, APIs, frameworks, deployment strategies, and integration best practices.
Marketing Link AI — AI-driven marketing: automation, personalization, analytics, ad optimization, and performance growth.
Productivity Link AI — AI productivity systems: task efficiency, collaboration, knowledge workflows, and smarter daily execution.
Sales Link AI — AI for sales: lead generation, sales intelligence, conversation insights, CRM enhancement, and revenue optimization.
Want the fastest path? Start at AugVation to access the latest resources, then explore the rest of the ecosystem from there.
