
Intelligent Defenders AI Agents Revolutionizing Threat Detection in 2026
To download this as a free PDF eBook and explore many others, please visit the AugVation webstore:
Introduction
Security Landscape in 2026 and Emerging Threats
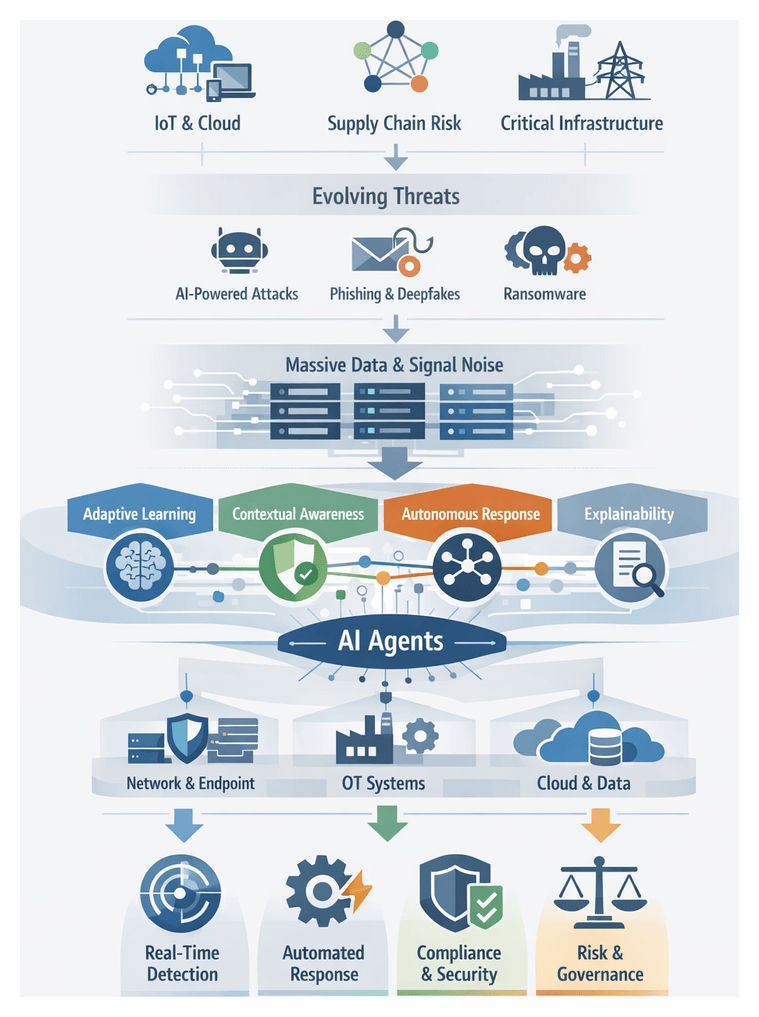
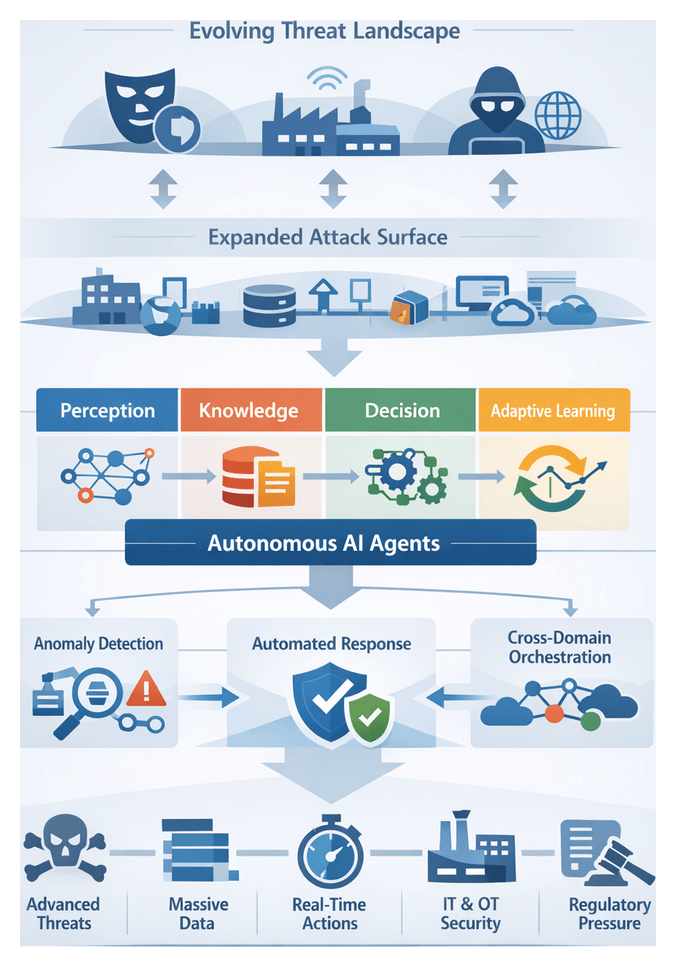
As organizations enter 2026, the security landscape has evolved into a complex battlefield spanning digital and physical realms. The rapid adoption of Internet of Things sensors, 5G-enabled edge computing clusters and expansive multi-cloud infrastructures has broadened the attack surface. Each connected device, cloud instance and third-party integration represents a potential foothold for adversaries. Supply chain interdependencies further amplify risk, as a breach in one vendor ecosystem can cascade through multiple downstream organizations.
Malicious actors now leverage automation and artificial intelligence to orchestrate large-scale campaigns. Automated reconnaissance tools map network topologies in seconds, while machine-generated phishing and voice deepfakes evade human scrutiny. Ransomware-as-a-service platforms dynamically customize payloads to bypass signature-based defenses. In this environment, static patch-after-breach strategies prove insufficient against adversaries who adapt faster than manual processes can respond.
Critical infrastructure sectors—energy grids, water treatment facilities and transportation networks—depend on operational technology systems originally designed without cybersecurity in mind. In late 2024, a minor vulnerability in an industrial controller allowed attackers to disrupt pipeline operations, illustrating how cyber-physical convergence can imperil millions of consumers. Such incidents underscore the necessity for real-time detection across network telemetry and sensor-level anomalies.
The volume and velocity of security data have exploded. Network flows, endpoint logs, user behavior analytics, threat intelligence feeds and cloud audit records collectively generate hundreds of millions of events per day. Even skilled analysts using platforms like Microsoft Azure Sentinel or Splunk struggle to prioritize alerts and uncover subtle attack patterns buried within routine noise.
Emerging threat categories amplify this complexity. Generative AI crafts highly personalized social engineering lures, adversarial machine learning corrupts detection models, and insider threats exploit legitimate privileges across blurred hybrid work environments. Legacy architectures built around perimeter defenses and static rule sets cannot adapt at the required speed or scale. Organizations thus face mounting regulatory pressures, board-level demands for transparent security metrics and supply chain mandates that raise the stakes of non-compliance.
To thrive in this dynamic environment, security teams must transition from reactive to proactive postures. Detection capabilities should evolve beyond signature matching toward behavioral analysis and anomaly detection driven by advanced machine intelligence. Automated workflows need to triage and remediate incidents with minimal human intervention, reserving expert resources for strategic tasks. Leading-edge organizations are piloting autonomous agent frameworks such as Darktrace Antigena and CrowdStrike Falcon Fusion XDR. These platforms integrate network metrics, endpoint process flows, user authentication events and external intelligence to construct holistic situational awareness. Agents can then initiate containment actions—isolating compromised hosts or quarantining malicious processes—often before human analysts become aware of an incident.
Deploying autonomous defenses at scale presents challenges in integration, orchestration and governance. Security leaders must define escalation thresholds, human override policies and audit trails. Investments in data hygiene and labeling practices ensure reliable inputs for learning algorithms, while cross-functional teams refine detection rules and guide continuous improvement. The convergence of cyber and physical threats, AI-driven adversary techniques and data volume growth has created a turning point: autonomous AI agents offer the potential to detect nuanced deviations, coordinate multi-vector responses and learn iteratively from emerging threat patterns. Operating continuously at machine speed, they bridge the gap between detection and action.
Conceptual Framework of Autonomous AI Agents
Autonomous AI agents represent a paradigm shift from tool-centric defenses to self-governing systems that operate with minimal human intervention. These dynamic entities sense environmental changes, evaluate emergent threats and execute adaptive responses. Unlike rule-based engines that rely on static signatures, agents ingest heterogeneous data streams, apply probabilistic inference and refine internal models over time to address polymorphic threats and zero-day exploits at scale.
Standards organizations and research consortia provide reference models that guide agent adoption. The National Institute of Standards and Technology (NIST) positions agents within the cyber resiliency lifecycle, while the MITRE ATT&CK framework offers a threat behavior ontology for categorization and prediction. Security operations leaders assess agent efficacy using metrics such as mean time to detect (MTTD), reduction in dwell time, true positive rate and false positive rate. Cost-benefit analyses examine total cost of ownership and projected return on investment when integrating agents into existing workflows.
Analysts apply classic decision-making theories, notably the OODA loop (Observe, Orient, Decide, Act), to autonomous agents. Instead of human operators, agents ingest telemetry, contextualize threat indicators, determine optimal response paths and execute containment or remediation steps continuously at machine speed. In Security Operations Centers, agents serve as force multipliers—escalating high-fidelity alerts, recommending investigative playbooks and automating routine triage tasks. Conceptually, an agent functions as a junior analyst with specialized capabilities, learning from human feedback to refine future actions.
Interpretive frameworks such as the security mesh view agents as interconnected nodes within a distributed fabric, sharing threat intelligence, harmonizing risk assessments and orchestrating coordinated responses. Within zero trust architectures, agents dynamically validate every transaction and user behavior, granting access based on continuous risk scoring. This alignment with zero trust principles—where trust is never assumed and decisions derive from real-time analytics—reinforces agents as dynamic policy engines.
Core Attributes of Autonomous AI Agents
- Adaptive Learning: Utilization of reinforcement learning and continuous retraining to evolve detection models in response to emerging threats.
- Contextual Awareness: Correlation of user behavior, asset profiles and external intelligence to generate alerts with richer context.
- Decentralized Execution: Operation at network edges and endpoints to minimize latency and maintain coverage during segmentation.
- Autonomous Response: Initiation of containment measures—such as isolating endpoints or modifying firewall rules—without manual approval.
- Explainability: Provision of human-readable justifications for decisions to support auditability and regulatory compliance.
From a governance perspective, risk officers incorporate agent-derived metrics into enterprise risk management models, informing board-level reporting. Auditors review logs that record decision rationales and evidence of change management for autonomous rule updates. In regulated industries, vendor evaluations use request-for-proposal frameworks that map agent capabilities—threat coverage, scalability, integration maturity and model transparency—to business outcomes, guiding procurement decisions.
Drivers Accelerating AI-Based Threat Detection
- Proliferation and Sophistication of Cyber Attacks: Adversaries employ automated exploitation, polymorphic malware and coordinated campaigns. Zero-day exploits have surged, while fileless techniques account for over a quarter of new attack methods. Platforms like Darktrace demonstrate how unsupervised learning models surface previously unseen threats by inferring malicious intent from anomalous activity.
- Explosion of Security Data and Signal Noise: Terabytes of daily telemetry across network flows, endpoint logs, cloud events and threat feeds overwhelm analysts. Autonomous AI agents use scalable data-fusion and statistical models to distill noisy inputs into actionable insights. For example, Google Chronicle applies high-throughput logging and threat scoring to reveal critical events hidden within billions of records.
- Imperative for Real-Time Detection and Response: Automated attacks can traverse networks and exfiltrate data within minutes. Streaming analytics architectures with sub-second threat scoring enable platforms like Azure Sentinel to trigger adaptive countermeasures instantly, reducing dwell time and limiting impact.
- Regulatory and Compliance Pressures: Regulations such as GDPR, CCPA and PCI DSS demand rapid breach detection, reporting and data protection. Automated detection technologies that log decision rationales and maintain immutable audit trails help substantiate compliance during audits.
- Persistent Skills Shortage and Operational Constraints: A global talent gap of over three million cybersecurity roles hinders 24×7 operations. AI agents automate routine analysis, triage incidents and execute low-risk remediation, allowing analysts to focus on threat hunting and strategy.
- Digital Transformation and Expanded Attack Surface: Cloud migration, software-defined networks and hybrid work models introduce diverse entry points. Unified agents such as CrowdStrike Falcon combine endpoint telemetry with cloud analytics to detect lateral movement and account compromise in real time.
- Convergence of Cyber and Physical Security: Cross-domain attacks exploit both IT and OT systems. AI agents that ingest data from access controls, surveillance platforms, industrial sensors and network logs provide a unified risk view, essential for protecting critical infrastructure.
- Competitive and Reputational Imperatives: Cyber resilience is a key differentiator in finance, healthcare and retail. Transparent metrics on time-to-detect, time-to-contain and false positive rates demonstrate proactive security postures that bolster stakeholder trust and brand equity.
Key Considerations and Limitations
- Data Quality and Bias: Agents depend on large volumes of training data that may contain inconsistencies or biases, leading to blind spots or discriminatory detection patterns.
- Model Drift and Adversarial Manipulation: Attackers may exploit vulnerabilities in models through adversarial inputs or induce concept drift. Continuous monitoring and robust retraining pipelines are essential.
- Integration and Interoperability: Seamless integration with heterogeneous security stacks and orchestration frameworks requires standardized interfaces and data schemas.
- Governance, Ethics and Privacy: Policies must govern autonomous actions, human override processes and data handling to ensure accountability, transparency and compliance with evolving AI regulations.
- Human Oversight and Skills Gap: Effective deployment relies on skilled teams capable of interpreting AI outputs, investigating alerts and tuning agent parameters.
- Scalability and Performance Trade-Offs: Real-time inference demands significant compute resources. Balancing throughput, latency and cost is critical to maintain operational performance.
- Explainability and Trust: Black-box models can erode stakeholder confidence. Investing in explainable AI techniques supports transparency and auditability.
- Resource and Cost Constraints: Licensing commercial platforms, building proprietary models and maintaining data pipelines can strain budgets. Clear cost-benefit analyses are necessary to prioritize investments.
- Emerging Unknown Threats: Rapid adversary innovation—zero-day exploits, deep-fake social engineering and quantum-resistant cryptanalysis—requires continuous research and collaboration to anticipate new vectors.
- Vendor Lock-In and Technical Debt: Dependence on specific platforms creates lock-in risks. Open architectures and modular frameworks help preserve strategic flexibility.
By acknowledging these limitations and addressing them through governance, skilled personnel and resilient architectures, organizations can harness the full potential of autonomous AI agents while mitigating attendant risks. As threats continue to converge across cyber and physical domains, success will hinge on strategic alignment, continuous evaluation and a balanced integration of human expertise and machine intelligence.
Chapter 1: The Evolution of Threat Detection
The Security Landscape in 2026 and New Emerging Threats
As organizations enter 2026, the security environment has evolved far beyond perimeter defense and signature-based detection. The integration of operational technology with information technology, the rapid proliferation of cloud services and the ubiquity of edge devices have blurred traditional boundaries, creating hybrid physical-cyber scenarios across smart cities, manufacturing floors and critical infrastructure. Cybercriminals and nation-state actors systematically exploit supply-chain weaknesses, injecting malicious components into software and hardware distribution channels. They leverage polymorphic malware frameworks, AI-driven social engineering and automated propagation tools to conduct targeted phishing, credential stuffing and deepfake campaigns that can traverse global networks within seconds, demanding defenses that operate at scale and in real time.
Modern digital ecosystems introduce novel attack vectors across industrial control systems, smart building infrastructure and connected medical devices, enabling adversaries to move laterally with minimal friction. Concurrently, digital transformation initiatives drive accelerated adoption of microservices architectures, containerized workloads, serverless functions and multi-cloud deployments. While these technologies offer unprecedented agility and efficiency, they also expand the threat surface and complicate vulnerability management. Security teams must ingest and analyze a deluge of telemetry from network flow logs, packet captures, endpoint sensors, user and entity behavior analytics, threat intelligence feeds and IoT device metrics—overwhelming traditional security operations centers and manual processes.
Regulatory frameworks such as the California Consumer Privacy Act and the European Union’s General Data Protection Regulation have heightened the stakes for data protection and transparency. Companies are required to demonstrate accountability in their security controls, maintain auditable logs and report breaches within strict timeframes. Industry standards bodies—from the National Institute of Standards and Technology Cybersecurity Framework to the MITRE ATT&CK knowledge base—provide structured guidance for threat modeling and risk management. Yet implementation gaps persist as organizations struggle with fragmented telemetry sources, siloed toolsets and the scarcity of skilled analysts. Against this backdrop, autonomous AI agents emerge as a strategic imperative for orchestrating real-time threat detection, reducing human burden and maintaining compliance in a dynamic threat landscape.
Autonomous AI Agents as a Conceptual Framework
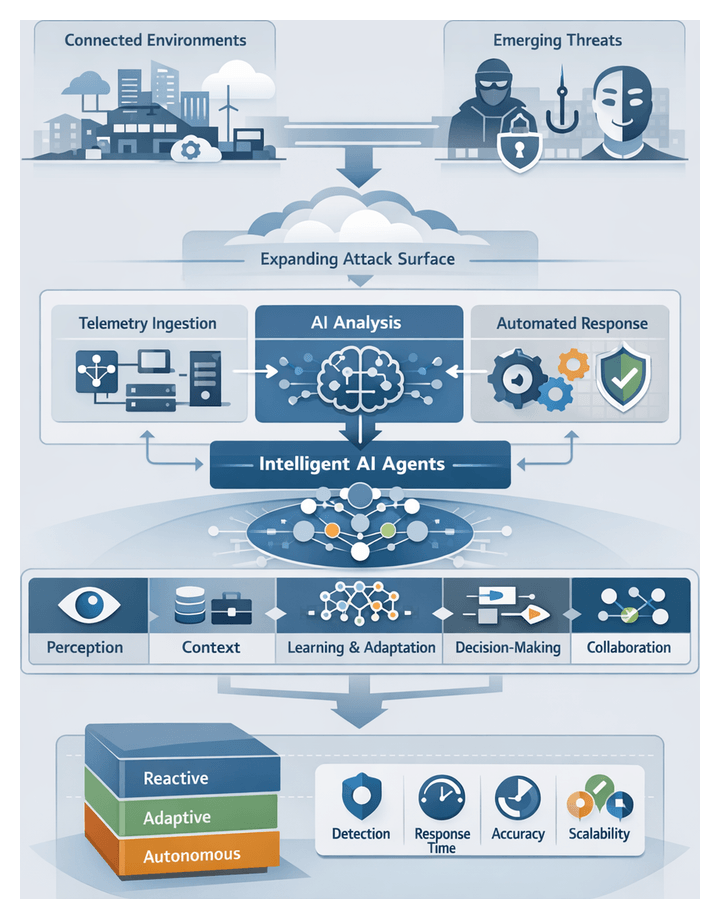
Autonomous AI agents represent a paradigm shift from reactive, rule-based security controls to proactive, self-directed systems that continuously learn, reason and act. Conceptualized as intelligent defenders, each agent maintains an ongoing perception of its environment, ingesting diverse telemetry streams, synthesizing contextual information and executing mitigation actions without manual intervention. By embedding advanced analytics engines, adaptive learning loops and policy-driven decision logic, autonomous agents evolve their detection strategies over time, refining models through feedback from false positives, adversarial testing and confirmed incidents.
Within a multi-agent ecosystem, these systems collaborate and share intelligence to maximize coverage and reduce mean time to detection. Agents delegate tasks to human analysts or peer agents, escalate high-risk alerts and coordinate containment workflows across network segments, cloud environments and edge deployments. Research in autonomous systems underpins this approach, emphasizing robust decision-making under uncertainty, explainability and federated learning to balance centralized governance with distributed adaptability.
Core Attributes
- Perception: Continuous ingestion and interpretation of network flow, endpoint activity, application logs and IoT telemetry to capture a comprehensive view of the threat surface.
- Contextual Reasoning: Correlation of signals with historical baselines, asset criticality, business processes and enterprise risk models to prioritize threats according to impact.
- Analysis and Adaptive Learning: Integration of supervised, unsupervised and reinforcement learning algorithms that detect anomalies, update detection thresholds and refine heuristics autonomously.
- Decision Autonomy: Ability to initiate response actions—ranging from alert escalation to automated containment—based on predefined risk policies and dynamic threat assessments.
- Collaboration: Information sharing between agents and human teams via standard protocols, enabling coordinated responses and collective intelligence.
- Scalability: Elastic performance across high-velocity data streams and distributed environments, from on-premises data centers to edge deployments.
Maturity Models and Benchmarking
Organizations leverage maturity models to chart their progress toward fully autonomous defense. Typical maturity levels include:
- Reactive Monitoring: Agents detect known threat signatures and generate alerts for human analysts, with minimal automation of responses.
- Adaptive Detection: Agents employ machine learning to identify anomalies and adjust thresholds, yet require manual validation and tuning before acting.
- Assisted Response: Agents propose or initiate predefined containment measures—such as quarantining compromised endpoints—subject to analyst approval.
- Autonomous Defense: Agents execute multi-stage response workflows, update detection heuristics in real time and coordinate with peer agents without human intervention.
Standardized benchmarking frameworks—such as MITRE ATT&CK evaluations—assess agent performance across key indicators:
- Detection Accuracy: Percentage of simulated or real-world threats correctly identified.
- Time to Detect (TTD): Elapsed time from initial compromise to agent recognition of malicious activity.
- Time to Respond (TTR): Interval from threat detection to automated or orchestrated containment actions.
- Alert Noise Ratio: Volume of non-actionable or false-positive alerts per genuine security incident.
- Adaptation Rate: Frequency and effectiveness with which models update to counter emerging adversary tactics.
Vendors like Vectra AI and Darktrace publish anonymized performance data from these benchmarks, enabling security teams to compare autonomous efficacy and drive vendor selection based on empirical metrics. Smaller organizations often adopt turnkey platforms—such as Microsoft Sentinel or CrowdStrike Falcon—that embed autonomous detection modules out of the box, prioritizing seamless integration and minimal customization.
Drivers Accelerating AI-Based Threat Detection
Several converging factors are accelerating the adoption of autonomous AI agents in enterprise security:
- Explosion of Data Volume and Velocity: Organizations generate terabytes of security-relevant telemetry daily, exceeding the processing capacity of manual and rule-based systems and necessitating automated analysis at machine speed.
- Increased Sophistication of Adversaries: Attackers leverage automation, polymorphic and fileless malware, as well as AI-powered social engineering, to evade traditional signature-based defenses and bypass static rule sets.
- Operational Constraints: Security teams face talent shortages, burnout and budget pressures. Autonomous agents handle routine alert triage, freeing analysts to focus on strategic threat hunting and incident response.
- Regulatory and Compliance Imperatives: Evolving privacy laws and industry mandates demand auditable, transparent security operations. AI-driven logging and decision-tracking provide verifiable trails to support compliance with CCPA, GDPR, PCI DSS and emerging AI governance regulations.
- Need for Real-Time Decision-Making: In a landscape where threats can propagate globally within seconds, automated agents minimize dwell time and limit potential damage by executing immediate containment actions.
These drivers have prompted vendors to integrate machine learning libraries, graph analytics engines, real-time streaming architectures and explainable AI frameworks into their platforms. Open-source initiatives and commercial offerings alike emphasize agent orchestration, federated learning and human-AI teaming to meet enterprise governance and scalability requirements.
Guide Overview and Reader Outcomes
Organized to support a logical progression from foundational concepts to strategic deployment, this guide provides analytical frameworks, conceptual models and practical case studies. Readers will advance through the following themes:
- Evolution from static signature engines to adaptive, AI-driven detection and the strategic implications for security operations
- Anatomy of an AI agent: perception modules, knowledge repositories, decision engines and adaptive learning loops
- Machine learning paradigms—supervised, unsupervised, reinforcement and transfer learning—and their applications in threat detection
- Data ecosystem mapping: normalization techniques, data quality considerations and integration of diverse telemetry sources
- Real-time analytics: streaming architectures, event correlation methods and automated countermeasure workflows
- Multi-agent collaboration and human-AI teaming frameworks for coordinated detection and response
- Cross-sector case studies with performance metrics, scalability considerations and operational impacts in finance, healthcare, infrastructure and retail
- Technical resilience: adversarial manipulation, model drift, false positives and strategies for sustaining agent reliability over time
- Ethical, privacy and regulatory considerations aligned with global governance frameworks, including the EU AI Act and the NIST AI Risk Management Framework
- Future trends: explainable AI, predictive threat hunting, quantum-enhanced detection and self-healing network architectures
By engaging with this guide, readers will:
- Align AI agent architectures with business objectives, risk appetites and security goals
- Apply comparative frameworks to evaluate learning paradigms, data quality impacts and analytics design trade-offs
- Assess scalability, performance and resilience of multi-agent deployments in hybrid environments
- Balance innovation with ethical, privacy and compliance imperatives through governance models and audit mechanisms
- Anticipate how emerging computational paradigms and threat hunting methodologies will reshape future defense strategies
Applying Insights to Security Roadmaps
Security teams can operationalize these frameworks by conducting internal maturity assessments aligned with the thematic pillars. Starting with threat landscape analysis, organizations should map existing capabilities against desired maturity levels and identify gaps across agent anatomy, data ecosystem and operational workflows. Cross-functional workshops facilitate human-AI teaming exercises to define roles, responsibilities and escalation protocols. Illustrated case studies provide performance benchmarks, while compliance checklists guide regulatory alignment. Structured roadmaps and pilot programs enable iterative refinement, supporting continuous improvement and rigorous model governance.
Contextual Boundaries
- Scope of Analysis: Focuses on conceptual frameworks and strategic guidance; detailed implementation requires further technical research.
- Rapid Technological Change: Agent capabilities and adversarial tactics evolve quickly; frameworks should be revisited and adapted periodically.
- Data Variability: Quality, volume and formats of telemetry differ across environments; data normalization and fusion strategies must be tailored locally.
- Regulatory Diversity: Global jurisdictions impose varying requirements on data sovereignty, privacy and AI governance; region-specific legal analysis is recommended.
- Case Study Applicability: Benchmarks from early adopters serve as reference points but may not directly translate to all organizational contexts.
Chapter 2: Anatomy of an AI Agent
Security Landscape and Emerging Threats
As organizations enter 2026, security defenses face an intricate fusion of cyber and physical attack vectors. The boundary between traditional IT environments and operational technology has dissolved under the pressure of hybrid work models, cloud migrations, and the proliferation of Internet of Things devices. Industrial control systems, smart buildings, and networked medical equipment now connect directly to corporate networks and public cloud services, offering adversaries diverse paths to exploit software vulnerabilities, manipulate programmable logic controllers, or compromise supply-chain components.
Malicious actors leverage automation and artificial intelligence to accelerate reconnaissance, craft highly personalized spear-phishing campaigns, and execute adversarial machine learning to evade detection. Custom generative models produce phishing content tailored to specific organizational contexts, while automated lateral-movement frameworks identify and exploit network misconfigurations without human intervention. As a result, breach lifecycles compress from weeks to hours, demanding security solutions that match this velocity.
The volume, velocity, and variety of security telemetry have grown exponentially. Daily petabytes of packet captures, endpoint logs, cloud audit trails, and user behavior analytics overwhelm traditional rule-based systems. Security operations centers struggle to extract meaningful signals from this noise in real time, leading to alert fatigue and unaddressed threats lingering undetected. Simultaneously, regulatory regimes—such as GDPR, CCPA, PCI DSS, and HIPAA—impose stringent breach notification timelines and transparency requirements, while geopolitical tensions drive nation-state actors to target critical infrastructure sectors.
Key dimensions of this evolving threat environment include:
- Convergence of cyber and physical systems, expanding attack surfaces across IT, OT, and IoT domains
- AI-augmented adversaries automating vulnerability discovery, evasion techniques, and phishing workflows
- Supply-chain compromises propagating malicious code across thousands of downstream environments in minutes
- Overwhelming telemetry growth challenging real-time analysis and signal discrimination
- Heightened regulatory and geopolitical pressures requiring rapid detection, transparent reporting, and compliance management
Legacy signature engines and static correlation rules can no longer keep pace with polymorphic malware, fileless attacks, or cloud misconfigurations. Excessive false positives and missed novel threats erode trust in alerts, while manual tuning cannot adapt swiftly enough. To confront this relentless environment, enterprises must embrace adaptive security architectures powered by autonomous AI agents capable of continuous learning, decentralized decision-making, and coordinated response across dispersed infrastructures.
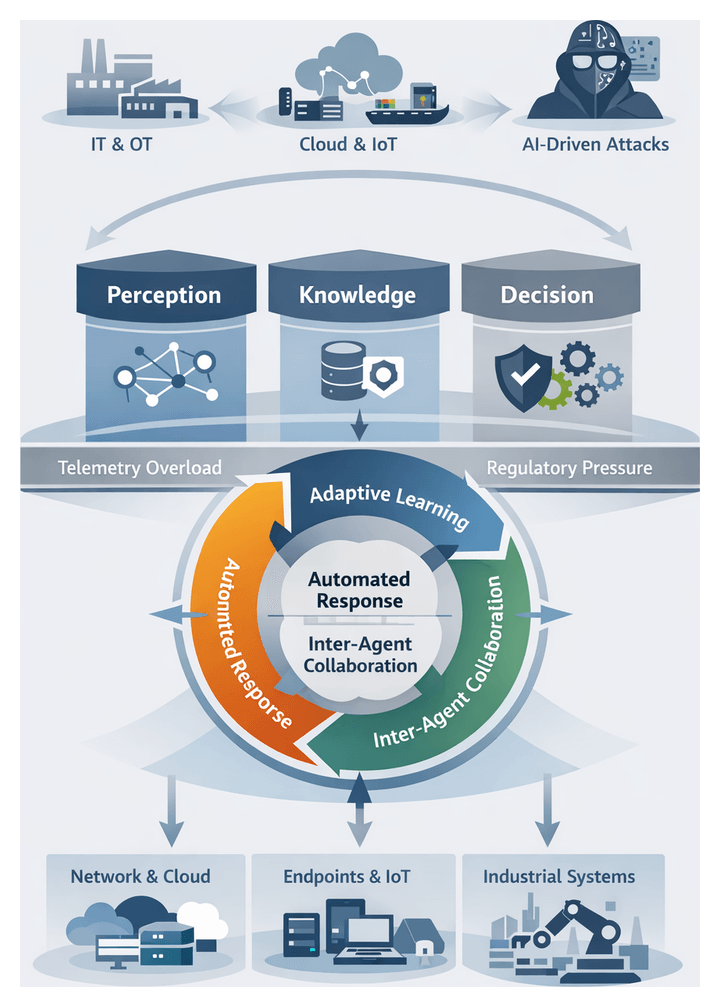
Conceptual Framework of Autonomous AI Agents
Autonomous AI agents represent a transformative approach to threat detection and response. These software entities function as intelligent sensors and responders, continuously perceiving inputs from diverse data sources, reasoning over contextual knowledge, and executing actions to neutralize or escalate incidents within predefined governance boundaries. Unlike traditional tools that depend on static signatures or rule sets, autonomous agents evolve their detection logic through feedback loops, refine confidence thresholds, and collaborate with peer agents to share threat intelligence.
Defining Attributes
- Perception and Contextual Awareness: Agents ingest network flows, host process logs, cloud API events, and threat intelligence feeds, normalizing and enriching raw data into structured events.
- Adaptive Learning Loops: Supervised, unsupervised, and reinforcement learning models enable agents to refine detection criteria, reinforce accurate identifications, and suppress false positives over time.
- Decentralized Decision Making: Localized analytics allow agents to autonomously trigger automated countermeasures—such as workload isolation or endpoint quarantine—when risk thresholds are exceeded.
- Inter-Agent Collaboration: Distributed agents exchange anonymized anomaly summaries and coordinate remediation actions across network segments and cloud regions.
- Governance-Conscious Autonomy: Policy and compliance guardrails define the scope of automated actions, ensuring that agents escalate complex incidents to human analysts according to organizational risk frameworks.
This modular architecture comprises a perception layer for data ingestion and feature extraction, a knowledge repository for contextual enrichment, decision engines executing inference and risk evaluation, and action modules for response orchestration. By decoupling these components, organizations can introduce new detection algorithms, integrate additional threat feeds, and update policies without disrupting core capabilities.
As a cohesive paradigm, autonomous AI agents align security operations with the dynamic nature of modern attacks, delivering continuous surveillance, rapid containment, and scalable defenses that adapt alongside evolving threat tactics.
Core Drivers of AI-Based Threat Detection
Several converging trends have elevated AI-driven detection from an innovation to an operational imperative:
- Escalating Attack Sophistication: Polymorphic malware, living-off-the-land techniques, and adversarial machine learning evade signature-based defenses, highlighting the need for behavior-centric analytics
- Data Volume and Velocity: Trillions of daily telemetry events—from endpoints, networks, clouds, and applications—overwhelm manual correlation, necessitating automated anomaly detection and prioritization
- Real-Time Decision Requirements: Automated response engines embedded within agents close the gap between detection and remediation, containing threats before they propagate
- Talent Shortages and Cost Pressures: The cybersecurity skills gap forces organizations to maximize efficiency; autonomous agents shoulder routine tasks, enabling lean teams to focus on advanced threat hunting and strategic initiatives
- Regulatory and Compliance Imperatives: Continuous monitoring and detailed audit trails support obligations under GDPR, CCPA, PCI DSS, HIPAA, and emerging national cybersecurity directives
- Digital Transformation and Cloud Adoption: As enterprises migrate to public clouds and microservices, security controls must adapt to ephemeral workloads; agents integrate with cloud APIs to maintain full visibility
Together, these drivers create a compelling case for embedding AI-based threat detection throughout security architectures. Organizations that harness machine learning, automation, and autonomous decision-making gain a decisive edge in detecting and disrupting sophisticated attacks.
Interplay of Perception, Knowledge, and Decision Modules
Effective AI-driven security depends on the tight integration of perception, knowledge representation, and decision engines. Industry practitioners view this triad as a unified analytical system where each layer enhances and depends on the others to deliver high-fidelity detections.
Perception as Threat Sensing
The perception layer functions as a global sensor network, gathering raw telemetry from endpoints, network taps, cloud environments, and external threat feeds. Leading solutions—such as IBM QRadar, Splunk, and Darktrace—employ advanced normalization and feature extraction to convert diverse data formats into consistent, enriched events. Breadth (coverage across network, host, cloud, and application layers) and depth (inspection granularity, from packet headers to system call traces) determine detection accuracy and analysis latency.
Knowledge Representation and Contextualization
Knowledge modules assign meaning to perceived events by fusing threat intelligence, attack graph constructs, behavioral baselines, and policy rules. The MITRE ATT&CK framework provides a standardized ontology, while proprietary feeds from CrowdStrike and Cortex XDR enrich detection with the latest indicators of compromise. Centralized knowledge stores ensure consistency; distributed repositories enhance local context awareness. Key evaluation criteria include coverage scope, update cadence, and the ability to reconcile conflicting sources without redundancy or bias.
Decision Engines and Analytical Frameworks
Decision engines synthesize perception outputs and knowledge context to determine risk and recommend responses. Architectures range from rule-based systems offering explainability, to statistical anomaly detectors adept at spotting deviations, to graph-based inference models that map entity relationships for multistage attack detection. Platforms like Microsoft Defender for Endpoint pair confidence scoring with explainable AI interfaces, enabling analysts to trace detections back to contributing features and accelerate validation.
Integrative Architectures and Data Flows
Orchestration layers coordinate synchronous pipelines for immediate correlation alongside asynchronous, event-driven streams—often leveraging Apache Kafka—for scalable, modular analysis. Hybrid designs route high-priority events through low-latency paths while funneling bulk telemetry into micro-batches for deep retrospective examination. This dual approach balances throughput, elasticity, and end-to-end latency requirements.
Strategic Evaluation Models
Security leaders employ frameworks such as the OODA loop, Belief-Desire-Intention cognitive models, the Kill Chain, and the Diamond Model of Intrusion Analysis to assess module synergy and emergent capabilities. Performance metrics—mean time to detect (MTTD), mean time to respond (MTTR), precision, recall, and alert fatigue indices—quantify operational efficiency. Comparative studies show that architectures with tightly integrated perception and knowledge modules can reduce false positives by up to 30%, while graph-based decision engines accelerate threat containment by 20–25%.
Deployment Contexts for Autonomous Agents
Optimal placement and configuration of AI agents across varied environments ensure comprehensive threat coverage. Deployment contexts include:
Network-Scale Deployments
Distributed agents act as sensors at data centers, branch offices, and cloud peering points. Lightweight edge modules detect anomalies early, while central inference clusters perform deep packet inspection and behavioral analytics. Integration with network detection and response platforms—such as Darktrace—leverages unsupervised learning models to establish baselines of “normal” traffic and flag subtle deviations, even within encrypted channels.
Endpoint and Workload Integration
Endpoint agents instrument kernel processes, user-mode activity, and in-memory execution to detect fileless attacks and living-off-the-land techniques. Solutions like CrowdStrike Falcon and Microsoft Defender for Endpoint combine on-device inference with cloud orchestration for cross-endpoint correlation, threat hunting, and automated response at scale.
Cloud-Native and Containerized Environments
AI agents interface with container orchestrators—such as Kubernetes—to monitor microservices, API calls, and resource utilization. Native detection services like AWS GuardDuty and Google Cloud Security Command Center embed AI agents within the provider’s infrastructure, enabling continuous assessment of configuration drift and malicious API behavior under the shared responsibility model.
Industrial Control Systems and IoT Networks
Resource-constrained MD sensors monitor industrial protocols—Modbus, DNP3, and proprietary SCADA communications—using passive or side-channel techniques. Vendors such as Claroty provide agent-lite appliances that inventory assets, track communication patterns, and detect command-sequence anomalies within segmented OT zones, safeguarding critical infrastructure operations.
Hybrid and Sector-Specific Architectures
Organizations with heterogeneous estates deploy hybrid agent architectures blending network, endpoint, and workload detection. Cross-domain correlation engines aggregate agent alerts with external feeds and historical incident data, mapping observations to MITRE ATT&CK techniques for prioritized response. Sector-specific adaptations include:
- Financial Services: Ultra-low latency agents monitor high-frequency trading systems and payment networks for transaction anomalies and insider threats, while supporting PCI DSS audit trails.
- Healthcare: Agents balance detection precision with HIPAA privacy requirements, distinguishing anomalous behavior in electronic health record systems and medical IoT devices without interrupting clinical workflows.
- Retail and E-Commerce: Agents integrate with point-of-sale networks and web application firewalls to detect payment card skimmers, credential harvesting, and unusual user journeys across online storefronts.
- Critical Infrastructure: Fault-tolerant agents operate under NERC CIP and IEC 62443 standards, providing early warning of coordinated attacks on utilities, transportation networks, and telecommunications backbones.
Risk-based models, kill-chain analysis, and resource-impact assessments guide agent placement and configuration, ensuring that detection coverage aligns with asset criticality and operational constraints.
Design Considerations and Performance Insights
Adopting autonomous AI agents requires careful balancing of architectural complexity, operational performance, and resource overhead. Security leaders should evaluate the following dimensions:
Component Complexity Versus System Overhead
Monolithic architectures minimize inter-module latency but complicate updates and scaling. Microservices designs enable independent component upgrades and horizontal scaling, though they introduce network serialization overhead. Clear API contracts and interface definitions facilitate targeted optimization of critical modules.
Scalability Trade-offs
Distributed agents processing parallel workloads require model synchronization. Eventual consistency reduces coordination delays but may produce temporary detection gaps, while strong consistency ensures uniform behavior at the cost of higher transport overhead. Organizations must align these trade-offs with latency requirements and autonomy preferences.
Accuracy Versus Latency
Ensemble learning models and multi-stage correlation pipelines improve detection precision and reduce false positives but demand greater compute cycles. Tiered decision frameworks conduct rapid initial scans for urgent threats, followed by in-depth secondary analysis, balancing speed and accuracy.
Resource Demand and Cost Management
AI inference and model training impose demands on CPU, GPU, memory, and storage resources. Elastic provisioning and usage-based scaling in cloud environments can optimize cost efficiency, while on-premises deployments may leverage hardware accelerators selectively for compute-intensive tasks.
Adaptability and Maintenance
Continuous learning loops sustain detection effectiveness but require staging environments for model validation, rollback mechanisms, and auditable change controls. Industries with stringent uptime mandates—such as healthcare and energy—often impose stricter update cadences to preserve stability.
Explainability and Analyst Trust
Transparent AI models that surface feature contributions, confidence intervals, and decision paths empower analysts to validate alerts and refine detection logic. Embedding contextual metadata—related historical events, threat intelligence matches, and policy references—enhances situational awareness and reduces triage time.
Integration with Security Ecosystems
Agents should support standardized data schemas—CEF, STIX/TAXII—and offer prebuilt connectors for SIEM, SOAR, and identity management platforms. Harmonized data flows enable unified dashboards, cross-system automation, and consolidated reporting, preventing siloed insights that obscure multi-stage attack patterns.
Robustness and Resilience Under Adversarial Conditions
Adversaries may attempt to poison models or exploit blind spots. Defensive measures—such as input sanitization, anomaly-based model monitoring, ensemble diversification, and graceful fallback modes (signature-based detection or manual escalation)—safeguard system integrity. Regular red-team exercises and adversarial testing detect drift early and restore efficacy before gaps widen.
Performance Benchmarking and Metrics
- True Positive Rate (TPR) and False Positive Rate (FPR)
- Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR)
- Throughput (events processed per second) and end-to-end latency
- Resource utilization under peak load
- Model drift indicators and retraining frequency
- Alert prioritization accuracy
Establishing baseline benchmarks under representative workloads guides capacity planning and supports compliance reporting. Continuous monitoring of metric trends reveals emerging constraints or model degradation, triggering proactive tuning or scaling measures.
Limitations and Future Directions
Despite their advanced capabilities, AI agents face inherent limitations: encrypted traffic and proprietary protocols may evade inspection, data biases can skew detections toward familiar patterns, and resource constraints may limit model complexity. Complementary defenses—network segmentation, manual threat hunting, and active deception—remain vital components of a layered security strategy. Looking forward, advances in hybrid human-AI workflows, edge inference, and quantum-enhanced analytics promise to address current gaps, while evolving data sovereignty regulations and privacy mandates will shape the design of context-aware, locally processing agents.
By thoughtfully balancing these design considerations and performance insights, security leaders can deploy autonomous AI agents that deliver scalable, adaptive, and transparent threat detection—prepared to meet the challenges of 2026 and beyond.
Chapter 3: Machine Learning Foundations

As organizations enter 2026, the security landscape has grown more complex and perilous. Traditional perimeter defenses no longer suffice against converging cyber and physical attack vectors. Ubiquitous connectivity, remote work, cloud adoption and the proliferation of Internet of Things devices have expanded the attack surface. Nation-state actors, organized cybercrime syndicates and opportunistic hackers exploit supply-chain compromises, fileless malware and advanced social engineering to disrupt operations and steal data. Operational technology networks converge with information technology systems, creating real-world safety risks in sectors such as energy, transportation and manufacturing. A successful breach can trigger production halts, safety incidents and regulatory violations with severe financial and reputational costs.
To counter these threats, organizations must shift from reactive, signature-based defenses to adaptive, intelligence-driven approaches. Real-time threat detection, context-aware analytics and proactive containment strategies are essential for resilience. In this context, autonomous AI agents emerge as a pivotal innovation, offering continuous monitoring, rapid decision-making and self-directed response capabilities that can outpace advanced adversaries.
Autonomous AI Agents as a Conceptual Framework
Autonomous AI agents represent a new paradigm in threat detection. Unlike traditional security tools that rely on static rules and manual intervention, autonomous agents integrate perception, knowledge, reasoning and learning in a unified architecture. They operate with a high degree of self-direction, continuously sensing their environment and adapting to emerging threats.
Key attributes of autonomous AI agents include:
- Self-governance, coordinating sensing and response workflows without manual orchestration
- Continuous learning, adapting to new threat patterns through online learning mechanisms
- Real-time autonomy, enabling sub-second threat identification and containment
- Collaborative intelligence, where multiple agents share insights to build a collective defense posture
Agents ingest diverse data streams—network telemetry, endpoint logs, user behavior analytics and external intelligence feeds—through perception modules. Knowledge repositories maintain formalized threat intelligence alongside contextual awareness of organizational assets and policies. Decision engines evaluate observations against evolving threat models, weighing risk factors and response options. Reinforcement learning techniques refine policies over time: upon detecting a novel threat, an agent triggers an immediate response—such as isolating an endpoint or throttling network access—while updating its internal models for improved future defense.
Drivers Accelerating AI-Based Threat Detection
Several factors are driving the rapid adoption of AI-driven threat detection and autonomous agent architectures:
- Escalating Attack Sophistication: Adversaries use polymorphic malware, living-off-the-land techniques and deepfake social engineering to evade static controls.
- Data Volume and Velocity: Security data streams—from network flows to cloud audit logs—have grown exponentially, overwhelming manual analysis.
- Workforce Constraints: Talent shortages and alert overload strain security teams, making automated triage and response essential.
- Real-Time Decision Needs: Rapid lateral movement of threats demands instantaneous containment without awaiting manual approval.
- Regulatory and Compliance Pressures: Frameworks such as GDPR and CCPA require demonstrable data protection controls and incident response audit trails.
- Cloud and Hybrid Architectures: Distributed environments introduce visibility gaps; agents ensure consistent monitoring across on-premises, cloud and edge.
Comparing Learning Paradigms for Threat Detection
The choice between supervised learning and reinforcement learning frameworks is a strategic decision that shapes detection capabilities and operational workflows.
Data Dependency and Labeling Requirements
Supervised models require labeled datasets of historical attacks and benign activity, creating labeling bottlenecks and potential dataset imbalances. Reinforcement learning reduces labeling overhead by interacting with simulated or live environments, using reward signals to guide learning. High-fidelity simulations or sandboxed environments are critical to avoid policies that perform poorly in production.
Adaptability to Evolving Threats
Supervised models detect known patterns but struggle with novel or polymorphic attacks until retrained. Reinforcement agents continuously refine policies through exploration and exploitation, adapting to changing adversary behaviors in real time. Safeguards are needed to prevent policy drift and ensure safe exploration.
Interpretability and Explainability
Supervised methods built on decision trees, random forests or gradient boosting offer clearer feature attributions and auditability. Tools such as TensorFlow support model visualization. Reinforcement learning policies, especially deep networks, are often opaque, requiring explainability layers or surrogate models to translate decisions into human-readable insights.
Training Complexity and Resource Considerations
Supervised training scales with dataset size and model complexity but benefits from parallelizable pipelines. Reinforcement learning demands extensive sampling of state-action trajectories and high-fidelity environment simulations, often necessitating specialized hardware accelerators and greater infrastructure investment.
Sample Efficiency and Convergence Time
Supervised models achieve high sample efficiency with labeled data and data augmentation. Reinforcement agents may require millions of interactions before policy convergence. Hybrid approaches that pretrain on labeled datasets before environment interaction can accelerate convergence.
Response Time and Real-Time Constraints
Supervised inference typically executes in milliseconds, suitable for high-throughput environments. Reinforcement-based decision engines may introduce additional latency due to sequential state evaluations; optimizations like model pruning and quantization help reduce response times.
Robustness Against Adversarial Manipulation
Supervised classifiers can be evaded by adversarial examples crafted to exploit model weaknesses. Reinforcement agents, with feedback-driven learning, can develop countermeasures but require explicit adversarial training or environment perturbations to maintain resilience.
Integration Within Existing Security Frameworks
Supervised models integrate smoothly via APIs with SIEM platforms and endpoint protection tools. Reinforcement agents require tighter coupling with enforcement mechanisms—such as automated containment systems and dynamic network segmentation—entailing more complex integration and strict access controls.
A comparative overview illustrates their complementary strengths:
- Supervised Methods: Pros: high interpretability, predictable resource demands, rapid inference Cons: limited adaptability, labeling bottlenecks, retraining latency
- Reinforcement Methods: Pros: continuous learning, reduced labeling reliance, adaptive resilience Cons: high computational overhead, opaque policies, integration complexity, risk of policy drift
Hybrid ensembles leverage both paradigms—using frameworks such as OpenAI Gym and Ray RLlib—to filter high-confidence threats with supervised classifiers and apply reinforcement-driven containment strategies. Feedback from adaptive modules enriches labeled datasets, creating a virtuous cycle of continuous improvement.
Deploying Models for Novel Threat Recognition
Recognizing zero-day exploits and polymorphic malware demands a shift from static training to continuous, context-driven adaptation. Deploying models for novel threat detection reshapes the architecture and governance of security analytics platforms.
Continuous Model Training and Adaptation
Continuous training pipelines enable agents to ingest telemetry and external intelligence in near real time. Solutions from Darktrace and Microsoft Azure Sentinel embed retraining triggers tied to anomalous event rates or flagged indicators of compromise. Governance mechanisms—such as drift detection and statistical quality gates—ensure retraining does not degrade performance or introduce bias.
Balancing Generalization and Specialization
Effective novel threat recognition balances broad anomaly detection with asset-specific specialization. Tiered model architectures funnel suspicious events from general detectors into specialized submodels for critical assets. Ensemble strategies combine unsupervised clustering with supervised classification to surface and validate context-rich anomalies.
Leveraging Transfer and Meta-Learning Frameworks
Transfer learning accelerates readiness by fine-tuning pre-trained models based on global threat intelligence—such as representations derived from CrowdStrike Falcon data—on local network logs. Meta-learning frameworks further enable rapid adaptation from few labeled examples, essential for low-frequency but high-impact attack types.
Contextual Feature Engineering and Embedding
Embedding temporal, spatial and behavioral contexts enhances sensitivity to irregular patterns:
- Temporal embeddings capturing session durations and sequence patterns
- Graph-based features mapping relationships between IP addresses, user accounts and devices
- User behavior profiles establishing baselines and flagging deviations for high-risk roles
Operational Implications and Strategic Considerations
Adaptive deployments require an integrated operating model blending AI-driven insights with human oversight:
- Explainability Tools: Platforms like IBM QRadar Advisor with Watson and Palo Alto Networks Cortex XDR supply contextual rationales for alerts.
- Cross-Functional Governance: Data scientists, threat hunters and compliance officers align on data retention, audit policies and performance SLAs.
- Resilience Planning: Redundant deployments across cloud and on-premises environments safeguard against service disruptions, with fallback rules maintaining baseline coverage during retraining.
Key Considerations in Model Selection and Adaptation
Model choice and adaptation strategies are shaped by data realities, operational constraints and regulatory frameworks. Critical considerations include:
- Data sufficiency and label reliability, ensuring representative and up-to-date samples
- Concept drift and model staleness, requiring online learning or scheduled retraining
- Adversarial vulnerability, mitigated through adversarial training and defense-in-depth
- Resource and latency constraints, balancing model complexity with real-time responsiveness
- Explainability and compliance, favoring transparent models or integrated interpretability layers
- Integration overhead, managing the complexity of ensemble or hybrid architectures
- Computational footprint and deployment topology, leveraging edge inference or split architectures
- Data governance and privacy, incorporating federated learning or differential privacy as needed
- Adaptation mechanisms, including canary testing, performance monitoring and automated rollback procedures
- Cross-disciplinary collaboration, aligning data scientists, security analysts and executive stakeholders
By adopting a holistic approach that integrates robust governance, continuous evaluation and cross-functional engagement, organizations can harness the full potential of machine learning for threat detection while maintaining resilience against evolving adversaries.
Chapter 4: Data Ecosystem and Integration
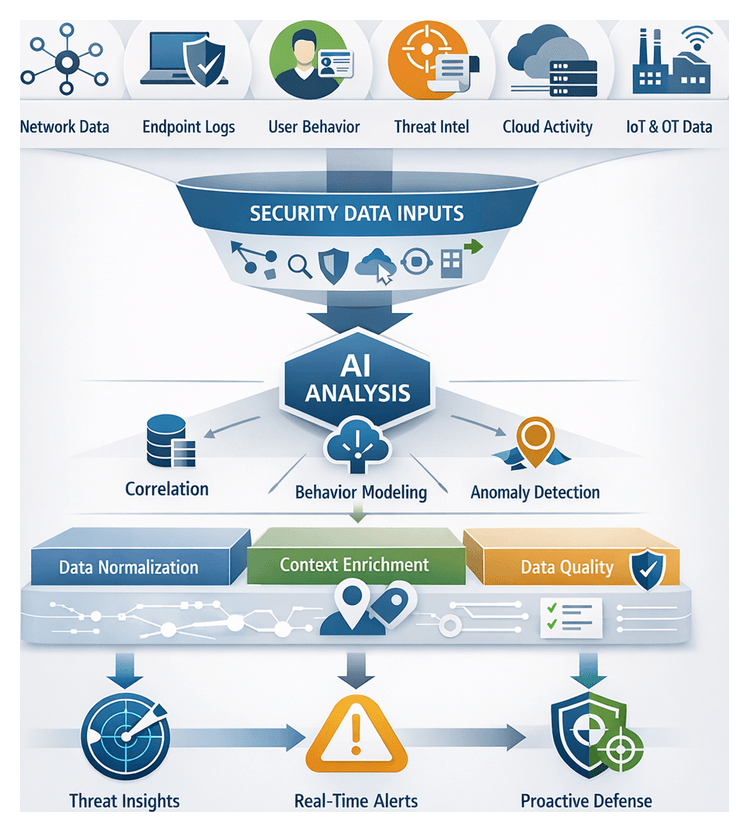
Security Data Inputs for AI-Driven Detection
AI-driven threat detection depends on a rich, diverse foundation of security data spanning network activity, endpoints, identities, applications, industrial systems, and external intelligence. Organizations operating across on-premises networks, cloud platforms, Internet of Things (IoT) deployments, and operational technology (OT) environments generate vast streams of telemetry, logs, and contextual signals. Autonomous agents synthesize these inputs to model baselines, detect anomalies, and predict emerging threats in real time. The following overview describes the core categories of security data that underpin next-generation detection architectures.
- Network Telemetry
- Endpoint and Workload Logs
- User and Entity Behavior Analytics (UEBA)
- Threat Intelligence Feeds
- Cloud and Application Activity Logs
- IoT and Operational Technology Sensor Data
- External Open Data Sources and Dark Web Indicators
Network Telemetry
Network telemetry—including packet captures, flow records, firewall logs, DNS queries, and proxy logs—reveals communication patterns and volumetric trends. AI agents analyze metadata such as protocol usage, session durations, and volumetric anomalies to detect lateral movement, data exfiltration, and command-and-control callbacks. Platforms like Splunk and Elastic ingest and index massive telemetry volumes for real-time correlation and retrospective hunts. Enrichment with geo-location databases and IP reputation services provides context for prioritizing alerts and isolating high-risk traffic.
Endpoint and Workload Logs
Endpoint detection and response (EDR) and workload protection solutions produce detailed logs of process executions, file accesses, registry modifications, and system calls. AI agents use these records to reconstruct attack kill chains, trace malware behaviors, and assign risk scores to hosts. Leading platforms such as CrowdStrike Falcon and Palo Alto Cortex XDR deliver continuous visibility into host activities and enable automated containment actions for anomalous behaviors.
User and Entity Behavior Analytics (UEBA)
As credential-based attacks and insider threats rise, UEBA platforms analyze authentication logs, access patterns, file transfers, and resource utilization to distinguish normal from anomalous behaviors. Solutions like Microsoft Sentinel feed AI models with enriched behavioral profiles, enabling detection of account takeovers, privilege misuse, and insider collusion. Correlating UEBA data with network and endpoint signals produces a holistic view that reduces false positives and accelerates investigations.
Threat Intelligence Feeds
External threat intelligence enriches local telemetry with indicators of compromise (IOCs), malware signatures, threat actor profiles, and emerging tactics. Feeds from commercial vendors, open-source communities, ISACs, and dark web monitoring services—such as Recorded Future and Anomali—supply dynamic blocklists and narrative intelligence. AI agents match local events against IOCs and leverage threat actor trends to adapt detection rules proactively.
Cloud and Application Activity Logs
Cloud platforms emit audit trails, API call logs, configuration changes, and access records via services like AWS CloudTrail, Azure Activity Log, and Google Cloud Audit Logs. Web application firewalls and performance monitors add event streams reflecting user interactions and anomalous HTTP requests. AI agents correlate cloud and on-premises telemetry to detect misconfigurations, token misuse, privilege escalations, and suspicious administrative actions, recommending policy adjustments and automated remediation.
IoT and Operational Technology Sensor Data
Industrial control systems, smart buildings, and critical infrastructure rely on sensors, PLCs, and embedded devices communicating over protocols such as Modbus, DNP3, and OPC UA. Specialized collectors ingest SCADA traffic, vibration and energy meter readings, and firmware inventories. Platforms like Nozomi Networks and Claroty enable AI models to detect deviations from process norms, unauthorized firmware changes, and lateral movement between IT and OT networks.
External Open Data Sources and Dark Web Indicators
Public repositories such as the National Vulnerability Database and exploit archives, combined with dark web monitoring by platforms like Intel 471, reveal zero-day disclosures, planned ransomware campaigns, and credential sales. Integrating these open data streams with internal telemetry and commercial intelligence enables forward-looking detection, allowing AI agents to adjust focus on emerging exploit patterns before full-scale attacks occur.
Harmonizing and Normalizing Security Data
Diverse data sources require alignment against common models and contextual enrichment to support accurate cross-domain analytics. Effective harmonization strategies encompass schema alignment, canonical modeling, metadata tagging, and temporal and spatial consistency frameworks. These foundations enable unified feature sets for machine learning and graph-based analyses.
Semantic Schema Alignment
Aligning source-specific attributes—IP addresses, user IDs, event types—to a unified vocabulary prevents semantic drift. Teams often extend frameworks such as MITRE ATT&CK to include organizational roles, regulatory contexts, and custom threat classes. Layered schema strategies maintain core entity consistency while accommodating evolving peripheral attributes, preserving correlation integrity and alert enrichment.
Canonical Data Modeling
A flexible canonical model bridges heterogeneous formats by ingesting each feed into a neutral representation capturing both event details and security context. Versioned schema contracts ensure backward compatibility and traceability as fields evolve. This approach balances the need for forensic granularity with real-time processing constraints.
Metadata Enrichment and Contextual Tagging
Enriching raw inputs with geolocation confidence, user risk scores, historical anomaly indices, asset criticality, and vulnerability tags transforms data into actionable intelligence. Metadata tags guide automated decision engines and provide transparent hooks for analysts to understand AI reasoning, strengthening trust in outcomes.
Temporal and Spatial Consistency Frameworks
Consistency frameworks align timestamps across time zones, reconcile clock drift, and map network segments and cloud regions into unified topologies. Sliding-window analyses preserve event order, while watermarking flags ingestion delays. These measures prevent misclassification of routine activities and ensure reliable anomaly detection over synchronized timeframes.
Interpretive Frameworks
Normalized data can be analyzed using multi-dimensional vector modeling for unsupervised clustering and anomaly scoring, or probabilistic graph models where entities become nodes linked by communication edges. Blending these approaches enables identification of suspicious corridors of activity and scoring of individual events, provided normalization integrity is maintained through cross-disciplinary validation exercises.
Normalization in Vendor Ecosystems
Vendors embed normalization modules within their platforms: Splunk offers the Common Information Model, IBM QRadar uses Device Support Modules, and Elastic Security integrates ingest pipelines with processors for date, geolocation, and threat enrichment. Organizations evaluate built-in strategies against adaptability needs, supplementing with custom microservices or community libraries to fill protocol gaps.
Governance and Adaptive Normalization
Data stewardship councils comprising IT operations, risk, compliance, and threat intelligence define normalization policies, approve schema changes, and oversee testing. Guardrail models combine non-negotiable rules with extension points for novel feeds. Looking ahead, AI-driven pattern recognition promises self-supervised inference of canonical structures, requiring validation mechanisms for schema drifts and clear analyst intervention pathways.
Ensuring Data Quality for Accurate Detection
Data quality—completeness, consistency, timeliness, accuracy, and relevance—directly impacts detection performance. Autonomous agents processing flawed or incomplete inputs generate elevated false positives and negatives, delayed alerts, and model drift. The following dimensions and strategies outline how to assess and enhance data ecosystems for optimal threat detection.
- Completeness and Coverage: Gaps in network flows or endpoint logs hinder correlation, increasing dwell times. Organizations with under 80 percent log coverage in critical segments experience up to 30 percent longer breach dwell times.
- Consistency and Standardization: Disparate formats and timestamp conventions require canonical schemas—such as OCSF—or tools like Splunk AI Advisor to standardize events and reduce heuristic workarounds.
- Timeliness and Latency: Streamed ingestion pipelines, exemplified by Microsoft Sentinel, minimize lag to support real-time anomaly detection. Legacy batch transfers introduce blind spots.
- Accuracy and Veracity: Misconfigured sensors, faulty collectors, or adversarial poisoning degrade analytic trust. Automated integrity checks aligned with NIST controls ensure only authentic data feeds models.
- Relevance and Representativeness: Domain-specific behaviors—such as medical device telemetry—require custom enrichment. Off-the-shelf models often underperform without tailored threat intelligence, as recommended by Elastic Security.
Domain-Specific Data Quality Challenges
- Network Traffic: Packet sampling and drops impede detection of low-and-slow exfiltration. Cisco Secure Network Analytics addresses this with enriched flow metadata but relies on robust capture strategies.
- Endpoint Telemetry: Sensor misconfigurations and agent version mismatches—common in deployments of CrowdStrike Falcon or VMware Carbon Black—fragment host visibility.
- Cloud and Containers: Ephemeral logs and inconsistent tagging across auto-scaled workloads generate noise and blind spots.
- OT and ICS: Proprietary protocols and infrequent communications challenge agents trained on IT data. Platforms like Nozomi Networks and Claroty provide specialized collectors for industrial traffic.
- User Behavior Analytics: Incomplete identity resolution and inconsistent multi-factor authentication logs dilute anomaly baselines, increasing false positives.
Assessing Data Quality
- Data Quality Maturity Model: Guides progression from ad hoc collection to optimized, monitored pipelines, prioritizing schema validation and redundant collectors.
- NIST SP 800-150: Prescribes minimum logging elements for threat scenarios, enabling enriched datasets through asset context and intelligence tags.
- Forrester Data Quality Framework: Aligns quality KPIs—false alert reduction, mean time to detection—with business risk, securing investment in foundational improvements.
Impacts of Poor Data Quality
- False Positives: Incomplete or inconsistent data inflates benign anomalies, overwhelming analysts and delaying response.
- False Negatives: Missing telemetry creates blind spots exploited by advanced actors.
- Detection Latency: Ingestion delays extend adversary dwell times.
- Model Drift: Static schemas and outdated training sets degrade relevance, missing new attack patterns.
- Compliance Risks: Incomplete audit trails expose organizations to regulatory fines and reputational harm.
Strategies to Improve Data Quality
- Data Governance and Ownership: Clear stewardship for each source ensures schema consistency and quality monitoring.
- Automated Validation and Profiling: Continuous profiling detects schema drifts and ingestion anomalies for proactive remediation.
- Domain-Enriched Models: Augment logs with MITRE ATT&CK mappings, asset criticality, and vulnerability scores for richer feature engineering.
- Cross-Domain Data Fusion: Federated query and semantic harmonization across IT, OT, cloud, and identity sources enable composite threat insights.
- Continuous Feedback Loops: Analyst input refines data classifications and exception handling, strengthening model trust over time.
Integrating Diverse Data Streams
Bringing together heterogeneous security data into a unified analytics architecture presents challenges across governance, scalability, interoperability, and compliance. A principled integration strategy balances these dimensions to deliver resilient, adaptable detection ecosystems.
Data Governance and Quality Assurance
- Implement a centralized metadata registry capturing source attributes, ingestion timestamps, schema versions, and transformation histories to support traceability and root-cause analysis.
- Define stewardship roles accountable for de-duplication, timestamp reconciliation, and semantic validation of log fields.
- Schedule periodic data profiling to measure completeness, consistency, and accuracy, guiding feed enhancements or decommissioning.
- Apply risk-based data classification at ingestion, enforcing masking, encryption, and retention policies for sensitive or regulated data.
Scalability and Performance Trade-offs
- Combine centralized data lakes with streaming platforms to ensure hot-path analytics leverage in-memory or partitioned stores optimized for low-latency inference.
- Use orchestration frameworks that decouple compute from storage, allowing parallelism adjustments without duplicating raw datasets.
- Establish end-to-end latency benchmarks from ingestion to alert generation, tuning partitioning strategies and identifying pipeline bottlenecks.
- Plan elastic capacity for peak ingestion events—major software updates or global incidents—and align provisioning with budget cycles.
Interoperability and Vendor Ecosystems
- Adopt standards such as STIX/TAXII for threat intelligence and Common Event Format for logs to reduce transformation overhead and future-proof integrations.
- Evaluate vendor support for modular connectors and extensible SDKs enabling bi-directional data flow between detection, ticketing, and orchestration systems.
- Maintain an inventory of licensed components, open-source libraries, and custom integrations, reviewing periodically for end-of-life risks.
- Conduct interoperability tests validating schema compliance, throughput, and error handling under simulated loads.
Security and Compliance Constraints
- Enforce fine-grained access controls and role-based policies at the pipeline level to restrict sensitive data fields to authorized processes.
- Apply end-to-end encryption for data in transit and at rest, backed by robust key management aligning with audit and compliance requirements.
- Perform privacy impact assessments to document lawful bases for personal data processing and retention under relevant regulations.
- Capture audit logs of data access, model training, and inference outcomes to support forensic investigations and compliance demonstrations.
Continuous Monitoring and Adaptation
- Define KPIs for pipeline health—ingestion completeness, transformation error rates, and model drift alerts—to drive proactive maintenance.
- Schedule architecture reviews aligned with intelligence updates, assessing the need for new data feeds or normalization adjustments.
- Adopt a modular integration approach, treating data connectors as replaceable components for rapid onboarding of innovative sources.
- Establish cross-functional governance forums—including security operations, data engineering, legal, and compliance—to evaluate and approve pipeline changes.
By aligning governance rigor with operational agility, planning for scalable performance, ensuring interoperability, and embedding continuous monitoring, organizations can integrate diverse security data streams into cohesive detection ecosystems. Such resilient architectures evolve alongside adversary tactics and regulatory mandates, sustaining effective AI-driven threat detection.
Chapter 5: Real-Time Analytics and Decision Making
Security Landscape and the Imperative for AI-Driven Defense
As organizations enter 2026, the security environment is more complex and dynamic than ever. Boundaries between cyber and physical domains have dissolved, enabling supply chain compromises, deepfake-enabled social engineering, and coordinated campaigns that disrupt digital systems, operational technology, and safety-critical infrastructure simultaneously. Nation-state actors and criminal syndicates exploit legacy defense gaps, mixing zero-day exploits with human-operated ransomware and targeted data exfiltration to maximize impact.
The proliferation of connected devices—from industrial control systems to consumer Internet of Things—expands the attack surface exponentially. Each endpoint becomes both a potential intrusion vector and a dependency nexus, where a breach on a low-value sensor network can cascade through production lines or critical services. Concurrently, networks now generate petabytes of logs, flows, and events daily, overwhelming security teams struggling to identify actionable indicators in a constant data firehose.
Physical safety and cyber resilience are inseparable imperatives. An attack that disables factory robotics or manipulates building controls can jeopardize human life and erode public trust. In this context, static, manual security practices have become obsolete. Organizations must adopt solutions capable of continuous adaptation, real-time analysis, and autonomous response to stay ahead of rapidly evolving threats.
Conceptual Framework of Autonomous AI Agents
Autonomous AI agents represent a next-generation paradigm for continuous threat detection and response. These software entities integrate four core attributes:
- Perception modules that collect and preprocess diverse data streams—network telemetry, endpoint sensors, user behavior analytics, and external intelligence.
- Knowledge repositories storing historical patterns and evolving threat intelligence, enabling contextualization of observations against a rich informational backdrop.
- Decision engines employing machine learning and heuristic reasoning to detect anomalies, assess risk, and determine appropriate countermeasures.
- Adaptive learning loops that refine models over time by incorporating feedback from successful detections and false-positive tuning.
Unlike static signature engines and rule-based systems that require constant manual updates, autonomous agents discover new indicators of compromise through self-learning and orchestrate countermeasures with minimal human intervention. This reduces mean time to detection and response while scaling to complex, distributed environments. Leading implementations include Splunk AI-Driven Security Analytics, and Microsoft Sentinel, each combining modular architectures with real-time inference and automated containment across cloud-native and on-premises deployments.
Drivers Accelerating AI-Based Threat Detection
Several converging factors compel organizations to embrace AI-driven threat detection:
- Escalating Attack Sophistication: Adversaries leverage supply chain poisoning, living-off-the-land techniques, encrypted command-and-control, and deepfakes that static defenses cannot counter.
- Explosion of Data Volume: Enterprise environments process millions of security events per second across distributed cloud and edge networks, overwhelming rule-based filtering and leading to alert fatigue.
- Demand for Real-Time Decisions: High-impact breaches unfold in minutes; organizations require instantaneous detection and automated response to contain lateral movement and prevent data exfiltration.
- Resource and Talent Constraints: The cybersecurity skills gap leaves teams understaffed and overextended. Autonomous agents augment human expertise by automating routine analysis and incident triage.
- Regulatory and Liability Pressures: Data privacy regulations such as GDPR and CCPA, along with emerging AI governance frameworks, demand transparent, auditable security controls.
- Convergence of IT and OT Security: Integrated visibility across operational technology and information technology is essential for holistic threat detection in industrial and critical infrastructure settings.
Together, these drivers create an imperative for solutions that combine high-throughput data ingestion, adaptive learning, and automated orchestration—characteristics inherent to the autonomous agent model.
Correlation Techniques for Anomaly Detection
Effective anomaly detection involves aggregating and contextualizing disparate signals into coherent threat narratives. Correlation techniques elevate isolated deviations into actionable insights by applying three foundational principles:
- Temporal Association: Align events by timestamp to uncover sequences or clusters indicating causality.
- Contextual Linkage: Overlay metadata—user identities, geolocation, process hierarchies—to tie events across infrastructure layers.
- Analytical Weighting: Use probabilistic or heuristic scoring to quantify relationship strength between events.
Statistical Correlation Models
Statistical frameworks track co-occurrence frequencies and baseline distributions, employing metrics such as Pearson’s correlation coefficient or mutual information to quantify relationships. Configurable modules in platforms like Splunk and Elastic SIEM enable tuning of sensitivity thresholds to balance false positives and detection coverage across high-velocity data streams.
Graph-Based Detection Frameworks
Graph analytics model entities—users, devices, processes—as vertices and interactions—network connections, file operations, API calls—as weighted edges. Traversal algorithms and community detection reveal anomalous subgraphs indicative of lateral movement or command-and-control infrastructures. Solutions such as IBM QRadar integrate graph databases to accelerate detection of stealthy, multistage intrusions, though adoption requires substantial compute resources and graph-theory expertise.
Sequence and Temporal Analysis
Sequence mining and time-series analysis identify recurrent event chains that diverge from established workflows. Sliding window techniques, hidden Markov models, and burst detection uncover anomalous patterns such as off-hours database queries or latency anomalies. Stream processors like Apache Flink and Esper enable continuous sequence detection at scale, but maintaining relevance demands adaptive window sizing and contextual filters to reduce spurious alerts.
Integrated Threat Context Correlation
Fusing internal telemetry with external threat intelligence enriches event streams with reputational scores, vulnerability data, and threat feeds. Microsoft Sentinel exemplifies this approach with native connectors and real-time feed updates. Centralized threat context repositories and metadata normalization ensure consistent enrichment without amplifying noise.
Evaluative Metrics and Interpretive Frameworks
Organizations assess correlation techniques using metrics such as detection latency, mean time to acknowledgement, false positive rate, and recall. Interpretive frameworks including the Kill Chain, MITRE ATT&CK matrix, and Pyramid of Pain guide coverage gap analysis and prioritize detection of adversary behaviors over low-level artifacts. Emerging trends involve adversarial training of correlation models, graph neural networks for dynamic relationship weighting, and the integration of explainable AI toolkits to enhance transparency and trust.
Operational Scenarios for Automated Countermeasures
Autonomous agents translate real-time detections into immediate actions across multiple domains. Understanding these scenarios helps organizations evaluate impact, governance requirements, and strategic benefits.
Endpoint Security and Host Containment
Agents monitor process behavior, file system changes, and memory usage to detect malware, ransomware, or lateral movement. High-confidence detections trigger host isolation, process termination, and token revocation. CrowdStrike Falcon uses behavioral AI to quarantine devices and rollback file changes, mapping containment actions to MITRE ATT&CK stages to ensure context-driven response.
Network Threat Isolation and Traffic Shaping
Streaming analytics identify volumetric anomalies and unauthorized protocols, prompting automated traffic shaping, blackhole routing, or micro-segmentation at enforcement points. Darktrace employs self-learning AI to adjust network segmentation dynamically, reducing manual ticketing and accelerating mitigation across hybrid infrastructures.
Cloud-Native Automated Remediation
Agents monitor cloud service logs, container orchestration events, and configuration drift to detect misconfigurations or compromised orchestration controllers. Automated remediation via infrastructure-as-code pipelines rolls back to known-good states, revokes compromised credentials, or enforces runtime policies. Microsoft Sentinel integrates AI-driven rule engines with Azure Automation runbooks, aligning measures with NIST SP 800-61 guidelines and improving mean time to remedy.
Operational Technology and IoT Response
In OT and IoT contexts, agents analyze sensor data, control loop feedback, and protocol communications for unauthorized commands or spoofing. Confirmed threats can trigger safety protocols—equipment shutdowns, subnet isolation, or manual control handoffs—while conforming to regulatory and safety standards. Palo Alto Networks Cortex XDR illustrates deep packet inspection and behavior analytics tailored for industrial environments.
Identity-Based Interventions
User and entity behavior analytics detect anomalies such as unusual login locations, privilege escalations, or data access bursts. Automated countermeasures include forced password resets, step-up authentication challenges, and temporary privilege revocations. IBM QRadar Advisor with Watson combines anomaly detection with identity governance, triggering SOAR workflows that automate case creation, stakeholder notifications, and policy enforcement.
Cross-Domain Orchestration and Escalation
Complex incidents spanning endpoint, network, cloud, OT, and identity domains require coordinated actions. Multi-agent networks share threat context to execute joint response strategies—combining device quarantine, network segmentation, cloud rollback, and identity lockouts. Splunk Phantom maps events to end-to-end playbooks with role-based approvals, audit trails, and back-out procedures, ensuring synchronized, accountable orchestration.
Strategically, organizations must define clear risk appetites, decision policies, and governance frameworks that blend human expertise with AI autonomy. Continuous validation, tuning, and post-incident reviews sustain trust in automated systems and align countermeasures with operational objectives.
Balancing Speed, Accuracy, and Alert Prioritization
Real-time analytics platforms must strike an ongoing balance between detection velocity, predictive precision, and effective alert prioritization. This equilibrium adapts to evolving threat landscapes, changing data patterns, and organizational risk tolerances.
Managing Speed-Accuracy Trade-offs
Key approaches include:
- Adaptive Latency Budgeting: Allocate dynamic processing priorities—critical indicators pass through lightweight, high-priority pipelines, while lower-severity anomalies undergo richer analysis.
- Progressive Model Refinement: Deploy multi-stage decision engines that apply simple heuristics first, followed by computationally intensive classification or clustering for validation.
- Contextual Feature Prioritization: Focus on high-impact features—such as sudden privilege escalations or anomalous process spawns—to reduce overhead while preserving detection efficacy.
- Model Confidence Scoring: Tag alerts with confidence metrics to guide automated responses or human reviews, balancing speed with certainty.
Alert Prioritization Frameworks
To prevent operational overload, organizations implement:
- Risk Scoring and Enrichment: Composite risk scores incorporate asset criticality, threat severity, user context, and temporal or geospatial factors. Enrichment with threat intelligence and incident history provides narrative context.
- Dynamic Thresholding and Suppression: Real-time adjustment of sensitivity levels and suppression of repetitive, low-impact alerts maintain focus on novel or dangerous events.
- Analyst Workload Management: Automated case assignment routes alerts to teams based on expertise, shift schedules, and historical workloads, preventing fatigue and improving mean time to resolution.
Operational Limitations and Continuous Optimization
- Data Quality Gaps: Diverse telemetry sources can introduce blind spots and schema inconsistencies. Continuous monitoring of data health and fall-back detection mechanisms are essential.
- Model Drift and Concept Evolution: Legitimate behavior patterns evolve with new collaboration tools and remote work habits. Drift monitoring and regular retraining keep models accurate and reduce false positives.
- Adversarial Evasion: Attackers probe detection thresholds and use slow-burn exfiltration or encrypted channels to blend in. Adversarial training and simulated evasion scenarios harden models against these tactics.
- Resource Contention and Scalability: Low-latency pipelines demand significant compute, storage, and network resources. Capacity planning, cloud-native autoscaling, and distributed processing architectures prevent bottlenecks.
- Alert Fatigue: High volumes of low-value alerts can desensitize analysts. Continuous tuning, suppression rules, and clear escalation criteria preserve attention for truly critical incidents.
Strategic Imperatives for Ongoing Optimization
- Closed-Loop Feedback: Implement analyst feedback mechanisms to capture false positive and false negative cases for model tuning and pipeline improvements.
- Clear Metrics and Service Levels: Define KPIs such as mean time to detection, alert triage time, and acceptable false positive rates. Service-level agreements drive accountability across security, IT, and development teams.
- Modular, Microservices Architectures: Decouple functions—feature extraction, anomaly detection, scoring, enrichment—into independent services for scalability and rapid iteration.
- Explainability and Transparency: Incorporate explainable AI techniques that produce human-readable rationales for automated decisions, building trust and facilitating audits.
- Alignment with Business Risk: Regularly review detection objectives, alert parameters, and response workflows with stakeholders to ensure synchronization with risk appetite, regulatory obligations, and strategic initiatives.
By integrating autonomous AI agents with human expertise under a governance framework that emphasizes continuous feedback, transparency, and alignment with business risk, organizations can build resilient defenses capable of proactive threat detection and adaptive response in an ever-changing security landscape.
Chapter 6: Multi-Agent Collaboration and Human-AI Teaming
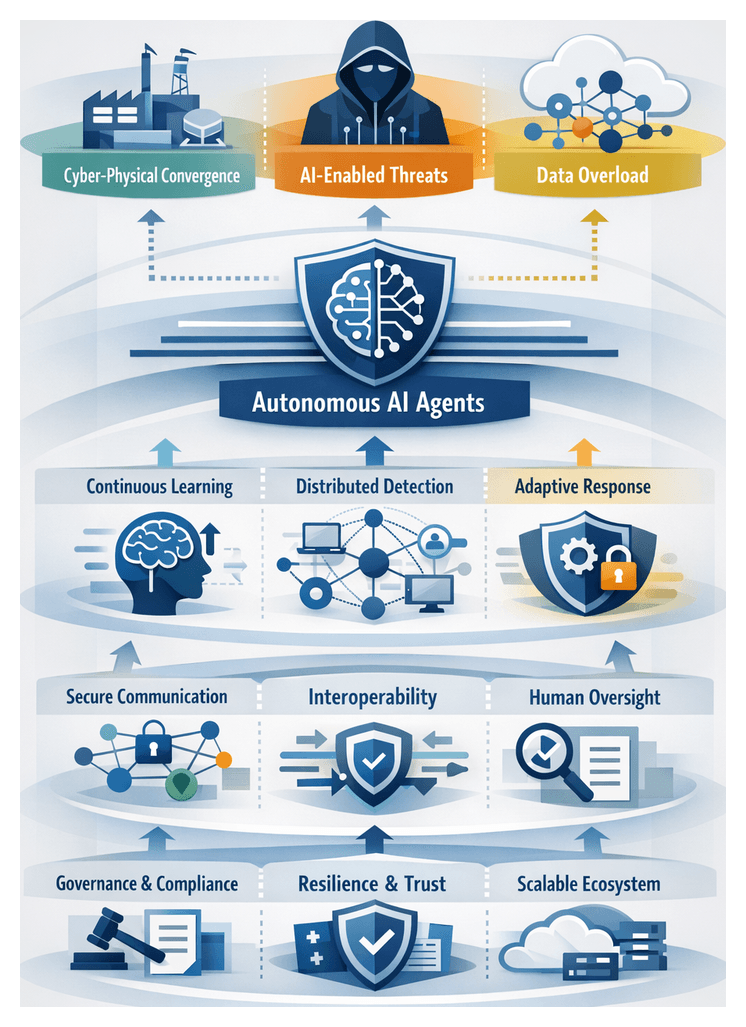
Security Landscape and the Rise of Autonomous Agents
Organizations entering 2026 face a security environment shaped by the seamless convergence of information technology and operational technology. Cloud-native platforms, edge computing and billions of Internet of Things endpoints enable real-time data flows but also offer adversaries pivot points into critical infrastructure and manufacturing processes. Recent incidents—from deepfake audio used to bypass call-center authentication to sophisticated firmware exploits in medical devices—underscore how rapidly threats have evolved beyond traditional IT perimeters.
Three dominant trends define this landscape:
- Cyber-Physical Convergence: Attackers deploy lateral movement through IoT and OT devices, targeting industrial control systems to disrupt production lines or public safety networks.
- AI-Enabled Adversaries: Malicious actors leverage custom machine learning models for automated reconnaissance, vulnerability discovery and generation of polymorphic malware that adapts to evade signature-based defenses.
- Data Proliferation and Noise: Telemetry volumes—from network flows to user behavior analytics—have grown exponentially, overwhelming legacy security information and event management systems and hindering timely incident analysis.
Coupled with geopolitical tensions and competitive pressures, these trends have elevated ransomware campaigns, supply chain compromises and disinformation operations to business-critical threats. Financial institutions contend with synthetic identity fraud at scale, healthcare providers face ransomware attacks that jeopardize patient care, and manufacturing firms grapple with stealthy insertion of counterfeit components.
Regulatory frameworks such as the EU’s NIS2 Directive and sector-specific mandates in energy, transportation and healthcare impose strict requirements for continuous monitoring, rapid incident reporting and resilience testing. Non-compliance can trigger substantial fines, reputational damage and operational shutdowns. Consequently, security leaders recognize that manual processes and static detection engines are insufficient for the speed and sophistication of modern threats.
Autonomous AI agents usher in a new defensive paradigm by marrying machine-speed analytics with adaptive decision logic. Key capabilities include:
- Continuous Learning: Models retrain dynamically on inbound telemetry to recognize previously unseen tactics, techniques and procedures without human intervention.
- Distributed Detection: Lightweight agents deployed across endpoints, cloud workloads and network segments collaborate in real time, sharing contextual insights to improve collective visibility.
- Adaptive Response: Decision engines enforce policy-driven containment actions—such as network microsegmentation or credential revocation—while escalating high-severity incidents to human analysts.
- Scalable Throughput: Architectures optimized for streaming analytics process millions of events per second, maintaining low latency and high accuracy under peak load.
Early adopters using platforms, like those listed on AgentLinkAI, report 50–70 percent reductions in mean time to detect and respond, as agents autonomously uncover supply chain tampering, insider reconnaissance and firmware-level compromises that bypass conventional analytics. By shifting the detection workload to machine-driven agents, security teams can redirect human expertise toward strategic threat hunting and post-incident analysis.
Architectural Foundations of Multi-Agent Collaboration
Effective multi-agent ecosystems hinge on carefully designed communication, interoperability, resilience and performance. Security architects evaluate agent networks through analytical frameworks that quantify robustness, scalability and semantic coherence.
Communication Paradigms
Agent communication models range from centralized broker architectures to fully decentralized peer-to-peer meshes. Centralized systems—where agents publish events to a message bus for orchestration services to aggregate and route—simplify governance and auditing but risk single-point failures. Decentralized meshes enable direct context sharing, reducing latency and enhancing resilience, though they introduce complexity in maintaining consistency and conflict resolution. Metrics such as degree centrality, average path length and clustering coefficients from network theory provide quantitative measures of each paradigm’s fault tolerance and communication overhead.
Interoperability and Standardized Protocols
Seamless collaboration among heterogeneous agents requires adoption of open data models and transport protocols. The STIX (Structured Threat Information Expression) and TAXII (Trusted Automated eXchange of Indicator Information) standards underpin semantic integrity for threat indicators, while RESTful APIs, AMQP or MQTT ensure quality-of-service features like guaranteed delivery and prioritization. Security orchestration and response platforms such as Cortex XSOAR extend interoperability through extensive connector libraries, schema validation and rapid onboarding of new exchange formats.
Analytical Metrics and Topology Visualization
Quantitative evaluation of inter-agent exchanges focuses on end-to-end latency, delivery reliability (error and loss rates), message fidelity and encryption integrity. Operational teams leverage graph analytics tools—such as those available in Splunk Phantom—to visualize communication topologies, identify chokepoints and optimize peer relationships. Performance tuning techniques including asynchronous buffering, batch transmission and differential compression allow teams to balance throughput against resource constraints.
Semantic Ontologies and Dynamic Context Propagation
Agents interpret shared content through common ontologies defining threat taxonomies, actor profiles and environmental context. Extensions like CybOX align observed behaviors with STIX indicators, while custom taxonomies map proprietary event types to standardized categories. Beyond static data, agents propagate evolving context profiles—risk scores, confidence levels and behavioral tags—enabling peers to adjust detection thresholds in real time. Authentication mechanisms and source validation guard against context poisoning and spoofed signals.
Trust Models, Resilience and Privacy
Secure multi-agent ecosystems rely on certificate-based mutual authentication, public key infrastructures and hardware security modules to protect sensitive exchanges. Role-based trust hierarchies govern which agents can share specific information classes—threat indicators, forensic artifacts or enforcement commands. Redundant communication paths, automatic failover and partition healing ensure continuity under node failures or network disruptions. Privacy and data minimization strategies—field redaction, hashing, secure multi-party computation and homomorphic encryption—address GDPR, HIPAA and CCPA obligations, enabling rich context sharing without exposing raw personal data.
Emerging Interpretive Frameworks
Interdisciplinary models from social network analysis, game theory and adaptive coding theory enrich agent communication strategies. Influence propagation techniques predict how threat intelligence disseminates across agent clusters and identify inoculation points to disrupt adversarial coordination. Adaptive encoding schemes adjust message formats in response to observed loss or tampering, preserving semantic integrity under hostile network conditions. These advanced interpretive lenses guide protocol design toward collaborative advantage in dynamic threat environments.
Human Oversight, Augmentation and Collaborative Sensemaking
Autonomous agents transform the security operations center by automating triage, threat detection and containment. Human professionals evolve from manual responders into strategic supervisors, interpreters of AI insights and stewards of ethical accountability.
Balancing Autonomy with Accountability
Layered governance models calibrate agent decision rights to preserve agility while maintaining human control over critical actions. Agents execute routine tasks—quarantining endpoints, blocking malicious IPs—automatically, yet escalate novel or high-impact events for analyst approval. Explicit thresholds based on anomaly severity, asset criticality and regulatory mandates ensure that autonomous responses align with organizational risk appetite.
Human-in-the-Loop and Human-on-the-Loop Postures
In human-in-the-loop contexts, AI agents defer enforcement of containment or remediation until an analyst validates recommendations—a model suited to regulated industries or environments with low tolerance for autonomous impact. The human-on-the-loop approach grants agents greater independence, with humans monitoring outcomes and intervening retrospectively if necessary, optimizing response speed in mission-critical, high-throughput settings. Dynamic oversight policies adjust these postures in real time based on agent confidence scores and threat severity.
Augmenting Analyst Capabilities and Distributed Cognition
AI agents act as cognitive amplifiers, surfacing subtle correlations, predicting attack trajectories and contextualizing alerts with historical intelligence. Summarized investigative briefs, prioritized hypotheses and visual kill-chain mappings free analysts from repetitive triage tasks and reduce alert fatigue. Bidirectional feedback loops allow human expertise to refine agent models—labeling false positives, enriching contextual datasets and guiding retraining—creating a cycle of continuous improvement and collective intelligence.
Trust Calibration and Explainability
Transparent confidence scores, anomaly severity indices and provenance metadata empower analysts to assess the reliability of agent recommendations. Explainability features that reveal the key factors driving AI decisions accelerate validation and foster progressive trust, enabling incremental increases in agent autonomy without sacrificing oversight.
Sector-Specific and Ethical Considerations
Oversight practices vary by sector and organizational maturity. Financial services embed multiple human checkpoints for transaction anomalies; healthcare environments emphasize patient privacy and require consent verification; critical infrastructure operators maintain dedicated supervisory consoles for real-time agent monitoring. Ethics committees periodically audit agent behavior to detect bias, enforce privacy-by-design principles and prevent discriminatory outcomes. Cultivating a culture of shared responsibility and transparent communication ensures that human and machine work in partnership toward resilient security operations.
Training, Metrics and Governance Models
Security professionals require training in AI literacy, model validation techniques and interpretability analysis. RACI (Responsible, Accountable, Consulted, Informed) frameworks delineate roles for agents and human stakeholders at each stage of detection and response. Key performance indicators—time to validation, reduction in false positives, analyst trust scores and prevented adverse outcomes—measure oversight effectiveness and guide iterative refinements in workflows and governance policies.
Integration, Governance and Sustainable Ecosystems
Deploying multi-agent systems at scale demands coordinated organizational structures, robust governance frameworks and a commitment to continuous improvement. Cross-functional steering committees—comprising security engineers, incident responders, data scientists, risk managers, legal and business representatives—define strategic objectives, risk thresholds and performance benchmarks for agent deployments.
Governance Frameworks and Best Practices
Core controls from the NIST Cybersecurity Framework and ISO 27001 establish asset management, access control and incident management protocols. AI-focused extensions address model transparency, data lineage, version control and drift detection. Policies on data sourcing, retention, anonymization and sharing standardize agent data processes. Embedding ethics-by-design mitigates algorithmic bias and upholds stakeholder privacy, while automated policy enforcement tools provide real-time compliance monitoring and rapid detection of deviations.
Technical Integration and Interoperability
Harmonizing diverse agent technologies requires standardizing on transport protocols (gRPC, AMQP), serialization formats and schema registries. Service discovery mechanisms support dynamic agent orchestration, and unified management layers simplify heterogeneous deployments. Robust encryption, key management and end-to-end logging ensure data integrity and provide visibility into inter-agent interactions.
Open Standards and Extension Strategies
Adopting open protocols—such as OpenC2 for command and control and Schema.org-based metadata conventions—reduces vendor lock-in and accelerates integration of third-party solutions. Capability negotiation layers enable agents to adjust communication parameters for peer compatibility, while backward compatibility roadmaps ensure legacy systems coexist with future agent releases without disruption.
Risks, Mitigation and Continuous Improvement
Complex multi-agent ecosystems introduce new vulnerabilities, from unpredictable agent behavior to governance gaps and expanded attack surfaces. Phased rollouts in isolated environments, canary deployments and sandbox testing validate interoperability and resilience under realistic conditions. Red teaming exercises target inter-agent logic, while automated drift detection and retraining pipelines preserve model accuracy. Centralized audit repositories and structured after-action reviews capture both agent logs and human decision records, informing iterative policy updates and architectural optimizations.
Regulatory Compliance and Ethical Accountability
Mapping agent data processes to regulatory data lifecycles—GDPR, CCPA, HIPAA and industry-specific mandates—identifies governance gaps and informs audit logging requirements. Immutable ledger technologies bolster evidentiary integrity for incident investigations. Privacy-preserving techniques such as federated learning, differential privacy and tokenization limit exposure of sensitive data. Ethical review boards scrutinize agent design changes and data collection expansions, reinforcing transparency and user trust.
Cultural Alignment and Final Reflections
Building sustainable multi-agent ecosystems is as much a cultural endeavor as a technical one. Leadership must champion cross-disciplinary collaboration, recognize contributions from both human analysts and AI agents, and communicate transparently about the capabilities and limitations of autonomous defenders. By institutionalizing feedback loops, performance metrics and governance reviews, organizations can evolve their agent architectures in lockstep with emerging threats, regulatory shifts and business imperatives—ensuring adaptive, accountable and resilient security operations over the long term.
Chapter 7: Industry Case Studies
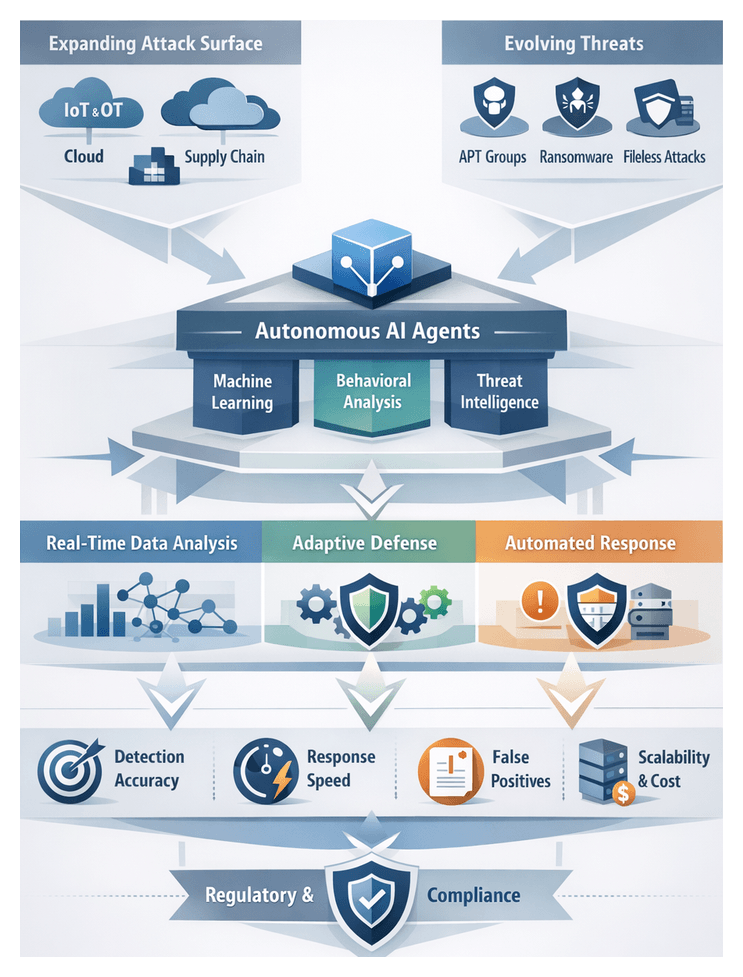
Security Landscape and Emerging Threats
As organizations enter 2026, they confront a security environment that is more complex and dynamic than ever before. The proliferation of connected devices, cloud services, and integration of operational technology with information technology have expanded the attack surface. Hybrid work models and global supply chains introduce additional intrusion vectors. Against this backdrop, traditional defenses based on static signatures and predefined rules are increasingly inadequate, prompting a shift toward adaptive, intelligent architectures driven by autonomous AI agents.
Digital transformation has dissolved network perimeters through cloud migration, software-defined networking, and edge computing, while the Internet of Things and Industrial Internet of Things devices increasingly power manufacturing, energy management, logistics, and smart buildings. These devices often lack robust security controls, making them attractive to attackers. Supply-chain dependencies further magnify risk as third-party software and services introduce vulnerabilities beyond the visibility of security operations centers.
Threat actors—from nation-state sponsored advanced persistent threats to opportunistic cybercriminal syndicates—employ sophisticated tactics to evade detection and escalate impact. Fileless malware resides purely in memory, polymorphic code alters signatures to thwart scanners, and living-off-the-land techniques abuse legitimate system tools for reconnaissance and lateral movement. Ransomware-as-a-service models with double extortion threaten both data confidentiality and reputations.
The exponential growth in telemetry—from network flows to endpoint logs and user behavior analytics—offers rich context for defense but also overwhelms human operators. Manual correlation of thousands of alerts per hour leads to fatigue, raising the risk of missed threats. Regulatory obligations compound pressure on incident response teams to detect, contain, investigate, and report breaches within strict timelines.
These converging trends demand solutions capable of ingesting and analyzing massive data streams in real time, learning evolving adversary behaviors, and orchestrating responses across cyber and physical domains. Autonomous AI agents fulfill this need by leveraging machine learning, graph analytics, and behavioral modeling to detect subtle anomalies, predict emerging threats, and execute countermeasures without human latency.
Evaluating AI-Driven Detection: Performance Metrics
Organizations assess autonomous AI agents using detection accuracy, response time, false positive rates, resource utilization, and cost efficiency. Industry priorities shape these metrics and analytical frameworks.
Detection Accuracy and Precision
Detection accuracy balances recall—the proportion of actual threats identified—and precision—the proportion of alerts corresponding to real incidents. Financial institutions prioritize recall to capture all fraudulent transactions, often reporting rates exceeding 98 percent with platforms such as Darktrace using unsupervised learning to identify anomalous payment flows. Healthcare providers balance recall with high precision to avoid false alarms that disrupt patient care, achieving precision rates above 90 percent in ransomware detection with CrowdStrike Falcon.
Critical infrastructure operators require precision above 95 percent to prevent spurious shutdowns, leveraging Palo Alto Networks Cortex XDR to distinguish legitimate control signals from malicious commands. Retailers adopt F1-score metrics to balance recall and precision, evaluating tools like Microsoft Defender for Endpoint for external threats and internal anomalies. Mean detection accuracy in retail ranges between 92 and 96 percent.
Response Time and Containment
Mean Time to Detect and Mean Time to Respond (MTTR) gauge how quickly agents identify and contain threats. Financial firms target detection within five minutes, achieving average MTTD of 3.8 minutes by correlating transaction telemetry with global fraud feeds. Healthcare systems accept detection windows under ten minutes and MTTR of 30 to 60 minutes, with some networks reducing MTTR from 120 minutes to 45 minutes through automated network segmentation and forensic data collection policies.
In critical infrastructure, reported MTTD values hover around two minutes with MTTR targets under 15 minutes, integrating directly with industrial control systems to trigger fail-safe procedures. Retailers average 12-minute MTTD and 75-minute MTTR, using Service Level Agreements to track containment percentages across omni-channel environments.
False Positives and Signal-to-Noise
False positive rates impact operational viability. Financial services target rates below one percent to avoid triggering compliance investigations, employing continuous model tuning. Healthcare accepts up to three percent, mitigating alert fatigue through prioritized queues and contextual metadata such as patient location and device type. Critical infrastructure enforces rates below 0.5 percent with multi-stage validation against control logic. Retailers tolerate rates up to four percent if the signal-to-noise ratio—true positives divided by total alerts—remains above defined thresholds.
Resource Utilization and Scalability
Scalable agent deployments demand efficient resource usage across diverse environments. Finance benchmarks aim for CPU and memory overhead under two percent per host, with some solutions processing hundreds of concurrent streams using less than 200 MB of memory. Healthcare offloads processing from legacy medical devices to analytics clusters, handling over 50,000 events per second. Industrial edge agents prioritize sub-millisecond inference latency and low power consumption. Retailers simulate peak volumes, such as Black Friday transactions, to ensure cloud-based analytics maintain performance under seasonal loads.
Cost Efficiency and ROI
Cost analyses integrate licensing, infrastructure, and staffing against incident impact reduction. Financial institutions report savings of hundreds of dollars per blocked fraudulent transaction when leveraging agent-driven detection. Healthcare networks measure avoided device downtime and patient notification costs, achieving seven-figure annual savings. Infrastructure providers justify multimillion-dollar investments by preventing unplanned power outages, while retailers factor prevented fraud losses and improved conversion rates into ROI models.
Cross-Sector Benchmarking
Benchmarking requires normalizing incident rates and operational impact across industries. Incident rate reflects frequency of events per device or transaction; operational impact measures business cost per incident. Plotting detection accuracy, MTTD, and false positive rates against these dimensions yields a vulnerability-performance matrix, guiding platform selection based on specific risk-impact profiles.
Operational Impact and Scalability
Deploying autonomous AI agents transforms security operations by accelerating detection and response, reallocating resources, and enhancing organizational agility. Agents such as CrowdStrike Falcon OverWatch and Darktrace ingest and analyze telemetry at machine speeds, enabling threat identification five times faster than legacy signature-based systems. This speed reduces Mean Time to Detect and Mean Time to Respond from hours to minutes, a force multiplier in environments where seconds equate to significant financial or safety risks.
Automating low-value triage tasks liberates security analysts to pursue complex investigations and proactive threat hunting. A leading healthcare provider documented a 30 percent reduction in routine log review workload after integrating Cortex XDR, allowing focus on compliance audits and strategic planning. Experts recommend a balanced scorecard approach to measure agent impact, tracking detection coverage, alert triage time, and containment efficiency alongside deployment costs.
Architecting for Scale
Enterprise-scale deployments require architectures that grow horizontally without bottlenecks. Cloud-native services like Azure Sentinel offer serverless ingestion and elastic compute, while hybrid models deploy edge agents for initial filtering and centralized engines for correlation. Global organizations partition agent fleets by geography to comply with data residency requirements, sharing synthesized threat indicators rather than raw logs in federated models.
Integration with Security Orchestration, Automation, and Response platforms such as Splunk Phantom and Microsoft Sentinel enables automated workflows spanning endpoint isolation, vulnerability scanning, and notifications. Modular AI agent frameworks simplify incremental rollouts, minimizing custom scripting and reducing maintenance overhead.
Resilience and High Availability
Scalability must coexist with operational resilience. Multi-zone deployments and automated failover mechanisms mitigate single points of failure, while synthetic transactions and heartbeat monitoring ensure agent health. These technical safeguards align with Recovery Time Objectives and Recovery Point Objectives in business continuity plans.
In regulated sectors such as healthcare and energy, AI agents contribute to compliance by producing detailed audit trails of decision contexts and data provenance, supporting frameworks like HIPAA and NERC CIP. Industrial control system environments impose constraints on processing power and network latency; lightweight inference models optimized for resource-constrained devices ensure uninterrupted operations.
Organizational Change and Roadmaps
Scaling AI agent deployments demands new operating models. Security teams evolve from log analysts to observability stewards, necessitating training and change management to build trust in AI-driven insights. Leadership frameworks such as the NIST Cybersecurity Framework can incorporate AI agent governance, defining responsibilities for model validation, threshold tuning, and incident escalation.
Strategic roadmaps for agent expansion begin with high-value assets and threat-exposed environments, then extend coverage to cloud workloads, managed service provider ecosystems, and third-party integrations. Continuous review points ensure alignment with evolving threats and business objectives, balancing rapid capability growth with measured risk management.
Adoption Frameworks and Lessons Learned
Cross-industry deployments reveal strategic themes that guide successful adoption of autonomous AI agents. Aligning agent capabilities with business risk objectives, maturing data ecosystems, establishing governance, and planning for continuous evolution are critical success factors.
Key Strategic Insights
- Align with Business Risk Objectives: Mapping agent deployments to existing risk registers accelerates leadership buy-in. Financial firms position agents as part of third-line defense in credit risk monitoring, quantifying expected reductions in dwell time and fraud losses avoided.
- Prioritize Data and Integration Maturity: Healthcare organizations with standardized telemetry pipelines and consolidated data warehouses achieve faster tuning and onboarding. Modular architectures that support incremental data source integration mitigate delays and reduce integration risk.
- Emphasize Continuous Learning: Retailers embed feedback loops from confirmed fraud and operational events to refine model thresholds dynamically. Regular model retraining cycles ensure agents adapt to shifting baselines and new adversary tactics.
- Facilitate Cross-Functional Collaboration: Engaging legal, compliance, OT, and business units early prevents governance bottlenecks. Cross-functional steering committees balance threat containment with operational continuity requirements.
- Leverage Hybrid Human-AI Workflows: Combining human oversight with agent suggestions optimizes investigation times. Platforms like Darktrace demonstrate that coupling AI-driven insights with human expertise reduces investigation duration by up to 40 percent.
Operational and Governance Considerations
- Governance and Accountability: Define roles such as “Security Agent Owner” for model governance, performance reviews, and change approvals.
- Skill Development: Invest in analyst training on anomaly scores, data science fundamentals, and vendor sandbox environments like those provided by CrowdStrike.
- Incident Response Integration: Automate triage and ticketing via SOAR platforms such as Microsoft Sentinel, reducing manual overhead and standardizing procedures.
- Performance Benchmarking: Establish KPIs—MTTD, MTTR, and false positive rates—and benchmark pre- and post-deployment to build an executive narrative.
- Vendor Evaluation: Conduct pilot tests under representative workloads, assessing detection accuracy, model transparency, integration APIs, and total cost of ownership. Solutions like Palo Alto Networks Cortex XDR often emerge as robust choices for extended detection and response.
Analytical Adoption Frameworks
- Technology-Organization-Environment Model: Evaluate data quality, leadership support, skill availability, regulatory mandates, and competitive pressures to identify capability gaps and prioritize investments.
- Maturity Curve Assessments: Define stages from experimentation and proof-of-concept to system-wide integration and optimization, aligning timelines and resources with maturity goals.
Limitations, Risks, and Future Pathways
- Model Drift: Periodic recalibration and automated drift detection prevent thresholds from becoming overly permissive or restrictive.
- Adversarial Manipulation: Validate telemetry integrity and employ data source redundancy to guard against training data poisoning.
- Privacy and Compliance: Implement data anonymization and role-based access controls to comply with GDPR and HIPAA without sacrificing analytical value.
- Cost Overheads: Perform total cost of ownership analyses that include hardware, software, and operational expenses to avoid budget overruns during scale-out.
- Vendor Lock-In: Enforce open API compliance and data export formats to preserve flexibility and portability of analytical investments.
Evolutionary Pathways
- Explainable AI: Adopt interpretable models that provide rationale for anomaly scores and feature contributions, meeting audit and regulatory requirements.
- Multi-Agent Ecosystems: Develop specialized agents for network, endpoint, cloud, and IoT domains coordinated by orchestration layers for dynamic task allocation.
- Continuous Red Teaming: Integrate adversary emulation into training cycles to rapidly incorporate new tactics into detection models.
- Cross-Industry Collaboration: Participate in federated learning consortia to share anomaly patterns and threat indicators without exposing raw data.
Successful adoption of autonomous AI agents hinges on a holistic approach that aligns technology, processes, and governance. By embedding lessons learned into strategic roadmaps and analytical frameworks, organizations can navigate complexities, manage risks, and realize the transformative potential of AI-driven security operations.
Chapter 8: Challenges and Resilience
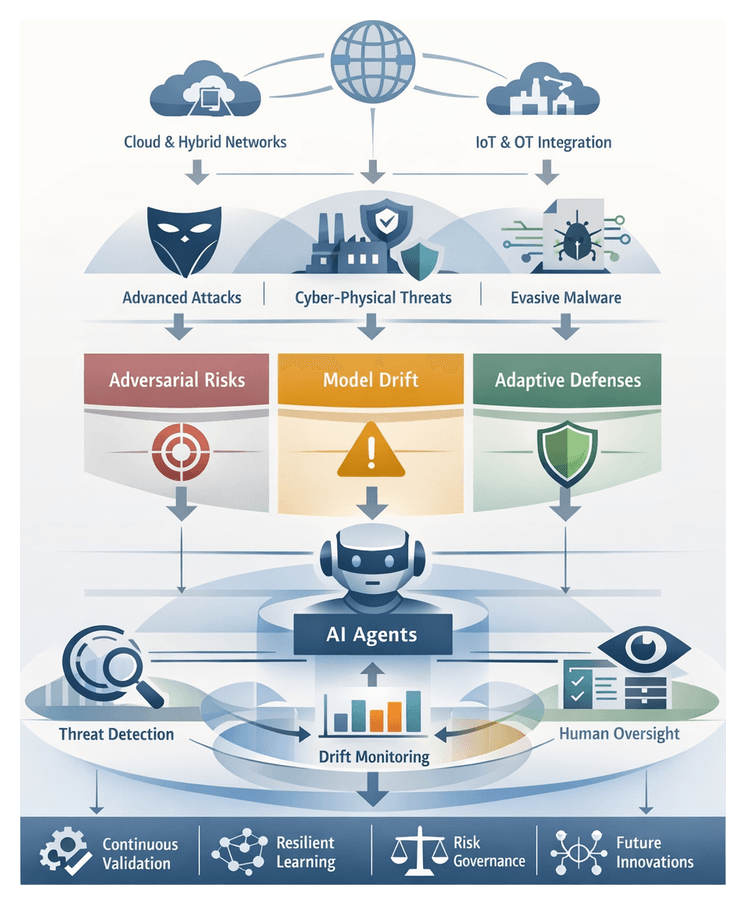
Evolving Threat Landscape in 2026
At the outset of 2026, organizations face a threat environment defined by rapid technological innovation, dispersed perimeters, and sophisticated adversaries. Ubiquitous cloud adoption and hybrid infrastructures have expanded risk surfaces, while the proliferation of Internet of Things devices in manufacturing, healthcare, and smart cities has introduced numerous low-footprint endpoints lacking robust security controls. Remote and hybrid work models have dissolved traditional network boundaries, creating dynamic perimeters that span home offices, co-working hubs, and multi-cloud ecosystems.
Simultaneously, cyber and physical domains are converging. Operational technology systems once isolated by air gaps now integrate with IT networks to enable remote management and predictive maintenance. Attackers exploit this integration to induce physical damage, disrupt utilities, or compromise safety by weaponizing vulnerabilities in programmable logic controllers. Multi-vector campaigns that combine physical infiltration—such as tailgating— with digital footholds amplify dwell time and complicate incident investigations.
Traditional detection methods based on static signatures and predefined rules are overwhelmed by terabytes of daily telemetry, polymorphic malware, fileless techniques, and living-off-the-land tactics. The widening cybersecurity skills gap forces security teams to prioritize triage over proactive threat hunting, while evolving regulations such as the European Cyber Resilience Act and updates to the NIST Cybersecurity Framework demand continuous visibility, rapid reporting, and control validation.
Emerging threat trends underscore the imperative for adaptive defenses. Adversaries employ AI-powered tools to craft highly personalized phishing campaigns, automate vulnerability discovery, and evade anomaly detection through adversarial techniques. They leverage ephemeral serverless compute instances that spin up, execute payloads, and terminate within seconds, leaving scant forensic artifacts. Supply-chain compromises—through code-signing abuses and dependency poisoning—deliver broad impact, while nation-state actors target identity providers and cloud collaboration platforms, magnifying the fallout of a single account compromise.
Addressing these challenges requires integrated security platforms that blend continuous learning with autonomous response. By synthesizing network flows, endpoint logs, identity signals, and threat intelligence in real time, adaptive architectures can detect novel attack patterns, assess risk contextually, and orchestrate remediation at machine speed—delivering the agility and accuracy needed to protect distributed, high-speed digital estates.
Analytical Challenges: Adversarial Risks and Model Drift
Autonomous AI agents tasked with threat detection must navigate adversarial manipulation and model drift—interrelated phenomena that erode detection accuracy and create exploitable blind spots. Addressing these challenges demands rigorous interpretive frameworks, quantitative metrics, and governance disciplines.
Adversarial Risk Taxonomy and Frameworks
Adversarial threats against AI pipelines are categorized according to the stage of attack:
- Evasion Attacks: Subtle perturbations to input features that mislead classifiers without raising alarms.
- Poisoning Attacks: Injection of malicious bias into training data or model updates to degrade generalization.
- Inference Attacks: Techniques such as model inversion or membership inference that extract sensitive training data or internal logic.
Organizations adopt standardized taxonomies to benchmark and compare threat patterns. The MITRE ATLAS knowledge base provides a unified taxonomy for adversarial tactics, while the NIST Adversarial Machine Learning Risk Management Framework offers structured guidance for risk identification, assessment, and mitigation. Security teams map exploit vectors, calibrate risk scores, and prioritize countermeasures based on industry context and threat severity.
Quantitative Robustness and Drift Metrics
Key metrics evaluate model resilience and performance over time:
- Adversarial Perturbation Threshold: The minimal feature alteration required to induce misclassification.
- Attack Success Rate: Proportion of adversarial samples that bypass detection under controlled conditions.
- Certified Radius: Formal guarantee around input-space stability derived from verification techniques.
Automated benchmarking and attack simulation leverage the Adversarial Robustness Toolbox. Model drift is classified as:
- Covariate Drift: Shifts in input feature distributions, such as changes in network traffic patterns or device profiles.
- Concept Drift: Evolution of the relationship between features and labels when adversaries adopt new evasion tactics.
Organizations measure drift through statistical techniques—Kullback-Leibler Divergence, Population Stability Index—and monitor detection performance over rolling intervals. Unsupervised clustering detectors uncover emerging patterns without labels. Solutions like Amazon SageMaker Model Monitor and the Databricks Feature Store automate drift detection, generating alerts and visual diagnostics that inform retraining or recalibration.
Interplay and Governance
Adversarial tactics and model drift reinforce each other: attackers may induce drift by introducing poisoned inputs over time, while natural drift can mask malicious manipulations. Holistic risk models integrate drift priors with adversarial likelihoods to adjust decision thresholds dynamically. Governance structures—regular adversarial red-teaming, automated drift reporting, and risk review boards—apply standardized scoring rubrics (for example, FAIR) to translate analytical insights into operational decisions, ensuring continuous agent integrity.
Future Analytical Directions
Advances in causal inference aim to distinguish benign distributional shifts from adversarial perturbations by modeling feature–outcome causality. Meta-learning approaches offer adaptive drift handling, dynamically reweighting historical data to maintain robustness across evolving environments. Research into certified robustness under distributional uncertainty seeks to provide formal performance guarantees despite combined adversarial and drift pressures.
Sustaining Resilience Through Adaptive AI Agents
Resilience—an agent’s ability to maintain detection accuracy and adapt to novel threats—emerges from interconnected strategies encompassing continuous validation, dynamic adaptation, collaborative architectures, and human-centered governance.
Continuous Self-Assessment and Validation
Resilient agents embed routine validation loops to surface blind spots before production impact:
- Synthetic Scenario Injection: Simulating detection against crafted adversarial patterns.
- Autonomous Red-Teaming: Generative modules produce adversarial inputs to probe model weaknesses.
- Benchmark Drift Analysis: Monitoring rolling performance metrics against reference threat sets to detect drift and integrity issues.
Adaptive Retraining and Calibration
Agents stay aligned with operational data through adaptive learning cycles and fine-tuned thresholds:
- Drift-Triggered Retraining: Automated model refresh when divergence thresholds are exceeded.
- Active Learning Pipelines: Human annotation of low-confidence or novel events for incremental updates.
- Dynamic Threshold Calibration: Statistical process control adjusts anomaly detection boundaries to balance sensitivity and false positives.
- Risk-Weighted Scoring: Mapping detection scores to organizational risk appetite to prioritize high-impact alerts.
Ensembles, Collaboration, and Meta-Learning
Collaborative and meta-learning frameworks diversify detection capabilities and accelerate adaptation:
- Diverse Model Ensembles: Combining statistical, graph-based, and deep learning detectors via weighted voting to mitigate single-model failure modes.
- Federated Learning: Sharing aggregated insights across domains while preserving data privacy.
- Consensus-Driven Alert Fusion: Exchanging metadata among peer agents to refine confidence scores through cross-validation.
- Meta-Learning Initialization: Pre-training on diverse threat corpora to enable rapid fine-tuning with minimal data.
- Online Adaptation Heuristics: Continuous tuning of learning rates and regularization parameters to optimize responsiveness.
Uncertainty Quantification and Human Oversight
Explicit uncertainty estimation guides when to invoke human expertise:
- Bayesian Confidence Estimation: Modeling outputs as probabilistic distributions and flagging low-confidence detections.
- Ensemble Variance Monitoring: Measuring variance across model outputs to identify unstable predictions.
- Information-Theoretic Alerts: Prioritizing events with highest information gain to focus analyst attention.
- Analyst-in-the-Loop Feedback: Incorporating labeled judgments on false positives and negatives into retraining pipelines.
Policy-aware adaptation, detailed audit trails, and executive-level oversight ensure that resilience is sustained across technology, processes, and people.
Risk Mitigation and Future Research
Balancing AI-driven innovation with control requires a comprehensive risk mitigation framework and focused research investments to enhance future agent capabilities.
Risk Mitigation Pillars
- Governance and Accountability: Defining ownership, decision rights, and policy-based controls for autonomous responses and escalation protocols.
- Technical Validation: Continuous adversarial testing and red-teaming against polymorphic malware and multi-vector campaigns, leveraging the MITRE ATT&CK knowledge base for benchmarking resilience.
- Data Assurance and Provenance: Metadata cataloging, automated anomaly detection on input streams, and periodic audits to verify integrity and lineage.
- Human-in-the-Loop Oversight: Configuring thresholds for human review of critical or novel alerts and maintaining clear escalation ladders for rapid triage.
Strategic Trade-Offs
Increased autonomy accelerates response but can amplify false positives without robust validation. Expansive data collection enhances situational awareness but raises privacy and compliance risks. Adversarial hardening improves resilience but introduces latency and computational overhead. Organizations must calibrate these trade-offs according to risk appetite, operational constraints, and strategic goals, supported by regular risk reviews and scenario-based planning.
Future Research Directions
Explainability and Transparency
- Human-readable explanations tracing detection rationale to specific features or data samples.
- Quantified confidence bounds and uncertainty estimates integrated into security workflows.
- Integration of explainable modules with existing security information and event management systems to build trust and accelerate response.
Continual and Federated Learning
- Architectures for incremental learning that incorporate new threat indicators without full retraining.
- Federated learning protocols enabling cross-organization model updates while preserving privacy and compliance.
- Adaptive weighting mechanisms that prioritize fresh, high-quality data over stale inputs.
Adversarially Robust Architectures
- Robust feature embeddings and certified defenses offering formal guarantees against perturbations.
- Generative adversarial network augmentation pipelines simulating complex attack scenarios during training.
- Collaborations with cryptography and formal verification experts to embed provable security properties into detection frameworks.
Quantum-Resilient Detection Strategies
- Quantum-safe encryption and integrity checks for data at rest and in motion.
- Quantum-accelerated algorithms for real-time pattern recognition and anomaly detection.
- Hybrid classical-quantum architectures distributing workloads while maintaining rigorous security postures.
By integrating governance, validation, and human oversight into current deployments while pursuing breakthroughs in explainability, continual learning, adversarial robustness, and quantum resilience, organizations will fortify defenses today and architect the autonomous agents of tomorrow—ensuring enduring adaptability in a perpetually evolving threat landscape.
Chapter 9: Ethical, Privacy, and Regulatory Considerations
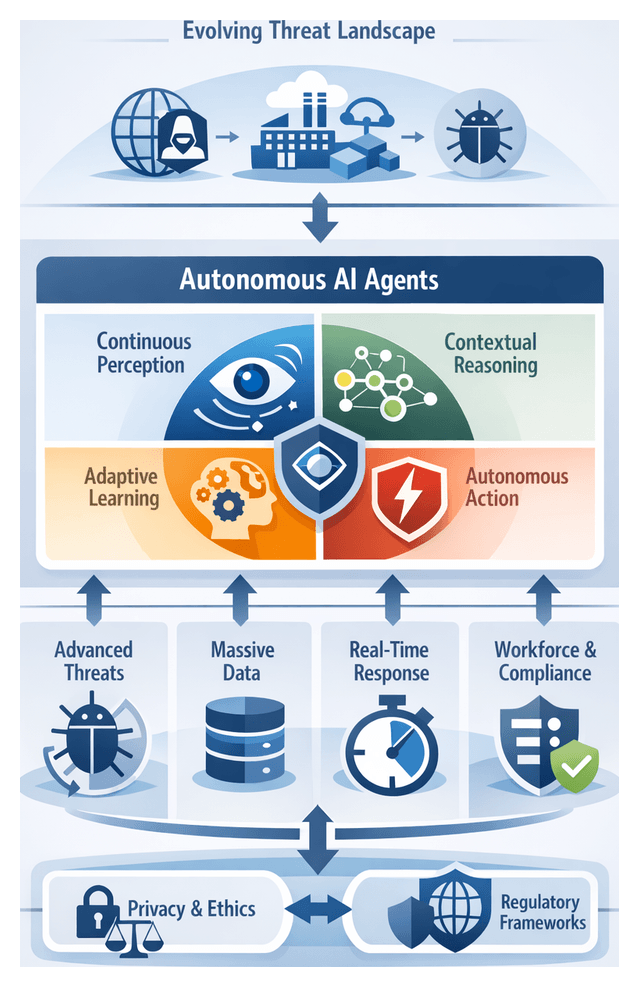
Evolving Threat Landscape and the Rise of Autonomous AI Agents
As organizations enter 2026, the threat environment has reached unprecedented levels of complexity. Traditional cyberattacks have evolved into multifaceted operations that blend digital exploits with physical tactics. Nation-state actors and organized crime syndicates leverage artificial intelligence to orchestrate adaptive malware, coordinate supply chain compromises and manipulate cloud-native environments at scale. Meanwhile, the proliferation of Internet of Things devices, operational technology networks and edge computing infrastructures has expanded the attack surface, creating new vectors for intrusion and disruption.
Threat actors deploy advanced evasion techniques such as fileless attacks, living-off-the-land execution and encrypted command-and-control channels, rendering legacy detection tools ineffective. The rapid adoption of hybrid work models and cloud services has fragmented traditional security perimeters, challenging organizations to maintain visibility over dispersed workloads and remote endpoints. Delays in threat identification translate directly into operational and financial impact: protracted dwell times allow adversaries to extract sensitive intellectual property, disrupt critical infrastructure and carry out ransomware campaigns with higher extortion yields.
This evolving environment demands a security paradigm capable of continuous monitoring, rapid context-aware analysis and automated response. Autonomous AI agents emerge as a dynamic framework that aligns with the speed, scale and sophistication of modern threats. Unlike traditional security tools that rely on fixed rule sets or manual workflows, these agents perceive their environment, reason about potential threats and act upon emergent risks without human intervention.
Conceptual Framework of Autonomous AI Agents
Autonomous AI agents integrate four key attributes to transcend the limitations of legacy architectures:
- Continuous Perception: Ingesting and normalizing data from network telemetry, endpoint logs, cloud APIs and threat intelligence feeds to maintain an up-to-date view of the security landscape.
- Contextual Reasoning: Correlating events across time and domain boundaries through embedded knowledge repositories and inference engines to recognize complex, multi-stage attack patterns.
- Adaptive Learning: Refining detection models via supervised classification, reinforcement training and feedback loops from human analysts to generalize from novel attack variants.
- Autonomous Action: Executing containment procedures—such as isolating endpoints, quarantining workloads or triggering forensics workflows—when predefined risk thresholds are exceeded, while preserving human oversight channels.
This paradigm shifts detection from retrospective analysis to proactive surveillance and mitigates reliance on continuously updated signature databases. A closed-loop design incorporates self-assessment and model calibration, ensuring resilience against evolving adversarial techniques. Through this framework, organizations achieve continuous posture improvements even as threat actors innovate.
Drivers Accelerating AI-Based Threat Detection
Multiple converging forces propel the adoption of AI-driven detection solutions:
- Escalating Attack Sophistication: Advanced persistent threats employ multi-stage intrusion chains, polymorphic malware and zero-day exploits beyond the reach of static defenses.
- Data Volume and Velocity: Enterprise environments generate terabytes of event data daily. Automated analysis is essential to identify subtle correlations within high-throughput streams.
- Real-Time Decision Imperative: Seconds of delay can allow lateral movement and data exfiltration. Automated decision engines deliver immediate containment and forensics triggers.
- Workforce Constraints: A chronic shortage of skilled security professionals drives automation of routine detection and triage tasks, enabling human teams to focus on strategic threat hunting.
- Regulatory and Compliance Pressures: Regulations such as GDPR and evolving AI governance frameworks demand demonstrable security controls, rapid breach notification and evidence of continuous monitoring.
Organizations that embrace autonomous AI agents can achieve transformative increases in threat visibility, operational efficiency and overall resilience.
Privacy Implications in Data-Driven Detection
AI agents collect vast volumes of user behavior, system operations and network transaction data. While deep visibility is instrumental for detecting advanced threats, it raises fundamental questions about privacy and the protection of sensitive information. Behavioral telemetry—such as keystroke timing, application usage statistics and file access sequences—may expose personal habits or proprietary workflows, undermining trust and creating avenues for misuse.
Privacy engineering frameworks guide analytical reasoning around data-driven detection. The NIST Privacy Framework and ISO 27701 offer taxonomies for governance, data management and communications controls. By mapping each stage of data ingestion, storage, processing and disposal to objectives—such as minimization, transparency and accountability—analysts derive structured assessments of potential exposures and mitigation levers.
Global regulations impose strict requirements on handling personal data. Under GDPR, monitoring activities must satisfy principles of lawfulness, fairness and purpose limitation. The California Consumer Privacy Act grants rights over automated decision-making and profiling. In healthcare and finance, HIPAA and GLBA impose additional constraints on protected data. Cross-industry consortia, such as the Cloud Security Alliance, publish best practices reconciling security analytics with privacy mandates.
Data minimization and anonymization techniques are central to privacy-preserving detection. Telemetry streams are often segmented into high-fidelity data for forensic analysis and reduced-fidelity aggregates for real-time anomaly detection. Tokenization, irreversible hashing and noise injection obscure direct associations with individuals while preserving analytical utility. Advanced methods—such as federated learning, homomorphic encryption and secure multi-party computation—show promise for privacy-preserving analytics, though performance and integration challenges remain.
Governance structures should define permissible data uses, retention periods and access controls. Data protection officers and security architects collaborate on impact assessments and audit trails, recording each data access event. Incident response workflows must scope surge data collections narrowly, with predefined escalation criteria and post-incident privacy audits to purge unnecessary data.
Balancing detection accuracy with privacy protection is an optimization challenge. Multi-criteria decision-making frameworks quantify competing objectives—regulatory severity and stakeholder concerns versus threat criticality and impact—enabling defensible collection parameters and documented risk tolerance decisions.
Compliance Contexts Under Global Regulations
Autonomous AI agents operate within a dynamic environment of privacy laws, sector-specific mandates and emerging AI governance frameworks. Mapping agent data flows against major regimes is essential for strategic compliance design:
- General Data Protection Regulation (GDPR): Requires lawful bases, purpose limitation, data minimization and Data Protection Impact Assessments for novel AI monitoring capabilities.
- California Consumer Privacy Act (CCPA) and California Privacy Rights Act (CPRA): Grants rights to opt out of profiling and automated decisions, necessitating disclosures and mechanisms for consumer rights exercise.
- Personal Information Protection Law (PIPL) of China: Governs personal data collection, storage and cross-border transfers with stringent security assessments.
- APEC Privacy Framework and OECD Privacy Principles: Offer harmonized approaches for cross-border cooperation and interpretive guidance across national laws.
Sector-specific frameworks add further constraints:
- Healthcare (HIPAA, GDPR health provisions): Encryption, access controls and audit logs are essential for anomaly detection on PHI and medical device telemetry.
- Financial Services (GLBA, PSD2, MiFID II): Real-time fraud detection requires explainability and record-keeping to satisfy regulators such as the SEC or European Banking Authority.
- Critical Infrastructure (NIS2 Directive): Minimum cybersecurity standards and incident-reporting timelines shape autonomous detection systems in energy, transportation and utilities.
- Retail and E-commerce (PCI DSS): Threat detection workflows must avoid exposing payment data or violating consumer protection laws governing profiling and marketing.
Organizations adopt interpretive frameworks for compliance by design, including risk-based models that prioritize controls according to potential harm, Privacy and Ethics by Design principles that integrate Privacy Enhancing Technologies from inception, and compliance maturity frameworks aligned to ISO/IEC 27001 and 27701 standards.
Cross-border data flows introduce complexities when laws conflict. Standard Contractual Clauses, regionalized deployments and policy-driven data controls help mitigate transfer restrictions and residency requirements. Transparent governance committees review agent risk assessments, data usage policies and model updates, while comprehensive audit trails and third-party certifications—such as SOC 2 reports—reinforce accountability.
Vendors such as Darktrace and Microsoft Azure Sentinel are evaluated for compliance certifications, data processing agreements and regional data residency capabilities. Continuous monitoring of regulatory changes and automated compliance tools support alignment of agent behavior with evolving mandates.
Ethical Responsibility and Governance
Ethical deployment of autonomous AI agents requires clear accountability frameworks, bias mitigation strategies and privacy-preserving design. When decision-making shifts from human analysts to algorithms, organizations must trace outcomes to human-defined policies and parameter settings. Frameworks such as value-sensitive design and IEEE’s Ethically Aligned Design guide the integration of fairness audits, adversarial testing and continuous monitoring throughout model development.
Robust governance structures embed cross-functional oversight bodies—comprising legal, compliance, ethics and technical experts—to review sensitive use cases, access controls and incident response protocols. Model governance platforms and knowledge repositories ensure documentation, version control and audit trails remain accessible for internal and external scrutiny. Explainable AI techniques balance the need for interpretability with operational performance, supporting human-readable rationales for threat determinations.
Technical resilience depends on continuous adversarial testing, red-teaming exercises and model retraining cycles to address evolving attack methods. Capacity building—through ethical AI training for analysts, data protection workshops for developers and regulatory briefings for leadership—cultivates organizational expertise in navigating complex trade-offs. Metrics for ethical performance, such as bias incident rates and mean time to compliance remediation, enable continuous improvement and benchmarking against industry consortia.
Key Considerations for Responsible Deployment
- Accountability Frameworks: Define governance structures and roles for decision ownership in autonomous systems.
- Bias Mitigation: Incorporate fairness audits, adversarial testing and continuous monitoring to detect and correct algorithmic bias.
- Privacy by Design: Embed data minimization, pseudonymization and Data Protection Impact Assessments into every stage of development.
- Regulatory Alignment: Adopt risk-based compliance programs that track GDPR, CCPA and emerging AI governance requirements across jurisdictions.
- Explainability Measures: Use interpretable algorithms and post-hoc explanation tools to balance transparency with performance.
- Adaptive Governance: Establish cross-functional ethics committees, audit trails and version control to support iterative updates and incident response.
- Technical Resilience: Conduct adversarial and red-teaming exercises regularly to assess vulnerabilities and drive model retraining.
- Continuous Learning: Implement feedback loops from human reviewers, stakeholders and external auditors to refine policies and enhance trust.
- Liability Management: Negotiate clear contractual terms with vendors and partners to delineate responsibilities for data stewardship and system failures.
- Capacity Building: Invest in training programs and knowledge repositories to cultivate expertise in ethical, privacy and regulatory domains.
Chapter 10: Future Directions and Innovations
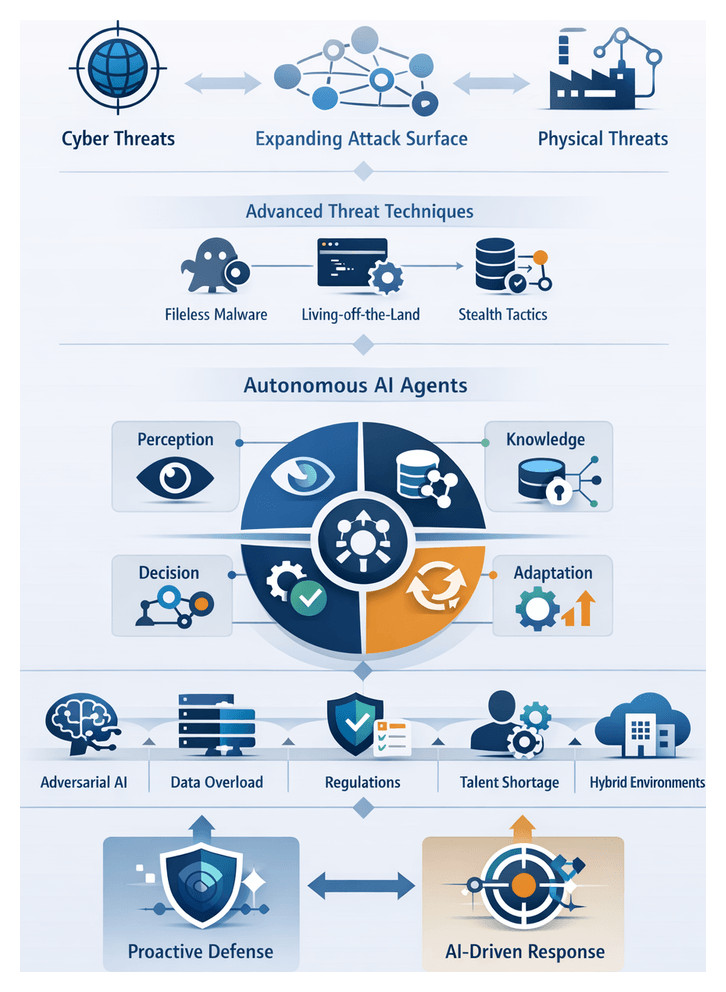
Evolving Threat Landscape in 2026
As organizations confront 2026, the distinction between cyber and physical realms has effectively dissolved. Industrial control systems, operational technology networks and critical infrastructure facilities face sophisticated, multi-vector campaigns orchestrated by nation-state actors and criminal syndicates alike. These adversaries leverage machine learning for automated reconnaissance, vulnerability discovery and real-time evasion. At the same time, the proliferation of Internet of Things devices—from medical equipment to smart grid sensors—has exponentially expanded the attack surface. Many of these endpoints lack robust security controls, enabling threat actors to pivot into more sensitive environments undetected.
Attack methodologies have matured to include fileless malware, living-off-the-land tactics and encrypted command-and-control channels as standard techniques for stealth and persistence. Static defenses based on signature detection or manually managed playbooks struggle to keep pace. Threat actors regularly dwell undetected for extended periods, extracting value before raising alarms. Simultaneously, legitimate enterprise transformations—cloud migrations, DevSecOps pipelines and distributed workforces—generate high-velocity telemetry that obscures malicious behavior, overwhelming traditional security operations centers.
The imperative is clear: reactive, siloed tools and human-centric workflows cannot match the pace of change. Security architectures must become adaptive, continuously anticipating emerging threats and autonomously responding to contain campaigns in progress. This evolution sets the stage for the adoption of autonomous AI agents as foundational components of next-generation defense.
Autonomous AI Agents: Conceptual Framework
Autonomous AI agents represent a shift from rule-based security tools to unified systems that combine real-time data ingestion, adaptive learning and autonomous decision-making. Four core attributes define their capabilities:
- Perception: continuous analysis of multi-modal data streams—network packets, endpoint logs, user behavior analytics and threat intelligence feeds.
- Knowledge: dynamic repositories synthesizing historical context and evolving adversary patterns, enabling reference to prior incidents and known Tactics, Techniques and Procedures.
- Decision: algorithmic engines that detect anomalies, estimate risk and determine optimal actions aligned with organizational objectives.
- Adaptation: feedback loops that refine detection models, update response playbooks and integrate new intelligence without manual intervention.
By linking these components, AI agents can identify subtle indicators of compromise, correlate events across disparate sources and execute containment or remediation steps with minimal human input. Unlike signature-based systems, they shift security operations from reactive to proactive, self-tuning platforms that continuously improve detection accuracy and reduce dwell time.
For example, when a zero-day exploit targets a web application, a traditional solution may await a signature update, delaying detection by days or weeks. An autonomous agent leveraging unsupervised anomaly detection can perceive deviations in request patterns and abnormal memory behavior within minutes. It then quarantines the affected server, alerts operators with contextualized evidence and updates its models to recognize similar exploits in the future.
Drivers and Imperatives for AI-Based Detection
Multiple factors converge to make AI-driven detection a strategic priority:
- Adversarial Automation: Attackers use machine learning to automate reconnaissance and social engineering at scale, creating an asymmetry that overwhelms manual defenses.
- Exponential Data Growth: Enterprises generate terabytes of logs, packet captures and cloud audit trails daily, exceeding human capacity for real-time analysis.
- Regulatory Mandates: Frameworks such as NIST SP 800-171 and ISO 27001 impose strict monitoring and breach notification requirements, driving the need for continuous, automated oversight.
- Talent Shortages: The global deficit of skilled security professionals necessitates augmentation. Autonomous agents handle routine detection and triage, escalating only high-risk cases for human review.
- Hybrid Environments: Cloud-native infrastructures and edge deployments demand distributed security that maintains consistent visibility and response capabilities across on-premises, public cloud and remote contexts.
These drivers underscore the urgency for organizations to adopt AI-driven platforms that scale detection, reduce fatigue among analysts and accelerate incident response.
From Reactive to Proactive Threat Hunting
Traditional threat hunting centered on post-compromise analysis and signature alerts. Autonomous threat hunting, by contrast, continuously scans data streams to identify emerging patterns and predict adversary behavior before breaches materialize. Two dimensions characterize this shift:
- Temporal Orientation: Transition from retrospective investigation to near-real-time analysis of subtle anomalies.
- Decision Autonomy: Evolving from human-driven triage to AI-powered first-level analysis, where agents escalate only high-confidence findings.
Leading vendors illustrate these models. Darktrace defines autonomous hunting as self-learning anomaly detection that adapts to unique network baselines. CrowdStrike Falcon positions agents as collaborative entities that enrich human workflows with automated data correlation and risk scoring.
Benchmarking Maturity and Measuring Success
Organizations often adopt maturity models and performance indicators to guide their autonomous hunting programs. A typical maturity framework includes:
- Level 1 — Manual Baseline: Hunting relies on static playbooks and manual queries.
- Level 2 — Assisted Analysis: Machine learning supports search queries and pattern prioritization.
- Level 3 — Autonomous Detection: Agents surface anomalies and propose leads independently.
- Level 4 — Predictive Forewarning: Agents anticipate adversary TTPs and recommend pre-emptive measures.
Key Performance Indicators for assessing effectiveness include:
- Mean Time to Detect (MTTD): The average interval from threat emergence to detection.
- Mean Time to Respond (MTTR): Time from detection to containment or remediation.
- Signal-to-Noise Ratio: Ratio of validated threats to total alerts, reflecting precision.
- Productivity Index: Measure of analyst time saved and high-confidence leads generated daily.
- Predictive Accuracy Score: Percentage of alerts that successfully preempt actual incidents.
Embedding these metrics in executive dashboards enables continuous improvement, with SOCs adjusting agent configurations and data integrations to optimize outcomes.
Integration into Security Operations Ecosystems
Autonomous agents must interface seamlessly with existing platforms—SOAR, SIEM and orchestration tools—to deliver unified alert management and investigation workflows. Integration frameworks include:
- Platform Convergence Lens: Treat autonomous hunting as a service within a broader ecosystem to ensure consistent alert triage.
- Human-Centered Workflow Lens: Position AI agents as co-workers that hand off prioritized leads to analysts, preserving human judgment.
- Threat Intelligence Fusion Lens: Enrich detection models with external feeds—such as Recorded Future—to refine predictive capabilities.
This interoperability relies on standardized data schemas and open interfaces, preventing operational silos and maximizing strategic impact.
Regulatory, Talent and Business Resilience Drivers
Regulatory regimes—GDPR, CCPA, NYDFS and sector-specific mandates like NERC CIP—require continuous monitoring, rapid breach notification and demonstrable control effectiveness. Autonomous agents generate standardized audit logs documenting detection decisions, model versions and response actions, supporting compliance and governance reviews.
Talent shortages in cybersecurity drive organizations to adopt AI-driven augmentation. Tools such as Microsoft Defender for Endpoint embed behavior-based detection that collaborates with human operators through clear risk summaries and recommended actions. Feedback loops, where analysts label ambiguous events and validate false positives, refine model accuracy over time and allow teams to focus on strategic threat hunting.
From a business continuity perspective, autonomous detection agents serve as force multipliers that enhance resilience. They feed structured intelligence into incident response playbooks and crisis management frameworks, enabling scenario simulations and stress tests. By anticipating and neutralizing threats before they escalate, organizations preserve operational uptime and maintain stakeholder trust.
Strategic Deployment and Governance of Next-Generation Defenses
Next-generation defenses require alignment with business objectives, risk tolerance and organizational culture. Key considerations include:
- Risk-Driven Prioritization: Map threat scenarios to critical business functions, assess control effectiveness and perform gap analysis to identify where AI agents deliver greatest value.
- Governance Guardrails: Define decision boundaries for automated responses, establish data retention and privacy controls, and maintain audit trails for agent-driven events.
- Performance Metrics: Augment MTTD and MTTR with adaptive detection rate, false positive suppression ratio and operational efficiency gain to validate strategic impact.
- Open Integration: Ensure agents ingest telemetry from on-premises, cloud and third-party systems and share insights via unified platforms, guided by frameworks such as MITRE ATT&CK.
- Skills and Culture: Cultivate data-driven decision-making, train teams in AI validation and threat intelligence synthesis, and foster cross-functional collaboration through tabletop exercises and governance forums.
- Vendor Selection: Evaluate research leadership, enterprise-scale deployments, interoperability and model governance features. Leverage open-source components to balance innovation and cost control.
Strategic planners must also recognize limitations—dependence on high-quality data, adversarial model poisoning, overreliance on automation and privacy constraints—and implement mitigations such as regular red teaming and human-in-the-loop workflows.
Phased Adoption and Continuous Evolution
Rather than rip-and-replace, a phased adoption approach mitigates risk. Begin with pilot programs focused on narrowly defined use cases—insider threat detection or lateral movement analysis—where success criteria are clear. Use lessons learned to refine configuration standards, operational playbooks and governance policies.
A strategic roadmap for leaders may include:
- Establish a cross-functional steering committee to align AI initiatives with business and compliance requirements.
- Conduct a capability gap analysis using a threat-centric framework to prioritize agent use cases.
- Select vendors and open-source projects based on research credentials, interoperability and governance features.
- Launch pilots with executive sponsorship and clear success metrics.
- Scale iteratively, integrating lessons into policy, training and architecture standards.
- Implement continuous monitoring of agent performance, adversarial trends and regulatory changes to guide future enhancements.
Through a holistic approach that integrates strategic prioritization, robust governance, seamless integration and a culture of continuous learning, organizations can harness autonomous AI agents as force multipliers. This enables enhanced detection of sophisticated threats, accelerated response times and optimized security operations, ensuring resilience in an era of unprecedented threat complexity.
Conclusion
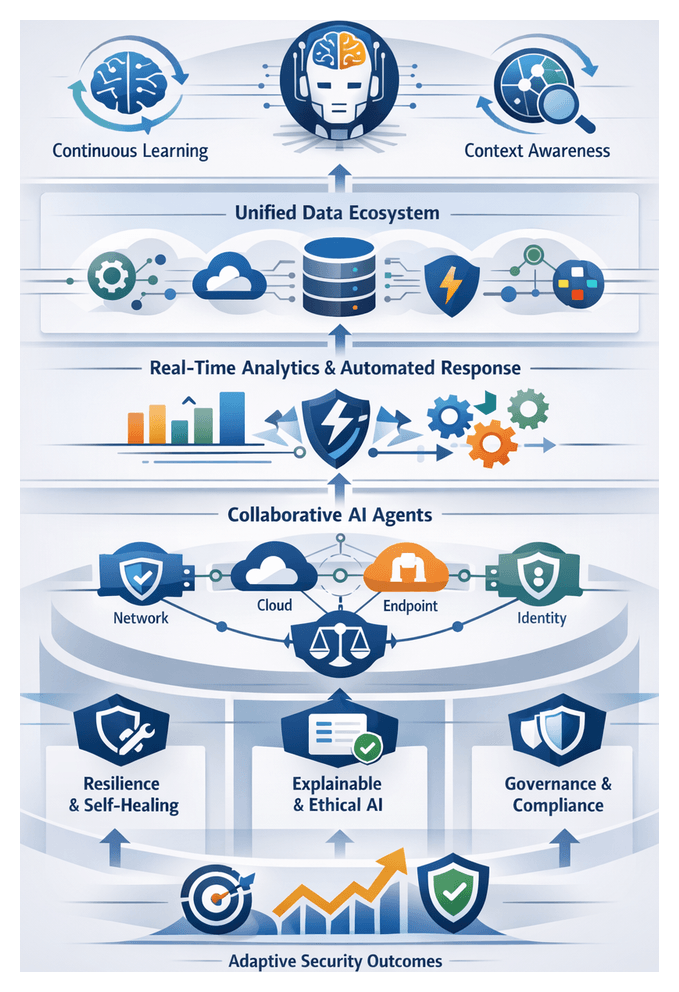
Key Principles of Autonomous AI-Driven Threat Detection
Organizations confronting sophisticated adversaries have moved from static, signature-based defenses to proactive, autonomous AI agents capable of continuous, context-aware monitoring and decision making. Embedding learning, perception, and response into modular agents delivers the agility and scalability required to neutralize advanced threats in real time. The foundational principles guiding these intelligent defenders include:
- Continuous Learning and Adaptation: Autonomous agents rely on supervised, unsupervised, reinforcement, and transfer learning to evolve with each new data input and feedback loop. Automated retraining pipelines and drift detection algorithms minimize vulnerability windows and free security teams from routine rule writing.
- Contextual Awareness: Perception modules fuse network telemetry, endpoint logs, cloud service events, and user behavior analytics into multi-dimensional representations. Correlating diverse inputs reduces false positives and aligns responses with business priorities.
- Unified Data Ecosystem: Data normalization pipelines clean, standardize, and enrich heterogeneous sources. Feature engineering extracts attributes such as traffic entropy and user-risk scores, enabling high-fidelity pattern recognition and seamless integration with SIEM and TIP platforms.
- Real-Time Analytics and Automated Response: Streaming architectures process high-velocity data with minimal latency. Decision engines evaluate anomalies against policy criteria, triggering automated playbooks that quarantine endpoints, block network segments, or isolate accounts without waiting for human approval.
- Scalable Multi-Agent Collaboration: Specialized agents for network, endpoint, cloud, and identity domains communicate securely, sharing threat indicators and contextual insights. Hierarchical orchestration layers assign tasks based on capability, enabling horizontal scaling as data volumes grow.
- Resilience and Self-Healing: Self-assessment routines monitor model performance and system health. Adversarial training, redundancy, and fallback strategies ensure protection persists despite tampering attempts or agent failures.
- Explainability and Transparency: Explainable AI techniques—feature attribution, decision trees, and local interpretable model-agnostic explanations—provide human-readable rationales. Transparent reporting dashboards translate complex reasoning into summaries that analysts can validate and auditors can review.
- Ethical Design and Regulatory Alignment: Privacy-enhancing methods such as anonymization, differential privacy, and federated learning limit collection of personally identifiable information. Governance frameworks codify usage policies and audit logs, ensuring compliance with GDPR, CCPA, and industry mandates.
Cross-Chapter Themes and Strategic Patterns
Across industry analyses and practitioner frameworks, several recurring themes shape how autonomous AI agents are conceptualized and evaluated. Recognizing these patterns helps security leaders make holistic investment decisions and anticipate future challenges.
- Data Ecosystem as Competitive Advantage: Breadth, quality, and contextual richness of data inputs drive detection fidelity. Organizations prioritize platforms that ingest heterogeneous streams, normalize formats, and enrich context over standalone algorithmic sophistication.
- Perpetual Learning Loops: The shift from static rule sets to continuous learning is viewed as a redefinition of security operations. Solutions are assessed on retraining frequency, online adaptation capabilities, and drift monitoring mechanisms.
- Hybrid Architectures and Autonomy Continuum: Multi-agent networks and human-AI teaming form hybrid architectures where agents range from passive monitors to fully autonomous responders. Governance controls map agent roles to risk tolerance and compliance requirements.
- Decision Velocity and Risk Calibration: Tuning detection thresholds involves balancing time to detection with false positive tolerance. Risk calibration matrices cross-reference detection latency with potential business impact to guide threshold settings.
- Governance, Ethics, and Accountability: Cross-functional committees evaluate agent behaviors against privacy, fairness, and security criteria. Ethical risk indicators include bias potential, data retention policies, and decision transparency.
- Resilience through Adaptive Countermeasures: Adversarial robustness is tested through simulated attacks. Automated self-healing and data integrity controls maintain model efficacy despite evasion or poisoning attempts.
- Explainability as a Trust Catalyst: Decision justifications, feature importance reporting, and audit trails are essential for enterprise adoption, incident response, compliance, and cross-team collaboration.
- Ecosystem Integration and Interoperability: Compatibility with existing tools, open APIs, and support for standards like STIX and TAXII are key evaluation axes. Reference architectures map agent interfaces to appliances, protection platforms, and orchestration engines.
- Security-Business Alignment: Value-at-risk analyses tie detection investments to potential breach costs. Models such as FAIR guide cross-functional dialogues and board-level reporting.
- Continuous Evolution and Future Velocity: Vendors are scored on their capacity for rapid iteration, open-source contributions, and ecosystem partnerships, reflecting the necessity of perpetual innovation.
Industry Impact and Strategic Opportunities
The maturation of autonomous AI agents is reshaping risk management, operational effectiveness, and strategic planning across sectors. Security teams are transitioning from defensive support functions to proactive partners driving measurable business value.
- Elevating Security Posture and Maturity: By integrating agents with frameworks such as the NIST Cybersecurity Framework and MITRE ATT&CK, organizations quantify improvements in threat visibility, mean time to detect, and MTTR. Extended maturity models now include agent confidence scores and ratios of automated to manual interventions.
- New Business Models and Differentiation: Security-as-a-service offerings, managed detection and response lines, and internal AI-driven monitoring services are emerging. Platforms like Darktrace and CrowdStrike Falcon enable accelerated market entry, stronger procurement positioning, and customer assurances around continuous monitoring.
- Sector-Specific Adoption Patterns: Finance emphasizes real-time fraud detection and regulatory reporting. Healthcare focuses on HIPAA compliance and anomalous access to records. Critical infrastructure blends cyber and operational technology protocols, while retail leverages omnichannel analytics for payment fraud mitigation.
- Data-Driven Strategic Decision Making: Rich metadata and predictive risk assessments inform capital planning and investment in initiatives such as 5G rollouts and hybrid cloud migrations. Integration of AI agent metrics into the Risk Management Framework fosters dynamic governance and near-real-time risk visibility.
- Collaborative Ecosystem Engagement: ISACs and threat intelligence platforms absorb agent-generated telemetry, enabling collective defense. Vendor partner networks co-develop modules for supply-chain risk and industrial control systems, standardizing threat schemas and reducing integration friction.
- Future-Focused Roadmap Alignment: Budgets now account for continuous model refinement, explainable AI pilots, and quantum-resistant detection research. Cross-functional governance bodies align agent capabilities with privacy commitments and ethical imperatives.
Leadership Considerations and Governance
Effective deployment and oversight of AI-driven threat detection ecosystems require a balanced approach that aligns technology with business objectives, ethical standards, and operational realities.
- Strategic Integration with Business Goals: Translate agent performance metrics into business-relevant KPIs and embed detection capabilities within enterprise risk management frameworks.
- Data Governance and Quality Assurance: Implement rigorous metadata cataloging, pipeline validation, and normalization to safeguard data lineage and support continuous model improvement.
- Human-AI Synergy: Define autonomy boundaries, escalation pathways, and audit controls. Provide analysts with interpretive dashboards showing confidence scores and rationale for agent recommendations.
- Cross-Domain Collaboration: Enable secure agent-to-agent communication across IT, OT, cloud, and third-party environments to maximize situational awareness and streamline incident response.
- Ethical and Privacy Stewardship: Adopt bias mitigation, data minimization, and explainability by design. Engage legal, compliance, and ethics teams to maintain stakeholder trust and regulatory compliance.
- Investment in Emerging Technologies: Allocate resources to pilot quantum-safe algorithms, self-healing network fabrics, and advanced explainable AI frameworks in partnership with academia and consortiums.
- Hybrid Cloud and Edge Orchestration: Prioritize platforms that support dynamic workload profiling, edge-optimized inference, and seamless telemetry routing from remote devices.
Limitations and Operational Challenges
While autonomous AI agents offer transformative capabilities, leaders must address inherent risks and constraints that can impede long-term success.
- Adversarial Vulnerabilities: Models can be evaded or poisoned without adversarial testing, input sanitization, and defensive distillation. Regular red-teaming and continuous validation are essential.
- Data Integration Gaps: Legacy systems, inconsistent telemetry, and undocumented schemas introduce blind spots that elevate false negatives.
- Alert Fatigue: Excessive alarms from overly sensitive thresholds can overwhelm analysts. Calibration frameworks and tiered playbooks are required to prioritize high-impact incidents.
- Talent and Skill Shortages: Expertise in data science, ML engineering, and threat intelligence is scarce. Bridging gaps through training, partnerships, and managed services accelerates capability building.
- Regulatory Complexity: Fragmented requirements under GDPR, CCPA, and AI governance rules necessitate embedded compliance checks throughout data and model lifecycles.
- Resource and Cost Constraints: Compute, storage, and continuous monitoring costs must be budgeted carefully. Leveraging cloud elasticity and optimizing model complexity help balance performance and cost.
- Vendor Lock-In Risks: Proprietary platforms can limit flexibility. Prioritize open standards, APIs, and modular architectures to avoid lock-in and enable best-of-breed integration.
Future Outlook and Emerging Frameworks
Anticipating the next frontier of AI-driven security requires forward-looking strategies that blend innovation with governance.
- Explainability-Centric Architectures: Integrate interpretability frameworks and visualization layers to satisfy regulatory demands and accelerate incident investigations.
- Predictive Threat Hunting: Combine real-time analytics with behavior forecasting and social graph analysis to shift from containment to preemption.
- Quantum-Resilient Security Fabrics: Pilot post-quantum encryption, key exchange protocols, and cryptographic agility to prepare for future decryption threats.
- Self-Healing Network Infrastructures: Define policy-driven orchestration that empowers agents to isolate anomalies, quarantine segments, and reconfigure network paths automatically.
- Multi-Stakeholder Collaboration Ecosystems: Champion open standards for agent interoperability and data sharing, enabling public-private partnerships and communal intelligence repositories.
- Augmented Human-AI Decision Platforms: Develop interactive hubs presenting ranked hypotheses, risk scores, and confidence intervals to refine agent performance through continuous human feedback.
- Edge-Native Detection Models: Leverage federated learning, model compression, and on-device analytics to extend threat detection to IoT and remote environments with minimal latency.
By harmonizing advanced research with disciplined governance, security leaders can transform reactive defenses into intelligence-driven, adaptive ecosystems. Those who integrate autonomous agents today will navigate tomorrow’s uncertainties with resilience and strategic agility, safeguarding digital assets while enabling sustained innovation.
Appendix

Glossary of Key Terms and Definitions
- Autonomous AI Agent: A software component that continuously monitors security-relevant data, applies learning algorithms to identify threats and executes predefined actions to mitigate risk without direct human intervention.
- Signature-Based Detection: A method relying on known indicators—file hashes or known malware patterns—to identify and block threats.
- Anomaly-Based Detection: Flags deviations from an established baseline of normal behavior as potential security incidents.
- Machine Learning: Algorithms that learn from data to make predictions or decisions.
- Supervised Learning: Models trained on labeled datasets to classify inputs or predict outcomes.
- Unsupervised Learning: Identifies patterns or groupings in unlabeled data.
- Reinforcement Learning: Agents interact with an environment, receive rewards or penalties, and adjust actions to maximize cumulative reward.
- Transfer Learning: Reuses a pre-trained model for a new, related task to accelerate learning.
- Perception Module: Ingests and preprocesses raw data from sensors, logs and telemetry sources.
- Knowledge Repository: Stores historical events, threat intelligence and contextual metadata for correlation and reasoning.
- Decision Engine: Evaluates risks, prioritizes alerts and determines response actions based on policies and real-time assessments.
- Adaptive Learning Loop: Refines models based on confirmed incidents, false positive tuning and emerging threat data.
- Data Drift: Statistical shifts in input data over time that degrade model accuracy if undetected.
- Adversarial Attack: Attempts to manipulate or deceive models by introducing malicious inputs to evade detection.
- Explainable AI (XAI): Techniques that make model outputs and decision logic transparent and interpretable to human users.
- Contextual Awareness: Enriches raw data with semantic metadata—asset criticality, user role, threat intelligence—to improve decision accuracy.
- Mean Time to Detect (MTTD): Average time between a security event occurrence and its detection.
- Mean Time to Respond (MTTR): Average time from detection to containment or remediation.
- False Positive Rate: Proportion of benign events incorrectly flagged as malicious.
- False Negative Rate: Proportion of actual threats missed by detection.
- SIEM (Security Information and Event Management): Centralized system that collects, aggregates and analyzes logs and events.
- SOAR (Security Orchestration, Automation and Response): Integrates security tools, automates workflows and coordinates incident response.
- XDR (Extended Detection and Response): Unifies endpoint, network and cloud data into a single detection and response solution.
- UEBA (User and Entity Behavior Analytics): Applies machine learning to user and device activities to identify insider threats through anomalous patterns.
- NDR (Network Detection and Response): Analyzes network traffic in real time to detect advanced threats and lateral movement.
- Threat Intelligence Feed: Curated data—indicators of compromise, attack campaign profiles—used to enrich analytics and detection models.
- Kill Chain: Model breaking down cyberattacks into stages—reconnaissance through actions on objectives—to guide detection and response.
- MITRE ATT&CK: Knowledge base of adversary tactics and techniques mapped to common attack scenarios.
- Diamond Model: Intrusion analysis framework mapping adversary, capability, infrastructure and victim relationships.
- Operational Technology (OT): Systems—hardware and software—that monitor and control physical processes in industrial environments.
- Internet of Things (IoT): Network-connected devices often lacking built-in security, increasing the attack surface.
- Data Normalization: Standardizes heterogeneous formats into a common structure for unified analysis.
- Data Enrichment: Augments raw data with context—geolocation, asset value, reputation scores—to improve accuracy.
- Streaming Analytics: Real-time processing of continuous data streams to identify anomalies as they occur.
- Graph Analytics: Examines relationships between entities to uncover complex attack pathways.
- Privacy by Design: Embeds data protection and privacy considerations throughout system development.
- Data Minimization: Collects only data necessary for a specific security objective to reduce privacy risks.
- Federated Learning: Trains models locally on edge devices and aggregates updates centrally without sharing raw data.
- Differential Privacy: Introduces noise into analysis to protect individual privacy while preserving insights.
- Drift Detection: Monitors data and model performance to identify shifts that require retraining.
- Adversarial Training: Includes manipulated inputs in training datasets to improve resilience against attacks.
- Zero-Trust Architecture: Requires continuous verification of user and device trust before granting resource access.
- Self-Healing Network: Autonomously reconfigures and heals itself in response to detected faults or incidents.
- Quantum-Enhanced Analytics: Leverages quantum computing to accelerate complex pattern recognition and cryptographic tasks.
Conceptual Models and Frameworks
These frameworks provide structured lenses for designing, evaluating and governing autonomous AI agent–driven security solutions.
- MITRE ATT&CK: A matrix of adversary tactics and techniques used to align detection rules, structure threat intelligence and benchmark coverage gaps.
- Cyber Kill Chain: Segments attack stages—reconnaissance through actions on objectives—to guide detection policies and automated response playbooks.
- Diamond Model of Intrusion Analysis: A graph‐based approach mapping adversary, capability, infrastructure and victim relationships for contextual correlation.
- OODA Loop: A cycle of Observe, Orient, Decide and Act, mirrored by agent modules for ingestion, contextualization, decision‐making and automated remediation.
- BDI Model: Conceptualizes agents by Beliefs (perception modules), Desires (policy objectives) and Intentions (decision engines) to enhance modularity.
- NIST Cybersecurity Framework: Guides risk management across Identify, Protect, Detect, Respond and Recover functions.
- NIST AI Risk Management Framework: Provides governance for trustworthy AI—risk assessment, validation, monitoring and accountability.
- FAIR (Factor Analysis of Information Risk): Quantifies risk components—threat frequency, vulnerability, loss magnitude—to align detection metrics with financial impact.
- Data Quality Maturity Model: Assesses governance, integration and profiling practices to ensure high-fidelity telemetry for model accuracy.
- Gartner Hype Cycle: Tracks technology maturity—from trigger through plateau—to inform adoption strategies and avoid early‐stage pitfalls.
- STIX/TAXII: Standards for sharing threat intelligence in a machine‐readable format, enabling automated exchange of indicators and contexts.
- OCSF (Open Cybersecurity Schema Framework): Standardizes event schemas across domains to simplify data ingestion and cross‐domain analytics.
- NIST SP 800-150: Specifies event logging requirements—authentication, privileged operations, network flows—to ensure reliable inputs.
- Forrester Data Quality Framework: Defines metrics—error rates, completeness, freshness—to prioritize telemetry improvements tied to business outcomes.
- MITRE ATLAS: Catalogues adversarial machine learning tactics—evasion, poisoning—informs resilience testing and red teaming.
- IEEE Ethically Aligned Design: Principles for responsible AI—human welfare, transparency, accountability—to shape agent policies and ensure compliance.
- Privacy by Design & DPIAs: Integrates data protection into architecture and uses impact assessments to evaluate personal data risks and mitigations.
Clarifications on Common Reader Questions
How do autonomous AI agents differ from traditional security tools?
Traditional tools rely on static signatures and manual rules, requiring constant updates. Autonomous agents ingest real‐time telemetry, apply adaptive learning to detect novel threats, and execute context‐aware responses without direct human intervention.
Do agents replace SIEM and SOAR platforms?
Agents complement SIEM and SOAR. They feed enriched, prioritized alerts into SIEM to reduce noise and invoke SOAR workflows for routine containment, while human analysts focus on complex cases.
What level of human oversight is required?
A human-in-the-loop model ensures low-risk actions are automated, while critical decisions require analyst approval. Audit logs and clear escalation criteria maintain accountability and trust.
How critical is data quality for agent performance?
High-quality, normalized, timestamp-synchronized inputs from diverse sources maximize detection accuracy and minimize drift. Continuous profiling, schema versioning and validation checks are essential data governance practices.
How do agents handle encrypted traffic and fileless attacks?
Agents analyze metadata—packet sizes, session timing—for encrypted traffic and integrate with TLS inspection when permitted. For fileless attacks, they monitor system calls, process trees and memory behavior to detect in-memory exploits.
What metrics evaluate agent effectiveness?
- Detection Accuracy: Recall and precision rates.
- Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR).
- False Positive Rate: Analyst fatigue indicator.
- Resource Utilization: CPU, memory and network overhead.
How do agents adapt to model drift and evolving threats?
Drift detection monitors feature distributions, triggering retraining pipelines that incorporate new incident data, threat intelligence and analyst feedback. Active learning solicits human annotations for low-confidence alerts.
Are agents vulnerable to adversarial attacks?
Mitigations include adversarial training, ensemble architectures, input validation and continuous red teaming to identify and remediate model weaknesses.
How transparent are agent decisions?
Rule-based and tree models offer native interpretability, while deep learning models rely on post-hoc explanation. Confidence scores, decision paths and feature attributions enhance analyst visibility.
What privacy considerations arise from continuous monitoring?
- Data Minimization: Collect only necessary attributes.
- Anonymization/Pseudonymization: Reduce re-identification risk.
- Access Controls: Role-based permissions on raw telemetry.
- Data Retention Policies: Automated purges aligned with regulations.
How do agents ensure compliance with global regulations?
Map data flows to GDPR, CCPA, HIPAA and NIS2, enforce regional data residency, establish Data Processing Agreements and maintain audit logs of model training and response actions.
How do agents integrate with existing infrastructure?
Integration via open APIs, standardized data formats (CEF, Syslog) and connectors. Common integrations include SIEM, SOAR, endpoint protection and cloud security controls. Standards such as STIX/TAXII and OpenC2 ensure interoperability.
Can agents scale across distributed and hybrid environments?
Yes. Architectures combine edge agents for low-latency inference, regional aggregators for mid-tier correlation and central analytics clusters for deep analysis and model retraining, with adaptive load-balancing for resilience.
What licensing and total cost considerations apply?
Consider subscription fees, data volume, number of endpoints, infrastructure costs and operational expenses. Elastic cloud deployment and consumption pricing help align costs with usage.
How should organizations begin with autonomous agents?
- Conduct a maturity assessment to identify priority use cases.
- Define success criteria—MTTD reduction, false positive targets—for pilot evaluation.
- Select a limited-scope pilot focusing on high-value assets.
- Establish cross-functional governance and data access protocols.
- Measure performance, gather feedback and refine iteratively.
- Scale incrementally, applying lessons learned to new domains.
AI Tools and Resources
This catalog summarizes AI-driven security platforms, open-source frameworks and standards referenced throughout this eBook.
- Darktrace: Self-learning detection system using unsupervised AI to model enterprise behavior and detect subtle anomalies.
- Vectra AI: NDR solution leveraging deep learning to uncover hidden attacker behaviors and prioritize investigations.
- CrowdStrike Falcon: Cloud-native EDR platform combining AI-driven detection with threat intelligence and automated containment.
- Microsoft Azure Sentinel: Cloud SIEM and SOAR with AI analytics for threat hunting and automated response.
- Palo Alto Networks Cortex XDR: Unifies endpoint, network and cloud data into AI-driven analytics and response playbooks.
- IBM QRadar: SIEM platform with integrated AI advisors and graph analytics for advanced threat correlation.
- AWS GuardDuty: Managed threat detection for AWS workloads using machine learning to identify suspicious activity.
- Elastic Security: Open-source analytics leveraging the Elastic Stack for unified SIEM, endpoint protection and threat hunting.
- Microsoft Defender for Endpoint: Endpoint security solution with behavior analytics, threat intelligence and integrated EDR.
- SentinelOne Singularity: Autonomous endpoint protection combining AI detection, active response and rollback.
- Claroty: OT and IoT security platform offering AI-driven visibility and threat detection for industrial networks.
- Nozomi Networks: OT security with real-time monitoring, anomaly detection and asset discovery for critical infrastructure.
- Cybereason: Endpoint detection and AI-driven hunting platform for advanced threat prevention.
- Recorded Future: Threat intelligence applying AI to open source and proprietary feeds for real-time risk assessments.
- Anomali: Aggregates and normalizes threat feeds, correlating indicators with internal telemetry.
- Intel 471: Provides deep dark web and threat actor intelligence using AI-powered data collection.
- IBM X-Force Exchange: Collaborative threat intelligence platform offering enriched indicators and research.
- TensorFlow: Open-source library for building and training machine learning models for security analytics.
- PyTorch: Deep learning framework for rapid prototyping of detection models and reinforcement learning.
- scikit-learn: Python library offering algorithms for classification, clustering and anomaly detection.
- OpenAI Gym: Toolkit for developing and comparing reinforcement learning algorithms in simulated security environments.
- Ray RLlib: Scalable reinforcement learning library for distributed training of security agents.
- Apache Kafka: Distributed event streaming platform for real-time security telemetry distribution.
- Apache Flink: Stream processing engine supporting event-driven analytics and complex correlation.
- Esper (Apache Esper): Real-time event processing library for complex pattern matching in security events.
- Apache Spark MLlib: Scalable machine learning library integrated with Spark streaming for large-scale inference.
- STIX and TAXII: Standards for structuring and exchanging threat intelligence.
- OpenC2: Language standard for interoperable command and control of cyber defense components.
- MITRE ATT&CK and MITRE D3FEND: Knowledge bases mapping adversary tactics to detection and defensive techniques.
- Open Cybersecurity Schema Framework (OCSF): Emerging schema for standardizing security event taxonomies.
- NIST AI Risk Management Framework: Guidelines for establishing trustworthy AI systems in security.
- NIST SP 800-150: Guidance on security event logging to support reliable detection.
- ISO/IEC 27001 and ISO/IEC 27701: Standards for information security and privacy management in detection systems.
- FAIR: Framework for quantifying information risk and reporting on security investments.
The AugVation family of websites helps entrepreneurs, professionals, and teams apply AI in practical, real-world ways—through curated tools, proven workflows, and implementation-focused education. Explore the ecosystem below to find the right platform for your goals.
Ecosystem Directory
AugVation — The central hub for AI-enhanced digital products, guides, templates, and implementation toolkits.
Resource Link AI — A curated directory of AI tools, solution workflows, reviews, and practical learning resources.
Agent Link AI — AI agents and intelligent automation: orchestrated workflows, agent frameworks, and operational efficiency systems.
Business Link AI — AI for business strategy and operations: frameworks, use cases, and adoption guidance for leaders.
Content Link AI — AI-powered content creation and SEO: writing, publishing, multimedia, and scalable distribution workflows.
Design Link AI — AI for design and branding: creative tools, visual workflows, UX/UI acceleration, and design automation.
Developer Link AI — AI for builders: dev tools, APIs, frameworks, deployment strategies, and integration best practices.
Marketing Link AI — AI-driven marketing: automation, personalization, analytics, ad optimization, and performance growth.
Productivity Link AI — AI productivity systems: task efficiency, collaboration, knowledge workflows, and smarter daily execution.
Sales Link AI — AI for sales: lead generation, sales intelligence, conversation insights, CRM enhancement, and revenue optimization.
Want the fastest path? Start at AugVation to access the latest resources, then explore the rest of the ecosystem from there.
